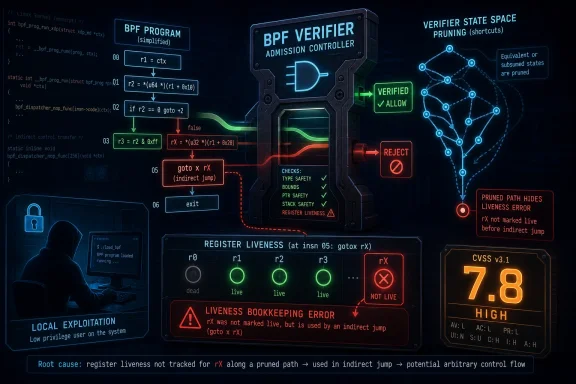
CVE-2026-43321 is a newly published Linux kernel vulnerability in the BPF verifier, disclosed through kernel.org and surfaced in Microsoft’s Security Update Guide on May 8, 2026, with a high CVSS 3.1 score of 7.8 and local, low-complexity exploitation characteristics. The bug is small in code but large in implication: a register used by an indirect BPF jump was not being marked live during verifier analysis. That kind of mistake lives in the narrow seam between compiler theory and operating-system security, which is exactly where modern kernel attack surfaces increasingly reside.
The patch behind CVE-2026-43321 is almost comically modest. In the Linux kernel’s BPF verifier, the
That is not the kind of change that looks dramatic in a diff viewer. There is no sprawling memory allocator rewrite, no obvious unchecked copy, no spectacular failure mode in the commit message. The vulnerability is a reminder that in verifier code, the map is the territory: if the verifier’s model of the program is wrong, then the kernel’s security decision may be wrong too.
BPF has become one of Linux’s most powerful extensibility mechanisms. It lets privileged software load constrained programs into the kernel for networking, tracing, observability, sandboxing, and security enforcement. The bargain is that those programs are allowed near dangerous machinery only because the verifier proves, ahead of time, that they obey strict safety rules.
CVE-2026-43321 sits precisely inside that bargain. The immediate flaw concerns register liveness for an indirect jump instruction. The broader concern is that verifier bookkeeping is not clerical work; it is part of the kernel’s security perimeter.
Local kernel vulnerabilities matter because attackers rarely arrive at the front door as root. They land through a compromised service account, a container escape path, a developer workstation foothold, a malicious package, or a userland exploit chain. Once code execution exists somewhere on the machine, local privilege escalation is the bridge from nuisance to control.
The BPF angle sharpens that concern. On many distributions, unprivileged BPF has been restricted or disabled by default for years, but BPF remains widely used by privileged daemons, observability agents, network stacks, container platforms, and security tools. A vulnerability that requires local privileges may still be reachable in environments where “local” includes semi-trusted workloads, administrative agents, or containerized services with more capability than their owners realize.
For WindowsForum readers, the word “Linux” should not invite complacency. Linux kernels now sit inside Windows-adjacent estates everywhere: WSL developer machines, Azure workloads, Kubernetes clusters, network appliances, security sensors, CI runners, and hybrid identity infrastructure. Microsoft listing the CVE in its update guide is not an accident of paperwork; it reflects the way Windows shops increasingly operate mixed-kernel environments.
That job is punishing because BPF is no longer a toy instruction set. It has grown from packet filtering roots into a general kernel programmability layer, with increasingly sophisticated control flow and helper ecosystems. Every new feature widens the verifier’s reasoning burden.
Indirect jumps are especially interesting because they complicate control-flow analysis. A direct jump points to a known target. An indirect jump uses a register to determine where execution goes, which means the verifier must correctly model not only the jump but the value feeding it. If the register involved in that decision is treated as irrelevant, the verifier can make unsafe equivalence judgments about program states.
That is the conceptual core of CVE-2026-43321. A register that influences control flow was not being marked live at the relevant point in liveness analysis. If later verifier logic prunes or compares states based on that liveness information, it can potentially disregard a value that should matter.
The patch description is terse because kernel commit messages often are. But terse does not mean trivial. In verifier land, “this register was not marked used” can mean “the model of this program’s possible behavior was incomplete.”
That optimization is necessary. It is also dangerous when the equivalence relation is wrong.
If the verifier decides that a register is not live, it may stop caring about differences in that register between two states. That is acceptable when the register truly cannot affect future execution. It is not acceptable when the register is later read by an indirect jump. In that case, two states that look equivalent to the verifier may actually lead the program to different code paths.
This is the kind of bug that makes security engineers uneasy because it does not require a classic memory corruption primitive at the point of the mistake. The corruption is in the proof. The verifier may accept a program based on an incomplete reasoning model, and the actual runtime behavior may step outside the conditions the verifier thought it had established.
The CVE record’s high impact scoring reflects that possibility. Kernel verifier bugs have a long history of becoming privilege escalation candidates because the verifier’s whole role is to prevent unsafe kernel execution. If an attacker can persuade it to accept a program it should reject, the kernel has already crossed the threshold from policy enforcement into misplaced trust.
This matters because many severe kernel bugs are not ancient ghosts lurking for a decade. Some are new defects introduced by new capabilities, found and fixed as the feature interacts with the rest of the subsystem. That does not make them less serious, but it changes how administrators should think about exposure.
Bleeding-edge kernel lines can carry newer functionality before enterprise distributions have widely adopted it. That can reduce exposure for conservative fleets, but it can also create blind spots for organizations running custom kernels, fast-moving cloud images, developer distributions, or upstream-based appliances. The relevant question is not “Do we run Linux?” but “Which kernel line and configuration are we actually running, and which BPF features are enabled?”
The removed reference in the CVE change history also deserves a cautious reading. CVE records evolve as maintainers refine the affected commit set, backport status, and stable references. Early CVE metadata is often useful but not final; administrators should treat it as a starting point for package-vendor advisories rather than a complete asset inventory.
Microsoft ships and supports Linux in more places than the old desktop-war mental model admits. Azure runs Linux at enormous scale. Azure Kubernetes Service depends heavily on Linux nodes. Defender for Cloud, container infrastructure, IoT deployments, and developer tooling all intersect with Linux kernels. WSL has made Linux a routine part of Windows developer workstations.
That does not mean every Windows 11 laptop is suddenly exposed to this CVE in the same way a Linux server might be. It does mean Windows administrators can no longer draw a clean boundary around “Microsoft patching” as Windows-only patching. The patch posture of a modern Microsoft-centered estate includes Linux images, containers, hypervisors, guest kernels, appliances, and developer environments.
For enterprises, this is where asset management becomes security engineering rather than procurement hygiene. If vulnerability dashboards ingest MSRC data, a Linux kernel CVE appearing there may trigger workflows owned by Windows teams. Those teams need enough Linux literacy to triage whether the issue affects WSL, Azure-hosted nodes, third-party appliances, or no deployed asset at all.
The worst response would be either panic or dismissal. The right response is classification: identify where affected kernels exist, determine whether the vulnerable BPF feature path is present and reachable, and patch through the distribution or platform channel that owns the kernel.
A local BPF verifier vulnerability requires a path to load BPF programs with the relevant capabilities and kernel support. On a normal Linux server, that depends on kernel configuration, sysctls, capabilities, namespace behavior, and distribution defaults. In WSL, the security model is different again, because the Linux environment runs inside a VM boundary managed by Windows.
For developers, the practical guidance is simple: keep WSL updated, especially if using it for security research, networking tools, container workflows, or privileged Linux experimentation. WSL has become “just another terminal” for many users, which is convenient but psychologically misleading. It is a kernelized environment with its own update lifecycle.
For defenders, the more serious WSL risk is not that this particular CVE automatically becomes a Windows host compromise. It is that developer endpoints often accumulate privileged tooling, experimental kernels, container runtimes, SSH keys, cloud credentials, and unreviewed scripts. A Linux local privilege escalation inside that environment may still matter operationally, even if it does not directly pierce the Windows kernel boundary.
That nuance is important. Overstating WSL exposure creates noise. Ignoring WSL entirely creates inventory gaps. The mature position is to treat WSL instances as managed compute surfaces when they are used for real work.
Most hardened Kubernetes environments do not allow arbitrary BPF program loading from ordinary pods. Seccomp, capabilities, AppArmor, SELinux, and distribution defaults can all reduce the reachable surface. But container fleets are full of exceptions: privileged pods, CNI components, observability agents, service meshes, eBPF-based security tooling, and node-level DaemonSets.
That is why BPF CVEs deserve attention from cluster operators even when the attack vector is local. The question is not whether a random web container can trigger the bug under default policy. The question is whether any workload class in the cluster has enough privilege to reach the affected verifier path, and whether compromise of that workload would turn into node-level kernel control.
The irony is that the organizations most likely to use BPF heavily are also the ones most likely to have mature observability and security programs. They deploy eBPF agents to see more, filter more, and enforce more. That makes BPF both a defensive superpower and a concentrated point of risk.
CVE-2026-43321 does not argue against BPF. It argues against treating BPF as invisible plumbing. If your fleet depends on kernel-resident programmability, you have to track the kernel as part of the application platform, not merely as a base image detail.
Linux administrators know this dance. The upstream kernel may be fixed, but the package name and version that matters depends on whether the system runs Ubuntu, Debian, Fedora, RHEL, SUSE, Arch, Alpine, a cloud-optimized kernel, a vendor appliance kernel, or a hand-rolled build. Some vendors backport fixes without changing the apparent upstream version, which makes naive version checks unreliable.
Microsoft-centered shops often struggle here because Windows patching has trained them to look for KB numbers, cumulative updates, and a relatively centralized release rhythm. Linux patching is more federated. The authoritative answer for a given system is usually the distribution or platform vendor’s security advisory and installed package changelog, not the upstream version string alone.
That is especially true for kernel CVEs attached to fast-moving subsystems. A fleet may run an older long-term-support kernel that never included the affected feature. Another may run a newer kernel with the vulnerable path but have unprivileged BPF disabled. A third may be patched through a vendor backport while still reporting a version number that appears vulnerable to a scanner.
This is where vulnerability management tools can be both useful and infuriating. They are good at raising the flag. They are less good at understanding kernel backports, feature reachability, and local policy. Administrators should expect some manual interpretation before declaring victory or emergency.
That pattern should shape expectations. As BPF gains features, the verifier has to model more of a language, more helper semantics, more architecture-specific behavior, and more interactions with JIT compilation. The security boundary is therefore partly a software proof engine maintained under real-world development pressure.
This is not unique to Linux. Windows has had its own long relationship with kernel-mode attack surfaces, driver verification, code integrity, and increasingly complex sandbox boundaries. The industry keeps moving enforcement earlier, into validators, verifiers, policy engines, and compilers. That is good security architecture, but it turns correctness bugs in the validator into high-value vulnerabilities.
The uncomfortable lesson is that modern operating systems are full of mechanisms that are safe only because another mechanism correctly predicts their behavior. When the predictor is wrong, the system can fail without looking like it failed. There may be no crash, no obvious log entry, and no malformed packet. There is simply a program that was accepted under false premises.
That is why these CVEs deserve serious treatment even when the patch looks mundane. Attackers like mundane. Mundane changes are easy to miss in reviews, easy to underprioritize in patch queues, and easy to bury under louder vulnerabilities with better marketing names.
A single-user Linux workstation with unprivileged BPF disabled and prompt kernel updates has a different risk profile from a multi-tenant CI host running untrusted builds. A Kubernetes node hosting privileged observability agents has a different profile from an appliance whose vendor kernel lacks the affected feature. A WSL development machine has a different profile again.
The highest-priority systems are those where local users or workloads are not fully trusted. That includes shared Linux servers, build farms, research environments, container hosts, bastion systems, and developer machines that regularly execute third-party code. In those settings, local privilege escalation is not a theoretical category; it is the second half of many real intrusion chains.
Security teams should also separate exploit availability from exploitability. At the time of writing, the public CVE metadata and patch trail describe the flaw and its fix, but public scoring does not prove a weaponized exploit is circulating. Waiting for proof of exploitation, however, is a poor strategy for kernel verifier bugs. Once the patch is public, the diff is public, and the research race begins.
The right posture is boring and disciplined: patch affected kernels, validate exposure, review BPF policy, and monitor for vendor advisories. Boring is underrated in kernel security.
The second step is to examine BPF access policy. Many distributions expose controls around unprivileged BPF usage, and many enterprise baselines already restrict it. Those settings are not a replacement for patching, but they can influence triage and reduce opportunistic exposure.
The third step is to identify privileged software that loads BPF programs. Observability, security, networking, and performance tooling may all depend on BPF. These components are often trusted implicitly because they are infrastructure. If one of them is compromised, misconfigured, or allowed to load user-influenced programs, the kernel attack surface changes.
The fourth step is to avoid overfitting to the name of the CVE. The vulnerable code path is specific, but the operational lesson is broader. If your organization cannot quickly answer which kernels are deployed, which ones support newer BPF features, and where BPF loading is permitted, CVE-2026-43321 is not the only problem.
In mixed Windows and Linux estates, this is also a communication problem. The team that sees the MSRC alert may not be the team that owns the affected kernels. The fix may live in Linux package management, Azure image rotation, AKS node upgrades, or vendor firmware. Someone has to translate the advisory into the correct maintenance lane.
Windows administrators routinely manage Linux-based appliances, cloud services, containers, and developer environments. Microsoft’s own ecosystem encourages that hybridity. Azure is not a Windows-only cloud. VS Code, WSL, GitHub Actions, AKS, and Defender all sit across platform boundaries. The operational estate has become polyglot even when the help desk still images Windows laptops.
That means Windows professionals need a working vocabulary for Linux kernel security. Not kernel-developer depth, but enough to distinguish a remote unauthenticated network bug from a local verifier flaw; enough to know when WSL matters; enough to ask whether AKS nodes inherit a patched kernel; enough to understand that a vendor backport may fix a CVE without a shiny new upstream version number.
CVE-2026-43321 is a useful case study because it is not flashy. It has no catchy name, no logo, and no immediate mass-exploitation narrative. It is exactly the kind of vulnerability that enters enterprise dashboards, gets assigned to the wrong queue, and waits for someone to decide whether Linux kernels are part of the Microsoft estate.
They are. Not always directly, not always visibly, but often enough that ignoring the alert is a process failure.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Six-Line Fix Lands in One of Linux’s Most Sensitive Subsystems
A Six-Line Fix Lands in One of Linux’s Most Sensitive Subsystems
The patch behind CVE-2026-43321 is almost comically modest. In the Linux kernel’s BPF verifier, the compute_insn_live_regs() function failed to treat the register operand of a gotox rX instruction as used. The fix adds logic so that when an indirect jump reads a destination register, the verifier’s liveness analysis records that read instead of pretending the instruction consumes no register state.That is not the kind of change that looks dramatic in a diff viewer. There is no sprawling memory allocator rewrite, no obvious unchecked copy, no spectacular failure mode in the commit message. The vulnerability is a reminder that in verifier code, the map is the territory: if the verifier’s model of the program is wrong, then the kernel’s security decision may be wrong too.
BPF has become one of Linux’s most powerful extensibility mechanisms. It lets privileged software load constrained programs into the kernel for networking, tracing, observability, sandboxing, and security enforcement. The bargain is that those programs are allowed near dangerous machinery only because the verifier proves, ahead of time, that they obey strict safety rules.
CVE-2026-43321 sits precisely inside that bargain. The immediate flaw concerns register liveness for an indirect jump instruction. The broader concern is that verifier bookkeeping is not clerical work; it is part of the kernel’s security perimeter.
The Vulnerability Is Local, but That Does Not Make It Boring
The CNA score attached to CVE-2026-43321 is CVSS 3.1 7.8, rated high, with local attack vector, low attack complexity, low privileges required, no user interaction, unchanged scope, and high confidentiality, integrity, and availability impact. That combination says something very specific. This is not a remote wormable network bug, but it is the sort of local kernel flaw defenders cannot shrug off.Local kernel vulnerabilities matter because attackers rarely arrive at the front door as root. They land through a compromised service account, a container escape path, a developer workstation foothold, a malicious package, or a userland exploit chain. Once code execution exists somewhere on the machine, local privilege escalation is the bridge from nuisance to control.
The BPF angle sharpens that concern. On many distributions, unprivileged BPF has been restricted or disabled by default for years, but BPF remains widely used by privileged daemons, observability agents, network stacks, container platforms, and security tools. A vulnerability that requires local privileges may still be reachable in environments where “local” includes semi-trusted workloads, administrative agents, or containerized services with more capability than their owners realize.
For WindowsForum readers, the word “Linux” should not invite complacency. Linux kernels now sit inside Windows-adjacent estates everywhere: WSL developer machines, Azure workloads, Kubernetes clusters, network appliances, security sensors, CI runners, and hybrid identity infrastructure. Microsoft listing the CVE in its update guide is not an accident of paperwork; it reflects the way Windows shops increasingly operate mixed-kernel environments.
The BPF Verifier Is a Security Boundary Built From Assumptions
The BPF verifier is often described as a static analyzer, but in security terms it is closer to an admission-control engine. It decides whether a program may execute in kernel context. It tracks registers, stack state, pointer provenance, bounds, helper calls, control flow, and the relationships between values.That job is punishing because BPF is no longer a toy instruction set. It has grown from packet filtering roots into a general kernel programmability layer, with increasingly sophisticated control flow and helper ecosystems. Every new feature widens the verifier’s reasoning burden.
Indirect jumps are especially interesting because they complicate control-flow analysis. A direct jump points to a known target. An indirect jump uses a register to determine where execution goes, which means the verifier must correctly model not only the jump but the value feeding it. If the register involved in that decision is treated as irrelevant, the verifier can make unsafe equivalence judgments about program states.
That is the conceptual core of CVE-2026-43321. A register that influences control flow was not being marked live at the relevant point in liveness analysis. If later verifier logic prunes or compares states based on that liveness information, it can potentially disregard a value that should matter.
The patch description is terse because kernel commit messages often are. But terse does not mean trivial. In verifier land, “this register was not marked used” can mean “the model of this program’s possible behavior was incomplete.”
The Dangerous Word Is “Pruning”
To understand why a liveness bug becomes a CVE, it helps to focus on pruning. Verifiers do not want to explore every possible execution path indefinitely; that would be too expensive and, for complex programs, impractical. They use state comparison and pruning to decide when two paths are effectively equivalent enough that one does not need to be rechecked in full.That optimization is necessary. It is also dangerous when the equivalence relation is wrong.
If the verifier decides that a register is not live, it may stop caring about differences in that register between two states. That is acceptable when the register truly cannot affect future execution. It is not acceptable when the register is later read by an indirect jump. In that case, two states that look equivalent to the verifier may actually lead the program to different code paths.
This is the kind of bug that makes security engineers uneasy because it does not require a classic memory corruption primitive at the point of the mistake. The corruption is in the proof. The verifier may accept a program based on an incomplete reasoning model, and the actual runtime behavior may step outside the conditions the verifier thought it had established.
The CVE record’s high impact scoring reflects that possibility. Kernel verifier bugs have a long history of becoming privilege escalation candidates because the verifier’s whole role is to prevent unsafe kernel execution. If an attacker can persuade it to accept a program it should reject, the kernel has already crossed the threshold from policy enforcement into misplaced trust.
The Timeline Shows a Fresh Feature Meeting an Old Lesson
The public trail around the fix points to a recent BPF feature path. The indirect jump machinery, includinggotox, arrived in the context of continuing BPF evolution, while the stable patch series carried the liveness correction back into affected kernels. The CVE was received on May 8, 2026, and modified on May 11, 2026, with kernel.org adding the CVSS vector.This matters because many severe kernel bugs are not ancient ghosts lurking for a decade. Some are new defects introduced by new capabilities, found and fixed as the feature interacts with the rest of the subsystem. That does not make them less serious, but it changes how administrators should think about exposure.
Bleeding-edge kernel lines can carry newer functionality before enterprise distributions have widely adopted it. That can reduce exposure for conservative fleets, but it can also create blind spots for organizations running custom kernels, fast-moving cloud images, developer distributions, or upstream-based appliances. The relevant question is not “Do we run Linux?” but “Which kernel line and configuration are we actually running, and which BPF features are enabled?”
The removed reference in the CVE change history also deserves a cautious reading. CVE records evolve as maintainers refine the affected commit set, backport status, and stable references. Early CVE metadata is often useful but not final; administrators should treat it as a starting point for package-vendor advisories rather than a complete asset inventory.
Microsoft’s Presence Turns a Linux Bug Into a Windows Estate Problem
The submitted source is Microsoft’s Security Update Guide entry for CVE-2026-43321, which may look odd at first glance. This is a Linux kernel vulnerability, assigned through kernel.org, with upstream stable commits as the central remediation trail. Yet Microsoft has good reason to surface it.Microsoft ships and supports Linux in more places than the old desktop-war mental model admits. Azure runs Linux at enormous scale. Azure Kubernetes Service depends heavily on Linux nodes. Defender for Cloud, container infrastructure, IoT deployments, and developer tooling all intersect with Linux kernels. WSL has made Linux a routine part of Windows developer workstations.
That does not mean every Windows 11 laptop is suddenly exposed to this CVE in the same way a Linux server might be. It does mean Windows administrators can no longer draw a clean boundary around “Microsoft patching” as Windows-only patching. The patch posture of a modern Microsoft-centered estate includes Linux images, containers, hypervisors, guest kernels, appliances, and developer environments.
For enterprises, this is where asset management becomes security engineering rather than procurement hygiene. If vulnerability dashboards ingest MSRC data, a Linux kernel CVE appearing there may trigger workflows owned by Windows teams. Those teams need enough Linux literacy to triage whether the issue affects WSL, Azure-hosted nodes, third-party appliances, or no deployed asset at all.
The worst response would be either panic or dismissal. The right response is classification: identify where affected kernels exist, determine whether the vulnerable BPF feature path is present and reachable, and patch through the distribution or platform channel that owns the kernel.
WSL Changes the Audience, but Not the Exploit Conditions
Windows Subsystem for Linux is the obvious place many readers will look first. WSL 2 uses a real Linux kernel inside a lightweight virtual machine, which means Linux kernel CVEs can be relevant to WSL in principle. But relevance is not the same as confirmed exploitability.A local BPF verifier vulnerability requires a path to load BPF programs with the relevant capabilities and kernel support. On a normal Linux server, that depends on kernel configuration, sysctls, capabilities, namespace behavior, and distribution defaults. In WSL, the security model is different again, because the Linux environment runs inside a VM boundary managed by Windows.
For developers, the practical guidance is simple: keep WSL updated, especially if using it for security research, networking tools, container workflows, or privileged Linux experimentation. WSL has become “just another terminal” for many users, which is convenient but psychologically misleading. It is a kernelized environment with its own update lifecycle.
For defenders, the more serious WSL risk is not that this particular CVE automatically becomes a Windows host compromise. It is that developer endpoints often accumulate privileged tooling, experimental kernels, container runtimes, SSH keys, cloud credentials, and unreviewed scripts. A Linux local privilege escalation inside that environment may still matter operationally, even if it does not directly pierce the Windows kernel boundary.
That nuance is important. Overstating WSL exposure creates noise. Ignoring WSL entirely creates inventory gaps. The mature position is to treat WSL instances as managed compute surfaces when they are used for real work.
Containers Make “Local” a Negotiation, Not a Place
BPF vulnerabilities often become more interesting in containerized environments because containers blur the meaning of local privilege. A process inside a container is local to the host kernel. The container may have a restricted view of the filesystem and process table, but it shares the kernel with the host unless additional virtualization is involved.Most hardened Kubernetes environments do not allow arbitrary BPF program loading from ordinary pods. Seccomp, capabilities, AppArmor, SELinux, and distribution defaults can all reduce the reachable surface. But container fleets are full of exceptions: privileged pods, CNI components, observability agents, service meshes, eBPF-based security tooling, and node-level DaemonSets.
That is why BPF CVEs deserve attention from cluster operators even when the attack vector is local. The question is not whether a random web container can trigger the bug under default policy. The question is whether any workload class in the cluster has enough privilege to reach the affected verifier path, and whether compromise of that workload would turn into node-level kernel control.
The irony is that the organizations most likely to use BPF heavily are also the ones most likely to have mature observability and security programs. They deploy eBPF agents to see more, filter more, and enforce more. That makes BPF both a defensive superpower and a concentrated point of risk.
CVE-2026-43321 does not argue against BPF. It argues against treating BPF as invisible plumbing. If your fleet depends on kernel-resident programmability, you have to track the kernel as part of the application platform, not merely as a base image detail.
The Patch Is Surgical, but Rollout Is Still Political
A six-line kernel fix can still take weeks to reach production. The upstream commit lands first, then stable trees, then distribution kernels, then cloud images, then enterprise maintenance windows, then appliance firmware, then the forgotten host under a lab bench. Every stage adds delay and interpretation.Linux administrators know this dance. The upstream kernel may be fixed, but the package name and version that matters depends on whether the system runs Ubuntu, Debian, Fedora, RHEL, SUSE, Arch, Alpine, a cloud-optimized kernel, a vendor appliance kernel, or a hand-rolled build. Some vendors backport fixes without changing the apparent upstream version, which makes naive version checks unreliable.
Microsoft-centered shops often struggle here because Windows patching has trained them to look for KB numbers, cumulative updates, and a relatively centralized release rhythm. Linux patching is more federated. The authoritative answer for a given system is usually the distribution or platform vendor’s security advisory and installed package changelog, not the upstream version string alone.
That is especially true for kernel CVEs attached to fast-moving subsystems. A fleet may run an older long-term-support kernel that never included the affected feature. Another may run a newer kernel with the vulnerable path but have unprivileged BPF disabled. A third may be patched through a vendor backport while still reporting a version number that appears vulnerable to a scanner.
This is where vulnerability management tools can be both useful and infuriating. They are good at raising the flag. They are less good at understanding kernel backports, feature reachability, and local policy. Administrators should expect some manual interpretation before declaring victory or emergency.
The Security Industry Keeps Rediscovering Verifier Bugs
BPF verifier vulnerabilities have become a genre. Some involve incorrect bounds tracking. Some involve pointer type confusion. Some involve scalar range propagation. Some involve state pruning. CVE-2026-43321 belongs to that lineage because the failure is not in an exposed syscall parser but in the verifier’s internal reasoning about a program.That pattern should shape expectations. As BPF gains features, the verifier has to model more of a language, more helper semantics, more architecture-specific behavior, and more interactions with JIT compilation. The security boundary is therefore partly a software proof engine maintained under real-world development pressure.
This is not unique to Linux. Windows has had its own long relationship with kernel-mode attack surfaces, driver verification, code integrity, and increasingly complex sandbox boundaries. The industry keeps moving enforcement earlier, into validators, verifiers, policy engines, and compilers. That is good security architecture, but it turns correctness bugs in the validator into high-value vulnerabilities.
The uncomfortable lesson is that modern operating systems are full of mechanisms that are safe only because another mechanism correctly predicts their behavior. When the predictor is wrong, the system can fail without looking like it failed. There may be no crash, no obvious log entry, and no malformed packet. There is simply a program that was accepted under false premises.
That is why these CVEs deserve serious treatment even when the patch looks mundane. Attackers like mundane. Mundane changes are easy to miss in reviews, easy to underprioritize in patch queues, and easy to bury under louder vulnerabilities with better marketing names.
CVSS Says High, but Your Fleet Decides Urgency
The 7.8 score is useful, but it is not a substitute for environmental risk. A local, low-complexity, low-privilege kernel issue with high impact is serious by default. Whether it is an emergency depends on kernel version, BPF exposure, workload trust, and compensating controls.A single-user Linux workstation with unprivileged BPF disabled and prompt kernel updates has a different risk profile from a multi-tenant CI host running untrusted builds. A Kubernetes node hosting privileged observability agents has a different profile from an appliance whose vendor kernel lacks the affected feature. A WSL development machine has a different profile again.
The highest-priority systems are those where local users or workloads are not fully trusted. That includes shared Linux servers, build farms, research environments, container hosts, bastion systems, and developer machines that regularly execute third-party code. In those settings, local privilege escalation is not a theoretical category; it is the second half of many real intrusion chains.
Security teams should also separate exploit availability from exploitability. At the time of writing, the public CVE metadata and patch trail describe the flaw and its fix, but public scoring does not prove a weaponized exploit is circulating. Waiting for proof of exploitation, however, is a poor strategy for kernel verifier bugs. Once the patch is public, the diff is public, and the research race begins.
The right posture is boring and disciplined: patch affected kernels, validate exposure, review BPF policy, and monitor for vendor advisories. Boring is underrated in kernel security.
The Practical Work Starts After the Scanner Alert
For administrators, the first step is not to grep the internet for exploit code. It is to determine whether the affected kernel code exists on the systems they own. That means checking distribution advisories, installed kernel package changelogs, and cloud image update notes rather than relying only on upstream commit IDs.The second step is to examine BPF access policy. Many distributions expose controls around unprivileged BPF usage, and many enterprise baselines already restrict it. Those settings are not a replacement for patching, but they can influence triage and reduce opportunistic exposure.
The third step is to identify privileged software that loads BPF programs. Observability, security, networking, and performance tooling may all depend on BPF. These components are often trusted implicitly because they are infrastructure. If one of them is compromised, misconfigured, or allowed to load user-influenced programs, the kernel attack surface changes.
The fourth step is to avoid overfitting to the name of the CVE. The vulnerable code path is specific, but the operational lesson is broader. If your organization cannot quickly answer which kernels are deployed, which ones support newer BPF features, and where BPF loading is permitted, CVE-2026-43321 is not the only problem.
In mixed Windows and Linux estates, this is also a communication problem. The team that sees the MSRC alert may not be the team that owns the affected kernels. The fix may live in Linux package management, Azure image rotation, AKS node upgrades, or vendor firmware. Someone has to translate the advisory into the correct maintenance lane.
The WindowsForum Angle Is Hybrid Reality, Not Brand Confusion
It would be easy to dismiss a Linux BPF bug as off-topic for a Windows community. That would have been more plausible fifteen years ago. Today, it misunderstands how Windows environments are built.Windows administrators routinely manage Linux-based appliances, cloud services, containers, and developer environments. Microsoft’s own ecosystem encourages that hybridity. Azure is not a Windows-only cloud. VS Code, WSL, GitHub Actions, AKS, and Defender all sit across platform boundaries. The operational estate has become polyglot even when the help desk still images Windows laptops.
That means Windows professionals need a working vocabulary for Linux kernel security. Not kernel-developer depth, but enough to distinguish a remote unauthenticated network bug from a local verifier flaw; enough to know when WSL matters; enough to ask whether AKS nodes inherit a patched kernel; enough to understand that a vendor backport may fix a CVE without a shiny new upstream version number.
CVE-2026-43321 is a useful case study because it is not flashy. It has no catchy name, no logo, and no immediate mass-exploitation narrative. It is exactly the kind of vulnerability that enters enterprise dashboards, gets assigned to the wrong queue, and waits for someone to decide whether Linux kernels are part of the Microsoft estate.
They are. Not always directly, not always visibly, but often enough that ignoring the alert is a process failure.
The Small Register Bug With a Long Administrative Tail
CVE-2026-43321 should leave administrators with a short list of concrete actions, not a vague sense that BPF is scary. The vulnerability is technical, but the response is mostly inventory, patching, and policy discipline.- Administrators should verify affected kernel status through their distribution, cloud provider, or appliance vendor rather than relying only on upstream kernel version strings.
- Systems that allow local users, CI jobs, containers, or semi-trusted agents to reach BPF functionality deserve faster triage than single-purpose hosts with tightly controlled access.
- WSL users should keep the WSL kernel updated, especially on developer workstations that run untrusted code, containers, or privileged Linux tooling.
- Kubernetes operators should review privileged pods, BPF-based agents, and node kernel update channels instead of assuming container isolation makes local kernel bugs irrelevant.
- Security teams should treat MSRC-listed Linux CVEs as hybrid-estate signals, not Windows patching anomalies.
- Restricting unprivileged BPF can reduce exposure, but it should be treated as a compensating control rather than a substitute for patched kernels.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center