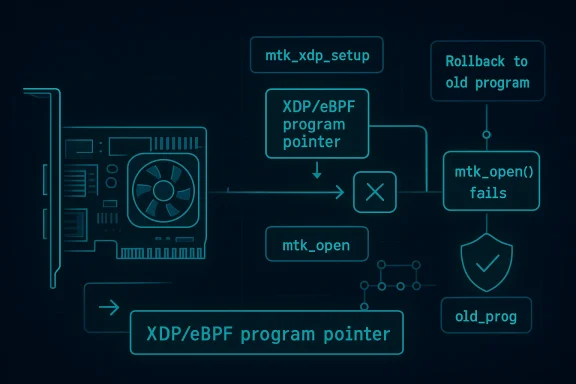
In the Linux kernel’s own security model, CVE-2026-23284 is the kind of bug that looks small on paper but matters because it sits in driver state management, one of the most failure-prone layers of the stack. The issue is described as a fix for mtk_eth_soc’s mtk_xdp_setup() path: if mtk_open() fails, the code must restore the old eBPF program pointer and avoid dropping its reference count prematurely. That makes this more than a housekeeping patch; it is a correction to object lifetime handling, which is exactly the sort of subtle mistake the kernel team tends to catalog through CVEs once a fix exists in a stable tree //www.kernel.org/doc/html/latest/process/cve.html))
Linux kernel CVEs are not assigned only for dramatic exploits. The kernel project explicitly says that it assigns CVEs after fixes are available in stable trees, and that it is intentionally cautious because even bugs that do not immediately look exploitable can still compromise security or system correctness under the right conditions (kernel.org). That policy matters here because CVE-2026-23284 appears to be a correctness and lifecycle flaw rather than an obvious memory-corruption primitive.
The affected code sits in the MediaTek Ethernet driver stack, specifically the path that configures XDP and eBPF program attachment. XDP has become a key performance and packet-processing feature for Linux networking, so even small errors in its control flow can ripple into packet handling, device bring-up, and failover behavior. In other words, a bug in a low-level network driver can become an enterprise problem long before it becomes an obvious security incident.
The published description is terse but revealing: reset the program pointer to old_prog if mtk_open() fails, and do not decrement the program’s refcount in that failure path. That is classic kernel lifecycle language. It implies there is a state transition where the driver tentatively swaps in a new program, then needs to unwind safely if initialization does not complete. When that unwind is imperfect, you can end up with stale pointers, premature cleanup, or a mismatch between what the driver thinks is attached and what is actually active.
That kind of flaw is particularly important in networking because driver state tends to be exercised under load, during resets, or while services are being reconfigured. Those are precisely the moments when operators least want ambiguity. A failure path that leaves the system in an inconsistent state can be hard to reproduce, hard to diagnose, and easy to misclassify as a transient hardware or firmware issue.
Microsoft’s Security Update Guide has become one of the places enterprise defenders encounter Linux CVEs, even when the actual fix originates upstream in kernel.org. Microsoft has been steadily expanding its advisory model to surface CVEs and supporting metadata in a cross-platform way, while the Linux kernel project maintains that CVEs are tied to fixes already present in released kernel trees (kernel.org). The practical result is a broader remediation ecosystem: one identifier, multiple vendor channels, and a need for defenders to understand the underlying kernel behavior rather than just the label.
That sounds narrow, but kernel bugs often live in the exact seam between speculative state changes and error unwinding. The code may have been written assuming the setup path would succeed often enough that the error branch felt secondary. In kernel work, though, the secondary path is where correctness problems tend to hide.
In a networking driver, that can produce crashes, use-after-free conditions, or subtle misrouting of later requests. Even if the exact impact remains limited to stability in many deployments, the kernel community treats these as security-relevant because lifecycle errors are often the seed of more serious issues.
That sort of inconsistency can lead to incorrect packet-processing decisions, misleading telemetry, or cleanup routines targeting the wrong object. In a subsystem as stateful as XDP, that is dangerous because the control plane and data plane need to agree.
A MediaTek Ethernet driver is not just another peripheral driver in this context. It is part of the infrastructure that may carry production traffic in embedded systems, appliances, routers, and low-cost servers. If XDP attachment is left in a confused state after a setup failure, operators may see inconsistent packet handling, missing acceleration, or a driver that behaves differently after a reconfiguration attempt.
That makes cleanup paths just as important as setup paths. If the system is designed to optimize the fast path but leaves the error path under-tested, then the most advanced feature can become the most fragile one.
That is especially true where object ownership is concerned. A pointer can be restored only if the lifetime accounting also rolls back correctly. Otherwise, the code may point at the right object while the refcount says that object is already on its way out.
The fix’s wording also suggests that maintainers consider the original issue narrow enough to patch without redesigning the subsystem. That is a good sign: it implies the bug is localized, the intended behavior is understood, and the problem can be eliminated without destabilizing unrelated functionality.
For administrators, the key question is not whether a CVE exists in the abstract. It is whether the running kernel includes the corrected error path. That requires version tracking, vendor advisory review, and sometimes validation of backported patches rather than relying on upstream commit names alone.
This is best treated as a kernel correctness vulnerability with possible operational consequences. It does not, based on the published description, advertise a direct privilege-escalation chain or an obvious memory-corruption primitive. But kernel bugs that affect object ownership, program attachment, and error unwinding are exactly the sort of issues that can create unstable or unsafe states.
A more responsible interpretation is that this CVE is narrow but real. It deserves patching where the affected driver exists, and it deserves attention from operators who rely on MediaTek-based Linux systems.
That makes CVE-2026-23284 a useful example of how modern kernel security actually works. A driver opens a device, swaps a program pointer, and then needs to unwind cleanly when initialization fails. The security significance is embedded in the routine mechanics of setup and teardown, not in an obviously malicious input.
In practice, this means that small defects in error handling can persist for a long time because they do not always show up during standard validation. The system may work perfectly under normal conditions and fail only when a device reset or partial initialization occurs. That makes field testing, fault injection, and robust code review essential.
The second question is whether the affected systems live in a class of deployment where driver instability is expensive. Appliances, edge devices, and embedded gateways often fit that description. In those environments, even a low-drama bug can translate into outages, restart cycles, or unpredictable behavior during reconfiguration.
This is why CVE identifiers are helpful but insufficient. The identifier gives teams a shared vocabulary; the actual fix validation still has to happen per platform and per build.
That matters because a growing number of security operations teams do not separate Windows, Linux, firmware, and cloud host advisories into unrelated processes. They feed into one patch-priority pipeline. A Linux kernel CVE appearing in Microsoft’s ecosystem therefore becomes part of a larger enterprise workflow, especially for organizations with mixed infrastructure.
That tension is why high-quality upstream metadata matters. The more accurately the fix is described, the easier it is for downstream vendors and operators to make good decisions.
A second thing to watch is whether this prompts a broader look at other XDP and driver setup paths in network subsystems. Once a failure-path bug is identified in one place, maintainers often revisit adjacent code for similar asymmetries. That kind of review can pay dividends, especially in fast-moving areas like eBPF and NIC offload support.
A third thing to watch is how vendors ultimately score the issue. NVD’s enrichment process was still pending at publication time, so severity guidance may evolve. That will matter for prioritization, but it should not be the trigger for action. The trigger is whether the kernel in production includes the corrected rollback logic.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Background
Background
Linux kernel CVEs are not assigned only for dramatic exploits. The kernel project explicitly says that it assigns CVEs after fixes are available in stable trees, and that it is intentionally cautious because even bugs that do not immediately look exploitable can still compromise security or system correctness under the right conditions (kernel.org). That policy matters here because CVE-2026-23284 appears to be a correctness and lifecycle flaw rather than an obvious memory-corruption primitive.The affected code sits in the MediaTek Ethernet driver stack, specifically the path that configures XDP and eBPF program attachment. XDP has become a key performance and packet-processing feature for Linux networking, so even small errors in its control flow can ripple into packet handling, device bring-up, and failover behavior. In other words, a bug in a low-level network driver can become an enterprise problem long before it becomes an obvious security incident.
The published description is terse but revealing: reset the program pointer to old_prog if mtk_open() fails, and do not decrement the program’s refcount in that failure path. That is classic kernel lifecycle language. It implies there is a state transition where the driver tentatively swaps in a new program, then needs to unwind safely if initialization does not complete. When that unwind is imperfect, you can end up with stale pointers, premature cleanup, or a mismatch between what the driver thinks is attached and what is actually active.
That kind of flaw is particularly important in networking because driver state tends to be exercised under load, during resets, or while services are being reconfigured. Those are precisely the moments when operators least want ambiguity. A failure path that leaves the system in an inconsistent state can be hard to reproduce, hard to diagnose, and easy to misclassify as a transient hardware or firmware issue.
Microsoft’s Security Update Guide has become one of the places enterprise defenders encounter Linux CVEs, even when the actual fix originates upstream in kernel.org. Microsoft has been steadily expanding its advisory model to surface CVEs and supporting metadata in a cross-platform way, while the Linux kernel project maintains that CVEs are tied to fixes already present in released kernel trees (kernel.org). The practical result is a broader remediation ecosystem: one identifier, multiple vendor channels, and a need for defenders to understand the underlying kernel behavior rather than just the label.
What the bug is doing
At the heart of this CVE is a rollback problem. The driver appears to temporarily replace an existing eBPF/XDP program pointer, then calls into mtk_open() as part of setup. If that open operation fails, the code must restore the original pointer and preserve the original reference-counting state. If it does not, the driver can end up with a program pointer that no longer matches the actual device state.That sounds narrow, but kernel bugs often live in the exact seam between speculative state changes and error unwinding. The code may have been written assuming the setup path would succeed often enough that the error branch felt secondary. In kernel work, though, the secondary path is where correctness problems tend to hide.
Why the refcount detail matters
The CVE description is explicit that the refcount for the old program should not be decreased if mtk_open() fails. That tells us the bug is not merely cosmetic. Reference counts govern lifetime, ownership, and release timing. If you drop a refcount too early, you risk freeing or invalidating an object while some part of the driver still believes it is valid.In a networking driver, that can produce crashes, use-after-free conditions, or subtle misrouting of later requests. Even if the exact impact remains limited to stability in many deployments, the kernel community treats these as security-relevant because lifecycle errors are often the seed of more serious issues.
Why the pointer reset matters
Restoring prog to old_prog is equally important. A kernel driver’s internal pointers are not just bookkeeping; they are the live source of truth for later operations. If the pointer remains switched to a failed candidate program, subsequent code may behave as if the new program were active when the open step never completed.That sort of inconsistency can lead to incorrect packet-processing decisions, misleading telemetry, or cleanup routines targeting the wrong object. In a subsystem as stateful as XDP, that is dangerous because the control plane and data plane need to agree.
- The bug affects a failure path, not the happy path.
- It involves state rollback, which is notoriously easy to get wrong.
- The issue is tied to program ownership and reference counting.
- The observable impact may vary by device usage and timing.
- The fix is surgical, but the underlying discipline is fundamental.
Why XDP makes this more sensitive
XDP has become one of the Linux networking stack’s most performance-sensitive extension points. It allows eBPF programs to operate very early in the packet path, which is exactly why it is attractive for filtering, load-balancing, traffic steering, and observability. That also means failures around XDP setup are not trivial administrative nuisances; they can alter how a NIC behaves under real traffic.A MediaTek Ethernet driver is not just another peripheral driver in this context. It is part of the infrastructure that may carry production traffic in embedded systems, appliances, routers, and low-cost servers. If XDP attachment is left in a confused state after a setup failure, operators may see inconsistent packet handling, missing acceleration, or a driver that behaves differently after a reconfiguration attempt.
Performance features need rigorous unwind paths
The security problem here is not that XDP exists; it is that high-performance code paths increase the cost of sloppiness. Drivers that support advanced packet processing often carry multiple layers of state: device readiness, queue configuration, attached programs, and refcounted objects that all have to agree.That makes cleanup paths just as important as setup paths. If the system is designed to optimize the fast path but leaves the error path under-tested, then the most advanced feature can become the most fragile one.
Enterprise impact versus consumer impact
For consumers, this bug may never surface unless they run hardware or workloads that actually exercise the affected driver path. For enterprises, especially those deploying embedded Linux, network appliances, or managed gateways, the story is different. These environments often care more about driver predictability than raw benchmark numbers.- Consumer risk is likely limited to affected hardware and workloads.
- Enterprise risk is amplified by scale, uptime requirements, and patch lag.
- Embedded deployments may keep kernels in service for years.
- Network appliances can be sensitive to even minor packet-path inconsistencies.
- Managed fleets need precise version mapping to ensure the fix is actually present.
What the fix suggests about the original design
The language of the fix tells us a lot about the shape of the original code. The driver likely performed a state transition without making the unwind logic fully symmetric. In well-written kernel code, every successful temporary ownership change should have a matching rollback. If the open step fails, the driver must return to the exact previous state, not just something that looks close enough.That is especially true where object ownership is concerned. A pointer can be restored only if the lifetime accounting also rolls back correctly. Otherwise, the code may point at the right object while the refcount says that object is already on its way out.
Symmetry is a security property
This is one of those cases where software design discipline has direct security value. Symmetric cleanup is not just elegant; it reduces the chance that a partially completed operation leaves the driver in an inconsistent state. In kernel networking, inconsistent state can become a reliability bug, and reliability bugs can become security bugs when they are reachable from untrusted inputs or repeated operational actions.The fix’s wording also suggests that maintainers consider the original issue narrow enough to patch without redesigning the subsystem. That is a good sign: it implies the bug is localized, the intended behavior is understood, and the problem can be eliminated without destabilizing unrelated functionality.
Why stable backporting matters
The Linux kernel documentation explains that CVEs are assigned as part of the stable release process after fixes are available, and that users should not assume a CVE applies universally to all systems because kernel relevance depends on the specific code in use (kernel.org). This is important operationally. A fix that is simple upstream may still need careful backporting across vendor trees and long-term support branches.For administrators, the key question is not whether a CVE exists in the abstract. It is whether the running kernel includes the corrected error path. That requires version tracking, vendor advisory review, and sometimes validation of backported patches rather than relying on upstream commit names alone.
How to interpret the severity
The current record shows NVD enrichment pending, with no assigned CVSS score at publication time. That is often a sign that the ecosystem has agreed a fix exists, but the formal scoring process has not yet fully caught up. In practical terms, that means defenders should avoid assuming the issue is benign just because a score is missing, and they should also avoid overstating it as catastrophic without evidence.This is best treated as a kernel correctness vulnerability with possible operational consequences. It does not, based on the published description, advertise a direct privilege-escalation chain or an obvious memory-corruption primitive. But kernel bugs that affect object ownership, program attachment, and error unwinding are exactly the sort of issues that can create unstable or unsafe states.
What not to assume
It would be a mistake to assume this is only a MediaTek problem in the consumer sense. Linux kernel CVEs often affect only some configurations, but those configurations can matter a great deal in production. Likewise, it would be a mistake to dismiss the lack of a CVSS score as evidence that the issue is minor. NVD’s scoring sometimes lags the publication of the kernel fix.A more responsible interpretation is that this CVE is narrow but real. It deserves patching where the affected driver exists, and it deserves attention from operators who rely on MediaTek-based Linux systems.
- Do not assume the bug is harmless because it is path-specific.
- Do not assume the absence of a CVSS score means no action is needed.
- Do verify whether your kernel tree includes the corrected rollback logic.
- Do treat driver unwind paths as security-relevant code.
- Do validate vendor backports, not just upstream version numbers.
Why this matters beyond one driver
This CVE is part of a broader trend in Linux security: the industry is increasingly paying attention to state management bugs rather than only headline-grabbing memory corruptions. The kernel project’s own guidance acknowledges that many bugs can be exploitable in ways that are not obvious at the time of the fix, which is why CVE assignment follows the stable-fix path rather than waiting for a public exploit chain (kernel.org).That makes CVE-2026-23284 a useful example of how modern kernel security actually works. A driver opens a device, swaps a program pointer, and then needs to unwind cleanly when initialization fails. The security significance is embedded in the routine mechanics of setup and teardown, not in an obviously malicious input.
The role of error paths in modern kernels
The more complex a subsystem becomes, the more important its error handling becomes. XDP, eBPF, hardware acceleration, and driver lifecycle all interact here. Each layer adds another place where an object can be acquired, referenced, conditionally swapped, or dropped.In practice, this means that small defects in error handling can persist for a long time because they do not always show up during standard validation. The system may work perfectly under normal conditions and fail only when a device reset or partial initialization occurs. That makes field testing, fault injection, and robust code review essential.
What enterprises should infer
For enterprise teams, this is not just a MediaTek issue. It is a reminder to review how network drivers handle setup failures across the fleet. If a kernel update fixes one pointer rollback problem in one driver, there may be similar latent issues in other code paths.- Audit error unwinding in packet-processing drivers.
- Treat refcount mismatches as security-relevant, not merely cosmetic.
- Track kernel updates by actual fixed build, not only by CVE label.
- Include hardware-specific drivers in patch planning.
- Remember that failure paths are often the least-tested paths.
Operational implications for administrators
For administrators, the first question is simple: does the deployed kernel include the fix? Because the Linux kernel community ties CVEs to stable fixes and because applicability depends on the local kernel tree and configuration, the relevant step is version verification, not general awareness alone (kernel.org). If your systems do not use the affected MediaTek Ethernet path, the practical exposure may be limited. If they do, the patch should be treated as routine but important.The second question is whether the affected systems live in a class of deployment where driver instability is expensive. Appliances, edge devices, and embedded gateways often fit that description. In those environments, even a low-drama bug can translate into outages, restart cycles, or unpredictable behavior during reconfiguration.
What to check first
A good response sequence is straightforward:- Confirm whether the Linux kernel version in use contains the corrected mtk_xdp_setup() logic.
- Determine whether the hardware fleet actually uses mtk_eth_soc or related MediaTek Ethernet support.
- Review vendor advisories for backported fixes under distribution-specific build numbers.
- Prioritize remediation on systems with XDP or eBPF networking features enabled.
- Verify that the old program pointer and refcount handling are correct in the shipped tree.
Why mixed fleets complicate this
Modern enterprises rarely run a single kernel stream. They operate a mix of vendor images, cloud templates, edge appliances, containers, and long-lived embedded systems. That makes CVE handling more complicated than just “install the patch.” The same vulnerability may be fixed upstream, backported by one vendor, delayed by another, and still absent from a custom image somewhere else.This is why CVE identifiers are helpful but insufficient. The identifier gives teams a shared vocabulary; the actual fix validation still has to happen per platform and per build.
- Different vendors may backport different commits.
- Package versions may not map cleanly to upstream release numbers.
- Hardware-specific firmware stacks can change how the bug is reached.
- Automation needs to understand vendor build metadata.
- Security teams should verify the live kernel, not just the advisory.
Industry and ecosystem implications
CVE-2026-23284 also illustrates how Linux vulnerability tracking has become more operationally integrated across the industry. The Linux kernel project maintains that CVEs are tied to already-fixed issues in stable trees, and Microsoft’s Security Update Guide increasingly acts as a distribution point for security intelligence that enterprises consume across multiple platforms (kernel.org). The result is a shared intake flow for what is still, at the end of the day, a Linux driver problem.That matters because a growing number of security operations teams do not separate Windows, Linux, firmware, and cloud host advisories into unrelated processes. They feed into one patch-priority pipeline. A Linux kernel CVE appearing in Microsoft’s ecosystem therefore becomes part of a larger enterprise workflow, especially for organizations with mixed infrastructure.
Why this changes patching behavior
The publication model helps normalize triage, but it also raises expectations. Once a CVE is visible in a mainstream advisory channel, teams expect precision: what’s affected, what’s fixed, and what version should be deployed. If the description is too terse, organizations may delay action while they wait for supplemental vendor guidance. If it is too broad, they may over-prioritize systems that are not actually exposed.That tension is why high-quality upstream metadata matters. The more accurately the fix is described, the easier it is for downstream vendors and operators to make good decisions.
Competitive implications for vendors
There is also a quiet competitive angle here. Vendors that can ingest upstream kernel fixes quickly, classify them correctly, and distribute clean backports will be seen as more trustworthy by enterprise buyers. In a market where patch velocity and patch quality both matter, the ability to ship a small but correct fix is a real differentiator.- Faster ingestion of upstream fixes builds confidence.
- Clean backports reduce support burden.
- Accurate advisories improve customer trust.
- Strong kernel hygiene lowers the risk of regressions.
- Clear lifecycle tracking helps enterprises prove compliance.
Strengths and Opportunities
The strength of this case is that the issue appears to have been found and corrected in a straightforward way, with the fix focused on restoring the original pointer and preserving the proper reference count. That is a sign of mature kernel maintenance, and it gives downstream vendors a clear patch target. It also highlights an opportunity for operators to use the incident as a checklist item for reviewing other driver unwind paths. In a subsystem like networking, small lifecycle fixes often reveal larger coding patterns worth auditing.- The fix is narrow and surgical.
- The bug lives in a well-defined failure path.
- The correction improves state consistency.
- The CVE provides a shared tracking identifier.
- Vendors can backport without redesigning the subsystem.
- Enterprises can fold the patch into normal kernel maintenance.
- The issue reinforces the value of reviewing error unwinding.
Risks and Concerns
The main concern is underestimation. A bug that only appears when mtk_open() fails can be dismissed as edge-case behavior, but edge cases are precisely where kernel state bugs persist longest. There is also the possibility of patch fragmentation across vendor kernels, where the fix exists upstream but not yet in the exact build an organization runs. That creates a false sense of safety if teams rely on the CVE label alone.- Failure-path bugs are often under-tested.
- Driver state mismatches can be hard to reproduce.
- Downstream backports may differ by vendor.
- Administrators may confuse published with deployed.
- The bug could be misclassified as a mere stability issue.
- Patch lag is a real risk in embedded and appliance fleets.
- Hardware-specific exposure complicates automated triage.
Looking Ahead
The immediate thing to watch is whether downstream kernel vendors have already absorbed the fix into their supported branches. Because Linux CVEs are tied to stable-tree fixes, the real-world question is adoption, not publication. Operators should expect the patch to move through vendor advisories and package updates rather than assume the upstream record alone is sufficient (kernel.org).A second thing to watch is whether this prompts a broader look at other XDP and driver setup paths in network subsystems. Once a failure-path bug is identified in one place, maintainers often revisit adjacent code for similar asymmetries. That kind of review can pay dividends, especially in fast-moving areas like eBPF and NIC offload support.
A third thing to watch is how vendors ultimately score the issue. NVD’s enrichment process was still pending at publication time, so severity guidance may evolve. That will matter for prioritization, but it should not be the trigger for action. The trigger is whether the kernel in production includes the corrected rollback logic.
- Track vendor backports and package rebuilds.
- Validate whether your hardware actually uses the affected driver.
- Watch for related cleanup patches in adjacent networking code.
- Reassess XDP deployment on systems with older kernel branches.
- Update vulnerability management records with the fixed build, not just the CVE number.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
Last edited: