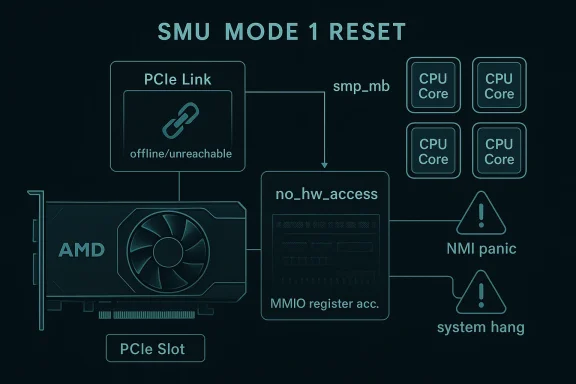
CVE-2026-23213 is a good example of how a small-looking kernel fix can carry outsized operational consequences for AMD GPU users. The underlying issue, titled “drm/amd/pm: Disable MMIO access during SMU Mode 1 reset,” centers on a brief but dangerous window in which the ASIC is resetting and temporarily unreachable over PCIe. If the driver or another thread keeps touching MMIO registers during that window, the result can be incomplete PCIe transactions, NMI panics, or a full system hang. Ubuntu’s advisory says the fix marks the device as unavailable with a no_hw_access flag immediately after the reset begins, and it adds an smp_mb() barrier so that other cores see the state change before any wait path continues
The AMD Linux graphics stack has a long history of balancing aggressive hardware control with the realities of a highly concurrent kernel. In amdgpu, the power-management block and the SMU firmware coordinate everything from clocks and voltages to reset behavior, which means timing matters. When that coordination fails, the symptoms are often not subtle: a GPU reset that should recover a device can instead wedge the machine, poison PCIe transactions, or leave user sessions staring at a frozen desktop.
Mode 1 reset is particularly interesting because it is not just a software retry path; it is a full hardware transition. The GPU is effectively offline for part of the operation, and that changes the safety assumptions for every other code path touching the device. In practical terms, the reset path has to become a guarded zone, or the rest of the driver may keep acting as if the hardware were still live.
The publication pattern around CVE-2026-23213 also tells a familiar story in kernel security. The issue was published on February 19, 2026 in Ubuntu’s security tracker, which points back to a stable kernel commit that hardens reset handling by suppressing register access during the unsafe interval. Microsoft’s vulnerability page appears to be unavailable for this ID, so the best public description comes from downstream Linux distro advisories and the kernel fix trail.
This is the kind of bug that sits at the intersection of reliability and security. It may not read like a classic remote-code-execution flaw, but anything that can induce a kernel panic, lock up a workstation, or brick a graphics session during a reset deserves to be treated as security-relevant. On modern systems, especially laptops and workstations that depend on the GPU for display output, a hard hang is a serious availability incident.
That matters because the kernel is not a single-threaded script. Interrupt handlers, work queues, display code, and power-management callbacks can all be active at once. If just one of them ignores the reset window, the driver can trip over its own recovery logic.
That detail makes the fix more robust than a narrow “set a boolean” patch. It addresses the race between the state change and the rest of the driver observing that state, which is where real-world hangs often come from. In kernel terms, this is the difference between a polite warning and a believable guarantee.
The Linux kernel documentation for amdgpu makes clear that the driver supports multiple reset methods, including mode1 as one of the selectable reset paths. That flexibility is important for field reliability, but it also expands the surface area for bugs. The more reset paths the driver carries, the more chances there are for a state assumption to go stale during a transition.
This is not merely a cosmetic issue. In a desktop environment, the display engine may be involved. In a workstation or compute host, the GPU may be part of a larger service chain, so one hung device can ripple into failed jobs, broken sessions, or watchdog resets. The blast radius is often larger than the patch size suggests.
Ubuntu labels the issue as Medium priority, which is a useful clue about its exploitability and impact balance. That rating suggests the bug is serious enough to fix promptly, while also implying that exploitation likely requires local conditions or a specific failure sequence rather than a trivial one-packet trigger. In other words, this looks like a stability flaw with security consequences, not a straightforward remote compromise.
In cloud or virtualization settings, GPU resets can also become platform incidents. A reset that should have recovered an adapter may instead trigger host-level instability or watchdog intervention. That is one reason kernel teams and distros take “just a hang” bugs seriously.
For administrators, that means the practical question is not “Is my Linux kernel vulnerable in the abstract?” but “Has my distribution already pulled in the backport?” The answer will differ by release train, kernel flavor, and hardware support stack. This is why GPU-related CVEs can be annoyingly operational: the vulnerability exists in a subsystem, but the fix lands through distribution-specific kernel packaging.
Consumer systems may also mask the bug by virtue of simpler usage patterns. A single desktop may reset a GPU only rarely, and the exact race may never appear. That does not make the issue harmless; it just means the risk is more unevenly distributed than a network worm or browser exploit.
That is not unusual in complex kernel code. Hardware vendors often optimize for fast access and later add synchronization around the edges. But each edge case that gets papered over increases the odds that a rarely used reset path will trip a stale assumption. The reset code is where hidden concurrency bugs go to become very visible.
The same principle appears throughout robust kernel subsystems. If a device is being torn down, rebuilt, or reinitialized, then every access path needs to know. The alternative is a split-brain driver where one thread is politely waiting and another is still poking dead hardware.
For rivals, the lesson is familiar: stability wins hearts in ways benchmarks cannot. NVIDIA’s and Intel’s Linux graphics stacks each face their own reliability scrutiny, but a well-publicized AMD reset issue can sway workstation and fleet procurement conversations. In the long run, the vendor that demonstrates the most boringly reliable recovery path often earns the most trust.
The broader market implication is that driver maturity is now a feature. Performance parity alone is no longer enough in high-end client and edge-computing segments. Buyers increasingly compare the total operational friction, including what happens when things go wrong.
The good news is that the mitigation path is straightforward: update to a kernel build that includes the backport. Ubuntu’s page shows the issue already tracked through the distribution’s security workflow, which usually means fixed packages will propagate through normal update channels once evaluation is complete.
It will also be worth seeing whether later kernel releases add additional guardrails around offline hardware state. If the reset path is a recurring source of bugs, we may see more explicit state machines, stricter access gating, or broader synchronization around device teardown and recovery. That would be a healthy outcome, because boring resets are good resets.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
The AMD Linux graphics stack has a long history of balancing aggressive hardware control with the realities of a highly concurrent kernel. In amdgpu, the power-management block and the SMU firmware coordinate everything from clocks and voltages to reset behavior, which means timing matters. When that coordination fails, the symptoms are often not subtle: a GPU reset that should recover a device can instead wedge the machine, poison PCIe transactions, or leave user sessions staring at a frozen desktop.Mode 1 reset is particularly interesting because it is not just a software retry path; it is a full hardware transition. The GPU is effectively offline for part of the operation, and that changes the safety assumptions for every other code path touching the device. In practical terms, the reset path has to become a guarded zone, or the rest of the driver may keep acting as if the hardware were still live.
The publication pattern around CVE-2026-23213 also tells a familiar story in kernel security. The issue was published on February 19, 2026 in Ubuntu’s security tracker, which points back to a stable kernel commit that hardens reset handling by suppressing register access during the unsafe interval. Microsoft’s vulnerability page appears to be unavailable for this ID, so the best public description comes from downstream Linux distro advisories and the kernel fix trail.
This is the kind of bug that sits at the intersection of reliability and security. It may not read like a classic remote-code-execution flaw, but anything that can induce a kernel panic, lock up a workstation, or brick a graphics session during a reset deserves to be treated as security-relevant. On modern systems, especially laptops and workstations that depend on the GPU for display output, a hard hang is a serious availability incident.
What the Bug Actually Changes
The patch is conceptually simple: once the reset starts, stop all MMIO access until the device is safely back online. Ubuntu’s description says the driver sets no_hw_access to true right after the reset is triggered, and that other driver threads are supposed to honor that flag and skip register operations while the hardware is offline. That is the core of the fix, and it is exactly the sort of defensive state transition kernel code needs during hardware recovery.Why MMIO Is the Sensitive Part
MMIO is the plumbing that lets the CPU talk to device registers through mapped memory addresses. It is fast, direct, and dangerous when the hardware behind it is not in a stable state. During a reset, those registers may stop responding normally, so a read or write that would be harmless a millisecond earlier can suddenly become a transaction that never completes.That matters because the kernel is not a single-threaded script. Interrupt handlers, work queues, display code, and power-management callbacks can all be active at once. If just one of them ignores the reset window, the driver can trip over its own recovery logic.
The Role of the Memory Barrier
The addition of smp_mb() is not decorative; it is there to enforce ordering. In a concurrent kernel, it is not enough to update a flag in one CPU’s cache and hope every other core notices immediately. The barrier helps ensure the no-hardware-access state becomes globally visible before the driver enters the sleep or wait phase described in Ubuntu’s advisory.That detail makes the fix more robust than a narrow “set a boolean” patch. It addresses the race between the state change and the rest of the driver observing that state, which is where real-world hangs often come from. In kernel terms, this is the difference between a polite warning and a believable guarantee.
How SMU Mode 1 Reset Fits Into AMD Power Management
AMD’s SMU, or System Management Unit, is the firmware-driven controller that handles a large share of GPU power and reset orchestration. The Mode 1 reset path is one of the deeper recovery mechanisms available to the driver, and that makes it useful when lighter resets fail. It also means the driver is engaging with the device at its most delicate moment.The Linux kernel documentation for amdgpu makes clear that the driver supports multiple reset methods, including mode1 as one of the selectable reset paths. That flexibility is important for field reliability, but it also expands the surface area for bugs. The more reset paths the driver carries, the more chances there are for a state assumption to go stale during a transition.
Why the GPU Becomes Temporarily Unreachable
During the reset cycle, the ASIC can become unavailable over PCIe. That is what makes the bug possible in the first place. If a background thread or interrupt-driven callback touches the hardware while it is unreachable, the PCIe transaction may never complete cleanly, leaving the kernel waiting on a dead response.This is not merely a cosmetic issue. In a desktop environment, the display engine may be involved. In a workstation or compute host, the GPU may be part of a larger service chain, so one hung device can ripple into failed jobs, broken sessions, or watchdog resets. The blast radius is often larger than the patch size suggests.
Why This Is a Cross-Component Problem
The reset path is not isolated inside one function. The amdgpu driver has multiple subsystems that can talk to each other: power management, display, memory management, scheduling, and firmware coordination. A safety flag like no_hw_access is therefore a global contract, not just a local note in one function. If any component ignores it, the reset logic is weakened.- The bug is about state synchronization, not just register access.
- The fix assumes every MMIO path checks the same “device offline” signal.
- The reset window is brief, but concurrency makes “brief” enough to matter.
- Firmware coordination does not eliminate the need for driver-side guards.
Why This Becomes a Security Issue
Not every kernel hang is automatically a CVE, but this one has the right characteristics to become one. A reset-time MMIO access bug can produce reliable denial of service behavior under the right timing conditions. If user activity, driver threads, or interrupt handling collide with the reset window, the system may freeze or panic, which is materially important in fleet environments.Ubuntu labels the issue as Medium priority, which is a useful clue about its exploitability and impact balance. That rating suggests the bug is serious enough to fix promptly, while also implying that exploitation likely requires local conditions or a specific failure sequence rather than a trivial one-packet trigger. In other words, this looks like a stability flaw with security consequences, not a straightforward remote compromise.
The Availability Angle
Availability bugs are often underrated because they do not steal data. But for enterprise desktops, CAD workstations, scientific nodes, and GPU-accelerated systems, a panic or hard hang can be operationally expensive. If the display stack is involved, the user experience can degrade into full reboot cycles; if the machine is headless, a hung kernel may take down jobs and require remote hands.In cloud or virtualization settings, GPU resets can also become platform incidents. A reset that should have recovered an adapter may instead trigger host-level instability or watchdog intervention. That is one reason kernel teams and distros take “just a hang” bugs seriously.
Why Concurrency Makes It Worse
The danger is not simply that MMIO can fail during reset. The danger is that other code keeps running while the hardware is offline. Interrupt-driven code is especially problematic here because it may be invoked precisely when the device is noisy or recovering. The moment one path assumes the device is still responsive and another path has already put it into reset, the race begins.- Interrupt handlers may fire at the wrong time.
- Work queues may try to service the device during offline windows.
- Display or PM code may continue sequencing register operations.
- Recovery logic may deadlock if it waits on itself.
Downstream Impact for Linux Distributions
The immediate consumers of this fix are Linux distributions that ship the relevant AMD kernel code. Ubuntu’s security page shows the issue tracked across multiple releases, with many still marked Needs evaluation at publication time. That is typical for distro security triage: the existence of a CVE does not mean every branch is equally exposed, but it does mean maintainers need to determine where the stable backport belongs.For administrators, that means the practical question is not “Is my Linux kernel vulnerable in the abstract?” but “Has my distribution already pulled in the backport?” The answer will differ by release train, kernel flavor, and hardware support stack. This is why GPU-related CVEs can be annoyingly operational: the vulnerability exists in a subsystem, but the fix lands through distribution-specific kernel packaging.
Enterprise Versus Consumer Exposure
Enterprise fleets may feel the issue more acutely because they tend to run longer-lived kernels and standardized hardware. If a company has a stock of AMD workstations or GPU-equipped laptops, a bug like this can show up in coordinated user sessions, conferencing, or CAD workloads. Consumer machines can also be hit, of course, but fleets are more likely to notice the same failure pattern repeatedly.Consumer systems may also mask the bug by virtue of simpler usage patterns. A single desktop may reset a GPU only rarely, and the exact race may never appear. That does not make the issue harmless; it just means the risk is more unevenly distributed than a network worm or browser exploit.
How Distro Maintainers Translate the Fix
Distribution kernels often backport security and stability changes under different commit IDs or package builds. Ubuntu explicitly references a cherry-pick from a specific commit hash in its advisory, which is standard practice for downstream maintenance. That matters because patch provenance helps administrators and vendors confirm whether the version they are running includes the hardening change.- Check whether your distro’s kernel build includes the backport.
- Confirm whether your AMD GPU model actually uses the affected reset path.
- Verify whether the system is on a desktop, workstation, or headless GPU stack.
- Treat display freezes during reboot or resume as potential signal, not noise.
What the Fix Suggests About AMD Driver Design
The patch tells us something important about how modern GPU drivers are built: they are increasingly stateful coordination systems, not simple register shims. A flag like no_hw_access exists because the driver already knows that some paths must be barred when the device is transitioning. The fact that this needed a CVE-worthy fix means that prior guardrails were not complete enough.That is not unusual in complex kernel code. Hardware vendors often optimize for fast access and later add synchronization around the edges. But each edge case that gets papered over increases the odds that a rarely used reset path will trip a stale assumption. The reset code is where hidden concurrency bugs go to become very visible.
Reset Logic as a Shared Contract
Once the driver enters reset, everyone has to agree on the rules. The power-management code cannot proceed as if the GPU were alive, and the rest of the stack must respect the offline flag. That shared contract is what makes the fix meaningful: it moves the driver from implicit hope to explicit enforcement.The same principle appears throughout robust kernel subsystems. If a device is being torn down, rebuilt, or reinitialized, then every access path needs to know. The alternative is a split-brain driver where one thread is politely waiting and another is still poking dead hardware.
What This Means for Future Hardening
The fix could encourage broader audits of reset-related MMIO access in other GPU paths. If one reset flow needed explicit suppression, other flows may deserve the same scrutiny. That is especially true on newer ASICs and firmware combinations where the timing envelope is tighter and the code paths are more fragmented.- Reset-state flags should be checked early, not late.
- Cross-thread visibility matters as much as the flag itself.
- Firmware-assisted recovery does not remove the need for driver fences.
- More granular reset methods usually mean more hardening work.
Competitive and Market Implications
For AMD, the issue is less about brand damage and more about confidence in platform stability. GPU buyers care about raw performance, but enterprise buyers care just as much about whether a system survives stressful real-world events. A reset bug that can panic a machine chips away at that confidence, especially in Linux-heavy environments where the driver stack is part of the sales story.For rivals, the lesson is familiar: stability wins hearts in ways benchmarks cannot. NVIDIA’s and Intel’s Linux graphics stacks each face their own reliability scrutiny, but a well-publicized AMD reset issue can sway workstation and fleet procurement conversations. In the long run, the vendor that demonstrates the most boringly reliable recovery path often earns the most trust.
Why This Matters Beyond the Specific CVE
A CVE like this is not likely to move markets by itself. But it contributes to the cumulative reputation of a platform. If administrators see repeated kernel fixes around resets, firmware coordination, or device-online state handling, they may hesitate before standardizing on that hardware for sensitive deployments.The broader market implication is that driver maturity is now a feature. Performance parity alone is no longer enough in high-end client and edge-computing segments. Buyers increasingly compare the total operational friction, including what happens when things go wrong.
The Linux Ecosystem Angle
Linux distributions benefit when upstream and downstream patches move quickly, and this case is another reminder of how important that pipeline is. Ubuntu’s advisory, for example, converts an upstream kernel fix into a distro-level security entry that administrators can actually act on. That translation layer is where kernel maintenance becomes enterprise value.- Better backporting shortens exposure windows.
- Faster advisories reduce guesswork for admins.
- Stable fixes preserve trust in Linux on workstations.
- Security teams can map CVEs to package versions more easily.
How Administrators Should Read the Advisory
The right response is not panic; it is inventory and patch hygiene. If a system includes an AMD GPU and runs a Linux kernel variant that has not yet absorbed the fix, it should be treated as needing review. That is especially true if the machine is used for graphics-heavy desktop work, scientific visualization, or any scenario that triggers GPU resets or aggressive power transitions.The good news is that the mitigation path is straightforward: update to a kernel build that includes the backport. Ubuntu’s page shows the issue already tracked through the distribution’s security workflow, which usually means fixed packages will propagate through normal update channels once evaluation is complete.
A Practical Triage Checklist
- Confirm the kernel package version currently installed.
- Identify whether the system uses an AMD GPU and the affected amdgpu stack.
- Check distro security advisories for backported fixes.
- Review whether the machine has seen unexplained hangs during resume or reset.
- Apply the vendor-recommended update path as soon as it is available.
What Not to Overinterpret
This is not evidence of a universally exploitable remote attack. It is a kernel hardening and stability issue with security implications. The distinction matters because it sets expectations: the main risk is local operational disruption, not necessarily broad attacker reach. That said, availability bugs can still be weaponized in targeted contexts, so they should not be dismissed.Strengths and Opportunities
The fix is strong because it targets the problem at the point of failure and aligns the driver’s behavior with the hardware’s actual state. It also has the advantage of being easy to reason about, which is exactly what you want in a reset path.- Clear mitigation logic: stop MMIO during reset.
- Low conceptual complexity: easy for maintainers to audit.
- Improved concurrency safety: the memory barrier reduces race risk.
- Better user experience: fewer hard hangs and panics.
- Enterprise value: more predictable GPU recovery on Linux fleets.
- Future hardening path: the patch can inspire similar audits elsewhere.
- Distribution-friendly: straightforward to backport into stable kernels.
Risks and Concerns
Even with the fix in place, the underlying lesson is that GPU reset paths remain fragile and timing-sensitive. Any future regression that weakens the no-hardware-access contract could reintroduce the same class of failure in a different form.- Incomplete backports could leave some distro kernels exposed.
- Race conditions may persist in adjacent driver paths.
- Hardware diversity makes field validation difficult.
- Users may ignore hangs until they become recurring incidents.
- Firmware interactions can complicate root-cause analysis.
- Headless systems may fail silently until services degrade.
- Overconfidence in one fix can discourage broader reset audits.
Looking Ahead
The most important next step is simple: watch for distro packages that include the backported fix and apply them promptly. Administrators should also pay attention to whether other amdgpu reset or PM patches follow in the same area, because these problems often cluster. A single CVE rarely exhausts the story; it usually reveals the seam where more work is needed.It will also be worth seeing whether later kernel releases add additional guardrails around offline hardware state. If the reset path is a recurring source of bugs, we may see more explicit state machines, stricter access gating, or broader synchronization around device teardown and recovery. That would be a healthy outcome, because boring resets are good resets.
- Monitor distro advisories for the patched kernel build.
- Reboot into updated kernels during normal maintenance windows.
- Watch for related amdgpu reset and PM hardening patches.
- Validate workstation and fleet behavior after update.
- Escalate repeated hangs as potential reset-path regressions.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: