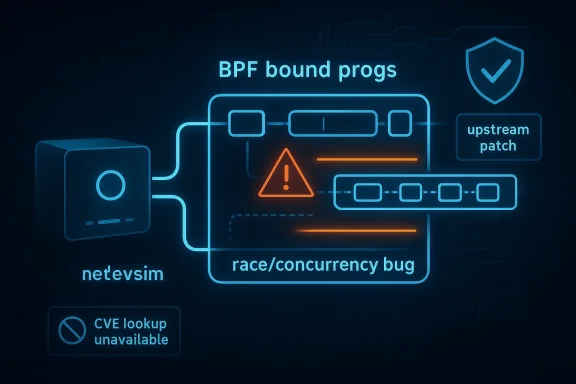
In the Linux kernel, CVE-2026-23126 is a reminder that even a driver meant for simulation can still expose real stability risk when its internal bookkeeping is touched from multiple execution paths at once. The flaw sits in netdevsim, the kernel’s software network-device emulator, where a race in operations on the bpf_bound_progs list can corrupt list state and destabilize the system. Microsoft’s security entry points to the upstream kernel fix, and the public advisories now frame the issue as a race-condition bug rather than a classic memory-safety bug, which matters because concurrency failures often look harmless right up until they are not. (nvd.nist.gov)
Background — full context
The netdevsim driver occupies a peculiar but important place in the Linux kernel ecosystem. It is not hardware, yet it behaves enough like hardware to let kernel engineers exercise networking paths, devlink resources, traps, and BPF-related workflows without needing a physical NIC. That makes it valuable for development, testing, and regression validation, especially in a subsystem where device state, packet handling, and offload interactions can be highly timing-sensitive. The kernel documentation explicitly describes netdevsim as a driver that exposes programmable resources and device-like behavior for testing, including IPv4 FIB resources and other devlink-managed constructs. (docs.kernel.org)BPF support in the kernel is a major reason netdevsim matters. eBPF has become a central mechanism for extending kernel behavior in networking, observability, and policy enforcement, and it operates by loading programs into privileged kernel paths. That means lists of attached programs, lifetime rules, and synchronization around attachment and detachment are not peripheral concerns; they are the mechanism by which kernel state remains coherent. Linux’s networking development model places BPF work squarely within the broader netdev process, and fixes in this area are typically routed through the netdev and BPF maintainers’ trees with a strong emphasis on correctness and review. (docs.kernel.org)
CVE-2026-23126 is described upstream as a race issue related to the operation on the bpf_bound_progs list in netdevsim. The public vulnerability text available through NVD traces the issue to a kernel commit message that says the bug was resolved by fixing the race in list operations. That phrasing matters: the bug is not primarily about a single bad pointer or a direct bounds check failure, but about the ordering of operations on a shared list that can be modified concurrently. In kernel space, that can be enough to produce list corruption, crashes, or harder-to-diagnose follow-on faults. (nvd.nist.gov)
The broader Linux kernel security pattern helps explain why this vulnerability is noteworthy. Kernel bugs rooted in races often look deceptively mundane in a patch note, yet they can cascade into denial of service, memory corruption, or control-flow anomalies depending on which execution path wins the race. Several Linux security advisories over the last few years have shown that the kernel community treats concurrency bugs as serious because they can be difficult to reproduce, difficult to fuzz, and highly sensitive to scheduling differences. For administrators, that means a “race fix” should be read as a correctness repair with real reliability implications, not merely a cleanup patch. (sentinelone.com)
What CVE-2026-23126 actually is
At the heart of CVE-2026-23126 is a synchronization problem in netdevsim’s handling of BPF-bound programs. The vulnerable area is thebpf_bound_progs list, which is used to track BPF programs bound to the simulated net device. When list operations are not properly serialized, concurrent attach, detach, teardown, or reconfiguration activity can interleave in ways the code did not intend. The result can be stale list pointers, inconsistent bookkeeping, or outright corruption of the list’s internal structure. (nvd.nist.gov)Why a list race matters
A linked list in kernel code is not just an accounting convenience; it is a live data structure whose integrity is assumed by every reader and writer. If one path removes an entry while another is iterating or updating the same list without the expected lock discipline, the kernel can follow invalid pointers or double-manipulate nodes. In a driver like netdevsim, that can surface as a crash, a warning, or a difficult-to-reproduce instability under stress testing. (nvd.nist.gov)The likely failure mode
The public summaries do not suggest a privilege-escalation primitive or a deterministic memory-exploitation gadget. Instead, they point to a race condition that can corrupt state and trigger a failure. That distinction is important for triage: the immediate consequence appears to be availability impact, not a clear-cut confidentiality or integrity breakout. Still, kernel races are rarely benign, because once invariants are broken, secondary bugs can become reachable. (sentinelone.com)Why netdevsim is still security-relevant
It is tempting to dismiss netdevsim because it is a simulated driver. That would be a mistake. Simulated drivers are often used precisely in privileged development and testing environments where kernel features are exercised aggressively. A crash in a test-only path can still take down a production CI host, disrupt validation pipelines, or complicate enterprise kernel deployments that include the module. In practice, “not hardware” does not mean “not exploitable for denial of service.” (docs.kernel.org)The role of BPF in the bug
BPF is central to understanding why this flaw appears in a network driver at all. Linux BPF programs are attached to kernel hooks and driver-facing objects to inspect, filter, or transform traffic and other events. That means a driver must maintain precise associations between a device and its bound programs. If the list of bound programs is mutable from multiple threads, list integrity becomes part of the security boundary. (docs.kernel.org)Attachment and detachment paths
BPF attachment is not a single action; it is a sequence. Programs may be attached, reattached, detached, and cleaned up during device teardown or reload. In a simulated driver that mimics device behavior, these transitions happen under test harnesses that are often deliberately adversarial, which increases the chance of exposing edge-case races. The kernel’s networking workflow expects fixes like this to be robust under concurrency because netdev operations are inherently parallel. (docs.kernel.org)Shared state under stress
The reason these bugs are hard is that they often require the right alignment of events: one thread unregistering a program while another is adding or walking the list, or teardown colliding with ongoing updates. The vulnerability summary makes clear that the issue is related to the operation on the list itself, which strongly implies a missing or insufficient locking discipline around shared state. That is the classic shape of a race in kernel data structures. (nvd.nist.gov)Kernel engineering lesson
The recurring lesson in BPF and networking code is that performance and concurrency are intertwined. The kernel avoids unnecessary serialization where possible, but when a structure is shared, the locking contract must be exact. A single missing lock or an inconsistent lock ordering choice can turn a routine maintenance path into a crash vector. (docs.kernel.org)How the fix is framed upstream
The upstream language attached to CVE-2026-23126 is concise: the Linux kernel resolved a “race issue related to the operation on bpf_bound_progs list” in netdevsim. NVD’s entry confirms that the vulnerability description was received from kernel.org on February 14, 2026, which means the issue entered the public vulnerability stream through the normal kernel disclosure pipeline rather than through a vendor-specific rewrite. (nvd.nist.gov)What that implies about remediation
When a kernel bug is fixed upstream first, downstream vendors typically pick it up through their own stable trees, security advisories, and package updates. In practical terms, administrators should think in terms of kernel version lines and distro backports, not just the CVE label itself. The relevant patch may be present in a vendor kernel even if the vanilla upstream version number suggests otherwise. (nvd.nist.gov)Why no exploit narrative is needed
The absence of a polished exploit chain does not reduce the need to patch. Race condition bugs are often more likely to be used as reliability disruptors than as neat, repeatable privilege-escalation gadgets. In a production environment, repeated kernel crashes are sufficient to create service outage, failed boot loops, or CI pipeline instability. (sentinelone.com)Comparison with other kernel race fixes
Linux has a long history of race-condition fixes in networking and BPF-related code. Many are subtle, involving life-cycle ordering, reference counting, or delayed cleanup. The same pattern appears in other recent kernel advisories where maintainers emphasize order-of-operations, proper locking, and careful teardown sequencing. CVE-2026-23126 fits that pattern cleanly. (github.com)Why Microsoft’s advisory matters
Microsoft’s update-guide entry for CVE-2026-23126 is valuable because it surfaces a Linux kernel vulnerability through a vendor security portal that many enterprise operators already monitor. That kind of cross-vendor visibility is increasingly common for open-source kernel issues, especially when the affected code is part of Linux distributions used in cloud, embedded, or hybrid environments. Microsoft’s listing also reinforces that this is a tracked security event rather than a mere upstream bugfix note. (nvd.nist.gov)Enterprise relevance
Enterprises do not always deploy upstream kernels directly. They frequently rely on vendor-maintained builds, cloud images, or hardware-specific kernels, which means they depend on advisories that map upstream CVEs to their environments. A Microsoft update-guide entry can therefore be a meaningful signal even for organizations that are not running Windows, because it indicates the issue has reached a formal patch-management workflow. (nvd.nist.gov)Monitoring implications
Security teams should interpret this type of listing as a cue to check their Linux fleet for any environment that includes netdevsim or BPF-heavy test infrastructure. Even if the module is not loaded in production servers, it may be present in validation systems, lab hosts, cloud images, or developer workstations. That is often where the first crash reports appear. (docs.kernel.org)The difference between “affected” and “exposed”
It is also useful to distinguish between a kernel being technically affected and a system being meaningfully exposed. A vulnerability in a driver that is not loaded by default may still matter if the module is routinely used in CI, automated testing, or dev environments. The practical exposure is driven by deployment behavior, not just by package inclusion. (docs.kernel.org)Technical context: netdevsim, devlink, and testing surfaces
Netdevsim is more than a toy driver. The kernel docs show it participating in devlink resource management and trap configuration, with resources such as IPv4 FIB capacity exposed for experimentation. That makes it a powerful way to validate logic that normally depends on hardware state. The same realism, however, means its internals must withstand the kinds of concurrent operations that real drivers see. (docs.kernel.org)Devlink as a force multiplier
Devlink is designed to let drivers expose resources, traps, and device behavior in a structured way. In netdevsim, this helps engineers test how networking code responds when resources are constrained, reset, or reconfigured. A race in any of the supporting lists or registration structures can ripple outward into these higher-level mechanisms. (docs.kernel.org)Why simulation code gets stressed harder than hardware
A simulated driver is often hit by automation in ways a physical device never would be. Test suites may rapidly create, destroy, reload, and mutate state, intentionally trying to expose the corner cases. That is excellent for quality, but it also means synchronization bugs can remain latent until a fuzzing or CI workload trips them. (docs.kernel.org)BPF and driver interaction
BPF program binding touches kernel objects that can be manipulated by administrative tools and test harnesses. If the bookkeeping around those bindings is not serialized, teardown and update paths may overlap. This is exactly why BPF-related kernel code tends to be reviewed with extraordinary care: the data structures are small, but the consequences of a mistake are large. (docs.kernel.org)Security impact in practical terms
The immediate classification here is a race condition with potential to cause list corruption and crashes. That puts the primary impact in the availability category. However, administrators should not underweight availability issues in kernel space. In many environments, a crash in a privileged test kernel is enough to break automation, invalidate test results, or require expensive manual recovery. (nvd.nist.gov)Most likely outcomes
- Kernel warning or crash during BPF binding activity.
- State corruption in netdevsim’s
bpf_bound_progsbookkeeping. - Failure of testing or CI jobs that rely on simulated network devices.
- Potential system instability if the corruption is triggered in a repeated way. (nvd.nist.gov)
Less certain but important possibilities
- Secondary faults caused by corrupted list traversal.
- Increased debugging complexity due to non-deterministic reproduction.
- Potential for broader denial of service in heavily instrumented hosts. (nvd.nist.gov)
What the public data does not yet show
The public summary does not present a high-confidence exploit chain or a confirmed user-facing privilege escalation path. That is important because it narrows the immediate operational response to patching and exposure reduction, rather than emergency containment for a known in-the-wild exploit. Still, kernel race bugs warrant prompt attention because their exploitability can evolve as more analysis appears. (nvd.nist.gov)Where this fits in the Linux kernel security story
CVE-2026-23126 is very much a Linux-maintainer-style vulnerability: narrow in code scope, rooted in state management, and fixed through a targeted repair to synchronize access to shared data. It is the sort of bug that usually appears first in kernel testing, syzkaller-style fuzzing, or heavy internal validation before becoming a CVE. (nvd.nist.gov)Why these bugs keep appearing
The kernel is a concurrent system with enormous surface area. Drivers, networking paths, and BPF hooks all interact with workqueues, interrupts, timers, teardown paths, and userspace-triggered state changes. Each of those interactions creates a chance for the wrong ordering to slip through review or testing. (docs.kernel.org)Why the fix matters beyond netdevsim
Even though netdevsim is a simulation driver, the same categories of mistake can occur in production network drivers, BPF attachment code, and devlink resource management. A fix in netdevsim is therefore often a teaching signal for the wider kernel: it reminds maintainers to audit similar list-handling patterns in neighboring code. (docs.kernel.org)The maintenance pattern
The Linux networking subsystem expects bug fixes to be clearly tagged and routed appropriately, withFixes: references and a bias toward conservative backports. That workflow exists because race bugs are easier to propagate than to eliminate once they reach stable branches. CVE-2026-23126 is the kind of issue that benefits from that discipline. (docs.kernel.org)Strengths and Opportunities
The good news is that this vulnerability appears to be the sort of bug that can be solved cleanly once identified. Race-condition fixes in kernel code often boil down to enforcing a lock, clarifying ownership, or reordering teardown steps so that one path cannot invalidate what another still expects to be live. The upstream description suggests exactly that kind of targeted remediation. (nvd.nist.gov)Strengths of the response ecosystem
- Upstream visibility through the kernel vulnerability pipeline.
- Downstream propagation through vendor advisories and stable updates.
- Clear subsystem ownership in the networking and BPF maintainers’ process.
- Well-defined test surface thanks to netdevsim’s purpose-built role. (nvd.nist.gov)
Opportunities for operators
- Use this event to audit kernel update workflows.
- Review whether netdevsim is loaded anywhere in test or staging environments.
- Confirm that BPF-heavy hosts are receiving backported kernel fixes.
- Treat simulated-driver bugs as production-relevant for CI and lab infrastructure. (docs.kernel.org)
Opportunities for developers
- Recheck list ownership and lifetime rules around BPF attachments.
- Add stress tests around attach/detach and teardown races.
- Look for similar unsynchronized list operations in adjacent code.
- Prefer explicit serialization when a data structure is touched from multiple contexts. (docs.kernel.org)
Risks and Concerns
The primary concern is that race bugs are notoriously non-deterministic. A patch may look straightforward, yet the original bug can be hard to reproduce and easy to miss in regression testing. That creates a risk that some systems continue to behave unpredictably even after a fix is available, especially if the relevant kernel version has been backported differently by various vendors. (nvd.nist.gov)Operational risks
- Divergent kernel versions across fleets can make exposure hard to track.
- Vendor backports may hide the fix under a different version number.
- Lab and CI hosts may be overlooked because they are not “production.”
- Crash symptoms may be blamed on unrelated networking components. (nvd.nist.gov)
Technical risks
- Concurrency bugs can manifest only under high load or rare timing.
- A list corruption issue may not fail at the exact point of the race.
- Secondary memory faults can obscure the original root cause.
- Test coverage may be insufficient if attach/detach sequences are not stressed. (nvd.nist.gov)
Governance risks
- Security teams may ignore simulation drivers despite their CI importance.
- Patch prioritization may lag because the vulnerability is not internet-facing.
- Documentation gaps can leave operators uncertain about module exposure. (docs.kernel.org)
What to Watch Next
The next thing to watch is how quickly downstream distributions and enterprise kernel vendors map the upstream fix into their own advisories. Because the original issue is already public and tracked in the kernel CVE stream, the practical question is no longer whether the bug exists, but which package builds still carry the vulnerable code path. (nvd.nist.gov)Items worth tracking
- Stable kernel backport notes for the relevant Linux branches.
- Distribution security advisories referencing the CVE.
- Any follow-on kernel patch that tightens similar BPF list handling.
- Whether test frameworks begin flagging the issue in CI or fuzzing pipelines. (nvd.nist.gov)
Signals that the story is evolving
- Broader references in vendor advisories beyond Microsoft’s update guide.
- Changes in CVSS scoring or impact categorization.
- Kernel commit history indicating adjacent fixes in netdevsim or BPF code.
- Evidence of active exploitation, which would significantly raise urgency. (nvd.nist.gov)
What administrators should do meanwhile
- Inventory kernels that include netdevsim in test or development images.
- Validate whether vendor updates already include the backport.
- Prioritize systems that run BPF-heavy networking workloads or CI harnesses.
- Treat crashy simulation hosts as security-relevant assets, not expendable toys. (docs.kernel.org)
CVE-2026-23126 is a small bug in a specialized driver, but it lives in exactly the part of the kernel where small bugs become expensive: shared state, concurrent access, and cleanup paths that must all agree on who owns what and when. The public evidence points to a straightforward race-condition repair in netdevsim’s BPF program bookkeeping, yet the operational lesson is broader: if your environment uses Linux kernels for testing, networking validation, or BPF-heavy workflows, even a simulated device can be a real stability risk until the fix is in place.
Source: Microsoft Security Response Center Security Update Guide - Microsoft Security Response Center
Last edited: