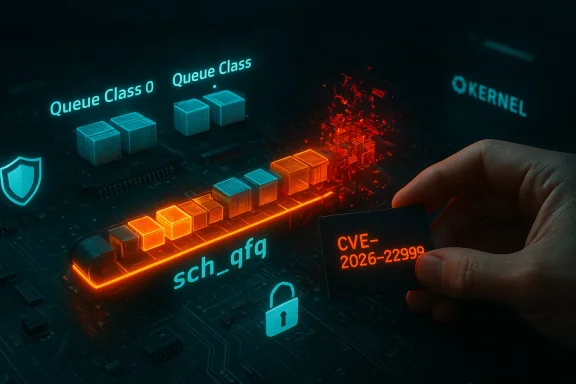
A subtle memory-management mistake in the Linux kernel’s Quick Fair Queueing (QFQ) packet scheduler has been cataloged as CVE-2026-22999 and fixed upstream: an error path in qfq_change_class() can free the existing class and its qdisc when it should not, producing a use‑after‑free (UAF) that risks kernel instability and, in specific circumstances, escalation from local crash to more serious compromise.
QFQ (Quick Fair Queueing) is a packet-scheduling qdisc used to fairly allocate outbound bandwidth across flows. It lives in the kernel networking scheduler under net/sched as sch_qfq and is typically used in environments that require fine-grained bandwidth control and fairness, such as routers, software network appliances, and some cloud or telco images.
The newly assigned CVE-2026-22999 addresses a narrow but real logic error in qfq_change_class(), the routine that updates an existing QFQ class or replaces it with a newly allocated class and accompanying qdisc object. The upstream patch alters the error-handling path: the existing class and class->qdisc must only be freed when a new class and a new qdisc were successfully allocated — freeing them otherwise risks dereferencing memory still in use elsewhere.
The upstream fix is small and surgical: guard the cleanup so that qdisc_put(cl->qdisc) and kfree(cl) only run if a new class/qdisc were actually created. In other words, do not free the "existing" class in the failure case. This is a minimal behavioral change that closes the UAF without altering normal successful-class-change semantics.
However, kernel UAFs are inherently dangerous: while many UAFs lead only to denial-of-service (kernel oops/panic), others can be turned into arbitrary memory corruption primitives by skilled exploit developers. The precise exploitability depends on kernel configuration, SMAP/SMEP availability, KASLR entropy, presence of mitigations (stack canaries, hardened memory allocators), and whether an attacker can perform repeated, deterministic operations to groom heap layout. Public telemetry (low EPSS/attack prediction published by community trackers) suggests active exploitation is not currently widespread, but that does not reduce the need for timely patching.
Note for Windows users and cloud customers: when a vendor’s product page or vendor-specific CVE entry appears missing (for instance, the Microsoft MSRC page the user provided returned no content at the time of checking), it is often because the vendor is still working inventory or because the product attestation is being staged. Microsoft and other large vendors sometimes publish product-scoped attestations that say “Product X includes the upstream component and is therefore potentially affected”; these are inventory statements, not technical analyses of exploitability. Treat such attestations as an authoritative inventory signal for the named product, but not as exhaustive coverage of all artifacts the vendor ships. If a vendor’s page is blank or missing, watch their advisory channels and VEX/CSAF feeds for updates.
Action checklist:
Conclusion: The sch_qfq fix for CVE-2026-22999 is a case study in why careful error-path resource management matters at the kernel level. The patch is straightforward, but the implications of leaving a UAF in a scheduler are disproportionate to the size of the change. Apply available updates, harden who can manipulate qdiscs, and monitor kernel telemetry to stay ahead of potential misuse.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
QFQ (Quick Fair Queueing) is a packet-scheduling qdisc used to fairly allocate outbound bandwidth across flows. It lives in the kernel networking scheduler under net/sched as sch_qfq and is typically used in environments that require fine-grained bandwidth control and fairness, such as routers, software network appliances, and some cloud or telco images.The newly assigned CVE-2026-22999 addresses a narrow but real logic error in qfq_change_class(), the routine that updates an existing QFQ class or replaces it with a newly allocated class and accompanying qdisc object. The upstream patch alters the error-handling path: the existing class and class->qdisc must only be freed when a new class and a new qdisc were successfully allocated — freeing them otherwise risks dereferencing memory still in use elsewhere.
What the patch changes (technical summary)
The bug, in plain terms
In the original code, the error path in qfq_change_class() could unconditionally call the routine that drops the qdisc reference and free the class object (qdisc_put and kfree) even when the attempt to allocate a replacement class/qdisc had failed. That sequence opens a window where other kernel code still holds references or expects the class to remain valid — a textbook recipe for a UAF.The upstream fix is small and surgical: guard the cleanup so that qdisc_put(cl->qdisc) and kfree(cl) only run if a new class/qdisc were actually created. In other words, do not free the "existing" class in the failure case. This is a minimal behavioral change that closes the UAF without altering normal successful-class-change semantics.
Where the fix landed
The change was submitted and discussed on the kernel networks lists, reviewed and signed off by maintainers, and merged into the appropriate stable trees and long-term kernels. Multiple stable-queue releases include the patch, and downstream distributions have begun tracking it in their kernel updates. The kernel patch metadata and mailing-list discussion identify the patch author and trace the fix’s provenance through the stable and longterm queues.Affected versions and distribution responses
- Upstream CVE metadata and NVD entries indicate the fix and list affected kernel trees; NVD’s record and OSV mirror the kernel commit message and point to the stable patch references. Distributions have picked up the CVE and are working it into their advisories.
- Several downstream trackers and vendor bug pages have registered the CVE. Red Hat’s bugzilla has an active bug entry reflecting the CVE and tracking remedial action. Debian and SUSE trackers also list the issue with their internal severity assessments. These entries confirm that the problem is in the upstream kernel and that distro kernels that include the vulnerable sch_qfq code will need either the upstream patch or a distribution backport.
- Long-term and stable kernel trees have been updated; various package release logs show the patch included in recent point releases for the affected series. Administrators running vendor-supplied kernels should expect vendor advisories and should apply distribution updates as they are published.
Exploitability and real-world risk
How easy is it to exploit?
This defect is a memory-safety error located in a qdisc implementation. The consensus in the public records is that exploitation would require local access and specific interaction with the QFQ qdisc code path (for example, privileged use of traffic-control utilities or netlink interfaces that trigger class-change operations). That places the primary attack vector squarely in the local/privileged-or-privileged-adjacent category rather than a remote, unauthenticated network vector. NVD’s initial scoring reflects a local attack vector.However, kernel UAFs are inherently dangerous: while many UAFs lead only to denial-of-service (kernel oops/panic), others can be turned into arbitrary memory corruption primitives by skilled exploit developers. The precise exploitability depends on kernel configuration, SMAP/SMEP availability, KASLR entropy, presence of mitigations (stack canaries, hardened memory allocators), and whether an attacker can perform repeated, deterministic operations to groom heap layout. Public telemetry (low EPSS/attack prediction published by community trackers) suggests active exploitation is not currently widespread, but that does not reduce the need for timely patching.
Divergent severity assessments
Different organizations have published differing severity ratings for the issue. Some commercial scanners and trackers labeled the bulletin with high-to-critical scores, while NVD’s published CVSS vector indicates a lower, medium-impact assessment tied to local exploitability and primary availability impact. This discrepancy stems from variable assumptions about potential privilege escalation paths, the presence of dispatchable attack surfaces on a given host, and how vendors map "kernel memory corruption" into severity. Administrators should treat this as a kernel memory-safety bug with real risk and prioritize remediation according to their threat model, not any single numeric score.Practical impact for WindowsForum readers (enterprises, cloud, appliance vendors)
- Systems that do not run QFQ at all are not directly affected. QFQ is a qdisc that must be configured to be invoked; most desktop or basic server installs do not enable it by default. That said, many network appliances, router images, container host kernels, and cloud guest or host kernels can include QFQ — especially if kernel builds include a broad set of schedulers. Administrators should confirm whether any of their images or hosts have QFQ enabled.
- In multi-tenant, containerized, or shared-host environments, a local attacker who gains the ability to issue tc/netlink commands could, under favorable conditions, trigger the vulnerable code and cause a kernel crash or attempt further exploitationary that separates tenants from host or elevating controls on who can manipulate queueing disciplines reduces risk materially.
- Network infrastructure appliances and embedded devices are particularly relevant: vendors shipping custom kernels or older (LTS) kernels may not have received this upstream fix unless they track or backport upstream changes. Those vendors must evaluate and ship updates quickly; administrators should watch vendor advisories. Vendor attestations (for example, those from large cloud providers) can be product-scoped and do not always indicate universal coverage—treat attestations as guidance, not a guarantee that a product is unaffected.
Detection, monitoring, and short-term mitigations
Detection and log signals
- Look for kernel oops or panic messages tied to net/sched, sch_qfq, or explicit KASAN/KMSAN traces in dmesg, journald, or kernel crash dumps. These diagnostics often point to use-after-free or invalid memory accesses in the qfq path.
- Audit and log netlink/tc invocations on infrastructure hosts: unusual or repeated netlink commands that create/modify qdiscs and classes should be flagged. If your environment logs who invoked tc via sudo or automation, review that audit trail.
- Leverage existing host intrusion detection that tracks kernel anomalies. Some organizations also deploy KASAN-enabled test images to detect memory-safety regressions in pre-production. The upstream report indicates the bug was found via sanitizer-assisted tools like syzbot, which demonstrates the effectiveness of such tooling for discovery.
Short-term mitigations (if you cannot patch immediately)
- Remove or disable QFQ usage where feasible: if your configuration does not require QFQ, delete QFQ qdiscs from affected hosts (for example, remove any tc qdisc root/child entries using qfq). This is a configuration-level mitigation, not a kernel hardening step.
- Restrict who can manage qdiscs: ensure only fully trusted administrators or automation run tc/netlink operations. Enforce least-privilege for users and containers; drop CAP_NET_ADMIN for untrusted containers and service accounts that do not need network configuration privileges.
- Isolate hosts that provide tc/netlink to untrusted users. In cloud or multi-tenant platforms, review container runtime and host configurations to prevent tenant-level operations from reaching host-level qdisc controls.
Recommended remediation steps
- Patch: apply vendor-supplied kernel updates that include the upstream fix. Watch your distribution’s security advisory list and install the kernel update in test, then prod. If a vendor has not yet published an advisory, track the vendor bugzilla and distro trackers referenced in the upstream metadata and apply backported fixes when available.
- Reboot during maintenance windows as appropriate: kernel updates typically require a reboot unless you use live kernel patching solutions; plan accordingly.
- For vendors and operators who maintain custom kernels: merge the upstream patch into your kernel tree and test it under representative workloads. The fix is small, but regression testing for schedulers and networking throughput is prudent.
- Audit qdisc usage: enumerate qdiscs across build images and hosts and identify whether QFQ is actively used. Remove or disable QFQ where it is unnecessary.
- Monitor for indicators of compromise and for kernel instability: set up alerting on kernel oops messages, and maintain crash-dump capture for forensic analysis if a host exhibits unexplained reboots.
Vendor posture and public disclosure behavior
Upstream kernel trees and public mailings show the fix was authored and submitted to the netdev/kernel maintainers and then merged into stable branches; public vulnerability databases (NVD, OSV) have recorded CVE-2026-22999 and point to the kernel commits and mailing-list entries. Distributions are following the usual cadence of converting upstream patches into distribution-levelorts.Note for Windows users and cloud customers: when a vendor’s product page or vendor-specific CVE entry appears missing (for instance, the Microsoft MSRC page the user provided returned no content at the time of checking), it is often because the vendor is still working inventory or because the product attestation is being staged. Microsoft and other large vendors sometimes publish product-scoped attestations that say “Product X includes the upstream component and is therefore potentially affected”; these are inventory statements, not technical analyses of exploitability. Treat such attestations as an authoritative inventory signal for the named product, but not as exhaustive coverage of all artifacts the vendor ships. If a vendor’s page is blank or missing, watch their advisory channels and VEX/CSAF feeds for updates.
Why this matters: risk analysis for defenders
- Memory-safety bugs in the kernel are high-impact by design: the kernel controls the entire machine. Even if a particular UAF initially appears to produce only crashes, dedicated exploit developers can sometimes weaponize such bugs into local privilege escalation. The small code delta here reduces the attack surface but does not remove the underlying classification: kernel UAFs are a class of bug defenders treat as high priority.
- Attack surface is constrained by the requirement to interact with QFQ: hosts which do not expose network configuration operations to untrusted users are less exposed. Nevertheless, in modern orchestration and container platforms, misconfigurations or elevated container capabilities (for example, CAP_NET_ADMIN) create pathways for attack that operators sometimes overlook.
- The practical uptick in risk for most organizations is therefore proportional to two factors: whether QFQ is present/used in deployed kernels, and whether untrusted principals can interact with kernel qdisc configuration. Address both to materially reduce risk.
Frequently asked operational questions
Is this a remote network exploit?
No. The vulnerability requires local operations that touch the qfq_change_class() code path; it is not a blind remote code-execution vector that can be triggered purely by sending packets to a remote host. Treat it as a local kernel memory-safety bug.If I run default desktop kernels, am I likely to be affected?
Most desktop and standard server installations do not enable QFQ by default. However, many distributions build the qdisc into their kernels. The presence of the code does not equal usage; the qdisc must be configured to be exercised. Still, keep systems patched per your vendor’s guidance.What if my vendor hasn’t issued an advisory yet?
If your vendor hasn’t published an advisory, use these steps:- Confirm whether your kernel includes sch_qfq.
- If it does, prioritize patching once the vendor releases an update or integrate the upstream patch into your own kernel rebuilds after testing.
- As an immediate mitigation, remove or avoid configuring QFQ and restrict netlink/tc operations to trusted admins.
Final analysis and takeaways
CVE-2026-22999 is a compact, repairable bug: the upstream fix is small, well-reasoned, and has been merged into stable trees. The risk profile is typical for kernel scheduling UAFs — important for defenders, especially in multi-tenant or privileged-container contexts, but not a broad remote compromise vector. Administrators should treat this as a high-priority patching item in environments that use QFQ or expose netlink/tc controls to untrusted actors.Action checklist:
- Inventory: find hosts and images with sch_qfq present or QFQ configured.
- Patch: apply vendor kernel updates or backport the upstream patch in your kernel lifecycle pipeline.
- Restrict: limit netlink/tc capabilities to trusted principals (drop CAP_NET_ADMIN for untrusted containers).
- Monitor: watch kernel logs for oops/KASAN indications and audit tc/netlink activity.
Conclusion: The sch_qfq fix for CVE-2026-22999 is a case study in why careful error-path resource management matters at the kernel level. The patch is straightforward, but the implications of leaving a UAF in a scheduler are disproportionate to the size of the change. Apply available updates, harden who can manipulate qdiscs, and monitor kernel telemetry to stay ahead of potential misuse.
Source: MSRC Security Update Guide - Microsoft Security Response Center