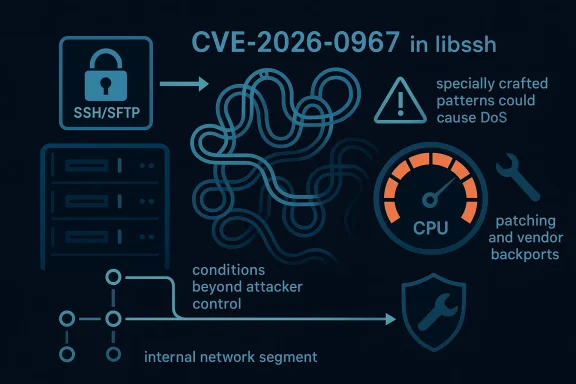
A successful attack against CVE-2026-0967 is not the kind of issue that can be triggered effortlessly from across the internet with a single packet and no setup. Microsoft’s own wording makes that distinction clear: the attack requires conditions beyond the attacker’s control, meaning the adversary may need to learn something about the target environment, prepare the environment to improve reliability, or position themselves in the network path before the vulnerable component can be pushed into failure. That is an important clue for defenders, because it suggests a practical denial-of-service scenario rather than a purely theoretical one.
At the same time, this should not be mistaken for a low-priority defect. libssh is a widely used SSH library, and the upstream project’s February 10, 2026 security release explicitly lists CVE-2026-0967 as a security fix, describing it as a case where “specially crafted patterns could cause DoS.” network-facing security library, a denial-of-service condition, and a trigger that depends on crafted input is exactly the sort of bug that can quietly disrupt servers, appliances, automation workflows, and embedded systems if administrators assume the issue is too obscure to matter.
libssh sits in a deceptively important place in the software stack. It is not a consumer-facing application that people open and close; it is a protocol library that other software embeds to speak SSH and SFTP. That means its bugs often show up as secondary failures elsewhere: a management interface that stops responding, an automation job that hangs, a file transfer service that exits, or a daemon that repeatedly crashes under load. When a protocol library becomes unstable, the blast radius is often larger than the headline makes it look.
The upstream release notes for libssh 0.12.0 and 0.11.4 show a broader security cleanup in the same release train, including several other CVEs fixed at once. CVE-2026-0967 appears alongside memory-safety and parser bugs, which tells us the maintainers treated it as part of a broader hardening effort rather than an isolated annoyance. That context matters: when a project issues a security release with multiple fixes, it usually means maintainers have been working through an accumulated backlog of edge cases that can be provoked by hostile or malformed input.
The wording “ineffiion processing” is also significant. It points to a classic denial-of-service class: regular expression engines can sometimes spend disproportionate amounts of CPU time on carefully chosen strings. In other words, the issue is not necessarily that the regex is “wrong” in a syntax sense, but that the cost of processing certain patterns can explode under adversarial input. That kind of weakness is especially dangerous in daemons and network services, where a single bad request can pin a worker thread, degrade latency, or force restarts.
The Microsoft advisory language adds one more layer of nuance. By stating that a successful attack depends on conditions beyond the attacker’s control, Microsoft is essentially telling defenders that exploitation may require more than a straightforward remote probe. That does not make the vulnerability harmless. It does mean that exposure can vary significantly depending on deployment topology, whether the component is internet-facing, and whether an attacker can influence traffic paths or craft inputs over time.
Security advisories around libssh have historically covered a mix of memory corruption, parsing mistakes, and denial-of-service conditions. The February 2026 release that contains CVE-2026-0967 fits that pattern, listing multiple fixes in a single maintenance drop. Upstream called out CVE-2026-0964, CVE-2026-0965, CVE-2026-0966, CVE-2026-0967, and CVE-2026-0968 together, which is a strong sign that the project was tightening several adjacent code paths at once.
That clustering of fixes matters becauseof-service bugs rarely exist in complete isolation. They often live near parsers, validators, configuration handlers, or matching logic that was originally written for convenience and later exposed to untrusted input. Once a pattern-matching routine becomes part of a network-facing workflow, even a small inefficiency can become a security issue if an attacker can repeat it at scale or force it into pathological behavior.
Another important point is that the CVE label itself does not guarantee a dramatic exploit chain. In modern vulnerability handling, availability bugs can be just as operationally serious as memory corruption, particularly when they affect shared infrastructure. A service that crashes, stalls, or burns CPU on demand can create service degradation, failover churn, and helpdesk noise even if no data is stolen and no code is executed.
Historically, the security industry has seen many regular-expression denial-of-service problems across stacks, from parsers and configuration tools to web filters and validation routines. The lesson is usually the same: backtracking engines and poorly bounded pattern handling are easy to underestimate. A crafted string can look innocent to a human reviewer while still forcing the engine into expensive work. That makes these issues appealing to attackers because they are often reproducible, low-noise, and hard to spot in casual testing.
It also suggests that network placement matters. If the vulnerable code is only reachable through authenticated, segmented, or internal pathways, the attack surface shrinks. If, however, the component sits behind a public-facing SSH endpoint, an automation gateway, or a management interface exposed through a reverse proxy, the barrier to abuse becomes much lower. In those deployments, the “conditions beyond the attacker’s control” may be easier to satisfy than the short advisory language implies.
The upstream libssh note does not publish the full technical exploit recipe in the release summary, so we should be careful not to overstate the mechanism. What we can say confidently is that the project itself framed CVE-2026-0967 as a DoS caused by specially crafted patterns. That language strongly suggests the vulnerable code used a pattern matcher in a way that could be pushed into pathological behavior under malicious input.
A key operational risk with regex-based DoS is that the triggin logs. Unlike a malformed packet that crashes immediately, a regex issue may first manifest as slow requests, CPU spikes, or increased latency. That makes it easy to blame “load” or “noisy neighbors” until someone correlates the slowdown with a crafted sequence of inputs.
The same dynamic appears in many libraries and frameworks: a feature designed for flexibility can become a performance sink under adversarial conditions. That is especially true when the code path is executed repeatedly in a network service. A few expensive inputs may not matter much on a desktop tool, but they can overwhelm a shared daemon or embedded appliance very quickly.
This also helps explain why the issue should be taken seriously even without dramatic exploitability. Security releases are not simply about preventing theoretical abuses; they are about reducing the odds that a bug in a shared dependency becomes a common failure mode across many products. The more widely a library is embedded, the more a single fix becomes a supply-chain event.
For that reason, patch validation matters as much as patch installation. A host that has “updated libssh” in package metadata may still be vulnerable if the wrong branch was backported or if a container image was rebuilt from stale layers. Administrators should verify the exact fixed build, not just the headline version.
It is also possible that the special pattern needed to trigger the problem becomes easier to deliver in certain protocol contexts than others. For example, a matching routine may only be reachable after a handshake, during configuration parsing, or when processing a specific class of metadata. That kind of structure means the real-world exposure can be far narrower than the library-wide CVE description suggests, but also more intense in the niches where the bug exists.
This is why operational intelligence matters. If a defender sees repeated requests with unusual patterns, long-lived sessions, or unexplained CPU consumption in SSH-adjacent services, that may be an early warning. In many cases, denial-of-service bugs leave behind clues in performance counters long before they produce a visible outage.
This is especially true in environments where the affected component runs with limited isolation. If the library is embedded in a shared daemon or a monolithic control plane, a denial-of-service event can affect more than one feature at once. A repeated crash in that layer can create cascading failures that make the original bug look worse than the advisory line suggests.
A practical response plan usually includes:
Embedded deployments deserve special attention because they often use older library branches and slower patch cadences. If a vendor has not issued a firmware refresh, the vulnerable libssh code may persist long after upstream has moved on. That makes consumer and small-office devices particularly vulnerable to long-tail exposure.
Consumers are also exposed through third-party services they do not control. Backup clients, sync tools, development environments, and vendor support utilities can all embed libssh transitively. If those tools are used in environments with hostile endpoints or manipulated network paths, the denial-of-service condition becomes a realistic operational headache.
There is also the usual downstream risk that package maintainers will patch differently across branches. One product may receive a backport that fully addresses the regex path, while another only updates surrounding code. That kind of inconsistency creates uncertainty for vulnerability management teams trying to classify exposure at scale.
A second point to watch is whether additional hardening follows in subsequent releases. Security bugs that involve pattern processing often reveal nearby code paths that deserve review. If libssh maintainers have found one inefficient regex path, they may find other places where input validation or cost control should be tightened. That kind of follow-on work is often what separates a one-off patch from a meaningful hardening cycle.
Finally, defenders should watch telemetry rather than waiting for a smoking gun. A sudden rise in CPU consumption, session stalls, or repeated resets around SSH-related services may be the first sign that a vulnerable path is being exercised. The best time to find this bug is before it becomes an incident.
Source: MSRC Security Update Guide - Microsoft Security Response Center
At the same time, this should not be mistaken for a low-priority defect. libssh is a widely used SSH library, and the upstream project’s February 10, 2026 security release explicitly lists CVE-2026-0967 as a security fix, describing it as a case where “specially crafted patterns could cause DoS.” network-facing security library, a denial-of-service condition, and a trigger that depends on crafted input is exactly the sort of bug that can quietly disrupt servers, appliances, automation workflows, and embedded systems if administrators assume the issue is too obscure to matter.
 Overview
Overview
libssh sits in a deceptively important place in the software stack. It is not a consumer-facing application that people open and close; it is a protocol library that other software embeds to speak SSH and SFTP. That means its bugs often show up as secondary failures elsewhere: a management interface that stops responding, an automation job that hangs, a file transfer service that exits, or a daemon that repeatedly crashes under load. When a protocol library becomes unstable, the blast radius is often larger than the headline makes it look.The upstream release notes for libssh 0.12.0 and 0.11.4 show a broader security cleanup in the same release train, including several other CVEs fixed at once. CVE-2026-0967 appears alongside memory-safety and parser bugs, which tells us the maintainers treated it as part of a broader hardening effort rather than an isolated annoyance. That context matters: when a project issues a security release with multiple fixes, it usually means maintainers have been working through an accumulated backlog of edge cases that can be provoked by hostile or malformed input.
The wording “ineffiion processing” is also significant. It points to a classic denial-of-service class: regular expression engines can sometimes spend disproportionate amounts of CPU time on carefully chosen strings. In other words, the issue is not necessarily that the regex is “wrong” in a syntax sense, but that the cost of processing certain patterns can explode under adversarial input. That kind of weakness is especially dangerous in daemons and network services, where a single bad request can pin a worker thread, degrade latency, or force restarts.
The Microsoft advisory language adds one more layer of nuance. By stating that a successful attack depends on conditions beyond the attacker’s control, Microsoft is essentially telling defenders that exploitation may require more than a straightforward remote probe. That does not make the vulnerability harmless. It does mean that exposure can vary significantly depending on deployment topology, whether the component is internet-facing, and whether an attacker can influence traffic paths or craft inputs over time.
Background
libssh is a mature C library implementing SSHv2 and related features for clients and servers. In practice, that makes it part of the plumbing for tools and services that need secure shell access, file transfer, automation, and remote administration. Because it is a library, many downstream projects inherit its behavior directly, including bugs in parsing and validation logic that users may never realize are coming from libssh until something breaks.Security advisories around libssh have historically covered a mix of memory corruption, parsing mistakes, and denial-of-service conditions. The February 2026 release that contains CVE-2026-0967 fits that pattern, listing multiple fixes in a single maintenance drop. Upstream called out CVE-2026-0964, CVE-2026-0965, CVE-2026-0966, CVE-2026-0967, and CVE-2026-0968 together, which is a strong sign that the project was tightening several adjacent code paths at once.
That clustering of fixes matters becauseof-service bugs rarely exist in complete isolation. They often live near parsers, validators, configuration handlers, or matching logic that was originally written for convenience and later exposed to untrusted input. Once a pattern-matching routine becomes part of a network-facing workflow, even a small inefficiency can become a security issue if an attacker can repeat it at scale or force it into pathological behavior.
Another important point is that the CVE label itself does not guarantee a dramatic exploit chain. In modern vulnerability handling, availability bugs can be just as operationally serious as memory corruption, particularly when they affect shared infrastructure. A service that crashes, stalls, or burns CPU on demand can create service degradation, failover churn, and helpdesk noise even if no data is stolen and no code is executed.
Historically, the security industry has seen many regular-expression denial-of-service problems across stacks, from parsers and configuration tools to web filters and validation routines. The lesson is usually the same: backtracking engines and poorly bounded pattern handling are easy to underestimate. A crafted string can look innocent to a human reviewer while still forcing the engine into expensive work. That makes these issues appealing to attackers because they are often reproducible, low-noise, and hard to spot in casual testing.
What Microsoft’s wording implies
Microsoft’s description is unusually useful because it gives defenders a hint about exploit preconditions. The advisory says the attack depends on conditions beyond the attacker’s control, and the example language references environment knowledge, preparation to improve exploit reliability, or being in a position to observe or modify traffic. That sounds less like a single-shot crash and more like a scenario where the attacker may need to shape the context around the vulnerable code before the pattern-processing weakness becomes actionable.Why that matters operationally
For defenders, this changes the triage conversation. An issue that requires environmental preparation may be less likely to be mass-exploited immediately, but it can still be very practical against a targeted server or a high-value appliance. Less automatable is not the same as less serious. In many real incidents, an attacker who can spend time preparing the environment is exactly the adversary you should worry about most.It also suggests that network placement matters. If the vulnerable code is only reachable through authenticated, segmented, or internal pathways, the attack surface shrinks. If, however, the component sits behind a public-facing SSH endpoint, an automation gateway, or a management interface exposed through a reverse proxy, the barrier to abuse becomes much lower. In those deployments, the “conditions beyond the attacker’s control” may be easier to satisfy than the short advisory language implies.
- The issue is likely context-sensitive rather than universally trivial.
- Network position may be part of exploitability.
- Target knowledge could improve success rate.
- Repeated attempts may be needed to trigger worst-case behavior.
- Availability impact can still be severe even without code execution.
Why regular expressions become security issues
Regular expressions are useful because they let developers express complex matching rules concisely. They become dangerous when developers assume that readable syntax also means predictable runtime cost. In practice, certain patterns can produce exponential or otherwise disproportionate processing time when matched against crafted inputs, particularly in engines that use backtracking.ReDoS in plain language
A regular-expression denial of service, often shortened to ReDoS, happens when a string that should be rejected or classified quickly instead causes the engine to chew through far more CPU than expected. The problem is not necessarily an infinite loop. It is excessive work. That distinction matters because the process may appear healthy right up until traffic spikes or an attacker keeps sending adversarial patterns.The upstream libssh note does not publish the full technical exploit recipe in the release summary, so we should be careful not to overstate the mechanism. What we can say confidently is that the project itself framed CVE-2026-0967 as a DoS caused by specially crafted patterns. That language strongly suggests the vulnerable code used a pattern matcher in a way that could be pushed into pathological behavior under malicious input.
A key operational risk with regex-based DoS is that the triggin logs. Unlike a malformed packet that crashes immediately, a regex issue may first manifest as slow requests, CPU spikes, or increased latency. That makes it easy to blame “load” or “noisy neighbors” until someone correlates the slowdown with a crafted sequence of inputs.
Why this class keeps returning
This problem keeps reappearing because developers often trust pattern matching too much. They may use it for validation, parsing, or classification in places where the input is ultimately attacker-controlled. Once that happens, the regex engine itself becomes part of the attack surface, and the cost profile of the pattern matters as much as whether it produces the correct match.The same dynamic appears in many libraries and frameworks: a feature designed for flexibility can become a performance sink under adversarial conditions. That is especially true when the code path is executed repeatedly in a network service. A few expensive inputs may not matter much on a desktop tool, but they can overwhelm a shared daemon or embedded appliance very quickly.
- Regex bugs are often reliability bugs before they are security bugs.
- Adversarial inputs can turn a “normal” parser into a CPU sink.
- Backtracking engines are particularly sensitive to pathological patterns.
- Slow failures are harder to triage than immediate crashes.
- Network services multiply the impact because the expensive path can be triggered repeatedly.
libssh’s security release and patch context
The libssh 0.12.0 and 0.11.4 security release is an important anchor because it shows the project shipped the fix as part of a coordinated maintenance effort, not as a standalone patch. The release notes list the security issues fixed in that train and explicitly include CVE-2026-0967 as “Specially crafted patterns could cause DoS.” That is the clearest upstream statement available in the materials at hand.Whtells us
When a project ships several security fixes together, downstream maintainers usually need to treat the entire release as a priority update. Even if one CVE seems modest on its own, the release cadence suggests the codebase was in a vulnerable state across multiple surfaces. In practice, that means package maintainers, distro vendors, appliance builders, and internal platform teams should check whether their libssh build lines have received the backport or the full upstream release.This also helps explain why the issue should be taken seriously even without dramatic exploitability. Security releases are not simply about preventing theoretical abuses; they are about reducing the odds that a bug in a shared dependency becomes a common failure mode across many products. The more widely a library is embedded, the more a single fix becomes a supply-chain event.
The significance for downstream users
Downstream consumers rarely see the regular expression itself. They see the service that depends on it. That means administrators may need to trace the vulnerable dependency through a chain of packages, container images, or vendor firmware builds before they can determine exposure. This is one of those situations where version numbers alone may be misleading, because vendors frequently backport fixes without matching the upstream release tag.For that reason, patch validation matters as much as patch installation. A host that has “updated libssh” in package metadata may still be vulnerable if the wrong branch was backported or if a container image was rebuilt from stale layers. Administrators should verify the exact fixed build, not just the headline version.
Attack conditions and exploitation realism
Microsoft’s wording suggests that exploitation may require more than casual remote interaction, which is an important distinction for threat modeling. A vulnerability that depends on environmental conditions can still be weaponized, but it may require better reconnaissance, a more controlled attack path, or patience. In security terms, that changes the attacker economics rather than removing the risk.Why “conditions beyond the attacker’s control” is not reassuring
Attackers do not need a universal exploit if they can repeatedly target one exposed server. If the vulnerable libssh component is part of an internet-facing service, an authenticated workflow, or an internal administrative plane, the attacker may be able to satisfy those conditions through normal interaction over time. The adversary does not have to win everywhere; they only have to win once where it matters.It is also possible that the special pattern needed to trigger the problem becomes easier to deliver in certain protocol contexts than others. For example, a matching routine may only be reachable after a handshake, during configuration parsing, or when processing a specific class of metadata. That kind of structure means the real-world exposure can be far narrower than the library-wide CVE description suggests, but also more intense in the niches where the bug exists.
- Environment knowledge can make the attack far more practical.
- Authentication does not always reduce risk enough to ignore the issue.
- A single exposed management endpoint can be enough.
- Path-dependent bugs are harder to scan for but still exploitable.
- Repeatable pressure against a CPU-heavy path can cause persistent service degradation.
The likely attacker playbook
A realistic attacker would probably start by identifying where libssh is used in the target environment. Then they would look for services that process untrusted SSH-related input, especially if those services have internet exposure or sit behind a public portal. Finally, they would test whether crafted patterns produce measurable slowdowns, CPU spikes, or crashes.This is why operational intelligence matters. If a defender sees repeated requests with unusual patterns, long-lived sessions, or unexplained CPU consumption in SSH-adjacent services, that may be an early warning. In many cases, denial-of-service bugs leave behind clues in performance counters long before they produce a visible outage.
Enterprise impact
Enterprises are where a libssh denial-of-service bug can become expensive fast. Shared infrastructure often relies on protocol libraries in ways that are invisible to end users. A single service crash may mean dropped automation tasks, failed backup jobs, broken bastion access, or management portals that become intermittently unavailable during maintenance windows.Infrastructure and service risk
The highest exposure is usually in network-facing services that handle arbitrary or semi-trusted input. That includes bastion hosts, file transfer gateways, orchestration tools, configuration management systems, and appliance web consoles that embed SSH functionality behind the scenes. In those environments, a CPU-intensive code path is more than a nuisance; it can starve co-located workloads or trigger autoscaling and failover behaviors that create secondary instability.This is especially true in environments where the affected component runs with limited isolation. If the library is embedded in a shared daemon or a monolithic control plane, a denial-of-service event can affect more than one feature at once. A repeated crash in that layer can create cascading failures that make the original bug look worse than the advisory line suggests.
Triage priorities for enterprises
Enterprises should focus on whether libssh is used in any externally reachable or authentication-sensitive service. They should then verify whether their vendor has backported the February 2026 security release or a later patch. If the answer is uncertain, the safest assumption is that the component still needs review.A practical response plan usually includes:
- Inventory every application, appliance, and container image that bundles libssh.
- Confirm whether the fixed upstream release or a vendor backport is present.
- Test the patched build in a staging environment for regressions.
- Roll the update to internet-facing or high-value management services first.
- Watch CPU, latency, and crash telemetry during and after deployment.
- Enterprise risk is mostly about shared blast radius.
- Edge services and administrative planes deserve first attention.
- Backported fixes must be verified, not assumed.
- Staging is useful, but exposure should not wait for perfection.
- Monitoring should include both crashes and resource exhaustion.
Consumer and embedded impact
Consumer users will usually never see “libssh” on a splash screen, but that does not mean they are untouched. Many consumer-adjacent tools, embedded systems, and vendor appliances rely on libraries like libssh to provide secure remote access, firmware transfer, or support tooling. When those components misbehave, the end user experiences the symptom, not the library name.Where the bug is most likely to surface
The most visible consumer impact is likely to be indirect. A router admin interface may become slow or unavailable. A storage appliance may stop responding to management commands. A desktop or command-line tool might fail to connect to a remote endpoint or hang while parsing unexpected data. In all of those cases, the user sees a reliability failure, not a security bulletin.Embedded deployments deserve special attention because they often use older library branches and slower patch cadences. If a vendor has not issued a firmware refresh, the vulnerable libssh code may persist long after upstream has moved on. That makes consumer and small-office devices particularly vulnerable to long-tail exposure.
Why users should still care
Even if the issue is “only” denial of service, repeated outages in a consumer or small-business setting can be disruptive and difficult to diagnose. A device that drops management access intermittently can appear flaky, damaged, or infected. That uncertainty makes patching even more important, because the user experience degrades long before anyone knows the root cause.Consumers are also exposed through third-party services they do not control. Backup clients, sync tools, development environments, and vendor support utilities can all embed libssh transitively. If those tools are used in environments with hostile endpoints or manipulated network paths, the denial-of-service condition becomes a realistic operational headache.
- Consumers rarely see the vulnerable library directly.
- Embedded products can lag upstream security fixes by months or years.
- Management-plane outages are often the first symptom.
- Indirect exposure through bundled tools is common.
- “Just a DoS” can still break critical consumer workflows.
Strengths and Opportunities
The good news is that this class of vulnerability is usually straightforward to remediate once the affected build is identified. Because libssh has already shipped a security release that names CVE-2026-0967 explicitly, the fix path should be clear for supported branches and for vendors willing to backport upstream changes.- The upstream project has already issued a security release covering the issue.
- The vulnerability clocused, which often simplifies validation after patching.
- Administrators can prioritize exposed services first instead of freezing the entire fleet.
- The advisory language provides useful guidance about attacker preconditions.
- Security teams can combine dependency inventory with traffic analysis to find exposure.
- Vendors have a clear backport target because the fix is already established upstream.
- The issue can be used to strengthen future regex review and input-handling practices.
Risks and Concerns
The biggest concern is that denial-of-service bugs tend to be underestimated, especially when they are framed as “special patterns” rather than memory corruption. That is a mistake. In production environments, CPU exhaustion and crash loops can be every bit as damaging as more sensational bugs, particularly when they affect shared control planes or embedded management services.- The exploit may be more practical than the short advisory language suggests.
- Different vendors may backport the fix unevenly.
- Some deployments may not realize libssh is present until an incident occurs.
- Regex-related performance bugs can be difficult to reproduce in labs.
- Attackers may use the issue selectively against high-value targets.
- Crashes may trigger orchestration churn, magnifying the outage.
- Monitoring gaps can hide the early signs of resource exhaustion.
Why the ambiguity matters
The advisory’s wording leaves room for interpretation about the exact trigger path. That is normal for security disclosures, but it does mean defenders should avoid overconfidence. A bug that sounds environment-dependent can still be reliable enough for a determined attacker, especially if the environment is stable and predictable. In other words, harder to exploit is not the same as hard to operationalize.There is also the usual downstream risk that package maintainers will patch differently across branches. One product may receive a backport that fully addresses the regex path, while another only updates surrounding code. That kind of inconsistency creates uncertainty for vulnerability management teams trying to classify exposure at scale.
Looking Ahead
The next thing to watch is downstream adoption. Upstream has already named the issue and shipped the release train that includes the fix, but the real question is how quickly vendors, appliance makers, and Linux distributions propagate it. In a library issue like this, the upstream patch is only the beginning; the operational risk remains until the fix lands in the products that actually ship libssh to users.A second point to watch is whether additional hardening follows in subsequent releases. Security bugs that involve pattern processing often reveal nearby code paths that deserve review. If libssh maintainers have found one inefficient regex path, they may find other places where input validation or cost control should be tightened. That kind of follow-on work is often what separates a one-off patch from a meaningful hardening cycle.
Finally, defenders should watch telemetry rather than waiting for a smoking gun. A sudden rise in CPU consumption, session stalls, or repeated resets around SSH-related services may be the first sign that a vulnerable path is being exercised. The best time to find this bug is before it becomes an incident.
- Verify whether your vendor has published a fixed libssh build.
- Check whether affected services are internet-facing or management-facing.
- Look for CPU spikes and timeouts around SSH-adjacent workloads.
- Rebuild container images rather than assuming the base image is patched.
- Treat embedded and appliance firmware as a separate patch track.
- Review whether similar regex or pattern-processing code exists elsewhere in your stack.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: