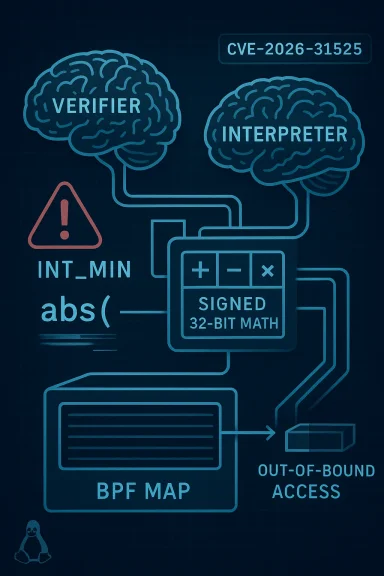
The Linux kernel’s BPF interpreter has a newly disclosed flaw, tracked as CVE-2026-31525, that exposes a subtle but important mismatch between the interpreter and the verifier when handling signed 32-bit division and modulo on
That tension between flexibility and correctness is what makes BPF bugs so interesting. The verifier tries to prove that a program is safe before it runs, while the interpreter or JIT is responsible for executing the instructions exactly as the kernel expects. If those two layers disagree, even slightly, the result can be dangerous. In this case, the verifier’s abstract interpretation is mathematically correct, but the interpreter’s use of the kernel
The kernel’s BPF ISA documentation makes the intended behavior clear. For 32-bit signed operations,
This is also part of a broader pattern in kernel security. Many recent Linux CVEs have been less about headline-grabbing code execution and more about the quiet, persistent danger of bad assumptions in low-level math, concurrency, or state tracking. A one-line arithmetic shortcut can be just as serious as ait breaks the contract between two kernel subsystems. CVE-2026-31525 fits that mold exactly.
The core issue is the interpreter’s use of
The detail that matters most is not just that the result is wrong, but that the result is wrong in a way the verifier does not expect. The verifier’s
Why
The Linux documentation for BPF signed modulo and division shows that the ISA already expects special-case handling around this boundary. In other words, the architecture knows the corner case exists; the bug is that the interpreter’s implementation missed it in one particular code path. That is why this issue is narrow in scope but still serious in security terms.
A mismatch like this is especially troubling because it can be subtle. Nothing necessarily crashes on the first execution, and nothing in the program looks obviously malicious. The issue emerges from a narrow arithmetic edge case, which makes it easier to overlook during review and harder to catch with ordinary test workloads. That is precisely why kernel fuzzing and selftests matter.
This is one of those fixes that looks deceptively small but is actually doing a lot of work. The old code path assumed that
The role of
The new helper is the heart of the fix. By casting to
This is also a good example of why kernel code often needs type-specific helpers rather than generic arithmetic macros. A macro like
At the same time, narrow scope should not be mistaken for low importance. Kernel vulnerabilities often live in a very small corner of the codebase but still have broad consequences because they sit on trusted execution paths. BPF is one of those places where a tiny arithmetic discrepancy can have system-wide significance.
The advisory says this mismatch can be exploited for out-of-bounds map value access. In plain terms, that means a BPF program may be able to read or write beyond the boundaries of a map value because the runtime result differs from the verifier’s model. That is a serious, even if it does not immediately imply remote code execution.
In security engineering, the phrase “just an arithmetic bug” is often misleading. Once the bug influences memory access decisions, it stops being merely arithmest-boundary problem. That is why CVEs like this deserve attention even when the root cause is a single bad helper call.
That coherence is one reason the Linux BPF selftests were updated alongside the fix. The merge log explicitly notes new tests for
Kernel maintainers generally prefer patches like this when possible. They are easy to audit, easy to backport, and less likely to introduce collateral behavior changes. This one is especially attractive because it does not alter the BPF ISA semantics; it merely ensures thews them correctly.
That matters for stable trees, vendor kernels, and enterprise rollouts. When a security fix is narrowly scoped and semantically aligned with the specification, it is more likely to be backported quickly and with fewer surprises. In other words, this is the kind of patch administrators hope to see.
That is exactly how mature kernel hardening should work: fix the bug, encode the edge case, and make the bug harder to recreate later. The test suite becomes part of the security boundary.
The BPF ecosystem has evolved from classic packet filtering into a broad programmable platform for observability, networking, tracing, and security enforcement. As the feature set expanded, so did the number of places where and runtime behavior had to remain perfectly aligned. The larger and more capable BPF becomes, the more expensive any implementation drift becomes.
In practice, BPF bugs often emerge where safety logic meets implementation shortcuts. The verifier reasons about an idealized model, while the interpreter must carry out the actual machine-level math. The more those two layers depend on exact corner-case behavior, the more likely it is that a bug will appear in the crack between them.
That is important because it tells operators the issue is real, understood, and already on the patch path. The practical question is not whether a fix exists; it is whether your kernel build includes it yet. That is where vendhe real story.
The issue is especially relevant for organizations that deploy kernel-integrated tooling, custom observability pipelines, or advanced networking components that depend on BPF. In those environments, a verifier/interpreter mismatch is not an academic concern. It is a direct challenge to the trust model that keeps programmable kernel features safe.
This is also a reminder that vulnerability management should not depend solely on the severity score at publication time. When the technical description already indicates a path to unsafe memory access, waiting for a final score can create unnecessary delay. Technical impact should drive triage.
The selftests added upstream are a good clue that the issue is deterministic enough to reproduce. That makes validation in staging environments more practical than it often is for kernel bugs. If you run BPF-heavy workloads, use that to your advantage and confirm the patched behavior explicitly.
Modern Linux desktops increasingly include subsystems and tooling that rely on BPF indirectly, especially through observability, security, or performance features. So while consumers are less likely to trigger the flaw intentionally, they still benefit from the fix as part of routine kernel maintenance. Security patches in this category are often about reducing latent risk across the platform rather than protecting a single obvious workflow.
The bug’s narrow trigger should not encourage important kernel fixes are precisely this kind of edge-case correction: small on the surface, meaningful underneath. Consumers benefit most when those fixes arrive before any realistic exploitation path becomes common knowledge.
That unpredictability complicates triated to dismiss the bug because they have not observed it in their own environment. That would be a mistake. The whole point of the patch is that the old code was relying on behavior the kernel cannot safely assume.
A second thing to watch is whether maintainers use this disclosure to audit other BPF interpreter helpers for similar signed-overflow traps. Kernel bugs often arrive in families, and once one helper is corrected, nearby code paths sometimes turn out to share the same assumption. That sort of follow-up is one of the healthiest outcomes of a CVE like this.
A third thing to watch is how security teams classify the issue in their tooling. Some products will reduce the urgency if no CVSS score is attached yet, but that would be short-sighted here. The disclosure already describes a plausible path to out-of-bounds access, and that should be enough to move the issue into active remediation.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
INT_MIN. The bug is not a dramatic memory corruption primitive on its face; it is a correctness failure rooted in undefined behavior, and that is exactly why it matters. In the wrong hands, the mismatch can be turned into out-of-bounds map value access, which is the kind of kernel-adjacent problem that security teams should treat with respect. The upstream fix is narrowly scoped, but it touches a foundational assumption in how the interpreter handles signed arithmetic. has always occupied an unusual place in the Linux kernel. It is a programmable execution environment that runs user-supplied logic in a privileged context, which means the kernel has to balance flexibility, performance, and hard safety guarantees at the same time. The official kernel documentation emphasizes that BPF is capable of running untrusted programs in a privileged context, and that the arithmetic semantics for signed division and modulo are explicitly defined for the instruction set.That tension between flexibility and correctness is what makes BPF bugs so interesting. The verifier tries to prove that a program is safe before it runs, while the interpreter or JIT is responsible for executing the instructions exactly as the kernel expects. If those two layers disagree, even slightly, the result can be dangerous. In this case, the verifier’s abstract interpretation is mathematically correct, but the interpreter’s use of the kernel
abs macro creates a divergence when the destination contains S32_MIN. That is the kind of edge case that rarely shows up in ordinary testing, on the boundary of safe execution.The kernel’s BPF ISA documentation makes the intended behavior clear. For 32-bit signed operations,
SDIV and SMOD have precise semantics, including special handling for INT_MIN divided by -1 and INT_MIN modulo -1. The point is not merely to avoid a crash; it is to preserve deterministic behavior across architectures and execution modes. When an interpreter strays from those semantics, it can invalidate the verifier’s assumptions and open the door to memory safety problems.This is also part of a broader pattern in kernel security. Many recent Linux CVEs have been less about headline-grabbing code execution and more about the quiet, persistent danger of bad assumptions in low-level math, concurrency, or state tracking. A one-line arithmetic shortcut can be just as serious as ait breaks the contract between two kernel subsystems. CVE-2026-31525 fits that mold exactly.
 What the Vulnerability Actually Is
What the Vulnerability Actually Is
The core issue is the interpreter’s use of abs on a signed 32-bit operand. The bug report says the kernel’s abs macro is documented to behave undefinedly when the input is the type minimum, and that abs((s32)DST) on S32_MIN can return the same negative value unchanged on arm64 and x86. That vanded to u64 and fed into do_div, which produces the wrong answer.The detail that matters most is not just that the result is wrong, but that the result is wrong in a way the verifier does not expect. The verifier’s
scalar32_min_max_sdiv logic computes the mathematically correct result for range tracking. So the kernel ends up with one view of the program at verification time and a different one at gap is where exploitability enters the picture.Why INT_MIN is the trigger
INT_MIN is dangerous because it cannot be negated within the same signed type without overflow. That is a classic two’s-complement trap. The interpreter’s old approach effectively tried to use a signed absolute value where the input domain includes the one value that signed arithmetic cannot represent cleanly after negation. The result is undefined behavior, and undefined behavior is exactly the sort of thing kernel code should avoid at all costs.The Linux documentation for BPF signed modulo and division shows that the ISA already expects special-case handling around this boundary. In other words, the architecture knows the corner case exists; the bug is that the interpreter’s implementation missed it in one particular code path. That is why this issue is narrow in scope but still serious in security terms.
Why the verifier mismatch matters
The verifier is effectively the safety gate for BPF programs. If it believes a value stays inside a safe range, it may allow access that would otherwise be rejected. When the interpreter then computes a differ the program can walk into memory it should not have been allowed to touch. That is the classic shape of a verifier/interpreter mismatch, and in BPF land, that is a red flag.A mismatch like this is especially troubling because it can be subtle. Nothing necessarily crashes on the first execution, and nothing in the program looks obviously malicious. The issue emerges from a narrow arithmetic edge case, which makes it easier to overlook during review and harder to catch with ordinary test workloads. That is precisely why kernel fuzzing and selftests matter.
How the Bug Was Introduced
The advisory points directly at the interpreter’ssdiv32 and smod32 handlers. Those handlers used the kernel abs macro on s32 operands, and the bug was present in all eight call sites that needed fixing. The patch introduces abs_s32(ed overflow by casting tou32` before negating. That change preserves correctness without relying on undefined behavior.This is one of those fixes that looks deceptively small but is actually doing a lot of work. The old code path assumed that
abs would be “good enough” for signed 32-bit math. The new code makes the type boundary explicit and removes the possibility that a mini leak into the rest of the arithmetic chain unchanged. In kernel terms, that is a very clean repair.The role of abs_s32
The new helper is the heart of the fix. By casting to u32 before negation, it avoids the undefined signed overflow that can occur when handling the minimum signed integer. That means S32_MIN is treated as a raw bit pattern, not as a value tn signed space. It is a small implementation detail with a large safety payoff.This is also a good example of why kernel code often needs type-specific helpers rather than generic arithmetic macros. A macro like
abs may be fine for everyday code, but kernel execution paths that must be exact across architectures need moPrecision is not optional when the verifier is involved.Why only 32-bit signed handlers were affected
The description is explicit thats32 is the only affected case. The 64-bit signed division and modulo handlers do not use abs, so they avoid this particular pitfall. That matters because it narrows the blast radius and helps administrathey do and do not need to prioritize.At the same time, narrow scope should not be mistaken for low importance. Kernel vulnerabilities often live in a very small corner of the codebase but still have broad consequences because they sit on trusted execution paths. BPF is one of those places where a tiny arithmetic discrepancy can have system-wide significance.
Why This Becomes a Security Issue
The important phrase in the disclosure is “verifier/interpreter mismatch.” That is the security story, not just the arithmetic bug itself. If the verifier computes the mathematically correct result and the interpreter compuan attacker can steer execution into a state the verifier never intended to permit.The advisory says this mismatch can be exploited for out-of-bounds map value access. In plain terms, that means a BPF program may be able to read or write beyond the boundaries of a map value because the runtime result differs from the verifier’s model. That is a serious, even if it does not immediately imply remote code execution.
Why out-of-bounds map access is so concerning
BPF maps are a major mechanism for sharing state between BPF programs and userspace. If bounds assumptions break, the kernel can end up exposing or manipulating data outside the intended region. That kind of flaw can lead to information disclosure, denial of service, or further privilege abuse depending on the surrounding conditions.In security engineering, the phrase “just an arithmetic bug” is often misleading. Once the bug influences memory access decisions, it stops being merely arithmest-boundary problem. That is why CVEs like this deserve attention even when the root cause is a single bad helper call.
The significance of interpreter-versus-JIT consistency
BPF’s security model depends on every execution path honoring the same semantics. If the interpreter and verifier disagree, but the JIT does not, or vice versa, the kernel’s trust model becomes uneven. The fix for CVE-2026-31525 is therefore about more than one code path; it is about keeping the whole BPF stack coherent.That coherence is one reason the Linux BPF selftests were updated alongside the fix. The merge log explicitly notes new tests for sdiv32/smod32 with INT_MIN dividend, which is a strong sign that maintainers want the behavior locked down and regression-resistant. That is a good sign for downstream stability. ([linux.googlesource.com](Diff - d5273fd3ca0bf0b59fff49fb59237440998fbec8^1..d5273fd3ca0bf0b59fff49f - linux/kernel/git/torvalds/linux - Git at Google
The Patch and Its Design Choices
The upstream change is simple but elegant: replace all eightabs((s32)...) call sites in the interpreter’s signed 32-bit division and modulo handlers with abs_s32. That keeps the fix localized, avoids redesigning the arithmetic flow, and removes the undefined behavior at the root.Kernel maintainers generally prefer patches like this when possible. They are easy to audit, easy to backport, and less likely to introduce collateral behavior changes. This one is especially attractive because it does not alter the BPF ISA semantics; it merely ensures thews them correctly.
Why the patch is low-risk
The fix does not change how valid inputs are interpreted. It only changes how theINT_MIN edge case is handled so that the interpreter does not wander into undefined behavior. That is a surgical fix, not a behavioral rewrite.That matters for stable trees, vendor kernels, and enterprise rollouts. When a security fix is narrowly scoped and semantically aligned with the specification, it is more likely to be backported quickly and with fewer surprises. In other words, this is the kind of patch administrators hope to see.
Why the selftests matter
The presence of new selftests in the merge log is important because it shows the issue was considered worth encoding as a regression test, not just a one-off patch. Tests forsdiv32/smod32 with INT_MIN dividend help ensure future changes do not reintroduce the same undefined-behavior trap.That is exactly how mature kernel hardening should work: fix the bug, encode the edge case, and make the bug harder to recreate later. The test suite becomes part of the security boundary.
Historical Context
This is not the first time BPF arithmetic semantics have needed careful attention. The BPF instruction set documentation explicitly defines how division and modulo should behave, including corner cases like division by zero andINT_MIN with -1. That sort of specificity exists because kernel implementers have learned, repeatedly, that “obvious” math is not enough in low-level execution engines.The BPF ecosystem has evolved from classic packet filtering into a broad programmable platform for observability, networking, tracing, and security enforcement. As the feature set expanded, so did the number of places where and runtime behavior had to remain perfectly aligned. The larger and more capable BPF becomes, the more expensive any implementation drift becomes.
Why edge cases keep resurfacing
Signed arithmetic is inherently tricky because the minimum negative value has no positive counterpart in the same signed range. That means helper functions that seem harmless in ordinary code can become landmines in kernel arithmetic, especially when the result feeds later range analysis. Boundary conditions are where abstractions break down. ([kernel.ol.org/doc/html/latest/bpf/standardization/instruction-set.html))In practice, BPF bugs often emerge where safety logic meets implementation shortcuts. The verifier reasons about an idealized model, while the interpreter must carry out the actual machine-level math. The more those two layers depend on exact corner-case behavior, the more likely it is that a bug will appear in the crack between them.
Why the timing of publication matters
The CVE record was recently published and added to NVD, and the advisory is already reflected in upstream references. The merge log also shows the fix landing alongside other BPF fixes, which suggests it was handled as part of a coordinated hardening pass rather than as an isolated emergency patch. ([linux.go://linux.googlesource.com/linux/kernel/git/torvalds/linux/%2B/d5273fd3ca0bf0b59fff49fb59237440998fbec8%5E1..d5273fd3ca0bf0b59fff49fb59237440998fbec8/))That is important because it tells operators the issue is real, understood, and already on the patch path. The practical question is not whether a fix exists; it is whether your kernel build includes it yet. That is where vendhe real story.
Enterprise Impact
For enterprises, the biggest question is exposure. Not every Linux system relies on BPF in the same way, and not every workload allows untrusted BPF program loading. But the kernel’s BPF subsystem is widely used across modern observability stacks, networkim features, so the affected code deserves attention even when the risk seems niche.The issue is especially relevant for organizations that deploy kernel-integrated tooling, custom observability pipelines, or advanced networking components that depend on BPF. In those environments, a verifier/interpreter mismatch is not an academic concern. It is a direct challenge to the trust model that keeps programmable kernel features safe.
What security teams should care about
Security teams should classify this as a kernel correctness issue with real exploitation potential, not as a harmless arithmetic cleanup. The disclosure specifically ties the bug to out-of-bounds access, which means it is not merely theoretical. That makes patch prioritization easier: if BPF is in use, this belongs on the shortlist.This is also a reminder that vulnerability management should not depend solely on the severity score at publication time. When the technical description already indicates a path to unsafe memory access, waiting for a final score can create unnecessary delay. Technical impact should drive triage.
What operations teams should verify
Operations teams should verify whether their distro kernel has picked up the fix, whether the patch is in the stable branch they use, and whether their BPF usage patterns make exposure realistic. For managed fleets, the important distinction is not just kernel version number,or backport includes the relevant interpreter change.The selftests added upstream are a good clue that the issue is deterministic enough to reproduce. That makes validation in staging environments more practical than it often is for kernel bugs. If you run BPF-heavy workloads, use that to your advantage and confirm the patched behavior explicitly.
Consumer Impact
For typical desktop users, the direct impact is probably lower than for enterprise Linux deployments. Many consumer systems do not load arbitrary BPF programs, and many uact with the relevant interpreter paths directly. That said, “unlikely” is not the same as “irrelevant.”Modern Linux desktops increasingly include subsystems and tooling that rely on BPF indirectly, especially through observability, security, or performance features. So while consumers are less likely to trigger the flaw intentionally, they still benefit from the fix as part of routine kernel maintenance. Security patches in this category are often about reducing latent risk across the platform rather than protecting a single obvious workflow.
The practical consumer takeaway
If your distribution ships the patched kernel, install it. If you maintain a mixed Linux environment, treat this as a reminder that “kernel update” is not just enterprise language. It is also a consumer reliability issue, because bugs in privileged execution engines can still affect system stability and hardening posture. Low visibility does not mean low value.The bug’s narrow trigger should not encourage important kernel fixes are precisely this kind of edge-case correction: small on the surface, meaningful underneath. Consumers benefit most when those fixes arrive before any realistic exploitation path becomes common knowledge.
Strengths and Opportunities
The good news is that the fix is disciplined, minimal, and well-aligned with the documented semantics of BPF arithmetic. It corrects the implementation without changing the intended behavior of signed division and modulo. That makes it easier to trust, easier to backport, and easier to verify.- The patch is surgical rather than architec*undefined behavior** at the source.
- It preserves the verifier’s mathematical model.
- It is straightforward to backport into stable kernels.
- The new selftests improve regression resistance.
- The issue is well-suited to code review and auditing.
- It reinforces the value of type-specific helpers in kernel math.
- It may prompt a wider review of BPF arithmetic edge cases.
Why this is a strong maintenance outcome
A fix like this reduces future ambiguity. Onceabs_s32 exists and the call sites use it consistently, the intent of the code becomes clearer to future maintainers. That kind of self-documenting repair is often one of the strongest signs of a healthy kernel hardening process.Why it matters beyond this one CVE
The broader opportunity is to audit similar arithmetic helpers for minimum-value edge cases. Kernel code is full of places where signed and unsigned boundaries meet, and the safe from making those boundaries explicit. This CVE is a reminder that such audits are not merely academic.Risks and Concerns
The biggest concern is the verifier/interpreter mismatch itself. Even a narrow arithmetic bug can become a security issue if the verifier true runtime engine produces another. That mismatch is the exact sort of condition that attackers look for in privilege-sensitive subsystems.- The flaw can lead to out-of-bounds map value access.
- The bug exists on a path involving untrusted programs in a privileged context.
- Undefined behavior can vary subtly across architectures and builds.
- Enterpri if they rely only on version strings.
- Vendor backport timing can differ across supported branches.
- The terse CVE description may lead some teams to underestimate impact.
- Similar arithmetic edge cases may still exist elsewhere in BPF code.
Why the undefined behavior angle is tricky
Undefined behavior is especially dangerous in kernel code because it can appear stable in testing yet still behave differently on different architectures, compilers, or optimization settings. The advisory explicitly notes thatabs((s32)DST) on S32_MIN can behave unexpectedly on arm64 and x86. That means the bug is not just theoretical; it is architecture-sensitive.That unpredictability complicates triated to dismiss the bug because they have not observed it in their own environment. That would be a mistake. The whole point of the patch is that the old code was relying on behavior the kernel cannot safely assume.
Why the verifier gap is operationally meaningful
The verifier is one of the main reasons BPF is safe enough to use iassumptions are undermined, the entire trust model weakens. That is why even a narrow mismatch deserves careful patching and validation. This is a correctness bug with security consequences, not a mere edge-case quirk.What to Watch Next
The most important near-term signal is downstream adoption. Because the upstream fix is already in the Linux kernel tree and selftests were added for the exact edge case, the key question now is which vendor kernels have backported the change and which have not. That is especially important for long-term-support distributions where version numbers may not obviously reflect the patch status.A second thing to watch is whether maintainers use this disclosure to audit other BPF interpreter helpers for similar signed-overflow traps. Kernel bugs often arrive in families, and once one helper is corrected, nearby code paths sometimes turn out to share the same assumption. That sort of follow-up is one of the healthiest outcomes of a CVE like this.
A third thing to watch is how security teams classify the issue in their tooling. Some products will reduce the urgency if no CVSS score is attached yet, but that would be short-sighted here. The disclosure already describes a plausible path to out-of-bounds access, and that should be enough to move the issue into active remediation.
- Confirm whether your distro kernel includes the abs_s32 fix.
- Check whether BPF workloads are enabled in your environment.
- Validate that vendor backports include the interpreter change, not just a nearby BPF fix.
- Watch for follow-up BPF selftests and adjacent arithmetic hardening.
- Prioritize systems that load or manage untrusted BPF programs.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center