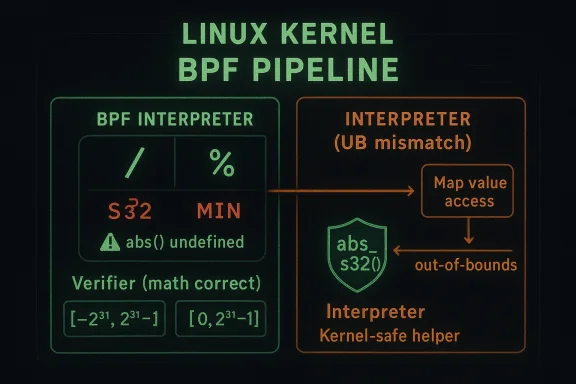
In the Linux kernel, CVE-2026-31525 has exposed a subtle but serious correctness flaw in the BPF interpreter’s signed 32-bit division and modulo paths. The issue is not a classic memory corruption bug; it is a math bug with security consequences, triggered when the interpreter handles
The newly published CVE describes a very specific failure mode. The interpreter’s signed 32-bit division and modulo handlers use the kernel
This kind of bug maifier is supposed to be the interpreter’s guardrail. If the verifier says a program is safe, the interpreter must execute the same semantics. When the two disagree, the kernel can end up approving a program under one mathematical model and running it under another. That is the kind of inconsistency that has historically underpinned many BPF exploitation chains. The exploit primitive is not the division itself; it is the broken assumption that the verifier and runtime agree.
The upstream fix is elegant. Rather thansue with ad hoc checks, maintainers introduced
This is also one of those CVEs where the technical wording tehe underlying engineering philosophy. The kernel team did not redesign BPF arithmetic; they corrected a single, well-isolated undefined behavior issue and aligned the interpreter with the verifier. That is the hallmark of a fix that is both backportable and security-relevant.
BPF security has matured dramatically over the last several kernly days, the key concerns were straightforward: could the verifier be tricked, could a helper be misused, and could a program escape the intended sandbox? Today the attack surface is more subtle. BPF programs interact with more helpers, more maps, more JIT and interpreter paths, and more architecture-specific details. That means a defect can be mathematically tiny but still operationally serious. CVE-2026-31525 fits that mold perfectly.
At a high level, the bug arises because the interpreter and verifier are doing two different things wite verifier’s abstract interpretation logic, specifically the
The kernel description makes the exploitation concern explicit: the mismatch can be exploited for out-of-bounds map value aclly important because BPF maps are foundational to a huge amount of kernel and userspace coordination. If a malicious or carefully crafted program can reach an out-of-bounds map access path, the impact can range from denial of service to information disclosure to privilege escalation, depending on the surrounding conditions and kernel hardening. The CVE record itself focuses on the undefined behavior and the mismatch, while the security implication comes from how BPF uses map access as part of its normal execution model.
The fix also reveals how kernel developers think about correctness. The maintainers did not introduce a special-case branch only for one architect try to “fix”
When
The significance here is not just “bad math happened.” The significance is that the interpreter and verifier are supposed to be two views of the same execution model. The verifier is the policy engine; the inution engine. If one believes a value is bounded and non-problematic while the other sees a wrapped or sign-extended edge case, the safety guarantee collapses. That mismatch can be especially dangerous in a system like BPF, where the verifier’s approval is what makes the program eligible to run at all. A verifier mismatch is often the real vulnerability, not the low-level bug that caused it.
Another reason this issue is notable is that it is narrowly scoped to signed 32-bit arithmetic. The CVE text explicitly says
Why
The kernel fix,
ismatch Matters
The BPF verifier is supposed to enforce a contract: if a program is accepted, the interpreter or JIT should execute it within the constraints the verifier modeled. When those two systems diverge, the verifier becomes a liability rather than a safety net. CVE-2026-31525 rning because the verifier’s logic was not obviously broken; instead, the runtime path was subtly wrong. That makes the bug harder to spot in code review and harder to catch with casual testing.
The description points specifically to
This is why BPF vulnerabilities are often dangerous even when they start as “just arithmetic.” The verifier is not a performance hint; it is the security boundary. A mismatch can undermine all the later reasoning about bounds checks, helper safety, and access constraints. In a subsystem as widely used as BPF, that is enough to justify rapid patching eveSS score is assigned. The danger is systemic, not local.
The broader security lesson is that abstract interpretation and concrete execution must stay synchronized. If the verifier handles corner cases one way and the interpreter another way, an attacker may be able to choose values that pass one model but fail the other. That class of bug has repeatedly shown up in BPF history because the design is inherently dual-layered: a progically approved and dynamically executed.
This also explains why the issue is security-relevant even though it seems narrow. Many kernel bugs become exploitable only when a particular edge value interacts with a trusted helper or storage abstraction. Here, the edge value is
The patch also bs((s32)...)
There is also a nice separation of concerns in the fix. The 64-bit division and modulo handlers are left alone because they are not using the problematic
The deeper point is that the fix respects the kernel’s arithmetic model. It does not reinterpretion or modulo, and it does not add artificial guardrails that could distort output for valid values. Instead, it makes the edge case behave like the rest of the domain. That is the difference between remediation and alteration.
Why
A naive guard like “if value is
A helper-based fix also improves maintainability. Future reviewers can see that thisy to compute a 32-bit absolute value safely in kernel code. That reduces the odds that another developer will reintroduce the same bug in a nearby call site six months later. In kernel security work, making the safe path obvious is almost as important as fixing the bug itself.
The practical impact depends on how BPF is deployed. If the workload uses only curated programs from trussure is narrower. If the platform allows program loading through automation, CI/CD, telemetry agents, or multi-tenant observability features, then the chance of a maliciously crafted edge case rises. The mismatch described in the CVE is especially relevant in shared environments because it turns a nominally verified program into one that may behave differently at runtime. That is the kind of bug that security teams hate to reason about after the fact.
Enterprises should also pay attention to vuse the CVE is rooted in an interpreter implementation detail, the actual fixed version may not line up neatly with upstream kernel release numbers. The more relevant question is whether the vendor kernel includes the
There is also an operational angle. BPF issues often show up first as strange, inconsistent, or hard-to-reproduce behavior rather than as an immediate crash. That can waste engineering time, especially when the bug only appeaputs or program shapes. If a team relies on BPF for production policy, the safest stance is to treat this as a real patch item, not a theoretical edge case.
Developers and kernel-adjacent engineers should take this as a reminder that undefined behavior does not stay local. In C and kernel code, the temptation is often to rely on helper macros whose limitations are easy to overlook. Buthe worst bugs often happen when two layers each behave “correctly” according to different assumptions. The compiler, interpreter, and verifier can all be doing something reasonable and still create a security bug in combination.
There is also a lesson for anyone writing BPF programs: avoid edge-case arithmetic unless you can prove how the verifier and runtime will interpret it. Signed division and modulo on boundary values are especially risky because they interact with both language-level and k. Even when the program looks mathematically sound, the implementation details can turn it into an exploit primitive.
For developers building tooling around BPF, this CVE underscores why test coverage should include pathological values. Values near zero are obvious. Values at the extremes are often forgotten. Yet those extremes are exactly where undefined behavior, verifier divergence, and architecture-specific surprises tend to show up. If you do not test
The problem also illustrates why undefined behavior is so dang A function can appear to work on common architectures like x86 and arm64, and yet still violate the language and kernel assumptions underneath. That creates a false sense of stability. When a value like
The kernel community has long known that helper macros can be loaded with hidden assumptions. The good news is that the fix pattern here is strong: create a helper that states the intended behavior clearly and make the call sites use it consistently. That is the sort of change that prevents recurrence rather than just suppressing one manifestation. It also makes the code easier to audit in the futury benefit in its own right.
future BPF hardening work will continue to focus on semantic consistency. The more the verifier, interpreter, and JIT share assumptions, the less room there is for mismatch-based exploitation. In that sense, CVE-2026-31525 is not just a patch note. It is a reminder that the kernel’s security model depends on exactness, especially at the boundaries where human intuition about math is least reliable. *Boundary conditions are where kernel trust is wonned behavior is a security problem, not a compiler footnote.
There is also a longer-term maintenance risk. Once a helper like
The next thing to watch is whether this CVE prompts broader inspection of BPF arithmetic helpers and verifier assumptions. The existence of a clean
Security teams should also pay attention to whether this bug appears in curated hardening advisories from distributions and enterprise vendors. Since BPF is used heavily in observability and network enforcement stacks, a fix that lands quietly can still have meaningful operational vrm, patch priority should be driven by whether BPF is enabled and whether the environment permits programs that can reach these arithmetic paths.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
S32_MIN and relies on an abs() macro that is explicitly undefined for that value. That mismatch between the interpreter and the verifier can lead to out-of-bounds map value access, which is exactly the sort of boundary-condition defect that kernel attackers and defenders both care about. The fix is small, surgical, and telling: add a safe abs_s32() helper and replace the eight affected call sites in the interpreter. has become one of the most important programmable subsystems in the Linux kernel. It powers observability, networking policy, packet filtering, tracing, and a growing number of security-sensitive workloads. That popularity is also what makes BPF bugs worth close attention: a flaw in the interpreter or verifier can have impact far beyond a single subsystem because BPF is often used as a privileged, high-trust execution environment. In practice, mistakes in BPF arithmetic or bounds tracking tend to be treated as kernel security issues first and implementation quirks second.The newly published CVE describes a very specific failure mode. The interpreter’s signed 32-bit division and modulo handlers use the kernel
abs() macro on s32 operands, but that macro is undefined for the minimum representable signed 32-bit value. When the destination register contains S32_MIN, the result can remain negative after abs() and then be sign-extended into a u64 in a way that breaks the division logic. The verifier, meanwhile, computes the mathematically correct result for range tracking, so the two code paths diverge. That divergence is the real danger: a verifier/interpreter mismatch can create a false sense of safety and allow out-of-bounds access to map values.This kind of bug maifier is supposed to be the interpreter’s guardrail. If the verifier says a program is safe, the interpreter must execute the same semantics. When the two disagree, the kernel can end up approving a program under one mathematical model and running it under another. That is the kind of inconsistency that has historically underpinned many BPF exploitation chains. The exploit primitive is not the division itself; it is the broken assumption that the verifier and runtime agree.
The upstream fix is elegant. Rather thansue with ad hoc checks, maintainers introduced
abs_s32(), which handles S32_MIN correctly by casting to u32 before negating. That avoids signed overflow entirely. They then replaced all eight abs((s32)...) call sites in the interpreter’s sdiv32 and smod32 handlers, while leaving the 64-bit division and modulo paths untouched because those do not use abs() in the same way.This is also one of those CVEs where the technical wording tehe underlying engineering philosophy. The kernel team did not redesign BPF arithmetic; they corrected a single, well-isolated undefined behavior issue and aligned the interpreter with the verifier. That is the hallmark of a fix that is both backportable and security-relevant.
 Overview
Overview
BPF security has matured dramatically over the last several kernly days, the key concerns were straightforward: could the verifier be tricked, could a helper be misused, and could a program escape the intended sandbox? Today the attack surface is more subtle. BPF programs interact with more helpers, more maps, more JIT and interpreter paths, and more architecture-specific details. That means a defect can be mathematically tiny but still operationally serious. CVE-2026-31525 fits that mold perfectly.At a high level, the bug arises because the interpreter and verifier are doing two different things wite verifier’s abstract interpretation logic, specifically the
scalar32_min_max_sdiv range tracking, uses mathematically correct signed division behavior. The interpreter, however, hits undefined behavior when it feeds S32_MIN into the kernel abs() macro. On common platforms such as arm64 and x86, that undefined behavior can leave the value unchanged, which is then misinterpreted downstream. That is not just an arithmetic quirk; it is a semantic split that can be weaponized.The kernel description makes the exploitation concern explicit: the mismatch can be exploited for out-of-bounds map value aclly important because BPF maps are foundational to a huge amount of kernel and userspace coordination. If a malicious or carefully crafted program can reach an out-of-bounds map access path, the impact can range from denial of service to information disclosure to privilege escalation, depending on the surrounding conditions and kernel hardening. The CVE record itself focuses on the undefined behavior and the mismatch, while the security implication comes from how BPF uses map access as part of its normal execution model.
The fix also reveals how kernel developers think about correctness. The maintainers did not introduce a special-case branch only for one architect try to “fix”
do_div() at the end of the pipeline. Instead, they eliminated the root cause by ensuring the absolute-value operation itself is well-defined for the full signed 32-bit domain. That is cleaner, less invasive, and much easier to reason about in stable trees. Kernel fixes that preserve semantics are usually the best fixes.How the Bug Emerged
The root of the problem is theabs() macro documentation in include/linux/math.h, which explicitly warns that the result is undefinede type minimum. That warning is not academic. For two’s-complement signed integers, -INT_MIN cannot be represented in the same signed type, so any implementation that tries to negate it directly risks overflow or implementation-defined behavior. In practice, the BPF interpreter landed right on that edge.When
DST contains S32_MIN (0x80000000), abs((s32)DST) triggers undefined behavior and, on arm64/x86, can return S32_MIN unchanged. The kernel then sign-extends that value into a0xFFFFFFFF80000000. That is a huge difference from the intended positive absolute value, and it corrupts the inputs passed todo_div()`. Once the arithmetic is wrong at that stage, the interpreter’s result no longer matches what the verifier predicted.The significance here is not just “bad math happened.” The significance is that the interpreter and verifier are supposed to be two views of the same execution model. The verifier is the policy engine; the inution engine. If one believes a value is bounded and non-problematic while the other sees a wrapped or sign-extended edge case, the safety guarantee collapses. That mismatch can be especially dangerous in a system like BPF, where the verifier’s approval is what makes the program eligible to run at all. A verifier mismatch is often the real vulnerability, not the low-level bug that caused it.
Another reason this issue is notable is that it is narrowly scoped to signed 32-bit arithmetic. The CVE text explicitly says
s32 is the only affected case, and the signed 64-bit division and modulo handlers do not use abs(). ngs. First, the bug is not a blanket flaw across all BPF arithmetic. Second, the maintainers already had different code paths for different widths, which made the bad assumption easier to isolate and fix.Why S32_MIN Is So Special
S32_MIN is one of those values that quietly punishes sloppy assumptions. It is a perfectly valid integer, but it sits at the exact point where a signed negation overflows. Any code that assumes absolute value is alwntegers is exposed here. The interpreter’s use of abs() on s32 inputs was therefore not merely a style issue; it was a latent correctness flaw waiting for the right input.The kernel fix,
abs_s32(), avoids that trap by converting to u32 before negating. That shifts the computation into an unsigned domain where the arithmetic can be expressed without signed overflow. In other words, the fix does not “force” the right answer by accident;nswer representable. That distinction is what separates a safe fix from a lucky one.S32_MINis the lowest signed 32-bit value.abs()is explicitly undefined there.- The interpreter could preserve the wrong value after sign extension.
- The verifier still tracked the mathematically correct range.
- That difference opened the door to out-of-bounds map access.
ismatch Matters
The BPF verifier is supposed to enforce a contract: if a program is accepted, the interpreter or JIT should execute it within the constraints the verifier modeled. When those two systems diverge, the verifier becomes a liability rather than a safety net. CVE-2026-31525 rning because the verifier’s logic was not obviously broken; instead, the runtime path was subtly wrong. That makes the bug harder to spot in code review and harder to catch with casual testing.
The description points specifically to
scalar32_min_max_sdiv, which is part of the verifier’s abstract interpretation machinery. That function computes the mathematically correct result for range tracking. So the verifier may believe a division or modulo operation yields a safe range, while the interpreter’s undefined behavior proue at runtime. If that value then controls a map index or influences pointer arithmetic, the gap can turn into memory safety trouble.This is why BPF vulnerabilities are often dangerous even when they start as “just arithmetic.” The verifier is not a performance hint; it is the security boundary. A mismatch can undermine all the later reasoning about bounds checks, helper safety, and access constraints. In a subsystem as widely used as BPF, that is enough to justify rapid patching eveSS score is assigned. The danger is systemic, not local.
The broader security lesson is that abstract interpretation and concrete execution must stay synchronized. If the verifier handles corner cases one way and the interpreter another way, an attacker may be able to choose values that pass one model but fail the other. That class of bug has repeatedly shown up in BPF history because the design is inherently dual-layered: a progically approved and dynamically executed.
Map Access and Exploitability
The CVE record’s reference to out-of-bounds map value access matters because maps are the most common state mechanism in BPF. They are where counters, policies, and scratch data live. If a program can reach beyond a map value boundary, the kernel may expose adjacent data or corrupt internal state, depending on the map type and surrounding protections. That is om “wrong arithmetic” to “security boundary violation.”This also explains why the issue is security-relevant even though it seems narrow. Many kernel bugs become exploitable only when a particular edge value interacts with a trusted helper or storage abstraction. Here, the edge value is
S32_MIN, the trusted abstraction is the BPF interpreter, and the storage boundary is a map value. That combination is exactly the kind of thing exploit developers look for.- The vehematically correct range.
- The interpreter could compute a different runtime value.
- That mismatch can affect map indexing or bounds.
- BPF maps are security-sensitive shared state.
- The issue therefore crosses from correctness into exploitability.
The Fix and Its Design
The fix is gratifyingly direct. The kernel introducesabs_s32(), a helper that handles S32_MIN without invoking signed by casting to u32 before negating, which keeps the arithmetic within a well-defined unsigned range. This is the kind of change kernel maintainers like because it corrects the logic at the point of error rather than layering checks around every downstream consumer.The patch also bs((s32)...)
call sites in the interpreter’ssdiv32andsmod32` handlers. That matters because a partial fix would leave inconsistency behind. If only one path were corrected, the interpreter could still expose undefined behavior in another branch, reintroducing the same mismatch under a different execution shape. The explicit replacement of all call sites tells us the maintainers wanted complete closure on the bug class, not a quick patmptom.There is also a nice separation of concerns in the fix. The 64-bit division and modulo handlers are left alone because they are not using the problematic
abs() path. That suggests the issue was not some general flaw in BPF division semantics, but specifically a 32-bit implementation detail with a very constrained blast radius. That kind of clarity is useful for both auditors and downstream vendors.The deeper point is that the fix respects the kernel’s arithmetic model. It does not reinterpretion or modulo, and it does not add artificial guardrails that could distort output for valid values. Instead, it makes the edge case behave like the rest of the domain. That is the difference between remediation and alteration.
Why abs_s32() Is Better Than a Guard
A naive guard like “if value is S32_MIN, return something else” would only disguise the defect. It might prevent undefined behavo leave room for inconsistency and special-case drift. By contrast, abs_s32() is a real mathematical correction: it preserves the absolute-value intent without requiring a signed overflow. That makes the helper reusable and easier to trust across the codebase.A helper-based fix also improves maintainability. Future reviewers can see that thisy to compute a 32-bit absolute value safely in kernel code. That reduces the odds that another developer will reintroduce the same bug in a nearby call site six months later. In kernel security work, making the safe path obvious is almost as important as fixing the bug itself.
abs_s32()avoids signed overflow.- Casting to
u32makes the negation well-defined. - All eight vulnerable interpreter call sites are corrected.
- The 64-bit handlers were .
- The patch is narrow enough to backport cleanly.
Impact on Enterprise Systems
For enterprises, the key question is not whether every Linux host is immediately vulnerable in the same way. It is whether the organization allows untrusted or semi-trusted BPF programs into environments where the interpreter path is used. That includes observability stacks, eBPF-based securitylatforms, service meshes, and custom kernel instrumentation. In those environments, BPF is not a toy; it is part of the production control plane.The practical impact depends on how BPF is deployed. If the workload uses only curated programs from trussure is narrower. If the platform allows program loading through automation, CI/CD, telemetry agents, or multi-tenant observability features, then the chance of a maliciously crafted edge case rises. The mismatch described in the CVE is especially relevant in shared environments because it turns a nominally verified program into one that may behave differently at runtime. That is the kind of bug that security teams hate to reason about after the fact.
Enterprises should also pay attention to vuse the CVE is rooted in an interpreter implementation detail, the actual fixed version may not line up neatly with upstream kernel release numbers. The more relevant question is whether the vendor kernel includes the
abs_s32() helper and the interpreter call-site replacements. In real fleets, that matters more than the abstract “mainline version” label.There is also an operational angle. BPF issues often show up first as strange, inconsistent, or hard-to-reproduce behavior rather than as an immediate crash. That can waste engineering time, especially when the bug only appeaputs or program shapes. If a team relies on BPF for production policy, the safest stance is to treat this as a real patch item, not a theoretical edge case.
Enterprise Checklist
- Identify whether your kernels include the vulnerable BPF interpreter code path.
- Confirm whether your vendors have backported the
abs_s32()fix. - Inventory where BPF programs can be loaded from automation or third-party tooling.
4internal BPF programs perform signed 32-bit division or modulo. - Prioritize systems that accept user-defined or tenant-influenced BPF input.
- Production observability stacks may be exposed.
- Multi-tenant systems deserve extra scrutiny.
- Vendor backports matter more than version headlines.
- Interpreter-only paths can still be security-critical.
- Internal BPF programs should be audited for risky# Consumer and Developer Implications
Developers and kernel-adjacent engineers should take this as a reminder that undefined behavior does not stay local. In C and kernel code, the temptation is often to rely on helper macros whose limitations are easy to overlook. Buthe worst bugs often happen when two layers each behave “correctly” according to different assumptions. The compiler, interpreter, and verifier can all be doing something reasonable and still create a security bug in combination.
There is also a lesson for anyone writing BPF programs: avoid edge-case arithmetic unless you can prove how the verifier and runtime will interpret it. Signed division and modulo on boundary values are especially risky because they interact with both language-level and k. Even when the program looks mathematically sound, the implementation details can turn it into an exploit primitive.
For developers building tooling around BPF, this CVE underscores why test coverage should include pathological values. Values near zero are obvious. Values at the extremes are often forgotten. Yet those extremes are exactly where undefined behavior, verifier divergence, and architecture-specific surprises tend to show up. If you do not test
S32_MIN, the kernst it for you.*Developer Takeaways
- Treat signed boundary values as first-class test cases.
- Avoid helper macros with documented undefined edge behavior.
- Keep verifier logic and runtime logic aligned.
- Prefer explicit safe helpers over ad hoc arithmetic.
- Audit map access logic after any arithmetic change.
Broader Kernel Security Lessons
This CVE is another reminder that the Linux keris not only about memory corruption. Correctness, determinism, and semantic agreement are just as important when the affected subsystem sits on the boundary between policy and execution. BPF is a particularly sensitive area because it combines compile-time reasoning, runtime interpretation, and privileged kernel access in one pipeline.The problem also illustrates why undefined behavior is so dang A function can appear to work on common architectures like x86 and arm64, and yet still violate the language and kernel assumptions underneath. That creates a false sense of stability. When a value like
S32_MIN survives an abs() call unchanged, the failure is not always obvious immediately; it may shomputed divisor or a mismatched range bound.The kernel community has long known that helper macros can be loaded with hidden assumptions. The good news is that the fix pattern here is strong: create a helper that states the intended behavior clearly and make the call sites use it consistently. That is the sort of change that prevents recurrence rather than just suppressing one manifestation. It also makes the code easier to audit in the futury benefit in its own right.
What This Says About BPF Maturity
BPF’s evolution from a packet-filtering mechanism into a general-purpose kernel execution substrate has raised the stakes. As the subsystem grows more powerful, the margin for arithmetic sloppiness shrinks. That means even small bugs in the interpreter deserve serious attention, because the interpreter is part of the trusted execution path for a large and expanding set of workloads.future BPF hardening work will continue to focus on semantic consistency. The more the verifier, interpreter, and JIT share assumptions, the less room there is for mismatch-based exploitation. In that sense, CVE-2026-31525 is not just a patch note. It is a reminder that the kernel’s security model depends on exactness, especially at the boundaries where human intuition about math is least reliable. *Boundary conditions are where kernel trust is wonned behavior is a security problem, not a compiler footnote.
- Helper consistency matters as much as helper performance.
- Semantic drift between verifier and interpreter is dangerous.
- Architecture-specific “it works here” behavior can hide real bugs.
- BPF maturity increases the importance of arithmetic precision.
Strengths and Opportunities
The strength of this fix is that it is narrow, comprehensible, and roles. Kernel maintainers solved the actual problem instead of building a compensating workaround, which reduces the chance of hidden regressions. It also creates an opportunity to review adjacent BPF arithmetic paths for similar assumptions about absolute value, signed overflow, and verifier/runtime agreement.- The patch is surgical and easy to review.
- It replaces undefined behavior with well-defined arithmetic.
- It preserves verifier/interpreter consistency.
- It ikport friendly**.
- It offers a chance to audit neighboring BPF math paths.
- It reinforces best practices around safe helper functions.
- It may improve confidence in BPF map access correctness.
abs((s32)...) pat related mistakes before they become public issues. That would be a strong example of how a small fix can drive broader hardening across a security-critical subsystem. Good security work often compounds.Risks and Concerns
The main concern is that this is the sort of bug that can be underestimated because it does not look dramatic on first read. There is no obvious buffer overflow in the description, no flashy race conditiote trigger spelled out in the record. But the verifier/interpreter mismatch is exactly what makes it dangerous, because it undermines the very mechanism meant to keep BPF safe.- It may be under-triaged because the root cause is arithmetic.
- Vendor backports may lag behind upstream fixes.
- Different kernels may carry different local patches.
- The undefined behavior can vary by architecavior.
- BPF users may wrongly assume verifier approval makes runtime behavior safe.
- Similar edge cases may exist in nearby interpreter code.
- The absence of an initial CVSS score can slow prioritization.
There is also a longer-term maintenance risk. Once a helper like
abs_s32() exists, future contributors may assume the arithmetic corner case is permanently solved and stop testing boundary values would be a mistake. A fix is only durable if the testing culture around it remains sharp.Looking Ahead
The immediate question is how quickly downstream vendors fold this fix into their kernel trees. Because the bug is confined to the interpreter’s signed 32-bit paths, the patch should be relatively easy to carry. But kernel users should still verify the exact build they are running, not just the upstream release line, because backses can obscure the real exposure window.The next thing to watch is whether this CVE prompts broader inspection of BPF arithmetic helpers and verifier assumptions. The existence of a clean
abs_s32() helper could become a standard pattern for future code, which would be a positive outcome. More importantly, maintainers may decide to grep for similar signed-edge arithmetic in other interpreter ore another mismatch emerges.Security teams should also pay attention to whether this bug appears in curated hardening advisories from distributions and enterprise vendors. Since BPF is used heavily in observability and network enforcement stacks, a fix that lands quietly can still have meaningful operational vrm, patch priority should be driven by whether BPF is enabled and whether the environment permits programs that can reach these arithmetic paths.
- Confirm whether your kernel includes the
abs_s32()fix. - Check vendor advisories for backported stable builds.
- Audit BPF programs that use signed 32-bit division or modulo.
- Prioritize systems that load BPF from automation or third-party tools.
- Look for adjacenthat might share the same assumption.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center