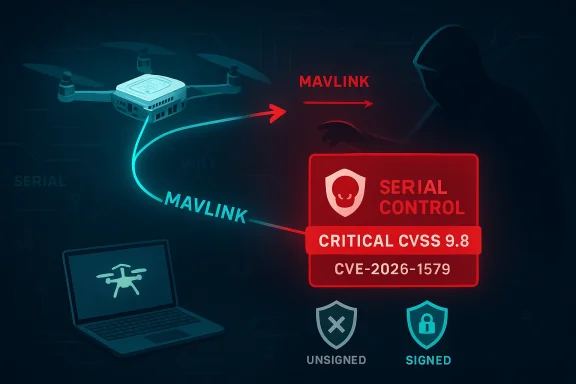
A newly published CISA industrial control systems advisory says PX4 Autopilot is vulnerable to remote command execution through the MAVLink interface when cryptographic message signing is not enabled, and the agency rates the issue critical at CVSS 9.8. The vulnerability, tracked as CVE-2026-1579, affects PX4 Autopilot v1.16.0_SITL_latest_stable and could let an attacker send unauthenticated MAVLink traffic that reaches the SERIAL_CONTROL function, effectively opening shell access on the vehicle or simulator. PX4’s own documentation already warns that unsigned MAVLink traffic can be used to issue shell commands, change parameters, upload missions, arm motors, or even terminate flight, which makes the advisory especially consequential for anyone deploying PX4 in real-world systems.
PX4 sits at the center of a large and increasingly important class of autonomous systems. It is open-source flight-controller firmware used across drones, robotics platforms, and companion-computer integrations, which means its security posture has direct implications for both hobbyists and industrial operators. CISA’s advisory places the affected product squarely in the Transportation Systems, Emergency Services, and Defense Industrial Base sectors, underscoring that this is not just a developer inconvenience but a control-system issue with operational consequences.
The technical root of the problem is familiar to anyone who has worked with MAVLink: by default, the protocol prioritizes openness and low latency over strong authentication. PX4’s current security guidance states plainly that, without message signing, any device that can send MAVLink messages to the vehicle over radio, network, or serial links can execute powerful actions, including shell access and flight-critical commands. That design choice made sense in early development workflows, but it becomes dangerous by default in production environments where attackers may be physically nearby or able to reach exposed telemetry links.
The specific CISA disclosure matters because it translates a general protocol weakness into a concrete vulnerability scenario. The advisory says the MAVLink interface can be abused to send the SERIAL_CONTROL message without cryptographic authentication, and that message can provide interactive shell access. In practice, that means an unauthenticated party with network or radio access to the interface may move from message injection to arbitrary command execution, which is why the CVSS vector is scored at the highest practical severity for confidentiality, integrity, and availability.
This is also part of a broader trend in cyber-physical systems: the weakest point is often not the flight code itself but the trust model around communications. PX4 supports MAVLink 2.0 message signing as its cryptographic authentication mechanism, and its documentation says unsigned messages are rejected when signing is enabled. That creates a stark split between secure and insecure deployments, because the same firmware can be resilient or trivially exposed depending on how the integrator configures the link.
The message-signing documentation adds another important detail: signing is built into the MAVLink module itself and does not require special build flags, but it is only effective when a valid secret key exists and the signing mode is configured correctly. PX4 stores the key and timestamp on the SD card, and it accepts provisioning only over USB via SETUP_SIGNING. That design protects remote channels from rekeying attacks, but it also means physical compromise or poor device handling can undermine the whole model.
The shell-access angle is especially sensitive because PX4 explicitly supports a MAVLink Shell over serial, USB, Wi‑Fi, UDP, and TCP links. In other words, the same architectural convenience that helps developers and operators troubleshoot vehicles can become a direct path to control when authentication is missing or misconfigured. The advisory therefore should be read as a warning not merely about one CVE, but about how many everyday operator tools can become attack primitives.
It is also notable that the advisory is issued in the context of operational technology. CISA’s recommended practices emphasize isolation, firewalls, VPNs, and minimizing internet exposure for control-system devices, which is standard guidance for industrial environments but still easy to neglect in drone deployments. That gap between best practice and field reality is where many cyber-physical incidents begin.
The impact is broader than the phrase “shell access” might suggest. A shell on an autopilot can be used for configuration inspection, log retrieval, parameter modification, file operations, and potentially further manipulation of mission behavior. In a fielded drone, those capabilities can affect not only the vehicle’s function but also safety, privacy, and evidentiary integrity.
The affected environment also matters. CISA says the vulnerability is relevant to Transportation Systems, Emergency Services, and the Defense Industrial Base, which points toward fleets, critical response vehicles, and defense-adjacent unmanned systems. Those sectors often mix ground stations, companion computers, long-range radios, and remote telemetry, all of which increase the number of places where MAVLink traffic could be intercepted or abused.
The practical danger lies in how ordinary the enabling conditions can be. PX4’s shell documentation states that the console can be reached via USB, telemetry, Wi‑Fi, UDP, or TCP on NuttX-based systems, which means real deployments may expose more paths than operators realize. Once any one of those paths is left open without signing, the attacker’s problem becomes one of reachability, not cryptanalysis.
The signing documentation also makes clear that configuration alone is insufficient. Operators must ensure a real key exists, set the correct
That reality is especially important for integrators and manufacturers. PX4 explicitly frames signing and link security as an integrator responsibility, which means organizations cannot assume the firmware will protect them from poor deployment choices. The firmware supplies the tools; the system builder decides whether they are actually used.
Longer term, the industry may need to rethink how much trust is placed in convenience features that were originally designed for development and debugging. As unmanned systems become more connected and more operationally critical, developer defaults are no longer good enough for production. PX4’s documentation already points in the right direction; the challenge now is enforcement, consistency, and ongoing operator discipline.
Source: CISA PX4 Autopilot | CISA
 Background
Background
PX4 sits at the center of a large and increasingly important class of autonomous systems. It is open-source flight-controller firmware used across drones, robotics platforms, and companion-computer integrations, which means its security posture has direct implications for both hobbyists and industrial operators. CISA’s advisory places the affected product squarely in the Transportation Systems, Emergency Services, and Defense Industrial Base sectors, underscoring that this is not just a developer inconvenience but a control-system issue with operational consequences.The technical root of the problem is familiar to anyone who has worked with MAVLink: by default, the protocol prioritizes openness and low latency over strong authentication. PX4’s current security guidance states plainly that, without message signing, any device that can send MAVLink messages to the vehicle over radio, network, or serial links can execute powerful actions, including shell access and flight-critical commands. That design choice made sense in early development workflows, but it becomes dangerous by default in production environments where attackers may be physically nearby or able to reach exposed telemetry links.
The specific CISA disclosure matters because it translates a general protocol weakness into a concrete vulnerability scenario. The advisory says the MAVLink interface can be abused to send the SERIAL_CONTROL message without cryptographic authentication, and that message can provide interactive shell access. In practice, that means an unauthenticated party with network or radio access to the interface may move from message injection to arbitrary command execution, which is why the CVSS vector is scored at the highest practical severity for confidentiality, integrity, and availability.
This is also part of a broader trend in cyber-physical systems: the weakest point is often not the flight code itself but the trust model around communications. PX4 supports MAVLink 2.0 message signing as its cryptographic authentication mechanism, and its documentation says unsigned messages are rejected when signing is enabled. That creates a stark split between secure and insecure deployments, because the same firmware can be resilient or trivially exposed depending on how the integrator configures the link.
Why this matters now
The timing is important because autonomous platforms are no longer isolated lab devices. They are increasingly tied to mission systems, cloud-connected ground stations, and companion computers, all of which expand the attack surface. In that environment, a protocol that assumes trusted senders can become an enterprise risk even when the underlying firmware is stable and well maintained.- Unauthenticated transport remains the central weakness.
- Shell access raises the impact well beyond simple telemetry tampering.
- Integrators rather than only firmware maintainers carry much of the operational burden.
- Network exposure is the most obvious route to exploitation.
- Physical access can also matter because of signing-key handling.
Overview
PX4’s guidance on MAVLink security has grown more explicit over time, and that evolution tells its own story. The current hardening guide says that production deployments should enable signing, restrict network exposure, and treat USB access differently from radio or IP-based links. It also recommends MAV_SIGN_CFG=1 for most deployments, which signs non-USB links while allowing unsigned USB access for maintenance. That recommendation is pragmatic, but it also reveals how much trust still rides on physical access assumptions.The message-signing documentation adds another important detail: signing is built into the MAVLink module itself and does not require special build flags, but it is only effective when a valid secret key exists and the signing mode is configured correctly. PX4 stores the key and timestamp on the SD card, and it accepts provisioning only over USB via SETUP_SIGNING. That design protects remote channels from rekeying attacks, but it also means physical compromise or poor device handling can undermine the whole model.
The shell-access angle is especially sensitive because PX4 explicitly supports a MAVLink Shell over serial, USB, Wi‑Fi, UDP, and TCP links. In other words, the same architectural convenience that helps developers and operators troubleshoot vehicles can become a direct path to control when authentication is missing or misconfigured. The advisory therefore should be read as a warning not merely about one CVE, but about how many everyday operator tools can become attack primitives.
It is also notable that the advisory is issued in the context of operational technology. CISA’s recommended practices emphasize isolation, firewalls, VPNs, and minimizing internet exposure for control-system devices, which is standard guidance for industrial environments but still easy to neglect in drone deployments. That gap between best practice and field reality is where many cyber-physical incidents begin.
The protocol design trade-off
MAVLink was built for lightweight, low-latency communication, not for zero-trust networking. That makes it efficient for drones and robotics, but it also means security features such as authentication are optional rather than inherent. The trade-off is understandable; the risk is that deployment teams sometimes inherit a development-centric default and mistake it for a hardened production setting.- Low latency and simplicity are MAVLink strengths.
- Default unauthenticated operation is the corresponding weakness.
- Signing solves authentication, not confidentiality.
- Operational discipline is required to keep the system safe.
The Vulnerability
The heart of CVE-2026-1579 is deceptively simple: if an attacker can reach the MAVLink interface and the deployment has not enabled message signing, the protocol does not distinguish between trusted and untrusted senders. CISA’s advisory says that unauthorized parties can use MAVLink traffic to invoke shell access without cryptographic authentication, and PX4’s own hardening guide confirms thatSERIAL_CONTROL with SERIAL_CONTROL_DEV_SHELL is one of the highest-risk commands in that model. That combination is why the issue is scored as critical rather than merely high.The impact is broader than the phrase “shell access” might suggest. A shell on an autopilot can be used for configuration inspection, log retrieval, parameter modification, file operations, and potentially further manipulation of mission behavior. In a fielded drone, those capabilities can affect not only the vehicle’s function but also safety, privacy, and evidentiary integrity.
Attack preconditions
The attack does not require code execution bugs in the firmware itself. Instead, the attacker needs access to the communication path and a target that still trusts unsigned MAVLink traffic. That may be a telemetry radio, a Wi‑Fi bridge, a serial line, or any exposed network service bound to MAVLink.- No cryptographic signing must be active.
- Attacker reachability to the MAVLink link is required.
- Shell-capable commands must be accepted by the target configuration.
- Operational exposure can be local, wireless, or network-based.
Affected Versions and Scope
CISA lists PX4 Autopilot v1.16.0_SITL_latest_stable as affected, with the product status marked known affected. The advisory’s wording suggests the issue is not tied to a narrow feature gate but to how MAVLink is deployed within that version family. That is significant because simulator and stable branches can still become operationally relevant in testing, integration, and even pre-production workflows.The affected environment also matters. CISA says the vulnerability is relevant to Transportation Systems, Emergency Services, and the Defense Industrial Base, which points toward fleets, critical response vehicles, and defense-adjacent unmanned systems. Those sectors often mix ground stations, companion computers, long-range radios, and remote telemetry, all of which increase the number of places where MAVLink traffic could be intercepted or abused.
Enterprise versus consumer exposure
For consumers, the immediate concern is often a single drone or test rig exposed through Wi‑Fi or a radio link. For enterprise and government operators, the issue scales across fleets, integrators, maintenance stations, and support workflows. That scale turns one insecure default into a potentially repeatable fleetwide failure mode.- Consumer operators may face local compromise or unsafe flight behavior.
- Fleet operators face systematic risk across many airframes.
- Integrators must manage key provisioning and port exposure.
- Maintenance workflows can unintentionally reintroduce unsigned access.
How Exploitation Works
CISA’s language and PX4’s security guidance together outline a straightforward exploitation path. An attacker who can send MAVLink messages to the vehicle can issueSERIAL_CONTROL requests to interact with the shell, assuming the link accepts unauthenticated traffic. If the target is reachable over radio, network, or serial and signing is not enforced, there is no protocol-level mechanism stopping the command.The practical danger lies in how ordinary the enabling conditions can be. PX4’s shell documentation states that the console can be reached via USB, telemetry, Wi‑Fi, UDP, or TCP on NuttX-based systems, which means real deployments may expose more paths than operators realize. Once any one of those paths is left open without signing, the attacker’s problem becomes one of reachability, not cryptanalysis.
Operational consequences
A successful attacker could do more than merely type commands into a shell. Depending on access level and system configuration, the attacker may be able to alter mission behavior, inspect logs, change parameters, or disrupt safe operation. That is precisely why the same vulnerability spans confidentiality, integrity, and availability in the CVSS model.- Mission interference is a realistic outcome.
- Parameter tampering can change flight behavior.
- File operations can affect logs and configuration.
- Crash or landing commands can create immediate safety hazards.
Remediation and Hardening
PX4’s primary mitigation is MAVLink 2.0 message signing, which provides authentication and integrity for MAVLink traffic. The hardening guide recommends enabling signing for non-USB links, provisioning a secret key, and verifying that unsigned messages from unknown sources are rejected. This is the most important step because it changes the protocol from “trust by transport” to “trust by shared key.”The signing documentation also makes clear that configuration alone is insufficient. Operators must ensure a real key exists, set the correct
MAV_SIGN_CFG mode, and provision the same key to all ground-control and companion systems that need to talk to the vehicle. If the key is missing or all zeros, PX4 can still accept messages regardless of the mode, which is the kind of subtle failure that turns a checkbox into a false sense of security.Hardening checklist
A sensible deployment should treat the advisory as a prompt for a full communications review, not a one-line fix. The recommendations below mirror PX4 and CISA guidance and help close the most obvious doors.- Enable MAVLink signing on all non-USB operational links.
- Provision a 32-byte secret key over USB only.
- Set
MAV_SIGN_CFG=1or2according to your access model. - Restrict MAVLink ports from internet exposure and untrusted networks.
- Segment control networks from business and public networks.
- Audit companion computers and radios for exposed UDP/TCP endpoints.
- Verify rejection of unsigned traffic during acceptance testing.
Deployment Realities
The gap between documented hardening and field deployment is often where security programs struggle. A lot of PX4-based systems are assembled from modular parts: the flight controller, telemetry radio, companion computer, ground-station software, and perhaps a cloud relay or maintenance port. Each component can be secure in isolation while the overall chain remains exposed because of one permissive interface.That reality is especially important for integrators and manufacturers. PX4 explicitly frames signing and link security as an integrator responsibility, which means organizations cannot assume the firmware will protect them from poor deployment choices. The firmware supplies the tools; the system builder decides whether they are actually used.
USB is not a loophole, but it is a policy choice
PX4’s default recommendation allows unsigned USB access when signing is enabled for non-USB links. That can be practical for maintenance, but it also creates a policy boundary that must be controlled physically and operationally. If USB ports remain exposed on deployed equipment, the “maintenance exception” becomes a live risk rather than a controlled one.- Physical access still matters in secure configurations.
- Maintenance ports should not be casually left reachable.
- Companion computers need the same scrutiny as radios.
- Remote support workflows often become hidden attack paths.
Strengths and Opportunities
Despite the severity of the advisory, there are important positives here. PX4 is not ignoring the issue; it already offers the core mitigation, documents the risk clearly, and gives operators concrete steps to harden production systems. That makes this a case where the ecosystem has a viable answer, even if many deployments may not yet have implemented it.- Message signing exists and is built into the platform.
- Documentation is unusually direct about the risks of unsigned traffic.
- USB-only key provisioning helps protect the setup process.
- CISA advisory visibility should accelerate awareness in safety-critical sectors.
- Operational guidance is available for integrators and manufacturers.
- Segmentation and VPN guidance align with established ICS best practices.
- The issue is actionable without waiting for a new protocol redesign.
Risks and Concerns
The biggest concern is that many operators may underestimate how accessible MAVLink links can be. A telemetry radio, a companion computer, or a Wi‑Fi-based console can become a viable attack path if it is left unsigned or exposed beyond the intended trust boundary. Because the exploit does not depend on a software bug in the traditional sense, it may also evade teams that only look for patchable code defects.- Legacy deployments may still rely on default unauthenticated links.
- Fleet inconsistency can leave some vehicles protected and others not.
- Physical maintenance ports can weaken strong network controls.
- Key management mistakes can nullify signing altogether.
- Assumptions about “local only” access may prove false in the field.
- Shell access creates a much larger blast radius than telemetry abuse.
Looking Ahead
The most likely near-term outcome is that operators will audit MAVLink signing status, review exposed endpoints, and update deployment documentation. For serious integrators, this advisory should trigger a checklist review that covers radios, companion computers, USB access, and any UDP or TCP bindings used for ground control. The key point is not just to enable signing once, but to verify that it stays enabled as hardware, software, and mission profiles evolve.Longer term, the industry may need to rethink how much trust is placed in convenience features that were originally designed for development and debugging. As unmanned systems become more connected and more operationally critical, developer defaults are no longer good enough for production. PX4’s documentation already points in the right direction; the challenge now is enforcement, consistency, and ongoing operator discipline.
- Confirm signing is enabled on every non-USB operational link.
- Inventory all MAVLink entry points across vehicles and support systems.
- Review maintenance access policies for physical and remote ports.
- Test rejection of unsigned messages as part of commissioning.
- Reassess network segmentation between mission, business, and public networks.
Source: CISA PX4 Autopilot | CISA
Last edited: