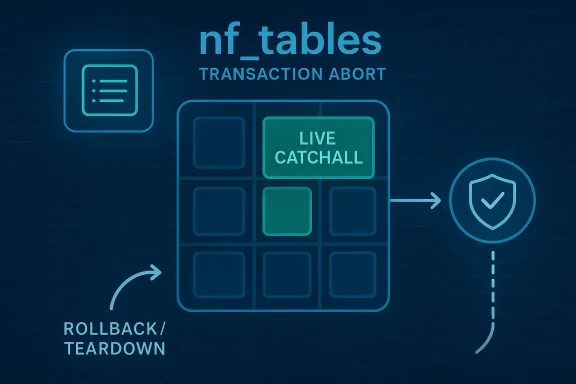
The Linux kernel’s nf_tables subsystem is once again in the security spotlight, this time for a flaw that looks subtle on paper but speaks volumes about how tricky transaction handling can be in kernel code. CVE-2026-23278 addresses a bug in catchall element cleanup, where the kernel may need to walk more than one pending catchall element during an abort path instead of stopping at the first viable candidate. The practical consequence is not just an ugly warning: it is a reminder that object lifetime, transaction rollback, and shared map teardown can collide in ways that destabilize the kernel’s internal accounting. Microsoft’s Security Update Guide and NVD both show the CVE as a fresh kernel.org disclosure from March 20, 2026, with the published description tied directly to the upstream fix and stable backports ore of the issue is straightforward, even if the code path is not. During an nf_tables transaction, the kernel can end up managing both a live catchall element and a pending catchall element that belongs to the next batch. If the map that holds those catchall elements is being torn down at the same time, the abort logic must toggle every relevant element, not merely the first one that appears usable. The upstream description says that failing to do so can trigger a warning in
That sounds like actness problem rather than a classic remote-code-execution bug, and that distinction matters. Kernel security issues are not all memory-corruption exploits; some are lifecycle failures that create use-after-free hazards, double-release conditions, or fatal assertions once the kernel’s internal invariants are violated. In this case, the bug lives in the awkward space where the control plane is trying to unwind partially prepared state while a set/map object is simultaneously disappearing. That is exactly the kind of situation where one skipped element can become one too few checks and one too many assumptions.
The interesting part is that the upstream fix is not a redesign. It is a correction in traversal discipline: walk all pending catchall elements, not just the first one that looks safe. That is usually a sign the maintainers are preserving an existing transaction model while tightening the abort path so that every catchall element that must be toggled actually gets toggled. In kernel terms, that is a surgical fix, but surgical does not mean trivial. It often means the bug sat at the intersection of several correct subsystems that were not sufficiently coordinated.
For WindowsForum readers, the relevance is broader than Linux administrators alone. Microsoft now surfaces Linux kernel CVEs in its vulnerability guidance because enterprise fleets increasingly straddle Windows, Linux, WSL-adjacent tooling, cloud images, containers, and hybrid management stacks. A kernel bug like this can therefore affect patch policy, compliance workflows, and vendor triage even where the affected hosts are not Windows systems at all .
The nf_tables subsystem is the modern netfilter rules engine in Linux, and it has become one of the most scrutinized parts of the kernel networking stack. It replaced older rule-management paths with a more flexible transactional design, but that flexibility comes at a cost: state changes are staged, validated, committed, or aborted in batches. When a subsystem works like a mini database engine inside the kernel, rollback correctness becomes just as important as steady-state performance.
That design has repeatedly produced security-relevant edge cases over the last several years. Linux kernel advisories around nf_tables have frequently involved inconsistencies in set element activation, catchall behavior, generation masks, and transaction rollback semantics. The reason is not mysterious. The subsystem supports rich rule composition, and rich rule composition means more opportunities for “this element is active now, pending next, or being destroyed while still referenced” mistakes. In a network stack, those mistakes become especially dangerous because the code is exposed to dynamic input and highly variable control flows.
The published CVE-2026-23278 description explicitly states that during transaction processing there may be both one live catchall element and one pending element arriving in the new batch. If the map containing those catchall elements is also being removed, the cleanup path must toggle every catchall element. The fix exists precisely because the abort path was not doing that before, which could provoke the warning in
This is not the first time catchall handling has mattered in nf_tables. security work around the same area dealt with catchall activation/deactivation logic, the interaction between current and next-generation masks, and the difficulty of ensuring that elements are retired exactly once. The recurring pattern suggests that “catchall” is not just a convenience feature; it is a lifecycle-sensitive object type whose semantics are easy to get wrong under batch updates and aborts.
There is also a policy angle here. Microsoft’s vulnerability portal is now part of the operational response chain for many enterprises, and once a Linux kernel CVE is indexed there, it becomes a triage item for teams that manage mixed estates. That is why a bug that looks like a kernel-internal cleanup issue still matters. It may not dominate headlines, but it can still land squarely in patch windows, risk dashboards, and downstream vendor advisories.
That kind of failure usually does not announce itself with dramatic symptoms. Instead, it surfaces as a warning, an unexpected release path, or a later crash in a function that assumes the invariant was already restored. In other words, the bug is upstream of the visible failure.
The kernel’s own description makes the failure mode concrete. It references a warning at
The fix therefore restores a broader invariant: if the map goes away, every pending catchall element that should be transitioned must be transitioned. That may sound boring, but boring is what correct kernel lifetime management looks like. The hard part is making sure the abort path is just as exhaustive as the commit path, especially when there are multiple generations of state in flight.
A helpful way to think about it is this: the kernel was trying to tidy up a room while forgetting that there were two piles of objects, not one. If it only gathered the first pile, the second could later trip the cleanup crew.
The CVE description shows that one live catchall element and one pending element can coexist during transaction processing . That coexistence is legitimate, but it imposes a strong burden on cleanup logic. If the map goes away, both statesd. If only one is handled, the kernel can be left with a dangling model of what is active and what has been deactivated.
This is a good example of why data structure semantics matter as much as memory safety in kernel security. You do not need an out-of-bounds write to create a serious bug. If the internal bookkeeping says one thing while ownership and generation state say another, a later helper may free something that still appears live or preserve something that should already be gone.
The most likely consequence is a warning first, but warnings in kernel code are often proxies for deeper trouble. The excerpt names
Kernel maintainers are oftee issues before they become exploitable, and that seems to be what happened here. The published references include stable kernel commits on the kernel.org stable tree, which indicates the patch is already part of the upstream remediation stream . That is a strong clue that maintainers considered the bug concrete and important enough for backporting.
The important competitive and architectural takeaway is that nf_tables is becoming more capable while also more complex. That is not a criticism; it is the natural price of modern rule management. But every additional feature such as batch updates, pending generations, or catchall semantics multiplies the number of states the kernel must reconcile when things go wrong. Security bugs often emerge where a subsystem is trying to be both fast and expressive.
This CVE is therefore less about one line of broken code than about the permanent difficulty of building a transactional policy engine inside the kernel. The abort logic needs to behave as if it is a database rollback, a memory manager, and a consistency checker all at once. That is a high bar, and nf_tables keeps paying for the complexity with a steady stream of fixes in the surrounding area.
Hybrid environments make this more important than it might appear. Microsoft’s security portal indexes Linux CVEs because many enterprise fleets now mix Windows management tooling with Linux workloads, and security teams want one place to track exposure. That means a Linux kernel issue can land in the same remediation queue as Windows updates, cloud image refreshes, and appliance firmware changes. The operational burden is real even when the technical flaw is narrowly scoped.
There is also a practical angle around backports. The kernel.org stable references indicate that the fix has already been pushed into the stable pipeline, which matters because most enterprises do not run mainline kernels in production. They run vendor kernels, long-term support branches, or appliance images that cherry-pick stable fixes. In other words, the patch path matters almost as much as the vulnerability itself.
The user-facing effect is usually indirect. A device might reboot under load, log warnings, or become unstable after a configuration change or rollback. Because these products are often managed through vendor firmware rather than generic Linux package managers, the remediation path can be slower and more opaque than on a desktop distro. That is one reason kernel CVEs in networking subsystems can linger in edge appliances long after upstream has issued a fix.
There is also an ecosystem lesson here. Edge hardware tends to get updated less frequently than servers, but it often sits directly on the Internet or at the boundary of a local network. That combination makes even a “cleanup bug” worth attention. If the wrong transaction abort can produce kernel instability, attackers and crash-inducing traffic both become part of the operational threat model.
The other strength is that the fix reflects disciplined kernel engineering. Rather than layering on complex new logic, it corrects the traversal behavior in the abort path. That is usually the right way to address a cleanup bug because it minimizes collateral risk while restoring the intended invariant.
Another concern is that the published description does not yet include an NVD severity score. That is not unusual this soon after publication, but it does mean some downstream tooling may still be waiting for a richer risk classification. In practice, that can delay prioritization in organizations that rely too heavily on scored feeds rather than on the technical description itself.
It will also be worth watching whether later advisories or hardening patches emerge around related nf_tables cleanup paths. Historically, fixes in this area tend to cluster because one corrected invariant often reveals neighboring assumptions that were never fully enforced. In that sense, CVE-2026-23278 may be less an endpoint than another marker in an ongoing cleanup campaign.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
nft_data_release() while aborting a batch, with the failure propagating through __nft_set_elem_destroy(), nf_tables_abort_release(), and nf_tables_abort() before the netlink batch machinery unwinds the transaction .That sounds like actness problem rather than a classic remote-code-execution bug, and that distinction matters. Kernel security issues are not all memory-corruption exploits; some are lifecycle failures that create use-after-free hazards, double-release conditions, or fatal assertions once the kernel’s internal invariants are violated. In this case, the bug lives in the awkward space where the control plane is trying to unwind partially prepared state while a set/map object is simultaneously disappearing. That is exactly the kind of situation where one skipped element can become one too few checks and one too many assumptions.
The interesting part is that the upstream fix is not a redesign. It is a correction in traversal discipline: walk all pending catchall elements, not just the first one that looks safe. That is usually a sign the maintainers are preserving an existing transaction model while tightening the abort path so that every catchall element that must be toggled actually gets toggled. In kernel terms, that is a surgical fix, but surgical does not mean trivial. It often means the bug sat at the intersection of several correct subsystems that were not sufficiently coordinated.
For WindowsForum readers, the relevance is broader than Linux administrators alone. Microsoft now surfaces Linux kernel CVEs in its vulnerability guidance because enterprise fleets increasingly straddle Windows, Linux, WSL-adjacent tooling, cloud images, containers, and hybrid management stacks. A kernel bug like this can therefore affect patch policy, compliance workflows, and vendor triage even where the affected hosts are not Windows systems at all .
 Background
Background
The nf_tables subsystem is the modern netfilter rules engine in Linux, and it has become one of the most scrutinized parts of the kernel networking stack. It replaced older rule-management paths with a more flexible transactional design, but that flexibility comes at a cost: state changes are staged, validated, committed, or aborted in batches. When a subsystem works like a mini database engine inside the kernel, rollback correctness becomes just as important as steady-state performance.That design has repeatedly produced security-relevant edge cases over the last several years. Linux kernel advisories around nf_tables have frequently involved inconsistencies in set element activation, catchall behavior, generation masks, and transaction rollback semantics. The reason is not mysterious. The subsystem supports rich rule composition, and rich rule composition means more opportunities for “this element is active now, pending next, or being destroyed while still referenced” mistakes. In a network stack, those mistakes become especially dangerous because the code is exposed to dynamic input and highly variable control flows.
The published CVE-2026-23278 description explicitly states that during transaction processing there may be both one live catchall element and one pending element arriving in the new batch. If the map containing those catchall elements is also being removed, the cleanup path must toggle every catchall element. The fix exists precisely because the abort path was not doing that before, which could provoke the warning in
nft_data_release() and associated destruction routines .This is not the first time catchall handling has mattered in nf_tables. security work around the same area dealt with catchall activation/deactivation logic, the interaction between current and next-generation masks, and the difficulty of ensuring that elements are retired exactly once. The recurring pattern suggests that “catchall” is not just a convenience feature; it is a lifecycle-sensitive object type whose semantics are easy to get wrong under batch updates and aborts.
There is also a policy angle here. Microsoft’s vulnerability portal is now part of the operational response chain for many enterprises, and once a Linux kernel CVE is indexed there, it becomes a triage item for teams that manage mixed estates. That is why a bug that looks like a kernel-internal cleanup issue still matters. It may not dominate headlines, but it can still land squarely in patch windows, risk dashboards, and downstream vendor advisories.
Why transaction rollback is hard
A transaction system is only as safe as its rollback path. In kernel code, rollback has to account for objects that were partially created, partially linked, or partially deactivated when something else went wrong. The nftables case is especially delicate because the rules engine can hold on to pending state from a new batch while older live state still exists. If cleanup only handles the first valid candidate, the rest of the state machine may remain in an impossible half-freed condition.That kind of failure usually does not announce itself with dramatic symptoms. Instead, it surfaces as a warning, an unexpected release path, or a later crash in a function that assumes the invariant was already restored. In other words, the bug is upstream of the visible failure.
What the Vulnerability Changes
The upstream fix changes the behavior of the abort path so it continues walking all pending catchall elements rather than stopping when it finds the first one that can be toggled. That matters because the transaction may include more than one catchall element, and each of them may need to be normalized before the map disappears. A rollback path that only handles a single element can leave the rest of the batch inconsistent with the teardown state.The kernel’s own description makes the failure mode concrete. It references a warning at
./include/net/netfilter/nf_tables.h:1281 inside nft_data_release(), with the call chain flowing through __nft_set_elem_destroy(), nf_tables_abort_release(), nf_tables_abort(), and nfnetlink_rcv_batch() during an abort sequence . That is exactly the sort of breadcrumb trail that tells experienced kernel readers this is no warning in a release path often means the code has encountered an object whose ownership or activity state is no longer what the helper functions expected.The fix therefore restores a broader invariant: if the map goes away, every pending catchall element that should be transitioned must be transitioned. That may sound boring, but boring is what correct kernel lifetime management looks like. The hard part is making sure the abort path is just as exhaustive as the commit path, especially when there are multiple generations of state in flight.
The shape of the bug
At a high level, the bug appears to be a state-coverage problem, not a parser bug and not a privilege-boundary mistake. That means the issue is about completeness of cleanup rather than validation of external input. In kernel engineering, those bugs are often underappreciated because they do not fit the classic exploit narrative. Yet they still matter because rollback code runs in error conditions, and error conditions are where assumptions are most likely to be wrong.A helpful way to think about it is this: the kernel was trying to tidy up a room while forgetting that there were two piles of objects, not one. If it only gathered the first pile, the second could later trip the cleanup crew.
Why Catchall Elements Are Special
Catchall elements are not ordinary list entries. They act as a broad routing or matching mechanism in set and map logic, and that makes their lifecycle especially sensitive. They are also likely to be touched by batch operations that update active rules while staging new ones, which means their active/pending distinction has to remain crystal clear at every point in the transaction.The CVE description shows that one live catchall element and one pending element can coexist during transaction processing . That coexistence is legitimate, but it imposes a strong burden on cleanup logic. If the map goes away, both statesd. If only one is handled, the kernel can be left with a dangling model of what is active and what has been deactivated.
This is a good example of why data structure semantics matter as much as memory safety in kernel security. You do not need an out-of-bounds write to create a serious bug. If the internal bookkeeping says one thing while ownership and generation state say another, a later helper may free something that still appears live or preserve something that should already be gone.
Catchall lifecycle in practice
The abort path is the worst place to be lazy. Commit paths are already complicated, but abort paths are worse because they must reverse partially completed work in the face of uncertainty. That means they need to be more thorough than the happy path, not less. The new fix reflects that philosophy by insisting the kernel walk all pending catchall elements instead of trusting the first one that looks eligible.- Pending and live states can overlap during batch processing.
- Teardown can invalidate assumptions made earlier in the transaction.
- Cleanup must be exhaustive when multiple catchall elements exist.
- A partial rollback can leave stale ownership metadata behind.
- Kernel warnings in release paths often indicate invariant breakage, not harmless noise.
The Abort Path and Its Consequences
The abort path is where many kernel bugs become visible because it is where the code has to reconcile “what was planned” with “what is now true.” In CVE-2026-23278, the problem arises when the abort machinery does not visit every pending catchall element before the map disappears. That means object destruction can happen before the associated element state has been properly toggled.The most likely consequence is a warning first, but warnings in kernel code are often proxies for deeper trouble. The excerpt names
nft_data_release() as the assertion point, which suggests the kernel is checking whether a data object is being released in a way that violates its expected generation or activity state . If that check fails, it is because the release path has wandered into territory the author did not expect.Kernel maintainers are oftee issues before they become exploitable, and that seems to be what happened here. The published references include stable kernel commits on the kernel.org stable tree, which indicates the patch is already part of the upstream remediation stream . That is a strong clue that maintainers considered the bug concrete and important enough for backporting.
Why warnings matter
A kernel warning is not jroduction environment, a warning may be the first sign that the kernel has encountered a logical contradiction in its own state machine. Even when it does not immediately crash the machine, it can point to the exact kind of flaw that later becomes a use-after-free, double-destroy, or rollback corruption issue. That is why operators should not treat release-path warnings as benign.- Warnings often mark invariant violations.
- Invariant violations often precede crashes or data corruption.
- Abort paths are especially hard to test exhaustively.
- A fix that broadens traversal can prevent future partial cleanup bugs.
- Kernel backports are a sign the issue matters operationally.
How It Fits the nf_tables Pattern
CVE-2026-23278 fits a familiar nf_tables pattern: the bug is rooted in transaction semantics, not in simple input validation. That is a recurring theme across the subsystem. The kernel has had to harden set element handling, generation checking, and state transitions repeatedly because the rules engine is designed to be flexible, and flexibility invites edge cases.The important competitive and architectural takeaway is that nf_tables is becoming more capable while also more complex. That is not a criticism; it is the natural price of modern rule management. But every additional feature such as batch updates, pending generations, or catchall semantics multiplies the number of states the kernel must reconcile when things go wrong. Security bugs often emerge where a subsystem is trying to be both fast and expressive.
This CVE is therefore less about one line of broken code than about the permanent difficulty of building a transactional policy engine inside the kernel. The abort logic needs to behave as if it is a database rollback, a memory manager, and a consistency checker all at once. That is a high bar, and nf_tables keeps paying for the complexity with a steady stream of fixes in the surrounding area.
Historical context
Linux networking code has long had to manage state across asynchronous or batch-style operations. What makes nf_tables distinct is that it codifies more of that state management in the rules engine itself. That gives administrators powerful capabilities, but it also means bugs in the engine can have a broader blast radius than older, simpler packet-filtering models. In practice, this creates a tradeoff between operational flexibility and the need for very disciplined cleanup logic.Enterprise Impact
For enterprise administrators, the biggest concern is not the headline CVSS score — NVD had not assigned one at the time of publication — but the reliability and observability impact of a kernel bug in a core networking subsystem . A warning in a busy firewall, router, container host, or ingress node can quickly become a service-affecting event if the affected code sits on a critical traffic path. Even if diately become exploitable, it can still create instability and trust issues for kernel-based policy enforcement.Hybrid environments make this more important than it might appear. Microsoft’s security portal indexes Linux CVEs because many enterprise fleets now mix Windows management tooling with Linux workloads, and security teams want one place to track exposure. That means a Linux kernel issue can land in the same remediation queue as Windows updates, cloud image refreshes, and appliance firmware changes. The operational burden is real even when the technical flaw is narrowly scoped.
There is also a practical angle around backports. The kernel.org stable references indicate that the fix has already been pushed into the stable pipeline, which matters because most enterprises do not run mainline kernels in production. They run vendor kernels, long-term support branches, or appliance images that cherry-pick stable fixes. In other words, the patch path matters almost as much as the vulnerability itself.
Who should care most
- Firewall and router operators using Linux-based packet filtering.
- Container platform teams that rely on nf_tables for host policy.
- Cloud operations teams managing mixed Linux estates.
- OEMs and appliance vendors shipping customized kernels.
- Security teams responsible for stable-branch patch verification.
- Incident responders investigating unexplained kernel warnings.
- Compliance teams mapping CVEs to remediation evidence.
Consumer and Edge-Device Impact
Consumers may never notice nf_tables directly, but they can still be affected through products that embed Linux networking stacks. Home routers, edge gateways, SD-WAN devices, and small-business appliances often rely on nftables-based policy engines under the hood. When those devices fail to handle cleanup paths correctly, the symptom may be a crash, a reset, or a degraded management experience rather than a neat security advisory in the UI.The user-facing effect is usually indirect. A device might reboot under load, log warnings, or become unstable after a configuration change or rollback. Because these products are often managed through vendor firmware rather than generic Linux package managers, the remediation path can be slower and more opaque than on a desktop distro. That is one reason kernel CVEs in networking subsystems can linger in edge appliances long after upstream has issued a fix.
There is also an ecosystem lesson here. Edge hardware tends to get updated less frequently than servers, but it often sits directly on the Internet or at the boundary of a local network. That combination makes even a “cleanup bug” worth attention. If the wrong transaction abort can produce kernel instability, attackers and crash-inducing traffic both become part of the operational threat model.
Why edge devices are different
Edge systems are often underpowered, remotely managed, and hard to inspect. That makes kernel warnings harder to notice and slower to triage. It also means a small defect in packet-filtering infrastructure can take out a whole branch office or a remote site without much warning. In that context, a bug in transaction cleanup is not theoretical bookkeeping; it is a device availability problem.Strengths and Opportunities
The good news is that this fix is narrow, understandable, and already documented through the kernel’s upstream and stable channels. That makes it easier for vendors and administrators to map exposure and verify remediation. It also shows that the Linux networking maintainers are catching the issue before it turns into a broader memory-safety story.The other strength is that the fix reflects disciplined kernel engineering. Rather than layering on complex new logic, it corrects the traversal behavior in the abort path. That is usually the right way to address a cleanup bug because it minimizes collateral risk while restoring the intended invariant.
- The fix is upstream and already referenced in stable kernel commits.
- The bug description is clear enough for downstream vendors to map exposure.
- The remediation is a focused traversal correction, not a sweeping redesign.
- The issue highlights strong review pressure on nftables transaction code.
- Administrators can use kernel warnings as an indicator of possible impact.
- The CVE shows active maintenance rather than neglected code.
- Enterprise patch teams can prioritize by kernel branch and vendor release.
Risks and Concerns
The obvious concern is that cleanup-path bugs can be hard to reproduce and easy to dismiss until they show up in the wrong environment. If a system only occasionally exercises the combination of live and pending catchall elements during teardown, the bug may sit quietly in production until a configuration churn event triggers it. That makes it sporadic in the worst possible way.Another concern is that the published description does not yet include an NVD severity score. That is not unusual this soon after publication, but it does mean some downstream tooling may still be waiting for a richer risk classification. In practice, that can delay prioritization in organizations that rely too heavily on scored feeds rather than on the technical description itself.
- Partial rollback bugs can hide until unusual state combinations occur.
- Kernel warnings may precede more severe consequences.
- Vendors may lag on stable backports for older product branches.
- Edge devices can be harder to patch than servers.
- Lack of a finalized NVD score can slow internal triage.
- Transaction bugs often evade ordinary test coverage.
- Mixed Linux/Windows workflows can complicate ownership of remediation.
Looking Ahead
The next thing to watch is how quickly downstream vendors pick up the stable fix. In kernel security, the upstream patch is only the start; the real exposure window closes when distro maintainers and appliance vendors carry the fix into their supported branches. That process can be rapid for mainstream server distros and much slower for embedded products.It will also be worth watching whether later advisories or hardening patches emerge around related nf_tables cleanup paths. Historically, fixes in this area tend to cluster because one corrected invariant often reveals neighboring assumptions that were never fully enforced. In that sense, CVE-2026-23278 may be less an endpoint than another marker in an ongoing cleanup campaign.
What to watch
- Stable kernel backport availability across major Linux branches.
- Vendor advisories for firewall, router, and appliance products.
- Any follow-on fixes in nftables abort or destroy code.
- Whether NVD later assigns a severity score and vector.
- Reports of kernel warnings tied to
nft_data_release()or set destruction. - Patch uptake in container hosts and network-policy-heavy fleets.
Practical next steps for operators
- Check whether your Linux estate uses nftables-based policy management.
- Identify kernel versions that include the upstream stable fix.
- Verify vendor advisories for embedded and appliance deployments.
- Monitor logs for abort-path warnings in networking subsystems.
- Prioritize updates on systems that rewrite firewall policy frequently.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center