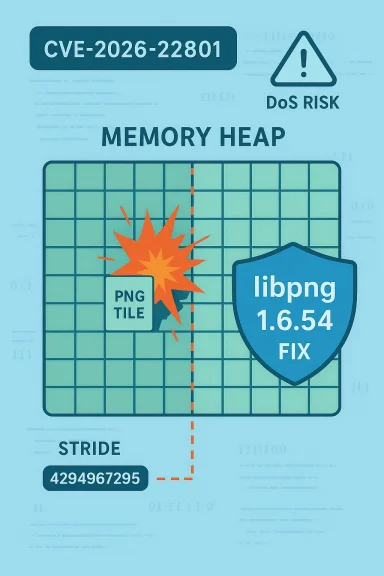
A recently disclosed flaw in the libpng library — tracked as CVE-2026-22801 — creates an integer truncation in libpng's simplified write APIs that can lead to a heap buffer over‑read and consequent denial‑of‑service or information disclosure when applications call png_write_image_16bit() or png_write_image_8bit() with malformed stride values. The bug affects libpng 1.6.26 through 1.6.53 and was fixed in libpng 1.6.54; downstream distributions and vendors have issued updates and advisories.
Libpng is the canonical C reference library for reading, writing, and manipulating PNG images; it is embedded in countless desktop applications, server software, image‑processing pipelines, and embedded devices. A vulnerability that lives inside the library therefore translates into a broad supply‑chain risk: any consumer of the library — from a web server that accepts user uploads to a photo editing app embedded in a device — can inherit the defect. Multiple security trackers and vendor advisories describe CVE‑2026‑22801 as a medium‑severity out‑of‑bounds read caused by integer truncation in the simplified write APIs.
The specific triggering condition is unusual but realistic: the library mishandles row stride values when they are negative (used for bottom‑up image layouts) or larger than 65535 bytes. Under those conditions a truncation introduced in libpng 1.6.26 causes code paths to read beyond allocated buffers, producing a heap buffer over‑read. The maintainers released libpng 1.6.54 on January 12, 2026 with a targeted fix.
Flag for readers: if you discover crash‑triggering PNGs against your services, treat them as high‑priority incidents — attackers can weaponize crash loops to sustain outages, induce expensive restarts, or combine with other bugs to escalate impact.
However, risk remains material for several reasons:
CVE‑2026‑22801 is a timely reminder that convenience APIs and machine‑era legacy assumptions (like casts for 16‑bit platforms) can become security liabilities. The fix is available; the remaining challenge is operational: finding every linked copy of libpng in complex supply chains and making sure it is replaced, container images are rebuilt, and embedded devices receive vendor fixes or mitigations. For teams that process user images at scale, this is an urgent patch‑and‑harden exercise — not a theoretical concern.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Libpng is the canonical C reference library for reading, writing, and manipulating PNG images; it is embedded in countless desktop applications, server software, image‑processing pipelines, and embedded devices. A vulnerability that lives inside the library therefore translates into a broad supply‑chain risk: any consumer of the library — from a web server that accepts user uploads to a photo editing app embedded in a device — can inherit the defect. Multiple security trackers and vendor advisories describe CVE‑2026‑22801 as a medium‑severity out‑of‑bounds read caused by integer truncation in the simplified write APIs.The specific triggering condition is unusual but realistic: the library mishandles row stride values when they are negative (used for bottom‑up image layouts) or larger than 65535 bytes. Under those conditions a truncation introduced in libpng 1.6.26 causes code paths to read beyond allocated buffers, producing a heap buffer over‑read. The maintainers released libpng 1.6.54 on January 12, 2026 with a targeted fix.
What exactly is wrong? A technical breakdown
The vulnerable APIs and conditions
- The affected functions are png_write_image_16bit() and png_write_image_8bit(), the simplified "write" APIs that let callers hand the implementation a single buffer and a row stride. These helper APIs are convenient but have always required correct stride handling by callers. The integer truncation issue is inside libpng's stride handling logic.
- Two stride-related conditions cause the problem:
- A negative row stride (commonly used to represent bottom‑up row order).
- A row stride value that exceeds 65535 (0xFFFF), which becomes truncated when cast into a 16‑bit quantity in older code paths.
Root cause: casts introduced for 16‑bit systems
The defect was introduced in libpng 1.6.26 (October 2016) as a side effect of casts added to silence compiler warnings on 16‑bit platforms. Those casts truncated a stride (and related counters) into a narrower integer type at a point in the code where the value was still relied upon as a full-width signed quantity. The truncation makes later buffer‑length checks inconsistent with subsequent memory accesses, permitting reads past an allocated heap buffer. This is classic integer‑truncation / sign‑mismatch territory that turns bounds-checks into illusions.Consequences of a heap buffer over‑read
A heap buffer over‑read typically causes one or more of the following:- Immediate crash of the process using libpng (denial‑of‑service).
- Reading and potentially leaking adjacent heap bytes into output streams (limited information disclosure).
- Triggering undefined behavior in memory‑safety mitigations or causing aborts under hardened allocators.
Affected versions, fixes, and vendor guidance
- Affected libpng versions: 1.6.26 through 1.6.53. The error was introduced in 1.6.26.
- Fixed in: libpng 1.6.54, released January 12, 2026. Change logs and the official libpng news entry explicitly list CVE‑2026‑22801 as fixed in 1.6.54.
- Downstream advisories: Major Linux distributions and security trackers (Ubuntu, Fedora, SUSE, others) have classified the issue as moderate/medium severity and published patches or packaged updates that track libpng 1.6.54 or higher. Organizations should consult their vendor‑specific security notices and apply distro updates.
How exploitable is CVE‑2026‑22801?
Attack vector and complexity
- Several trackers characterize the attack vector as local (AV:L) because exploitation requires a calling application to pass an invalid stride value into the simplified write API. In many real‑world deployments the calling application is the same process that parses or constructs user‑supplied PNG data; therefore, the attacker only needs to supply a specially crafted PNG file to an application that exposes a path to the simplified API. This means remote exploitation is plausible in contexts where an application will open or write PNG content supplied by untrusted users (web upload endpoints, image conversion microservices, desktop apps that automatically import images), so the practical attack surface is broader than the "local" label might imply.
- Attack complexity is low once the triggering conditions are understood, but the trigger requires either a negative stride or a stride > 65535; not all callers use or expose such stride values. In effect, exploitability depends heavily on how downstream applications use the simplified API.
Real‑world exploit observations
At the time of disclosure and initial vendor patches there were no widely observed, confirmed exploits in the wild specifically tied to CVE‑2026‑22801. That does not mean PoCs (proofs‑of‑concept) will not appear, and the presence of many prior libpng bugs exploited in targeted attacks means defenders should treat the window between disclosure and patching as high‑risk. Trackers continue to flag the issue for detection and incident response efforts.Flag for readers: if you discover crash‑triggering PNGs against your services, treat them as high‑priority incidents — attackers can weaponize crash loops to sustain outages, induce expensive restarts, or combine with other bugs to escalate impact.
Where does this matter most? Downstream risks and high‑priority targets
Certain environments need immediate attention:- Public image processing services, image upload endpoints, and content management systems that accept user images without strict pre‑validation. These are natural attack surfaces because attackers can deliver arbitrary PNG files.
- Server‑side renderers and thumbnail generators used in mail servers, chat systems, and content aggregation pipelines. Those services often run batch image processing and may not be sandboxed per upload, amplifying the damage of repeated exploit attempts.
- Desktop/image editing applications and document viewers that automatically open or preview images from untrusted sources. A crafted PNG could crash the host application and potentially leak memory contents.
- Embedded devices and appliances that include libpng in their firmware: camera firmware, IoT hub image processors, print devices, and networked appliances that accept image data may be difficult to patch quickly, increasing persistent risk.
Detection, hunting, and triage guidance
Incident triage signals
- Crashes in processes that touch image‑writing code (especially crashes during image export or conversion) should be investigated for libpng involvement. Look for stack traces referencing png_write_image_8bit, png_write_image_16bit, or png_write_row/png_write_rows call sites. Vendor packages and debuginfo may be required to resolve symbols.
- Unusual memory reads or process aborts triggered by specific PNGs: a repeatable crash against a particular file is a strong indicator of exploitation attempts against image parsing/writing code. Capture the file and treat it as evidence.
Hunting and signatures
- Log and fingerprint image‑processing code paths on end services. If you have instrumentation (uWSGI, application logs, crash dump capture), correlate image ingestion events with crashes to find suspect inputs.
- Use runtime instrumentation or sanitizers (ASAN/LSAN/UBSAN) in a safe test environment to reproduce and confirm heap over‑reads. Fuzzing frameworks and OSS‑Fuzz artifacts have been used by maintainers to find related issues; enabling fuzzing or production‑like fuzzing harnesses in CI helps discover similar patterns.
- Where signatures are available from content security solutions, flag PNGs with metadata/structures intended to produce extreme row strides or malformed IHDR/IDAT chunk arrangements. Because the trigger involves stride handling rather than strictly malformed PNG structure, simple file‑format validators may not detect the condition — you must observe the resulting stride used by the application.
Mitigations, workarounds, and short‑term controls
When immediate patching is not possible, implement layered mitigations:- Update: the single best action is to upgrade libpng to 1.6.54 or later as soon as feasible and rebuild/redeploy all artifacts that link to libpng. This is the official remediation.
- Sandbox image processors: move image conversion and thumbnail generation into isolated processes or containers with resource limits and restart‑protection. Even if crashes occur, isolation reduces blast radius.
- Pre‑validate inputs: reject PNG uploads that declare exceedingly large row strides in metadata or whose dimensions would imply row lengths above safe thresholds for your application. Note: this requires careful handling so you do not reject legitimate large images indiscriminately.
- Disable simplified write API: if your codebase directly calls the simplified png_write*image** helpers and you cannot update the library quickly, consider switching to lower‑level, more explicit write paths that perform their own robust stride validation before invoking libpng internals. This is a developer‑level mitigation for controlled codebases.
- Rate limit and monitor: apply upload rate limits and anomaly detection for image submissions to public endpoints so an attacker cannot easily drive repeated crashes. Combined with sandboxing, this makes sustained DoS attacks harder.
- Backport patches: for long‑lived vendor packages, check whether your Linux distribution or appliance vendor provides a backported fix; many maintainers release vendor patches that keep ABI compatibility while correcting the bug. Apply these vendor updates per your patch management policy.
Developer guidance: code fixes and safe API usage
If you maintain code that calls libpng's simplified write API, take these steps:- Inspect all call sites of png_write_image_8bit and png_write_image_16bit.
- Ensure that row stride values are validated before passing them to libpng:
- Reject or clamp negative strides unless your code explicitly implements bottom‑up layouts and validates memory layout.
- Reject or carefully validate strides that would exceed sensible application limits (e.g., > 65535 may legitimately appear for very wide images, but treat such cases as suspicious and validate buffer sizes).
- Prefer using explicit row‑by‑row write loops in performance‑sensitive or safety‑critical code; explicit loops make validation trivial and reduce reliance on fragile helper semantics.
- Add defensive checks: verify that the buffer length (rows * stride) matches or exceeds the expected image size before passing pointers to libpng.
- Run test harnesses using sanitizers and fuzzers to confirm that altered inputs do not cause reads beyond allocated memory.
Patch management: how to prioritize and roll out updates
- Triage your inventory: find all packages and binaries that ship libpng, including statically linked binaries and containers. Search container images, language runtime packages, and vendor firmware repositories for libpng 1.6.x artifacts. Use SBOMs if available.
- Prioritize externally‑facing services that process untrusted images, and internal high‑availability services (thumbnailing queues, mail servers, ingestion pipelines). These should be patched first because the impact of an exploit is immediate and potentially repeatable.
- Test updates in staging: for services where image behavior is critical (e.g., color management, custom row ordering), exercise regression tests. The fix is targeted, but any change in image write behavior deserves a smoke test on representative images.
- Deploy with canary/rolling strategies: use canary deployments and monitor crash rates and error logs during rollout so you can detect regressions quickly. Maintain a rollback plan.
Why this class of bug keeps happening — and what defenders should learn
CVE‑2026‑22801 is structurally familiar: integer narrowing/casting mistakes, especially introduced to silence compiler warnings on odd platforms, have historically created off‑by‑one, truncation, and sign‑mismatch vulnerabilities. The lesson is persistent:- Casts that change the numeric width or sign of values used in bounds checking are dangerous; they need explicit review and test coverage.
- Simplified convenience APIs that accept compact inputs (single buffer + stride) are easy to misuse; they demand defensive validation both in libraries and in application code.
- Supply‑chain hygiene (SBOMs, recording which binaries statically link libpng) reduces the uncertainty about where vulnerable code lives.
Community response and disclosure timeline
- The libpng project and its maintainer(s) published a rapid remediation in libpng 1.6.54 on January 12, 2026, fixing CVE‑2026‑22801 alongside another simplified‑API regression (CVE‑2026‑22695). Release notes and the public announcement came through the libpng site, SourceForge release pages, and the maintainer's messages to oss‑security.
- Vendor ecosystems (Ubuntu, Fedora, SUSE, others) moved to package and distribute the fixed libpng quickly; defenders should track vendor advisories for backports and rebuild schedules.
- Public trackers and vulnerability databases (NVD, OpenCVE, Rapid7, SUSE advisories) catalog the CVE and provide CVSS and remediation guidance. CVSS estimates vary slightly across CNAs and trackers, but the consensus places the issue in the medium severity band (CVSS ~6.1–6.8 depending on assumptions about scope and privileges).
Recommended immediate checklist for sysadmins and developers
- Inventory: identify all hosts, containers, and artifacts that include libpng 1.6.26–1.6.53.
- Patch: upgrade to libpng 1.6.54 or later on all systems and rebuild static binaries with the updated library where necessary. Apply vendor backports if your distro provides them.
- Harden: sandbox image processing, rate‑limit uploads, and add input validation for image dimensions and stride values.
- Monitor: watch crash logs and instrument image ingestion endpoints for anomalies; capture suspect PNG files for forensic analysis.
- Test: run CI tests with sanitizers and consider targeted fuzzing for image code paths to detect regressions and other latent bugs.
Final analysis: strengths, risks, and the path forward
The libpng maintainers addressed CVE‑2026‑22801 promptly with a targeted fix in 1.6.54; the disclosure window was handled in line with modern coordinated‑disclosure norms and vendors have rolled out updates. That rapid response is a major strength: the upstream project and Linux distributors moved quickly to protect users.However, risk remains material for several reasons:
- The attack surface is broad because libpng is ubiquitous; unpatched, externally‑facing services that accept images are easy targets for a denial‑of‑service campaign.
- Static linking, container images, and vendor firmware can keep vulnerable copies of libpng alive long after upstream releases patches. These artifacts require active inventory and rebuilds.
- The underlying class of bug — integer truncation and unsafe casts — is predictable and repeatable. Even with this fix, defenders should expect similar issues in related image‑handling code unless development teams systematically adopt narrower, machine‑checked invariants and fuzzing/sanitizer-driven QA.
CVE‑2026‑22801 is a timely reminder that convenience APIs and machine‑era legacy assumptions (like casts for 16‑bit platforms) can become security liabilities. The fix is available; the remaining challenge is operational: finding every linked copy of libpng in complex supply chains and making sure it is replaced, container images are rebuilt, and embedded devices receive vendor fixes or mitigations. For teams that process user images at scale, this is an urgent patch‑and‑harden exercise — not a theoretical concern.
Source: MSRC Security Update Guide - Microsoft Security Response Center