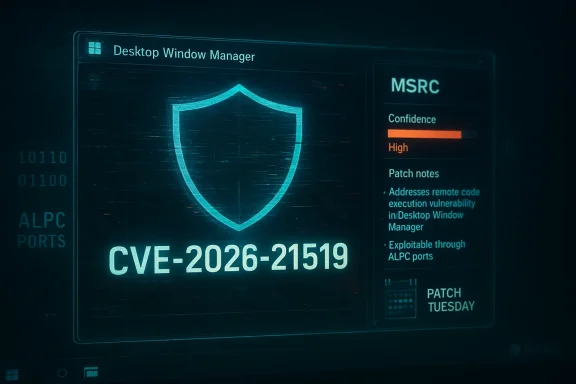
Microsoft’s Security Update Guide shows a Desktop Window Manager (DWM) vulnerability identified as CVE‑2026‑21519, but the public technical details for that specific identifier are limited at the time of writing; the vendor’s built‑in “confidence” metric — which signals how certain Microsoft is about a vulnerability and how much exploit-level detail it will publish — should therefore be treated as the primary triage signal for defenders while independent technical corroboration is sought. ](Security Update Guide - Microsoft Security Response Center))
Desktop Window Manager (DWM) is the Windows compositing host responsible for GPU‑accelerated window composition, visual effects and the exchange of graphical objects between user processes and privileged subsystems. Because DWM runs in a higher‑privilege context and interacts with untrusted inputs (window handles, shared surfaces, ALPC ports), memory‑safety and parsing bugs in DWM have historically produced high‑value local elevation‑of‑privilege (EoP) primitives. That architectural reality makes every DWM CVE worth expedited operational attenttial public write‑ups are sparse.
Microsoft’s Security Update Guide now attaches a short Exploitability / Confidence signal to CVE entries that communicates two separate things: (1) the vendor’s existence confidence that the vulnerability is valid and mapped to a remediation (KB), and (2) the technical‑detail confidence about how much root‑cause, exploit primitive, or PoC material is being published. Use this two‑part signal as your triage lever: act on vendor‑confirmed records immediately for patch mapping and deployment, and escalate telemetry and hunting if technicars publicly.
Security vendors (Rapid7, Check Point, PTSecurity and others) typically publish their own advisories and detection signatures shortly after MSRC publishes KBs and after initial independent analysis. Use their writeups for detection logic but treat MSRC as the source of truth for KB mappings.
End of analysis and guidance.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Desktop Window Manager (DWM) is the Windows compositing host responsible for GPU‑accelerated window composition, visual effects and the exchange of graphical objects between user processes and privileged subsystems. Because DWM runs in a higher‑privilege context and interacts with untrusted inputs (window handles, shared surfaces, ALPC ports), memory‑safety and parsing bugs in DWM have historically produced high‑value local elevation‑of‑privilege (EoP) primitives. That architectural reality makes every DWM CVE worth expedited operational attenttial public write‑ups are sparse.Microsoft’s Security Update Guide now attaches a short Exploitability / Confidence signal to CVE entries that communicates two separate things: (1) the vendor’s existence confidence that the vulnerability is valid and mapped to a remediation (KB), and (2) the technical‑detail confidence about how much root‑cause, exploit primitive, or PoC material is being published. Use this two‑part signal as your triage lever: act on vendor‑confirmed records immediately for patch mapping and deployment, and escalate telemetry and hunting if technicars publicly.
Why the confidence metric matters to defenders
- The metric separates “is this real?” from “how much can we see about it?” — two operationally distinct questions.
- A confirmed entry with low technical detail should still be treated as urgent because vendor acknowledgement usually accompanies shipped fixes and authoritative KB→SKU mappings.
- A low‑confidence or uncorroborated entry means Microsoft is still validating details; in that case use conservative mitigations and monitor for follow‑up disclosure.
- When Microsoft marks a vulnerability as high confidence and indicates active exploitation or abundant technical detail, assume short weaponization timelines measuistinctions are not academic: in January 2026 Microsoft’s Patch Tuesday cycle showed several DWM entries that followed the same disclosure pattern (brief vendor advisory, then third‑party confirmation and rapid community analysis), and security teams that acted on the vendor mapping rather than waiting for PoCs materially reduced their risk exposure.
What we can verify now about CVE‑2026‑21519 (and what we cannot)
- Verifiable: Microsoft’s Security Update Guide mechanism includes an entry for CVE‑2026‑21519 and the platform displays the vendor’s confidence flag on entries. The MSRC entry is the authoritative place to map a CVE to the exact KBs that remediate it. (msrc.microsoft.com)
- Unverified: At the time of this article there is no widely‑published, detailed technical write‑up or public PoC for CVE‑2026‑21519 that we can corroborate across independent vendor advisories or research blogs. Where those writeups exist for other DWM CVEs, they typically appear separately after MSRC publishes KB diffs or after community researchers release analyses. If an analyst claims specifics about 21519 (exploit primitives, exact API surface,tatements as provisional until corroborated by at least one other high‑quality source or the vendor’s patch diffs.
Technical context: why DWM vulnerabilities are high‑value
DWM’s role in Windows creates several attractive exploitation advantages for attackers:- It executes with elevated privileges and touches kernel/driver resources, so userland memory corruption inside DWM can escalate into SYSTEM‑level execution if converted into token replacement or function pointer hijack.
- DWM accepts structured objects and handles from lower‑privilege processes — a convenient input parsing attack surface.
- Anre bug (memory leak) in DWM can defeat ASLR and make subsequent EoP or RCE exploitation far easier; a modest leak is often the crucial first staain.
- In multi‑user environments (VDI, RDP), a compromise of DWM on a single host can affect multiple sessions, increasing potential blast radius.
Evidence, corroboration, and how to read signals
Operational evidence that should change your posture:- Vendor acknowledgement and KB mapping in MSRC — authoritative trigger to remediate. (msrc.microsoft.com)
- Inclusion in CISA’s Known Exploited Vulnerabilities (KEV) or other national advisories — raises urgency and often sets patch deadlines. (Examples: a recent DWM info‑disclosure CVE was added to KEV and carried a federal patch deadline.)
- Independent technical write‑ups, PoC code, or CVE writeups by trusted vendors (Rapid7, Check Point, PTsecurity, etc.) — these provide exploit mechanics and elevate detection urgency//www.rapid7.com/db/vulnerabilities/microsoft-windows-cve-2026-20871/)
Plausible exploitation models (what attackers will try)
Note: these are historically consistent exploit models for DWM defects — not claims about the specific root cause for CVE‑2026‑21519 unless later verified.- Stage 1 — Local foothold: An attacker gains low‑privilege code execution on a host (phishing, malicious document, or container escape).
- Stage 2 — Interact with DWM surface: The attacker crafts inputs (window messages, composition buffers, ALPC interactions) that DWM will parse in privileged context.
- Stage 3 — Memory corruption → primitive: A heap overflow or UAF turns into an arbitrary read/write primitive through heap sion.
- Stage 4 — Escalation: Use the write primitive to overwrite a token pointer, vtable, or function pointer to execute code as SYSTEM or steal credentials from higher-privileged processes.
- Stage 5 — Post‑exploit actions: Credential theft, disabling of endpoint defenses, lateral move domain compromise.
Practical, prioritized actions for defenders
Below is a conservative, operational playbook you can apply immediately. Treat it as a blueprint to adapt to your organization’s risk tolerance and patch windows.1. Triage and inventory (first hour)
- Query Microsoft’s Security Update Guide for CVE‑2026‑21519 and extract every KB mapped to your supported SKUs; the MSRC entry is authoritative. (msrc.microsoft.com)
- Identify high‑vntrollers, admin workstations, jump boxes, RDP/VDI hosts, and systems hosting secrets or identity services.
- Tag and prioritize these hosts for immediate patching.
2. Short‑term mitigations (day 0–3)
- Apply vendor KBs to high‑priority hosts first; use test rings for compatibility checks (GPU drivers and DWM patches can interact poorly with OEM drivers).
- If patching is temporarily impossible, implement compensating controls:
- Enforce application allow‑er).
- Remove local administrative rights where possible.
- Block unnecessary outbound SMB/ALPC exposure and restrict local untrusted code execution policies.
- Harden remote access and reduce the number of users with interactive sessions on high‑privilege hosts.
- Rotate high‑value credentials if you suspect in‑the‑wild exploitation.
3. Detection and hunting (hours → weeks)or:
- Unexpected SYSTEM process spawns initiated by low‑privilege processes.
- DWM/dwmcore crashes and abnormal memory access patterns.
- ALPC port activity from untrusted processes (where telemetry is available).
- Preserve memory dumps from affected hosts with DWM crashes for vendor triage and forensic analysis.
4. Patch validation and rollout (days → weeks)
- Test KBs in representative canary rings (include VM images with different GPU drivers and VDI clients).
- Stage deployment to prioritized rings, monitor for regressions (display problems are a common signal), and maintain rollback plans.
- Once validated, push to production-wide rings and confirm via SIEM/CMDB that KBs are present on all targeted hosts.
5. Post‑disclosure review (weeks → monthsm exercises simulating chained attacks that use DWM info leaks or EoP primitives to validate detection and response effectiveness.
- Rework high‑risk document preview and in‑process rendering pipelines to render untrusted content out‑of‑process or in sandboxes where feasible.
Example KB mapping and vendor confirmation (how to use MSRC)
When MSRC publishes a DWM CVE, the entry is the canonical mapping to KBs that fix the issue for each Windows build. For example, recent DWM advisories from January 2026 were mapped into specific cumulative updates and KB numbers — those KBs are what you must schedule and verify in your update tooling. Do not rely solely on third‑party aggregators for critical KB→SKU mapping; confirm in MSRC or the Microsoft Update Catalog before deployment.Assessing exploitation likelihood and operational urgency
Ask these five pragmatic questions to set your internal SLA for CVE‑2026‑21519:- Has Microsoft marked the CVE as confirmed in the MSRC update guide? If yes, elevate to emergency SLA. (msrc.microsoft.com)
- Is the CVE included in national advisories (CISA KEV, CERTs) with patch deadlines? If yes, fast‑track federal/critical hosts.
- Have reputable vendors or researchers published a PoC or detailed analysis? If yes, treat detection and blocking as urgent. ([rapid7.com](Rapid7 the vulnerability allow remote or local-only exploitation? DWM items are commonly local; map that into your risk model for exposed endpoints.
- Can you short‑circuit the attack chain (e.g., disable risB egress, enforce least privilege) while patching? If yes, use those mitigations immediately.
Risks and secondary effects to plan for
- Display and driver regressions: DWM patches may interact with OEM GPU drivers and remote desktop graphics stacks; test in canaries before wide deployment.
- False comfort from moderate CVSS: Even mid‑range CVSS numbers on DWM items hide the fact that info leaks and local EoPs are valuable chaining primitives. Treat them as high priority.
- Public PoC shockwaves: When PoC or patch diffs appear, expect an immediate uptick in scanning and exploit attempts; pre‑position detection rules and signatures.
How vendors and national authorities are reacting (context)
Microsoft’s January 2026 Patch Tuesday cycle included multiple DWM fixes; independent vendors and advisories mirrored the operational profile and urged rapid patching. Some DWM items were confirmed as being exploited in the wild and were added to national vulnerability lists that impose patch timelines. That pattern — vendor entry, patch mapping, vendor or government urging — is the practical flow defenders should monitor for CVE‑2026‑21519.Security vendors (Rapid7, Check Point, PTSecurity and others) typically publish their own advisories and detection signatures shortly after MSRC publishes KBs and after initial independent analysis. Use their writeups for detection logic but treat MSRC as the source of truth for KB mappings.
Forensics and incident response pointers
- If you suspect exploitation:
- Preserve full memory dumps and system logs immediately from suspected hosts.
- Capture DWM crash dumps and ALPC‑related traces (if your tooling supports it).
- Isolate suspected hosts from networks and rotate credentials for accounts that may have been exposed.
- Share anonymized telemetry with vendor incident response only under appropriate NDAs to help accelerate vendor patch diff analysis.
- Prioritize forensic preservation over hasty reboots when feasible; volatile memory may contain the artifacts needed to prove exploitation.
Communication checklist for IT leadership
- Notify stakeholders that MSRC lists CVE‑2026‑21519 and that the vendor’s confidence signal must be treated as the primary triage lever. (msrc.microsoft.com)
- Declare an initial patching window for jump hosts and admin workstations (24–72 hours depending on risk appetite).
- Instruct operations to test KBs in a validated canary ring before broad deployment.
- Have the SOC stand up hunts for DWus local privilege escalation behavior.
- Prepare communication templates to end users for scheduled reboots and service windows that are short and factual.
Final assessment and recommendations
- Treat CVE‑2026‑21519 as a vendor‑acknowledged DWM vulnerability until proven otherwise; MSRC confirmation + KB mapping is the operational trigger to remediate at scale. Confirm the exact KB numbers for each Windows build in your estate before you close remediation tickets. (msrc.microsoft.com)
- Apply the most consposture: patch high‑value hosts first, apply compensating controls on other systems, and escalate detection/hunting ahead of or concurrent with deployment.
- Assume DWM flaws are chainable: even information‑disclosure weaknesses materially increase the risk of full compromise when combined with foothold techniques. Prioritize detection capability and credential hygiene as immediate defenses.
- If you see third‑party claims describing exploit mechanics for CVE‑2026‑21519, insist on multi‑sondependent vendor write‑up, PoC hosted on a verified research channel, or Microsoft patch diffs) before operationalizing blocking rules or public advisories. Flag any unverified claims internally and proceed conservatively.
End of analysis and guidance.
Source: MSRC Security Update Guide - Microsoft Security Response Center