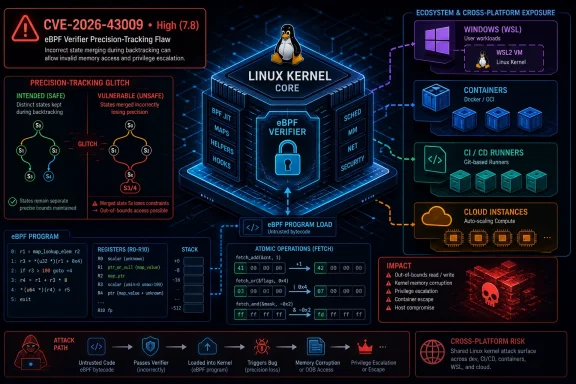
CVE-2026-43009 is a Linux kernel eBPF verifier flaw disclosed by kernel.org on May 1, 2026, affecting versions from 5.12 through before 6.19.12 and scored 7.8 High because a local privileged user could potentially compromise confidentiality, integrity, and availability. The short version is that a verifier optimization got too clever about when two program states were “the same.” The longer version is more interesting: this is another reminder that the safety of modern kernel extension systems rests not only on permission checks, but on the correctness of compiler-like reasoning buried deep inside the kernel.
For WindowsForum readers, the relevance is not theoretical just because the bug lives in Linux. Linux is now routinely present inside Windows estates through WSL, Azure images, developer workstations, appliances, containers, CI runners, and security tooling. A kernel bug in eBPF is therefore not “somebody else’s Unix problem”; it is part of the cross-platform substrate that modern Windows shops increasingly depend on.
The affected code sits in the Linux kernel’s BPF verifier, the subsystem that decides whether an eBPF program is safe enough to run in kernel context. eBPF has become one of Linux’s most important extensibility mechanisms, powering observability, packet filtering, tracing, security policy, and performance tooling. Its bargain is simple but precarious: users can load small programs into the kernel, provided the verifier can prove those programs will not do anything unsafe.
CVE-2026-43009 is a verifier bug, not a classic buffer overflow in a driver or a missing bounds check in a syscall handler. The problem is in precision tracking, the verifier’s internal accounting for values that must remain exact rather than merely approximated. In this case, atomic fetch operations were not being modeled correctly during backtracking.
That sounds dry, but it goes to the heart of why eBPF security is difficult. The verifier is not merely checking syntax. It is simulating possible execution paths, tracking register values, stack slots, pointer provenance, scalar ranges, and whether a value is precise enough to make later decisions safe. When that model is wrong, the kernel may accept a program based on a proof that was never true.
The bug report describes a specific failure mode: when
That mistake allowed the backtracking logic to stop too early. It failed to propagate precision back to the relevant stack location, leaving a stack value unmarked as precise. Later, path pruning could then decide that two states were equivalent even when their stack state differed. In verifier terms, that is a dangerous kind of false sameness.
But the verifier has to reason about programs under enormous constraints. It cannot execute every possible path indefinitely. It must summarize states, merge equivalent branches, prune redundant paths, and track enough information to reject unsafe programs without rejecting too many legitimate ones. That is where bugs like CVE-2026-43009 live: not in the obvious checks, but in the optimizations that make the checks tractable.
Path pruning is especially delicate. If the verifier explores one branch and later sees what it believes is the same state, it may skip rechecking the second path. That is essential for performance and termination. Without pruning, valid programs could become prohibitively expensive to verify.
The catch is that “same” has to mean same in every security-relevant way. If two paths differ in stack contents, pointer relationships, or exact scalar values, treating them as equivalent can erase the very distinction that would have exposed an unsafe operation. CVE-2026-43009 is essentially a bug in that equivalence machinery.
This is why the patch is conceptually narrow but security-significant. It teaches the backtracking logic that atomic fetch operations should be handled like loads for precision purposes. When the destination register of an atomic fetch is being tracked, the verifier must clear that register from the current tracking set and propagate precision back to the stack slot that supplied the old value. For non-stack memory, the precision walk stops at the atomic instruction, mirroring existing load behavior.
The sample trace in the vulnerability description shows exactly that shape. A value is stored on the BPF stack, an atomic fetch operation reads the old value back, and the resulting register is used in arithmetic. Before the fix, the precision walk followed the register only to the atomic instruction and then failed to continue back to the stack slot. After the fix, the verifier correctly sees that the register’s value originated from the stack location and continues tracking back to the earlier store.
That difference is not cosmetic. If the verifier does not know that the stack slot needs precision, later reasoning may allow two states to collapse into one. From the kernel’s point of view, this can mean accepting a program after evaluating a safer-looking path while discarding another path that still matters.
The CVSS vector assigned by kernel.org is local, low attack complexity, low privileges required, no user interaction, unchanged scope, and high impact across confidentiality, integrity, and availability. That rating does not prove there is a public exploit. It does signal that the class of bug is serious enough to justify fast patching wherever untrusted or semi-trusted users can load BPF programs.
The “local privileged” phrase deserves careful reading. On many hardened systems, loading powerful BPF programs is restricted. On developer machines, CI runners, container hosts, and observability-heavy servers, the picture can be messier. Capabilities, namespaces, distribution defaults, sysctls, and security modules all influence who can reach BPF attack surface and under what constraints.
Distribution kernels are not simple mirrors of upstream version numbers. Red Hat, Ubuntu, Debian, SUSE, Amazon Linux, Oracle, and others routinely backport fixes into older kernel branches while keeping the external version string stable. A system reporting an older kernel version may be fixed; a system reporting a newer custom kernel may not be. Administrators should trust vendor advisories and package changelogs over raw version comparisons.
Amazon’s advisory data, for example, marked some Amazon Linux kernel lines as pending fixes while others were not affected. That kind of divergence is normal. It reflects different kernel bases, feature configurations, backport status, and exposure decisions. It also means asset scanners that only match “Linux kernel version less than X” will produce both false comfort and false alarms.
For Windows-adjacent environments, the most likely exposure points are not desktop Windows itself. They are Linux virtual machines on Hyper-V, WSL distributions that ship their own userland against Microsoft’s WSL kernel, Azure Linux images, Kubernetes nodes, network appliances, and third-party security products that embed Linux. The operational question is not whether a machine has a Windows logo on the lid; it is whether a vulnerable Linux kernel is running anywhere in the estate.
This is where CVE triage often goes wrong. Security teams see “Linux kernel” and route the ticket to the Unix group. Developer platform teams assume WSL is managed by desktop engineering. Cloud teams assume marketplace images will be patched by image publishers. Meanwhile, the vulnerable component is quietly present in all three places.
Still, Microsoft’s involvement is a useful signal for Windows administrators. The modern Windows environment is not cleanly separable from Linux. WSL has made Linux a normal part of developer desktops. Azure made Linux a first-class server workload long ago. Defender, Sentinel, GitHub Actions, container registries, and Kubernetes services all blur the old boundary between Windows patching and Linux patching.
That boundary matters because eBPF itself is increasingly central to cloud-native operations. It underpins observability agents, policy engines, packet inspection, and runtime security products. Some of the most capable tools in a mixed Windows and Linux estate now depend on the same kernel machinery that CVE-2026-43009 touches.
The practical lesson is not that Microsoft must patch every Linux kernel everywhere. It is that Windows-centric teams need inventory that sees Linux kernels as first-class assets. If an organization treats Linux as an implementation detail of developer tooling or cloud infrastructure, bugs like this will sit in the gap between teams.
There is also a subtler point for WSL users. WSL’s kernel lifecycle is not the same as a conventional distribution kernel lifecycle. Updating packages inside Ubuntu, Debian, or another WSL distro does not necessarily update the WSL kernel itself. Developers who live inside WSL should understand which kernel they are running and how it is updated in their organization.
That framing should reduce panic, not urgency. Local kernel vulnerabilities are valuable because attackers often arrive with a foothold first and escalate later. A compromised developer account, container escape chain, malicious CI job, or low-privilege shell on a server becomes much more dangerous if a kernel verifier bug can be used to cross into higher privilege.
The eBPF permission model is not uniform across all systems. Some distributions restrict unprivileged BPF by default; others have evolved defaults over time. Container runtimes may expose or block relevant capabilities. Security modules can narrow access. Cloud providers may apply their own kernel hardening and backports.
Administrators should therefore ask two questions in parallel. First, is the kernel fixed? Second, who can load BPF programs on the systems I care about? The first is a patch-management question. The second is an exposure-management question, and it often produces faster risk reduction while waiting for vendor packages or maintenance windows.
There is no need to invent exotic mitigations before checking the basics. If unprivileged BPF is enabled on a system that does not need it, disabling it is usually a sensible hardening move. If containers have unnecessary capabilities, remove them. If developer machines run stale WSL kernels, bring them into the same update discipline as the rest of the endpoint fleet.
But targeted does not mean trivial. Verifier changes are notoriously sensitive because they affect both security and program compatibility. Tighten the verifier too much and legitimate BPF programs may stop loading. Loosen it by accident and unsafe programs may pass. Fixes must preserve the intended semantics while making the proof more accurate.
This is one reason kernel security advisories can look strange to outsiders. The description reads like an internal compiler bug report: registers, stack slots, pruning, atomic fetch variants, and precision walks. Yet the consequence is framed in CIA terms: confidentiality, integrity, availability. That translation from microscopic state modeling to macroscopic security impact is the kernel’s daily reality.
For defenders, the key detail is not the exact instruction encoding. It is the class of failure: verifier state equivalence was too coarse. That is enough to justify patching even if exploit details remain sparse. Attackers with strong eBPF knowledge can turn verifier mistakes into powerful primitives; defenders do not need to wait for a polished proof-of-concept to care.
It is also worth noting that NVD had not assigned its own CVSS score at the time of the provided record, while kernel.org supplied the 7.8 High assessment. That lag is common. NVD enrichment often trails CNA publication, especially when the CNA is upstream and the affected-product mapping is still being refined.
A CPE match can tell you that an upstream version range is affected. It cannot reliably tell you whether your vendor kernel has a backported fix. It also cannot tell you whether the relevant feature is enabled, whether BPF access is restricted, or whether compensating controls make exploitation impractical. The scanner sees a version; the real world sees a kernel build, config, patchset, and policy.
This does not make scanners useless. It means their output has to be interpreted. For CVE-2026-43009, a good triage workflow should combine package metadata, vendor advisories, kernel build information, and runtime exposure. Blindly suppressing the finding because “it needs local access” is as lazy as blindly declaring every flagged host exploitable.
The broad upstream range also means organizations should expect advisories to evolve. Vendors may mark certain kernels unaffected because the vulnerable code path was absent, disabled, or differently backported. Others may ship fixes under older version numbers. Cloud images may be refreshed before on-prem packages land. Livepatch providers may or may not cover this specific fix immediately.
For Windows-heavy shops, the hard part is discovering all the Linux kernels that do not look like servers. Developer laptops running WSL, nested lab VMs, build agents, container hosts, appliance VMs, and security sensors often live outside the normal Linux server inventory. CVE-2026-43009 is a good excuse to close that inventory gap.
Every one of those wins increases the importance of the verifier. If eBPF is a controlled gateway into kernel behavior, the verifier is the lock. CVE-2026-43009 is one more case where the lock’s internals needed correction.
That does not mean eBPF is a mistake. The alternative is often worse: out-of-tree kernel modules, invasive agents, fragile tracing hacks, or blind spots in production. eBPF’s safety model is ambitious precisely because the demand for kernel-level extensibility is real. The right conclusion is not to abandon it, but to treat it like a privileged platform rather than a magical safe sandbox.
Organizations should know which products load BPF programs, which teams are allowed to deploy them, and which hosts permit unprivileged BPF activity. They should also test important BPF-dependent tooling after kernel updates. Verifier fixes can change whether marginal programs are accepted, and production observability should not be the first place anyone discovers that an agent’s BPF program no longer loads.
There is a governance angle here that Windows administrators will recognize from PowerShell, macros, drivers, and endpoint agents. A powerful administrative technology starts as a specialist tool, spreads because it solves real problems, and eventually becomes common enough that attackers study it seriously. eBPF is already at that stage.
For WSL, the answer depends on how the environment is managed. Individual users may receive kernel updates through Microsoft’s delivery mechanisms, while enterprises may control Store updates, inbox WSL behavior, or custom WSL kernels. A developer updating packages inside the distro is not the same as updating the kernel. That distinction should be documented in internal guidance, because it is a common source of false confidence.
For Azure and other cloud Linux workloads, images and instances need separate attention. A marketplace image may be refreshed, but running virtual machines generally do not become patched simply because the image changed. Scale sets, Kubernetes node pools, golden images, and long-lived pets all need their own update paths.
For containers, the vulnerable kernel is the host kernel, not the container image’s userland. Rebuilding a container image may be necessary for other CVEs, but it will not fix a host kernel verifier bug. This is a perennial source of confusion in vulnerability dashboards, especially when container teams and infrastructure teams own different parts of the stack.
For appliances and embedded products, administrators are dependent on vendor firmware or OS updates. Those systems are easy to forget until a scanner flags them, and harder to patch once identified. If the appliance exposes local shell access only to administrators, the risk profile may differ, but the patch obligation does not vanish.
The most useful response is disciplined rather than dramatic:
CVE-2026-43009 will probably not be remembered as the loudest Linux vulnerability of 2026, but it is exactly the kind of flaw that separates mature security programs from checkbox patching. The bug lives in a narrow corner of eBPF precision tracking, yet the lesson is broad: when operating systems become platforms for programmable policy, tracing, and networking, the correctness of their internal reasoning becomes part of the security boundary. The next verifier fix will look just as esoteric, and the organizations best prepared for it will be the ones that stopped treating Linux kernels in Windows-era infrastructure as invisible plumbing.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
For WindowsForum readers, the relevance is not theoretical just because the bug lives in Linux. Linux is now routinely present inside Windows estates through WSL, Azure images, developer workstations, appliances, containers, CI runners, and security tooling. A kernel bug in eBPF is therefore not “somebody else’s Unix problem”; it is part of the cross-platform substrate that modern Windows shops increasingly depend on.
 The Vulnerability Is Small, but the Trust Boundary Is Not
The Vulnerability Is Small, but the Trust Boundary Is Not
The affected code sits in the Linux kernel’s BPF verifier, the subsystem that decides whether an eBPF program is safe enough to run in kernel context. eBPF has become one of Linux’s most important extensibility mechanisms, powering observability, packet filtering, tracing, security policy, and performance tooling. Its bargain is simple but precarious: users can load small programs into the kernel, provided the verifier can prove those programs will not do anything unsafe.CVE-2026-43009 is a verifier bug, not a classic buffer overflow in a driver or a missing bounds check in a syscall handler. The problem is in precision tracking, the verifier’s internal accounting for values that must remain exact rather than merely approximated. In this case, atomic fetch operations were not being modeled correctly during backtracking.
That sounds dry, but it goes to the heart of why eBPF security is difficult. The verifier is not merely checking syntax. It is simulating possible execution paths, tracking register values, stack slots, pointer provenance, scalar ranges, and whether a value is precise enough to make later decisions safe. When that model is wrong, the kernel may accept a program based on a proof that was never true.
The bug report describes a specific failure mode: when
backtrack_insn encountered a BPF_STX instruction with BPF_ATOMIC and BPF_FETCH, it treated the source register as if it were only an input. But atomic fetch operations also return the old memory value into a register. In other words, the register is both participant and recipient. The verifier’s bookkeeping missed that dual role.That mistake allowed the backtracking logic to stop too early. It failed to propagate precision back to the relevant stack location, leaving a stack value unmarked as precise. Later, path pruning could then decide that two states were equivalent even when their stack state differed. In verifier terms, that is a dangerous kind of false sameness.
eBPF’s Safety Story Depends on Boring Accounting
The eBPF verifier exists because running arbitrary code in the kernel would otherwise be an invitation to disaster. It is the gatekeeper that makes eBPF palatable in production systems. Developers get near-kernel speed and visibility; administrators get tooling that can observe or influence live systems without rebooting; the kernel gets a formal-ish approval process before anything runs.But the verifier has to reason about programs under enormous constraints. It cannot execute every possible path indefinitely. It must summarize states, merge equivalent branches, prune redundant paths, and track enough information to reject unsafe programs without rejecting too many legitimate ones. That is where bugs like CVE-2026-43009 live: not in the obvious checks, but in the optimizations that make the checks tractable.
Path pruning is especially delicate. If the verifier explores one branch and later sees what it believes is the same state, it may skip rechecking the second path. That is essential for performance and termination. Without pruning, valid programs could become prohibitively expensive to verify.
The catch is that “same” has to mean same in every security-relevant way. If two paths differ in stack contents, pointer relationships, or exact scalar values, treating them as equivalent can erase the very distinction that would have exposed an unsafe operation. CVE-2026-43009 is essentially a bug in that equivalence machinery.
This is why the patch is conceptually narrow but security-significant. It teaches the backtracking logic that atomic fetch operations should be handled like loads for precision purposes. When the destination register of an atomic fetch is being tracked, the verifier must clear that register from the current tracking set and propagate precision back to the stack slot that supplied the old value. For non-stack memory, the precision walk stops at the atomic instruction, mirroring existing load behavior.
Atomic Fetch Was the Footnote That Changed the Proof
The vulnerable behavior turns on a subtle property of atomic operations. A normal store writes a value to memory, and the source register remains only a source. An atomic fetch-and-add, by contrast, updates memory and returns the old memory value to a register. That old value may then influence address arithmetic or control flow.The sample trace in the vulnerability description shows exactly that shape. A value is stored on the BPF stack, an atomic fetch operation reads the old value back, and the resulting register is used in arithmetic. Before the fix, the precision walk followed the register only to the atomic instruction and then failed to continue back to the stack slot. After the fix, the verifier correctly sees that the register’s value originated from the stack location and continues tracking back to the earlier store.
That difference is not cosmetic. If the verifier does not know that the stack slot needs precision, later reasoning may allow two states to collapse into one. From the kernel’s point of view, this can mean accepting a program after evaluating a safer-looking path while discarding another path that still matters.
The CVSS vector assigned by kernel.org is local, low attack complexity, low privileges required, no user interaction, unchanged scope, and high impact across confidentiality, integrity, and availability. That rating does not prove there is a public exploit. It does signal that the class of bug is serious enough to justify fast patching wherever untrusted or semi-trusted users can load BPF programs.
The “local privileged” phrase deserves careful reading. On many hardened systems, loading powerful BPF programs is restricted. On developer machines, CI runners, container hosts, and observability-heavy servers, the picture can be messier. Capabilities, namespaces, distribution defaults, sysctls, and security modules all influence who can reach BPF attack surface and under what constraints.
The Version Range Is Broad Enough to Matter
NVD’s initial analysis lists affected Linux kernel versions from 5.12 up to, but excluding, 6.19.12, along with 7.0 release candidates rc1 through rc6. That is a wide span of kernel history, covering many enterprise, cloud, appliance, and enthusiast environments depending on vendor backports. As usual with kernel CVEs, the mainline version range is only the start of the operational story.Distribution kernels are not simple mirrors of upstream version numbers. Red Hat, Ubuntu, Debian, SUSE, Amazon Linux, Oracle, and others routinely backport fixes into older kernel branches while keeping the external version string stable. A system reporting an older kernel version may be fixed; a system reporting a newer custom kernel may not be. Administrators should trust vendor advisories and package changelogs over raw version comparisons.
Amazon’s advisory data, for example, marked some Amazon Linux kernel lines as pending fixes while others were not affected. That kind of divergence is normal. It reflects different kernel bases, feature configurations, backport status, and exposure decisions. It also means asset scanners that only match “Linux kernel version less than X” will produce both false comfort and false alarms.
For Windows-adjacent environments, the most likely exposure points are not desktop Windows itself. They are Linux virtual machines on Hyper-V, WSL distributions that ship their own userland against Microsoft’s WSL kernel, Azure Linux images, Kubernetes nodes, network appliances, and third-party security products that embed Linux. The operational question is not whether a machine has a Windows logo on the lid; it is whether a vulnerable Linux kernel is running anywhere in the estate.
This is where CVE triage often goes wrong. Security teams see “Linux kernel” and route the ticket to the Unix group. Developer platform teams assume WSL is managed by desktop engineering. Cloud teams assume marketplace images will be patched by image publishers. Meanwhile, the vulnerable component is quietly present in all three places.
Microsoft’s Appearance in the Story Is About Ecosystem Gravity
The user-provided source points to Microsoft’s Security Update Guide, but the CVE itself is sourced to kernel.org. That distinction matters. Microsoft tracks many non-Windows CVEs because its platforms, cloud services, developer tools, container offerings, and Linux distributions intersect with upstream open source projects. A CVE appearing in Microsoft’s orbit does not automatically mean “Windows is vulnerable” in the traditional Patch Tuesday sense.Still, Microsoft’s involvement is a useful signal for Windows administrators. The modern Windows environment is not cleanly separable from Linux. WSL has made Linux a normal part of developer desktops. Azure made Linux a first-class server workload long ago. Defender, Sentinel, GitHub Actions, container registries, and Kubernetes services all blur the old boundary between Windows patching and Linux patching.
That boundary matters because eBPF itself is increasingly central to cloud-native operations. It underpins observability agents, policy engines, packet inspection, and runtime security products. Some of the most capable tools in a mixed Windows and Linux estate now depend on the same kernel machinery that CVE-2026-43009 touches.
The practical lesson is not that Microsoft must patch every Linux kernel everywhere. It is that Windows-centric teams need inventory that sees Linux kernels as first-class assets. If an organization treats Linux as an implementation detail of developer tooling or cloud infrastructure, bugs like this will sit in the gap between teams.
There is also a subtler point for WSL users. WSL’s kernel lifecycle is not the same as a conventional distribution kernel lifecycle. Updating packages inside Ubuntu, Debian, or another WSL distro does not necessarily update the WSL kernel itself. Developers who live inside WSL should understand which kernel they are running and how it is updated in their organization.
High Severity Does Not Mean Internet Worm
A 7.8 High score will get attention, and rightly so. But the score should not be read as “remote unauthenticated compromise.” The vector is local. An attacker generally needs some level of local privilege and a path to load or influence BPF programs. That makes the bug more relevant to shared systems, multi-tenant hosts, developer platforms, and post-compromise privilege escalation than to a random laptop sitting behind a firewall.That framing should reduce panic, not urgency. Local kernel vulnerabilities are valuable because attackers often arrive with a foothold first and escalate later. A compromised developer account, container escape chain, malicious CI job, or low-privilege shell on a server becomes much more dangerous if a kernel verifier bug can be used to cross into higher privilege.
The eBPF permission model is not uniform across all systems. Some distributions restrict unprivileged BPF by default; others have evolved defaults over time. Container runtimes may expose or block relevant capabilities. Security modules can narrow access. Cloud providers may apply their own kernel hardening and backports.
Administrators should therefore ask two questions in parallel. First, is the kernel fixed? Second, who can load BPF programs on the systems I care about? The first is a patch-management question. The second is an exposure-management question, and it often produces faster risk reduction while waiting for vendor packages or maintenance windows.
There is no need to invent exotic mitigations before checking the basics. If unprivileged BPF is enabled on a system that does not need it, disabling it is usually a sensible hardening move. If containers have unnecessary capabilities, remove them. If developer machines run stale WSL kernels, bring them into the same update discipline as the rest of the endpoint fleet.
The Patch Shows How Narrow Fixes Can Carry Broad Consequences
The upstream fix is not a wholesale redesign of the verifier. It adds recognition for atomic fetch instructions during precision backtracking through anis_atomic_fetch_insn() helper and adjusts the tracking logic so the relevant stack slot becomes precise. In code-review terms, that is a targeted repair.But targeted does not mean trivial. Verifier changes are notoriously sensitive because they affect both security and program compatibility. Tighten the verifier too much and legitimate BPF programs may stop loading. Loosen it by accident and unsafe programs may pass. Fixes must preserve the intended semantics while making the proof more accurate.
This is one reason kernel security advisories can look strange to outsiders. The description reads like an internal compiler bug report: registers, stack slots, pruning, atomic fetch variants, and precision walks. Yet the consequence is framed in CIA terms: confidentiality, integrity, availability. That translation from microscopic state modeling to macroscopic security impact is the kernel’s daily reality.
For defenders, the key detail is not the exact instruction encoding. It is the class of failure: verifier state equivalence was too coarse. That is enough to justify patching even if exploit details remain sparse. Attackers with strong eBPF knowledge can turn verifier mistakes into powerful primitives; defenders do not need to wait for a polished proof-of-concept to care.
It is also worth noting that NVD had not assigned its own CVSS score at the time of the provided record, while kernel.org supplied the 7.8 High assessment. That lag is common. NVD enrichment often trails CNA publication, especially when the CNA is upstream and the affected-product mapping is still being refined.
Asset Scanners Will Be Messy Here
The CPE list in the NVD record includes upstream kernel versions and release candidates, but the page itself effectively invites corrections with the familiar “missing a CPE” prompt. That is not surprising. Linux kernel vulnerability mapping is one of the more difficult corners of automated vulnerability management.A CPE match can tell you that an upstream version range is affected. It cannot reliably tell you whether your vendor kernel has a backported fix. It also cannot tell you whether the relevant feature is enabled, whether BPF access is restricted, or whether compensating controls make exploitation impractical. The scanner sees a version; the real world sees a kernel build, config, patchset, and policy.
This does not make scanners useless. It means their output has to be interpreted. For CVE-2026-43009, a good triage workflow should combine package metadata, vendor advisories, kernel build information, and runtime exposure. Blindly suppressing the finding because “it needs local access” is as lazy as blindly declaring every flagged host exploitable.
The broad upstream range also means organizations should expect advisories to evolve. Vendors may mark certain kernels unaffected because the vulnerable code path was absent, disabled, or differently backported. Others may ship fixes under older version numbers. Cloud images may be refreshed before on-prem packages land. Livepatch providers may or may not cover this specific fix immediately.
For Windows-heavy shops, the hard part is discovering all the Linux kernels that do not look like servers. Developer laptops running WSL, nested lab VMs, build agents, container hosts, appliance VMs, and security sensors often live outside the normal Linux server inventory. CVE-2026-43009 is a good excuse to close that inventory gap.
eBPF Keeps Becoming More Useful and More Dangerous
The uncomfortable truth about eBPF is that its usefulness keeps expanding faster than many organizations’ governance around it. Observability vendors love it because it can see what user-space agents miss. Security vendors love it because it can enforce policy close to the kernel. Network teams love it because it can move packet decisions into fast paths. Developers love it when it makes production systems visible without invasive code changes.Every one of those wins increases the importance of the verifier. If eBPF is a controlled gateway into kernel behavior, the verifier is the lock. CVE-2026-43009 is one more case where the lock’s internals needed correction.
That does not mean eBPF is a mistake. The alternative is often worse: out-of-tree kernel modules, invasive agents, fragile tracing hacks, or blind spots in production. eBPF’s safety model is ambitious precisely because the demand for kernel-level extensibility is real. The right conclusion is not to abandon it, but to treat it like a privileged platform rather than a magical safe sandbox.
Organizations should know which products load BPF programs, which teams are allowed to deploy them, and which hosts permit unprivileged BPF activity. They should also test important BPF-dependent tooling after kernel updates. Verifier fixes can change whether marginal programs are accepted, and production observability should not be the first place anyone discovers that an agent’s BPF program no longer loads.
There is a governance angle here that Windows administrators will recognize from PowerShell, macros, drivers, and endpoint agents. A powerful administrative technology starts as a specialist tool, spreads because it solves real problems, and eventually becomes common enough that attackers study it seriously. eBPF is already at that stage.
The Kernel Version Is Only Half the Patch Story
For conventional Linux servers, the immediate answer is straightforward: follow the distribution’s kernel advisory and reboot or livepatch as appropriate. Kernel updates still frequently require reboots, and postponing them because a bug is “only local” has become a risky habit. Attack chains are built from exactly these kinds of local steps.For WSL, the answer depends on how the environment is managed. Individual users may receive kernel updates through Microsoft’s delivery mechanisms, while enterprises may control Store updates, inbox WSL behavior, or custom WSL kernels. A developer updating packages inside the distro is not the same as updating the kernel. That distinction should be documented in internal guidance, because it is a common source of false confidence.
For Azure and other cloud Linux workloads, images and instances need separate attention. A marketplace image may be refreshed, but running virtual machines generally do not become patched simply because the image changed. Scale sets, Kubernetes node pools, golden images, and long-lived pets all need their own update paths.
For containers, the vulnerable kernel is the host kernel, not the container image’s userland. Rebuilding a container image may be necessary for other CVEs, but it will not fix a host kernel verifier bug. This is a perennial source of confusion in vulnerability dashboards, especially when container teams and infrastructure teams own different parts of the stack.
For appliances and embedded products, administrators are dependent on vendor firmware or OS updates. Those systems are easy to forget until a scanner flags them, and harder to patch once identified. If the appliance exposes local shell access only to administrators, the risk profile may differ, but the patch obligation does not vanish.
The Practical Signal Buried in the Verifier Noise
CVE-2026-43009 is a reminder that kernel vulnerability management is no longer just about the kernel teams. It intersects with endpoint management, developer experience, cloud operations, container platforms, and security engineering. That is particularly true in Windows-centric organizations that adopted Linux incrementally and now discover it everywhere.The most useful response is disciplined rather than dramatic:
- Inventory Linux kernels across WSL, virtual machines, container hosts, cloud images, appliances, and CI runners, not just traditional Linux servers.
- Treat vendor kernel advisories and package changelogs as authoritative, because upstream version numbers alone can misrepresent backported fixes.
- Restrict unprivileged or unnecessary BPF access wherever workloads do not require it, especially on shared hosts and developer platforms.
- Patch or livepatch affected kernels when vendor updates become available, and plan reboots instead of letting “local only” become a permanent exception.
- Validate BPF-dependent observability and security agents after kernel updates, because verifier changes can affect whether their programs load cleanly.
- Make WSL kernel servicing explicit in Windows endpoint guidance, since updating Linux packages inside a distro is not the same as updating the kernel underneath it.
CVE-2026-43009 will probably not be remembered as the loudest Linux vulnerability of 2026, but it is exactly the kind of flaw that separates mature security programs from checkbox patching. The bug lives in a narrow corner of eBPF precision tracking, yet the lesson is broad: when operating systems become platforms for programmable policy, tracing, and networking, the correctness of their internal reasoning becomes part of the security boundary. The next verifier fix will look just as esoteric, and the organizations best prepared for it will be the ones that stopped treating Linux kernels in Windows-era infrastructure as invisible plumbing.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center