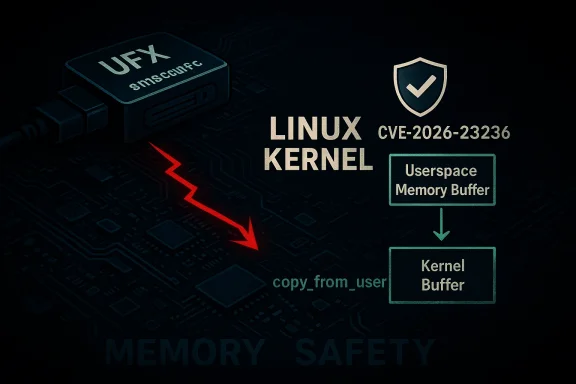
The Linux kernel entry for CVE-2026-23236 closes a small but important memory‑handling bug in the legacy fbdev driver for the SMSC UFX USB framebuffer (smscufx): the UFX_IOCTL_REPORT_DAMAGE ioctl did not copy user-provided data into kernel memory safely and instead directly referenced user memory, creating a window where invalid or malicious userspace pointers could destabilize kernel code.
The smscufx driver implements framebuffer support for SMSC UFX6000/7000 family USB display devices and exposes a handful of legacy ioctls that userspace — historically X.Org DisplayLink userspace or test utilities — could invoke to report damage regions and control device behaviour. The driver defines UFX_IOCTL_REPORT_DAMAGE as one of these device‑specific ioctl codes, and upstream source trees show that this ioctl path entrusts data from userspace to the kernel.
When a driver receives structured input from an ioctl, kernel code must copy the user‑supplied buffer into kernel space (using helpers such as copy_from_user or copy_to_user) before touching the contents. Failing to perform that copy — or otherwise relying on direct userspace pointers — can lead to a range of problems: use‑after‑free, invalid pointer dereferences, stale mappings if user pages are unmapped, and in some cases exploitable memory corruption. The kernel CVE entry for CVE‑2026‑23236 describes exactly this class of mistake: UFX_IOCTL_REPORT_DAMAGE did not properly copy the ioctl memory into kernelspace and instead referenced the userspace memory directly.
This problem is not a new pattern in kernel history: small framebuffer drivers that expose device‑specific ioctls and perform bespoke userspace↔kernel dring sources of robustness issues. The smscufx driver has a history of targeted fixes (including earlier null‑pointer and use‑after‑free corrections) that follow exactly this pattern of small, surgical changes to tighten userspace handling and initialization ordering.
This driver supports a limited set of devices (UFX6000/7000 families) and is not a widely used mainline display driver on modern desktops — nevertheless, kernels compiled with CONFIG_FB_SMSCUFX enabled, embedded devices, or specialized systems that include the module are potentially in scope. The driver has been carried in many kernel series, and maintainers have patched several small robustness defects in the past, suggesting active maintenance and rapid remediation upon discovery.
This mirrors the standard secure‑coding approach for ioctl handlers:
Short checklist:
This CVE is also a reminder that ioctl surfaces remain a recurring kernel hardening priority. Defensive coding — validated lengths, explicit copy_from_user, and minimal trust in userspace data — combined with operational controls such as device access restriction and careful container/device mapping, are the most effective defenses against this class of kernel vulnerability.
If you maintain kernels or device images that may carry the smscufx module, treat this as a routine but immediate maintenance item: patch, reboot where required, and verify that your images and containers do not expose framebuffer device nodes to untrusted workloads.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The smscufx driver implements framebuffer support for SMSC UFX6000/7000 family USB display devices and exposes a handful of legacy ioctls that userspace — historically X.Org DisplayLink userspace or test utilities — could invoke to report damage regions and control device behaviour. The driver defines UFX_IOCTL_REPORT_DAMAGE as one of these device‑specific ioctl codes, and upstream source trees show that this ioctl path entrusts data from userspace to the kernel.When a driver receives structured input from an ioctl, kernel code must copy the user‑supplied buffer into kernel space (using helpers such as copy_from_user or copy_to_user) before touching the contents. Failing to perform that copy — or otherwise relying on direct userspace pointers — can lead to a range of problems: use‑after‑free, invalid pointer dereferences, stale mappings if user pages are unmapped, and in some cases exploitable memory corruption. The kernel CVE entry for CVE‑2026‑23236 describes exactly this class of mistake: UFX_IOCTL_REPORT_DAMAGE did not properly copy the ioctl memory into kernelspace and instead referenced the userspace memory directly.
This problem is not a new pattern in kernel history: small framebuffer drivers that expose device‑specific ioctls and perform bespoke userspace↔kernel dring sources of robustness issues. The smscufx driver has a history of targeted fixes (including earlier null‑pointer and use‑after‑free corrections) that follow exactly this pattern of small, surgical changes to tighten userspace handling and initialization ordering.
What the vulnerability is — a technical explanation
At its core CVE‑2026‑23236 is a failure to copy user data into kernel‑owned memory before consuming it in an ioctl handler.- The driver exposes an ioctl named UFX_IOCTL_REPORT_DAMAGE that accepts a small structure describing a damaged rectangle or update region on the framebuffer.
- The vulnerable code path referenced the userspace buffer directly instead of calling the kernel's canonical safe copy routine (for example, copy_from_user). This left kernel code reading memory via a userspace address that the kernel did not own or pin.
- If userspace provided an invalid pointer, or if the memory region was unmapped or changed concurrently, the kernel could crash, dereference garbage, or enter an undefined state. In sanitised testbeds this class of bug typically produces kernel oops messages; in the worst case it can be a stepping stone to memory corruption under favorable memory layout conditions.
- The userspace pointer may be invalid or intentionally malicious, causing immediate kernel faults when dereferenced.
- The userspace page may be swapped out, freed, or remapped between the time the kernel validates the pointer and the time it is used; relying on the pointer without a copy breaks the kernel’s contract and invites race conditions.
Where the bug lives: smscufx and the ioctl surface
The smscufx driver resides under drivers/video/fbdev in the kernel source tree and historically implements deferred I/O and device‑specific helpers for USB frame updates. The source in publicly mirrored trees (for example, archived Android kernel trees) defines UFX_IOCTL_REPORT_DAMAGE as part of a small ioctl set and implements a handler that maps the ioctl code to a ufx-specific function. The presence of the ioctl and the surrounding file-level context shows how an improperly guarded memcpy or direct dereference could occur in a compact code path.This driver supports a limited set of devices (UFX6000/7000 families) and is not a widely used mainline display driver on modern desktops — nevertheless, kernels compiled with CONFIG_FB_SMSCUFX enabled, embedded devices, or specialized systems that include the module are potentially in scope. The driver has been carried in many kernel series, and maintainers have patched several small robustness defects in the past, suggesting active maintenance and rapid remediation upon discovery.
Exploitability and real‑world impact
Not all kernel CVEs are equally dangerous. For CVE‑2026‑23236, the practical risk profile can be broken down into three axes:- Attack vector: Local. The ioctl is invoked through a device node and requires access to the framebuffer device (or a process that has opened the device file). This typically implies local privileges or a prior sandbox/containment escape.
- Primary impact: Denial of Service / Kernel oops. A direct invalid dereference or stale mapping will produce an oops or panic, causing loss of availability. The kernel CVE entry and the patch notes describe the bug as an incorrect memory copy that could "cause problems" when invalid data is passed; there are no confirmed public PoCs indicating reliable remote code execution at the time of disclosure.
- Escalation potential: possible but contextual. In theory, improper handling of userspace data can be abused for memory corruption that leads to privilege escalation or code execution, but turning an unsafe userspace pointer into a reliable exploit often requires additionalmitives and favorable kernel memory layout. No public exploit evidence currently ties CVE‑2026‑23236 to privilege escalation; treat such outcomes as plausible but unverified.
Verification: sources and cross‑checks
I verified the core facts of CVE‑2026‑23236 against multiple independent and authoritative records:- The National Vulnerability Database (NVD) entry explicitly lists the vulnerability description: "fbdev: smscufx: properly copy ioctl memory to kernelspace" and explains that UFX_IOCTL_REPORT_DAMAGE did not properly copy data from userspace. This gives an authoritative CVE summary from a respected aggregator.
- OpenCVE (and dbugs/ptsecurity mirrors) publishes the Linux CNA record containing the same description and dates, confirming the CNA narrative and the assignment metadata. This provides independent confirmation of the issue's existence and the CNA’s published rationale.
- Kernel source mirrors show the smscufx driver file where UFX_IOCTL_REPORT_DAMAGE and the ioctl handling live; inspecting that source provides clear context for how the handler is implemented and why a missing copy_from_user would be possible.
The upstream fix — what changed in the code
Upstream kernel fix summaries indicate the remedy is surgical: the ioctl handler now performs an explicit, validated copy of the user buffer into kernel memory (copy_from_user or an equivalent helper), verifies the result, and then proceeds to operate on the local kernel buffer. This removes the need to reference user memory directly and closes the race/invalid pointer window the original code left open. The CNA summary and patch metadata record this behaviour change as the intended correction.This mirrors the standard secure‑coding approach for ioctl handlers:
- Validate the ioctl code and expected buffer length early.
- Allocate a kernel buffer sized to hold the expected structure.
- Perform a checked copy_from_user into that kernel buffer and handle short copies or failures gracefully.
- Use the kernel buffer for internal processing and free or zeroize it on exit.
Affected systems and tions
Who should be concerned?- Systems that include the smscufx driver in their kernel build or distribute it as a kernel module. The driver has been present in many kernel series historically, and CONFIG_FB_SMSCUFX is the kernel build flag that enables it. Embedded images, specialized appliances, or older desktop kernels that retained fbdev support are the primary targets.
- Hosts that expose device nodes for USB framebuffers into containers or to untrusted processes. Any environment that maps /dev/fb* or the specific udev device node for UFX devices into sandboxes increases the attack surface.
- Organizations that accept user‑provided images, files, or devices where untrusted code could invoke the ioctl on an attached UFX device.
Recommended mitigations and remediation steps
For administrators and security teams, treat CVE‑2026‑23236 as a targeted kernel robustness fix requiring routine but prompt handling. Prioritize systems where untrusted users have access to device nodes.Short checklist:
- Inventory
- Identify hosts with CONFIG_FB_SMSCUFX compiled into their kernel or where smscufx is available as a module.
- Search for presence of the driver: check /lib/modules/$(uname -r)/ and kernel configs for FB_SMSCUFX.
- Identify whether the device node for the UFX device exists or whether screens using DisplayLink-like devices are attached.
- Apply vendor updates
- Install your distro/OEM kernel update that contains the upstream patch. Reboot if the vendor guidance requires it (most kernel updates do).
- If your vendor has pdate, monitor vendor advisories and kernel stable backport lists.
- Interim mitigations (if immediate patching is impossible)
- Restrict access to the framebuffer device node(s) so only trusted users or root can open them (chmod/chown/udev rules).
- Unload or blacklist the smscufx module on hosts that do not require attached UFX devices (modprobe -r smscufx; add to /etc/modprobe.d/blacklist.conf).
- In container platforms, avoid mapping framebuffer device nodes into untrusted containers and restrict CAP_SYS_ADMIN or device access where possible.
- Detection
- Watch dmesg and system logs for kernel oopses or traceback lines that mention smscufx functions, UFX_IOCTL_REPORT_DAMAGE, or unexpected invalid pointer dereferences.
- Correlate device open/close patterns and ioctl calls in logs with any crashes.
- For forensic response
- Collect full kernel logs, include oops traces and stack dumps, and preserve the unstable host for post‑mortem if exploitation is suspected.
- If an oops occurred, check whether a process opened the device shortly before the crash; that process or container may be the trigger.
Why this matters: broader implications for kernel ioctl design
CVE‑2026‑23236 is small in scope but instructive in two larger ways for kernel maintainers and security teams:- Ioctl surfaces are fragile by nature. They accept binary data from untrusted userspace and often carry custom formats. Small mistakes — forgetting a copy_from_user call or misvalidating length — produce disproportionately severe outcomes because they operate in kernel context.
- Legacy drivers and compatibility code accumulate patterns that predate modern auditing tools. Many code paths in drivers/video/fbdev were written when ioctls were common and trusted, and they sometimes rely on implicit expectations that no longer hold in modern threat models (containers, multi‑tenant cloud VMs, fuzzing). The kernel community’s ongoing approach of surgical fixes and conservative hardening is appropriate: prefer precise fixes that closndow rather than large rewrites that risk regressions.
Risk analysis — strengths and limitations of the fix
Strengths- The upstream fix is minimal and appears to follow standard secure‑coding practices (explicit copy and validated length), reducing regression risk.
- The change is straightforward to backport and audit, so distributions can reasonably include it in stable kernels without heavy integration cost.
- The vulnerability is local and requires access to device nodes; systems that intentionally expose devices to untrusted users or containers remain operationally risky unless mitigated. Blacklisting the module or tightening udev/device permissions is an operational control that must be enforced consistently.
- Small fixes of this kind do not eliminate the entire class of ioctl risks: other drivers with bespoke ioctls may still contain similar mistakes. Continued auditing and automated fuzzing of ioctl paths remain essential.
Conclusion and action plan
CVE‑2026‑23236 is a compact, fixable kernel robustness bug: an ioctl handler in fbdev’s smscufx driver failed to copy user data into kernel space before use. The correct, low‑risk mitigation is already recorded upstream and should be applied via vendor kernels as they become available. For administrators, the practical playbook is straightforward: inventory systems for the smscufx driver, apply vendor kernel updates that include the fix, and harden device access in environments that expose device nodes to untrusted code.This CVE is also a reminder that ioctl surfaces remain a recurring kernel hardening priority. Defensive coding — validated lengths, explicit copy_from_user, and minimal trust in userspace data — combined with operational controls such as device access restriction and careful container/device mapping, are the most effective defenses against this class of kernel vulnerability.
If you maintain kernels or device images that may carry the smscufx module, treat this as a routine but immediate maintenance item: patch, reboot where required, and verify that your images and containers do not expose framebuffer device nodes to untrusted workloads.
Source: MSRC Security Update Guide - Microsoft Security Response Center