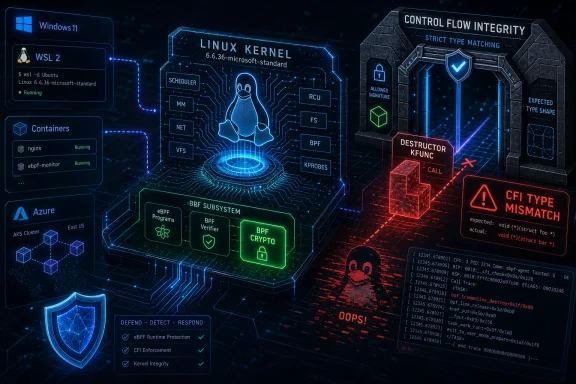
CVE-2026-43306 is a newly published Linux kernel vulnerability recorded by NVD on May 8, 2026, covering a BPF crypto bug where a destructor kfunc used the wrong function type under Control Flow Integrity enforcement. It is not the kind of headline-grabbing remote code execution flaw that sends administrators scrambling through emergency runbooks. Its significance is subtler: a small type mismatch in a fast-moving kernel subsystem can still become a formally tracked security issue once it can crash a protected kernel. For WindowsForum readers, the story matters because Linux is no longer “over there” — it is inside WSL, Azure fleets, containers, developer workstations, CI runners, and the hybrid estates Windows admins are increasingly expected to understand.
The short version of CVE-2026-43306 is almost comically specific: the Linux kernel’s BPF crypto support registered a destructor kfunc with a function pointer type that did not match what the kernel expected. With
That makes this vulnerability awkward to classify in ordinary enterprise language. It is not a memory corruption primitive, at least from the public description. It is not presented as remotely exploitable. It does not currently carry an NVD CVSS score, and the NVD entry says enrichment has not yet supplied the familiar vector string security teams often use to sort patch queues.
But the bug still lives in the kernel, and it still produces an oops under a security configuration designed to make type-confused indirect calls fail closed. That distinction matters. The kernel did not discover that the code was safe; it discovered that the code was wrong enough for a hardening feature to refuse execution.
The fix is equally telling. Rather than weaken the verifier or loosen CFI expectations, the kernel change adds a small stub function with the correct destructor type and registers that stub instead. In other words, the patch preserves the security model and adapts the BPF crypto interface to it. That is the right engineering instinct, and it is also the reason this CVE is more interesting than its likely severity rating will suggest.
The price of that flexibility is a dense contract between BPF programs, the verifier, kernel types, and the helper or kfunc interfaces exposed to them. A kfunc is not just a regular function call with a fashionable name. It is a kernel function made available to BPF programs under rules enforced by the verifier, often annotated with lifetime, ownership, and type information that decides what a program may acquire, store, release, or pass onward.
The affected area, BPF crypto, sits at the intersection of BPF’s programmability and the kernel’s cryptographic API. Public BPF documentation describes
That is why “wrong destructor kfunc type” is not a cosmetic bug. In C, it is easy for function pointer signatures to look morally equivalent to a human reviewer while remaining distinct to a compiler, a verifier, or CFI instrumentation. The whole point of CFI is to make those distinctions enforceable at runtime.
The CVE text is unusually plain about what happened: with
This is exactly the kind of failure hardening features are supposed to expose. Without CFI, the same mismatch might pass unnoticed if the calling convention happened to work in practice. With CFI, implementation details are no longer allowed to masquerade as correctness. The mismatch becomes a crash, the crash becomes a fix, and the fix becomes a CVE.
Some administrators will look at that chain and conclude the issue only affects hardened kernels, so it can be deprioritized. That is too glib. Security hardening often exposes latent bugs before attackers or unusual workloads do. A crash under CFI may be less frightening than a privilege escalation exploit, but it still indicates a boundary where the kernel’s internal model and its executable reality diverged.
In this case, the solution was not to generalize the release function into a looser
That is a small fix with a larger message. Modern kernel security increasingly depends on layers of type information agreeing with one another: C types, BTF metadata, verifier rules, kfunc flags, lifetime annotations, and compiler instrumentation. When those layers disagree, a bug can surface even if no attacker has supplied malicious input.
It is tempting to think of this as bureaucracy inside the kernel, a paper cut created by too many safety systems. But that would miss the point. These systems exist because the old kernel model — trust the caller, hope the types line up, rely on convention — does not scale to a world where BPF programs are generated by tools, deployed by platforms, and used for security-sensitive policy decisions.
WSL2 is the obvious example. It uses a real Linux kernel maintained in Microsoft’s public WSL2 kernel repository, with recent releases tracking modern long-term kernel lines. That does not mean every upstream Linux CVE automatically applies to every WSL installation in the same way it applies to a general-purpose Linux server. Configuration, enabled subsystems, kernel version, and exposed attack surface all matter.
Azure is the broader example. Enterprises that think of themselves as Windows shops often run Linux appliances, Linux containers, Azure Linux images, Ubuntu images, Kubernetes nodes, build agents, and security tooling that depends on BPF. A vulnerability in a Linux kernel subsystem may be operationally relevant even if no one in the organization has ever installed a traditional Linux desktop.
That is why the presence of an MSRC page should not be read as “this is a Windows vulnerability.” It is better read as evidence that Microsoft now has to track, surface, and sometimes remediate vulnerabilities across a hybrid operating system estate. The Windows admin’s job has expanded from patching Windows to understanding which Linux kernels are hiding behind Windows-adjacent workflows.
The absence of a score is not the same as the absence of risk. It means the public enrichment process has not yet attached a standard severity model to the record. In kernel land, especially under the Linux kernel CNA process, CVEs are often tied to fixes after they land in stable trees, and the security meaning can be narrower than the identifier alone implies.
That makes CVE-2026-43306 a good example of why CVSS is a sorting aid, not a substitute for engineering judgment. A local crash reachable only through specialized BPF self-test conditions is very different from a weaponized local privilege escalation circulating in exploit kits. But a kernel oops in a privileged subsystem is also not a harmless documentation typo.
Security teams should ask practical questions before they panic. Is the affected kernel version deployed? Is BPF crypto enabled and usable in the relevant environment? Is
The commit subject — “bpf: crypto: Use the correct destructor kfunc type” — is unusually descriptive and refreshingly unmelodramatic. It says this is a correctness fix in BPF crypto object lifetime handling. There is no need to embellish it into a catastrophe.
Still, the patch is not trivial in the way a typo fix is trivial. Destructor registration is about ownership and cleanup. In BPF, object lifetime bugs are exactly where verifier assumptions, reference counts, map storage, and kernel memory management meet. A release path with the wrong callable type is the sort of plumbing defect that looks small because the abstraction is doing so much work.
The important operational point is that administrators should not attempt to outsmart this class of issue with local mitigations unless a vendor specifically recommends one. Disabling BPF broadly can break observability and security tooling. Disabling crypto-related kernel features can break workloads. The clean answer is the boring one: take the vendor kernel update when it arrives for your platform.
That distinction is important because kernel CVE fatigue is real. If every new kernel CVE is treated as an emergency, administrators stop listening. If every low-drama CVE is ignored, latent reliability and security problems accumulate until a future update becomes far harder to reason about.
The better model is triage by exposure and consequence. A kernel crash that requires a particular configuration and code path may rank below an exploited privilege escalation. But it should still be patched in normal kernel maintenance windows, especially on systems that deliberately enable hardening options such as CFI. If you went to the trouble of running a hardened kernel, you probably do not want known CFI failures lurking in the object cleanup path.
This is also where developer workstations deserve more attention than they usually get. BPF self-tests, custom kernels, observability agents, and experimental networking stacks are often found in engineering environments before they are found in production. A bug that surfaced under self-test conditions may be most visible to the very teams building the next layer of platform automation.
That means BPF bugs have to be read differently from ordinary niche kernel defects. Even when the immediate impact is narrow, the subsystem sits in a privileged position. It is a programmable interface into the kernel guarded by a verifier and constrained by type metadata. When something goes wrong there, the blast radius depends heavily on who can load programs, what helpers or kfuncs are available, and how the distribution configures unprivileged access.
Most mainstream distributions have spent years tightening unprivileged BPF access because the feature is too powerful to expose casually. Cloud platforms and container hosts often run BPF-based agents with elevated privileges because the operational value is enormous. Security vendors use BPF to inspect behavior with less overhead than older kernel-module approaches. Observability vendors use it to extract signal from production systems without recompiling applications.
CVE-2026-43306 is therefore not alarming because this particular bug appears catastrophic. It is notable because it shows how refined the BPF contract has become. A destructor’s exact function type is now part of the security boundary, and the kernel’s hardening stack is prepared to enforce it.
For WSL users, the right answer is usually to keep WSL and its kernel package updated through Microsoft’s supported update channels. For enterprise-managed developer workstations, it is worth confirming whether WSL kernel updates are actually flowing under your endpoint management policy. Developers who manually pin or replace kernels for testing can drift away from the supported path.
For Azure and container environments, the answer is more conventional but more urgent: track the distribution kernel packages and node images you actually deploy. A CVE attached to upstream Linux does not tell you whether your managed Kubernetes nodes, marketplace images, or custom golden images have received the relevant backport. The version string alone may not tell the full story either, because enterprise distributions often backport fixes without moving to the upstream version where the fix first appeared.
For security teams, this is a reminder to correlate kernel CVEs with configuration data. A scanner that reports CVE-2026-43306 on every Linux host without knowing whether BPF crypto or CFI are relevant is creating noise. A process that ignores the CVE because “NVD score: N/A” is creating blind spots. The goal is neither panic nor dismissal; it is informed maintenance.
CVE-2026-43306 is a clean example of that tradeoff. CFI did not create the type mismatch. It exposed it. The kernel fix did not sidestep the hardening feature. It made the affected BPF crypto destructor path conform to the type CFI expected.
That is the direction kernel development should move. Modern operating systems are too large and too exposed to rely on informal correctness. When a kernel subsystem exports programmable functionality to privileged or semi-privileged consumers, exact types and lifetimes are not academic details. They are part of the defense.
There is a parallel here for Windows readers. Microsoft has spent years pushing similar ideas through virtualization-based security, kernel-mode code integrity, hardware-enforced stack protection, and driver signing requirements. Every one of those technologies has broken some legitimate code along the way. The long-term answer has not been to abandon enforcement; it has been to force the ecosystem to meet stricter contracts.
The most concrete lessons are straightforward:
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Kernel Crash Became a CVE Because Hardening Did Its Job
A Kernel Crash Became a CVE Because Hardening Did Its Job
The short version of CVE-2026-43306 is almost comically specific: the Linux kernel’s BPF crypto support registered a destructor kfunc with a function pointer type that did not match what the kernel expected. With CONFIG_CFI enabled, that mismatch is not tolerated. The kernel’s Control Flow Integrity machinery sees an indirect call whose type does not line up with the target and stops the party with a CFI failure.That makes this vulnerability awkward to classify in ordinary enterprise language. It is not a memory corruption primitive, at least from the public description. It is not presented as remotely exploitable. It does not currently carry an NVD CVSS score, and the NVD entry says enrichment has not yet supplied the familiar vector string security teams often use to sort patch queues.
But the bug still lives in the kernel, and it still produces an oops under a security configuration designed to make type-confused indirect calls fail closed. That distinction matters. The kernel did not discover that the code was safe; it discovered that the code was wrong enough for a hardening feature to refuse execution.
The fix is equally telling. Rather than weaken the verifier or loosen CFI expectations, the kernel change adds a small stub function with the correct destructor type and registers that stub instead. In other words, the patch preserves the security model and adapts the BPF crypto interface to it. That is the right engineering instinct, and it is also the reason this CVE is more interesting than its likely severity rating will suggest.
BPF Keeps Moving From Power Tool to Kernel Contract
To understand why this tiny mismatch matters, you have to understand what BPF has become. eBPF began life as a mechanism for running constrained programs in the kernel, but modern BPF is now a sprawling platform for observability, networking, security enforcement, tracing, and increasingly sophisticated kernel-adjacent logic. It is one of the reasons Linux can be bent into shapes that would once have required custom modules.The price of that flexibility is a dense contract between BPF programs, the verifier, kernel types, and the helper or kfunc interfaces exposed to them. A kfunc is not just a regular function call with a fashionable name. It is a kernel function made available to BPF programs under rules enforced by the verifier, often annotated with lifetime, ownership, and type information that decides what a program may acquire, store, release, or pass onward.
The affected area, BPF crypto, sits at the intersection of BPF’s programmability and the kernel’s cryptographic API. Public BPF documentation describes
bpf_crypto_ctx_create as a way to allocate a crypto context that can be used by BPF programs for encryption and decryption, with matching acquire and release operations. That release path is where destructor semantics become important, because the kernel needs to know how to tear down objects safely when references are dropped.That is why “wrong destructor kfunc type” is not a cosmetic bug. In C, it is easy for function pointer signatures to look morally equivalent to a human reviewer while remaining distinct to a compiler, a verifier, or CFI instrumentation. The whole point of CFI is to make those distinctions enforceable at runtime.
CFI Turns Sloppy Interfaces Into Observable Failures
Control Flow Integrity is one of those mitigations that tends to disappear from view until it breaks something. Its job is to constrain indirect calls so that attackers cannot easily redirect execution to arbitrary code locations. In the Linux kernel, CFI support is particularly valuable because the kernel is an enormous body of C code full of function pointers, callbacks, subsystems, and architecture-specific execution paths.The CVE text is unusually plain about what happened: with
CONFIG_CFI enabled, the kernel strictly enforces that indirect function calls use a function pointer type matching the target function. The reported failure occurred in bpf_obj_free_fields, targeting bpf_crypto_ctx_release, with CFI expecting a different type. That is the kernel saying, in effect, “I was asked to call this function through the wrong-shaped door.”This is exactly the kind of failure hardening features are supposed to expose. Without CFI, the same mismatch might pass unnoticed if the calling convention happened to work in practice. With CFI, implementation details are no longer allowed to masquerade as correctness. The mismatch becomes a crash, the crash becomes a fix, and the fix becomes a CVE.
Some administrators will look at that chain and conclude the issue only affects hardened kernels, so it can be deprioritized. That is too glib. Security hardening often exposes latent bugs before attackers or unusual workloads do. A crash under CFI may be less frightening than a privilege escalation exploit, but it still indicates a boundary where the kernel’s internal model and its executable reality diverged.
The Verifier Was Not the Villain
One of the more revealing lines in the description is that using avoid * argument for bpf_crypto_ctx_release would make the BPF verifier unhappy. That sentence captures the tension at the heart of BPF development. The verifier is there to prevent unsafe programs from entering the kernel, but its strictness means kernel developers sometimes need wrapper functions and carefully annotated types to express what is safe.In this case, the solution was not to generalize the release function into a looser
void * shape. That might have made one side of the type system happier while making the BPF side less precise. Instead, the patch adds a stub with the expected destructor type and leaves the BPF-facing function signature intact.That is a small fix with a larger message. Modern kernel security increasingly depends on layers of type information agreeing with one another: C types, BTF metadata, verifier rules, kfunc flags, lifetime annotations, and compiler instrumentation. When those layers disagree, a bug can surface even if no attacker has supplied malicious input.
It is tempting to think of this as bureaucracy inside the kernel, a paper cut created by too many safety systems. But that would miss the point. These systems exist because the old kernel model — trust the caller, hope the types line up, rely on convention — does not scale to a world where BPF programs are generated by tools, deployed by platforms, and used for security-sensitive policy decisions.
Microsoft’s Presence in the Entry Is a Sign of the New Linux Supply Chain
The source material here points to Microsoft’s Security Update Guide, which is why this story belongs on a Windows-focused site as much as a Linux one. Microsoft’s security world now regularly intersects with Linux kernel CVEs, not only because Azure runs vast Linux workloads, but because Windows developers increasingly consume Linux through WSL and containerized toolchains. The boundary between “Windows patching” and “Linux patching” has blurred into a supply-chain problem.WSL2 is the obvious example. It uses a real Linux kernel maintained in Microsoft’s public WSL2 kernel repository, with recent releases tracking modern long-term kernel lines. That does not mean every upstream Linux CVE automatically applies to every WSL installation in the same way it applies to a general-purpose Linux server. Configuration, enabled subsystems, kernel version, and exposed attack surface all matter.
Azure is the broader example. Enterprises that think of themselves as Windows shops often run Linux appliances, Linux containers, Azure Linux images, Ubuntu images, Kubernetes nodes, build agents, and security tooling that depends on BPF. A vulnerability in a Linux kernel subsystem may be operationally relevant even if no one in the organization has ever installed a traditional Linux desktop.
That is why the presence of an MSRC page should not be read as “this is a Windows vulnerability.” It is better read as evidence that Microsoft now has to track, surface, and sometimes remediate vulnerabilities across a hybrid operating system estate. The Windows admin’s job has expanded from patching Windows to understanding which Linux kernels are hiding behind Windows-adjacent workflows.
The Missing CVSS Score Is Not Permission to Ignore It
As of the NVD publication date, CVE-2026-43306 had no NVD-provided CVSS v4.0, v3.x, or v2.0 score. That will cause predictable behavior in vulnerability management dashboards. Some tools will push it to the bottom because it lacks a numerical severity. Others will inherit vendor ratings later. Still others will flag it simply because it is a kernel CVE and let administrators sort out the meaning manually.The absence of a score is not the same as the absence of risk. It means the public enrichment process has not yet attached a standard severity model to the record. In kernel land, especially under the Linux kernel CNA process, CVEs are often tied to fixes after they land in stable trees, and the security meaning can be narrower than the identifier alone implies.
That makes CVE-2026-43306 a good example of why CVSS is a sorting aid, not a substitute for engineering judgment. A local crash reachable only through specialized BPF self-test conditions is very different from a weaponized local privilege escalation circulating in exploit kits. But a kernel oops in a privileged subsystem is also not a harmless documentation typo.
Security teams should ask practical questions before they panic. Is the affected kernel version deployed? Is BPF crypto enabled and usable in the relevant environment? Is
CONFIG_CFI enabled? Can unprivileged users load BPF programs, or is BPF restricted to privileged services? Is the platform a developer workstation, a container host, a production Kubernetes node, or a locked-down appliance?The Patch Tells a Better Story Than the CVE Text
The public references attached to the CVE point to stable kernel commits, which suggests the fix has been propagated across multiple maintained branches rather than existing only as an upstream development change. That matters because kernel CVEs are often operationally resolved through distribution updates, cloud image refreshes, vendor kernel builds, and long-term support backports. Most administrators will never apply the exact upstream commit; they will consume it through Red Hat, Ubuntu, Debian, SUSE, Azure Linux, WSL, or another vendor channel.The commit subject — “bpf: crypto: Use the correct destructor kfunc type” — is unusually descriptive and refreshingly unmelodramatic. It says this is a correctness fix in BPF crypto object lifetime handling. There is no need to embellish it into a catastrophe.
Still, the patch is not trivial in the way a typo fix is trivial. Destructor registration is about ownership and cleanup. In BPF, object lifetime bugs are exactly where verifier assumptions, reference counts, map storage, and kernel memory management meet. A release path with the wrong callable type is the sort of plumbing defect that looks small because the abstraction is doing so much work.
The important operational point is that administrators should not attempt to outsmart this class of issue with local mitigations unless a vendor specifically recommends one. Disabling BPF broadly can break observability and security tooling. Disabling crypto-related kernel features can break workloads. The clean answer is the boring one: take the vendor kernel update when it arrives for your platform.
This Is Not Copy Fail, and That Difference Matters
The Linux kernel security news cycle has recently been dominated by much louder vulnerabilities, including actively discussed local privilege escalation flaws with simple proof-of-concept exploit stories. CVE-2026-43306 does not belong in that category based on currently public information. It is a CFI-triggered type mismatch in BPF crypto destructor handling, not a widely advertised path to root.That distinction is important because kernel CVE fatigue is real. If every new kernel CVE is treated as an emergency, administrators stop listening. If every low-drama CVE is ignored, latent reliability and security problems accumulate until a future update becomes far harder to reason about.
The better model is triage by exposure and consequence. A kernel crash that requires a particular configuration and code path may rank below an exploited privilege escalation. But it should still be patched in normal kernel maintenance windows, especially on systems that deliberately enable hardening options such as CFI. If you went to the trouble of running a hardened kernel, you probably do not want known CFI failures lurking in the object cleanup path.
This is also where developer workstations deserve more attention than they usually get. BPF self-tests, custom kernels, observability agents, and experimental networking stacks are often found in engineering environments before they are found in production. A bug that surfaced under self-test conditions may be most visible to the very teams building the next layer of platform automation.
BPF’s Security Model Is Becoming a Product Surface
For years, administrators could treat BPF as either a kernel feature they did not use or a mysterious implementation detail of performance tools. That era is over. BPF now underpins container networking, runtime security, low-overhead telemetry, tracing, DDoS mitigation, policy enforcement, and increasingly ambitious platform features.That means BPF bugs have to be read differently from ordinary niche kernel defects. Even when the immediate impact is narrow, the subsystem sits in a privileged position. It is a programmable interface into the kernel guarded by a verifier and constrained by type metadata. When something goes wrong there, the blast radius depends heavily on who can load programs, what helpers or kfuncs are available, and how the distribution configures unprivileged access.
Most mainstream distributions have spent years tightening unprivileged BPF access because the feature is too powerful to expose casually. Cloud platforms and container hosts often run BPF-based agents with elevated privileges because the operational value is enormous. Security vendors use BPF to inspect behavior with less overhead than older kernel-module approaches. Observability vendors use it to extract signal from production systems without recompiling applications.
CVE-2026-43306 is therefore not alarming because this particular bug appears catastrophic. It is notable because it shows how refined the BPF contract has become. A destructor’s exact function type is now part of the security boundary, and the kernel’s hardening stack is prepared to enforce it.
Windows Admins Should Inventory the Linux They Already Own
The practical WindowsForum angle is not that Windows 11 suddenly becomes vulnerable because a Linux kernel CVE appeared in the MSRC ecosystem. The practical angle is that many Windows-first organizations have accumulated Linux kernels without building equivalent Linux kernel governance. WSL on developer machines, Linux build containers, AKS nodes, Azure Linux images, GitHub or self-hosted runners, firewall appliances, and storage systems all complicate the asset picture.For WSL users, the right answer is usually to keep WSL and its kernel package updated through Microsoft’s supported update channels. For enterprise-managed developer workstations, it is worth confirming whether WSL kernel updates are actually flowing under your endpoint management policy. Developers who manually pin or replace kernels for testing can drift away from the supported path.
For Azure and container environments, the answer is more conventional but more urgent: track the distribution kernel packages and node images you actually deploy. A CVE attached to upstream Linux does not tell you whether your managed Kubernetes nodes, marketplace images, or custom golden images have received the relevant backport. The version string alone may not tell the full story either, because enterprise distributions often backport fixes without moving to the upstream version where the fix first appeared.
For security teams, this is a reminder to correlate kernel CVEs with configuration data. A scanner that reports CVE-2026-43306 on every Linux host without knowing whether BPF crypto or CFI are relevant is creating noise. A process that ignores the CVE because “NVD score: N/A” is creating blind spots. The goal is neither panic nor dismissal; it is informed maintenance.
The Real Lesson Is That Kernel Hardening Has Consequences
Security hardening is often sold as pure upside: enable a flag, get more protection. In practice, hardening turns undefined assumptions into failures. That is good, but it is not free. Code paths that worked by convention can break when the compiler, runtime, or verifier insists on a stricter contract.CVE-2026-43306 is a clean example of that tradeoff. CFI did not create the type mismatch. It exposed it. The kernel fix did not sidestep the hardening feature. It made the affected BPF crypto destructor path conform to the type CFI expected.
That is the direction kernel development should move. Modern operating systems are too large and too exposed to rely on informal correctness. When a kernel subsystem exports programmable functionality to privileged or semi-privileged consumers, exact types and lifetimes are not academic details. They are part of the defense.
There is a parallel here for Windows readers. Microsoft has spent years pushing similar ideas through virtualization-based security, kernel-mode code integrity, hardware-enforced stack protection, and driver signing requirements. Every one of those technologies has broken some legitimate code along the way. The long-term answer has not been to abandon enforcement; it has been to force the ecosystem to meet stricter contracts.
The Small CVE That Belongs in the Patch Queue
CVE-2026-43306 should not be treated as a five-alarm incident unless later analysis changes the impact story. It should be treated as a kernel correctness and hardening compatibility fix that deserves normal patch discipline. That means understanding where Linux kernels exist in your Windows-adjacent estate and making sure the stable updates reach them.The most concrete lessons are straightforward:
- CVE-2026-43306 was published by NVD on May 8, 2026, and currently lacks an NVD CVSS score.
- The bug involves a BPF crypto destructor kfunc registered with a type that conflicts with CFI’s indirect-call checks.
- The public description indicates a kernel oops under
CONFIG_CFI, not a confirmed remote exploit or public privilege escalation chain. - The upstream-style fix preserves verifier expectations by adding a correctly typed stub rather than loosening the BPF-facing release function.
- Windows administrators should check WSL, Azure, containers, CI systems, and Linux-based security tooling before assuming a Linux kernel CVE is irrelevant.
- The appropriate remediation path is vendor kernel updates, not improvised local changes to BPF or crypto subsystems unless a platform vendor explicitly recommends them.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center