CVE-2026-31729 is a high-severity Linux kernel flaw published on May 1, 2026, in the USB Type-C UCSI driver, where a bogus connector number from hardware can trigger an out-of-bounds array access before fixed kernel builds reject it. For WindowsForum readers, the point is not that Windows suddenly has a new USB-C bug. The point is that modern Windows environments increasingly contain Linux kernels — in WSL, appliances, developer laptops, containers, and edge systems — and kernel CVEs now travel across platform boundaries faster than many patch processes do.
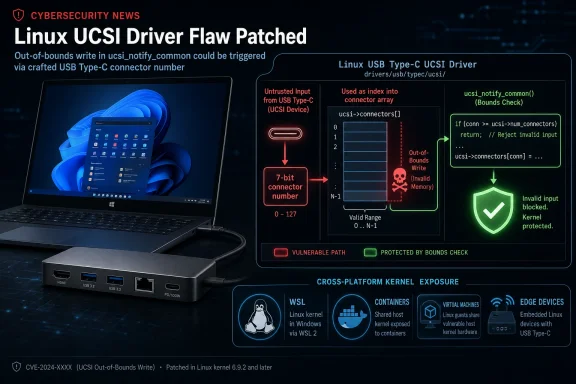
On paper, CVE-2026-31729 is almost boring: a missing bounds check in a kernel driver path. The UCSI code receives a connector number from a command completion indicator, extracts a 7-bit value, and uses that value to identify which USB-C connector changed state. The catch is that the field can represent numbers from 0 to 127, while a real device usually reports only a handful of connectors.
That is the sort of mismatch C programmers have been paying for since the beginning of systems software. A value is technically valid according to one representation, but invalid according to the structure it is about to index. If the driver trusts the larger range and the array was allocated for the smaller one, the result is exactly what NVD classified here: CWE-129, improper validation of an array index.
The practical risk is narrower than the CVSS headline might suggest, but not trivial. NVD assigned CVSS 3.1 score 7.8, with local attack vector, low complexity, low privileges required, no user interaction, and high impact across confidentiality, integrity, and availability. In ordinary English, that means the issue is not a remote drive-by Internet bug, but a local kernel memory safety problem with serious possible consequences if an attacker can reach the relevant path.
This is where the vulnerability becomes more interesting than its small patch implies. USB-C is not a luxury interface anymore; it is the universal physical layer for charging, display, storage, docking, network adapters, phone tethering, and development boards. A bug in the code that listens to connector-state changes is a reminder that “local” now includes the messy world of peripherals, docks, firmware, and machines that constantly cross trust boundaries.
The CVE description says the connector number is extracted through
The bug is not that USB-C has 128 ports hiding in your laptop. It is that one layer of the driver treated the connector identifier as a plausible input before proving it belonged to the actual connector set. A malicious or malfunctioning device could report an out-of-range connector number, and the subsequent path,
The fix is correspondingly direct: add validation in
That is the kind of small defensive change security engineers like because it turns a class of downstream confusion into a single choke point. It is also the kind of change that looks obvious after the fact. Most good kernel bug fixes do.
CVE-2026-31729 requires local access in the CVSS model. The description points to a malicious or malfunctioning device as the trigger source. That shifts the threat model away from a remote attacker spraying packets and toward someone or something able to influence a USB-C/UCSI event path.
That may sound exotic until you look at what modern endpoints actually do. Developers plug in debug boards, sysadmins test docks, conference rooms rotate adapters, and employees attach phones, storage, displays, and chargers from everywhere. USB-C collapsed several formerly separate categories of hardware into one small reversible connector, and the operating system has to believe enough of the surrounding firmware story to make the port useful.
For a Windows-centric shop, the temptation is to wave this away as “a Linux thing.” That would be a mistake. The vulnerability itself is in the Linux kernel, but Linux kernels increasingly exist inside Windows estates, alongside Windows estates, and underneath services Windows users depend on. The operational question is not whether your desktop OS is Windows. It is where Linux kernels are running in your environment and whether anyone owns their patch cadence.
An MSRC page for a Linux kernel CVE does not automatically mean Windows itself is vulnerable. It means Microsoft has enough product or service exposure to track the vulnerability in its update guide ecosystem. In 2026, that is normal. The Windows administrator who ignores Linux CVEs because “we do Windows” is often ignoring the Linux kernel in WSL, the Linux image in a build agent, the Linux node pool in a Kubernetes cluster, or the Linux-based appliance sitting in the same rack.
This is the quiet cultural change behind CVE-2026-31729. The most important security boundary in many organizations is no longer Windows versus Linux. It is managed versus unmanaged. A fully inventoried Ubuntu server may be less risky than a forgotten developer workstation running WSL images, old containers, and vendor tools no one has updated since the last project shipped.
MSRC’s presence should therefore be read less as a Windows panic flag and more as a nudge toward hybrid inventory discipline. If Microsoft is tracking a Linux kernel UCSI flaw, enterprise IT should assume the vendor ecosystem is more cross-platform than its ticket queues suggest.
Those ranges are useful because they make clear this was not a one-off mistake in a single experimental snapshot. The vulnerable code spans multiple maintained and development branches. Stable fixes landed in several kernel lines, which is why administrators should think in terms of distribution-provided kernel updates rather than cherry-picking one commit from kernel.org.
There is also a versioning trap here. Raw upstream kernel numbers rarely map neatly to what enterprises actually run. Ubuntu, Debian, Red Hat-family distributions, SUSE, Android-derived systems, appliance vendors, hypervisor hosts, and embedded platforms all backport fixes differently. A system may report a kernel version that appears older than the fixed upstream version while still containing the backported patch.
That means the right question is not simply “is my kernel lower than 6.12.81?” The right question is whether the distribution or vendor has marked the CVE fixed for the specific package stream you run. Kernel security management is a package provenance exercise, not a numerology contest.
For WindowsForum readers, that distinction should sound familiar. Windows build numbers, cumulative updates, and servicing baselines have trained administrators not to judge security state by marketing version alone. Linux kernel security needs the same habit: identify the vendor kernel package, check the advisory state, apply the update, and reboot into the fixed kernel.
Operating systems have always had to trust hardware at some level. Without trust, there is no boot, no storage, no network, no display, and no power management. But modern kernel design increasingly tries to treat device-provided data as hostile until validated, especially when the device is removable, externally supplied, or mediated through firmware that may vary wildly by vendor.
USB-C multiplies that pressure. It is not merely a port for serial data. It negotiates power delivery, alternate modes, roles, orientation, and device identity across a chain of controllers, firmware, cables, docks, and operating-system drivers. Every place where that chain converts a hardware field into a software index is a potential fault line.
In CVE-2026-31729, the fault line was narrow: a connector value could exceed the array sized for actual connectors. The fixed design places the check in
The broader industry has spent years learning this lesson in network stacks, file parsers, browser engines, and media codecs. Kernel hardware paths deserve the same skepticism. A peripheral is not automatically benign because it is physically close to the machine.
NVD had not provided a CVSS 4.0 assessment at the time of its listed analysis, and the vulnerability’s public description is focused on the memory-safety condition rather than a weaponized exploit chain. That matters. Many kernel memory bugs sit somewhere between “crashable under controlled conditions” and “turnkey privilege escalation,” and public advisories often do not settle the point.
The safer editorial line is to avoid both extremes. It is not responsible to dismiss a high-scoring kernel out-of-bounds access in a hardware-facing subsystem. It is also not responsible to imply that every Linux laptop with USB-C is one malicious dongle away from instant compromise unless evidence supports that.
For administrators, that nuance does not change the action. Kernel updates that fix high-severity memory safety bugs should move through normal expedited patch lanes. The nuance changes the messaging: this is a patch-and-reboot issue, not a reason to rip out every dock in the building tomorrow morning.
WSL is not automatically implicated by every Linux kernel CVE in the same way a native Linux install is; its kernel is delivered through Microsoft’s servicing path rather than a distribution’s normal kernel package. But WSL has made Linux kernel presence on Windows endpoints ordinary. That changes the inventory conversation, even when a particular vulnerability’s hardware path may not map cleanly to every WSL scenario.
The broader developer stack is even messier. A Windows laptop may host WSL distributions, Docker Desktop, virtual machines, USB-attached test hardware, Android tools, embedded boards, serial adapters, and local Kubernetes clusters. Some of those components rely on Microsoft-maintained layers, some on vendor images, and some on distributions the user installed once and never touched again.
CVE-2026-31729 is a useful excuse to audit that sprawl. Which machines run Linux kernels? Which of those kernels can see physical USB-C hardware directly? Which are updated by Windows Update, which by a Linux package manager, and which by a vendor appliance firmware process? If the answer is “we do not know,” the real vulnerability is not just the missing bounds check.
Developer endpoints are also culturally prone to exception. They are where policy bends because work must continue, debugging requires privileges, and hardware experiments are part of the job. That makes local kernel bugs more interesting than they would be on a locked-down kiosk.
USB-C docking stations have become little ecosystems. They may contain firmware, multiple controllers, network chips, audio devices, display paths, storage interfaces, and power negotiation logic. Enterprise fleets often standardize on a dock model, but users still bring in personal adapters, travel hubs, monitors with built-in docks, and chargers of unknown provenance.
This does not mean every adapter is suspicious. It means the OS-facing driver stack must assume the adapter can be wrong. In this case, the Linux UCSI code now performs the check it should perform: if the connector number exceeds the number of known connectors, reject the event before it can index outside the array.
There is a subtle availability angle too. Even if exploitation never progresses beyond a crash, kernel panics on machines attached to common docks are still operationally painful. A bug that can be triggered by malformed hardware state can become a support nightmare in offices where every laptop is tethered to the same class of docking station.
That is why administrators should resist treating USB and Type-C bugs as consumer-edge curiosities. The modern office desk is a peripheral bus with a monitor attached.
The reason is backporting. Enterprise and LTS distributions often take a fix from a newer upstream kernel and apply it to an older supported package. The package version may not resemble the upstream fixed version, yet the vulnerability may be remediated. Conversely, a kernel that looks numerically close to safety may still be vulnerable if it is a custom build without the relevant patch.
This is also where container thinking can mislead people. Containers share the host kernel. Updating a container image does not patch a host kernel vulnerability unless the host itself is updated. If CVE-2026-31729 is relevant to a container host’s kernel and hardware exposure, the remediation lives on the host, not inside the application image.
Cloud systems complicate the picture in the opposite direction. Some managed services abstract kernel patching away from the customer, while infrastructure-as-a-service instances leave the guest OS kernel squarely in the customer’s lap. The same CVE can be vendor-managed in one environment and customer-managed in another.
The operational rule is simple even if the estate is not: follow the advisory for the platform that supplied the kernel you are actually booting. Upstream commit IDs are evidence. Vendor packages are the remediation vehicle.
Start with the obvious: Linux servers, hypervisor hosts, appliances, NAS devices, security sensors, and cloud instances. Then move to the less obvious: WSL deployments, developer VMs, container hosts, lab machines, build runners, kiosks, and embedded systems connected to Windows-managed networks. Finally, ask which of those systems have direct or indirect exposure to USB-C hardware.
The last question matters because CVE-2026-31729 sits in a hardware notification path. A headless cloud VM with no relevant hardware path may carry a vulnerable source lineage but have very different practical exposure from a Linux laptop used with random docks. Risk is not just version number; it is version number plus reachable code path plus threat model.
Still, patching should not become paralyzed by perfect exploitability analysis. If a supported distribution ships a kernel update for this CVE, install it through normal security maintenance. If a vendor appliance is affected, track the firmware or OS update. If a system is unsupported, this is one more data point in the argument to replace or isolate it.
A mature Windows shop already understands monthly cumulative updates, driver servicing, firmware updates, and reboot coordination. Linux kernel patching requires the same muscles, just with different tooling and sometimes less centralized governance.
For CVE-2026-31729, NVD’s listed CPE configurations are useful because they identify upstream kernel ranges and release candidates. But they are not the whole map. They do not automatically tell you which exact distribution kernels, cloud images, vendor appliances, or custom builds in your environment are exposed.
This is why scanners sometimes produce both false comfort and false panic. A scanner that keys too aggressively on upstream version numbers may flag backported kernels as vulnerable. A scanner that lacks product coverage may miss vendor-maintained kernels entirely. Both errors are common enough that administrators should treat vulnerability metadata as input to judgment, not a substitute for it.
The best remediation records tie together several things: CVE ID, vendor advisory, installed package, fixed package version, reboot state, and asset role. Without reboot state, kernel patch reporting is especially treacherous. A package can be updated while the machine is still running the old kernel.
That last detail is where Windows and Linux administrators can find common ground. Patch installed is not the same as patch active. On kernel bugs, the reboot is part of the fix.
What makes the bug contemporary is the path it took. It came through a USB-C subsystem designed to mediate complex hardware and firmware behavior. It was assigned a public CVE by the kernel ecosystem, enriched by NVD, surfaced by MSRC, tracked by distributions, and absorbed into the patch calendars of organizations that may not think of themselves as Linux shops.
That is the security world WindowsForum readers now inhabit. The Windows endpoint is still important, but it sits in a mesh of kernels, hypervisors, firmware, controllers, and developer runtimes. A single laptop may be a Windows client, a Linux development host, a container platform, a USB hardware lab, and a cloud admin console before lunch.
The old platform silos made vulnerability management look cleaner than it was. The new reality makes the mess visible. CVE-2026-31729 is not the largest kernel bug of the year, but it is a neat specimen of how small driver assumptions propagate into enterprise risk conversations.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A USB-C Bug Becomes a Fleet-Management Problem
A USB-C Bug Becomes a Fleet-Management Problem
On paper, CVE-2026-31729 is almost boring: a missing bounds check in a kernel driver path. The UCSI code receives a connector number from a command completion indicator, extracts a 7-bit value, and uses that value to identify which USB-C connector changed state. The catch is that the field can represent numbers from 0 to 127, while a real device usually reports only a handful of connectors.That is the sort of mismatch C programmers have been paying for since the beginning of systems software. A value is technically valid according to one representation, but invalid according to the structure it is about to index. If the driver trusts the larger range and the array was allocated for the smaller one, the result is exactly what NVD classified here: CWE-129, improper validation of an array index.
The practical risk is narrower than the CVSS headline might suggest, but not trivial. NVD assigned CVSS 3.1 score 7.8, with local attack vector, low complexity, low privileges required, no user interaction, and high impact across confidentiality, integrity, and availability. In ordinary English, that means the issue is not a remote drive-by Internet bug, but a local kernel memory safety problem with serious possible consequences if an attacker can reach the relevant path.
This is where the vulnerability becomes more interesting than its small patch implies. USB-C is not a luxury interface anymore; it is the universal physical layer for charging, display, storage, docking, network adapters, phone tethering, and development boards. A bug in the code that listens to connector-state changes is a reminder that “local” now includes the messy world of peripherals, docks, firmware, and machines that constantly cross trust boundaries.
The Vulnerability Lives in the Gap Between a Field and an Array
The vulnerable logic sits in the Linux kernel’s USB Type-C UCSI subsystem. UCSI, the USB Type-C Connector System Software Interface, is the mechanism by which operating systems talk to platform firmware or embedded controllers about Type-C connector events. It is supposed to abstract messy hardware details so the OS can respond when a cable is inserted, a power role changes, or an alternate mode comes into play.The CVE description says the connector number is extracted through
UCSI_CCI_CONNECTOR() from the CCI, a value coming from hardware. That connector number is a 7-bit field, which means it can describe 128 possible values. But the actual connector array is sized according to how many connectors the device says it has, typically two to four.The bug is not that USB-C has 128 ports hiding in your laptop. It is that one layer of the driver treated the connector identifier as a plausible input before proving it belonged to the actual connector set. A malicious or malfunctioning device could report an out-of-range connector number, and the subsequent path,
ucsi_connector_change(), could use that number outside the allocated array.The fix is correspondingly direct: add validation in
ucsi_notify_common(), the central place where CCI data is parsed after arriving from hardware. That placement matters. Rather than relying on every downstream caller to remember that connector numbers are untrusted, the patch rejects bogus values at the point where hardware-originated data enters the software path.That is the kind of small defensive change security engineers like because it turns a class of downstream confusion into a single choke point. It is also the kind of change that looks obvious after the fact. Most good kernel bug fixes do.
“Local” Does Not Mean “Irrelevant”
The word local has a way of deflating security conversations, especially among administrators trained to prioritize remotely exploitable bugs. A local kernel vulnerability rarely deserves the same emergency posture as an unauthenticated network RCE. But local kernel bugs remain valuable because they sit exactly where isolation, privilege boundaries, and device trust are supposed to become real.CVE-2026-31729 requires local access in the CVSS model. The description points to a malicious or malfunctioning device as the trigger source. That shifts the threat model away from a remote attacker spraying packets and toward someone or something able to influence a USB-C/UCSI event path.
That may sound exotic until you look at what modern endpoints actually do. Developers plug in debug boards, sysadmins test docks, conference rooms rotate adapters, and employees attach phones, storage, displays, and chargers from everywhere. USB-C collapsed several formerly separate categories of hardware into one small reversible connector, and the operating system has to believe enough of the surrounding firmware story to make the port useful.
For a Windows-centric shop, the temptation is to wave this away as “a Linux thing.” That would be a mistake. The vulnerability itself is in the Linux kernel, but Linux kernels increasingly exist inside Windows estates, alongside Windows estates, and underneath services Windows users depend on. The operational question is not whether your desktop OS is Windows. It is where Linux kernels are running in your environment and whether anyone owns their patch cadence.
Microsoft’s Presence in the Advisory Is the Signal, Not the Surprise
The user-facing wrinkle here is that the submitted source is Microsoft’s Security Response Center entry for a Linux kernel CVE. That will look odd only to people still thinking of Microsoft and Linux as separate planets. Microsoft ships, supports, documents, and secures Linux-adjacent infrastructure across Azure, WSL, container workflows, developer tooling, and cloud-hosted images.An MSRC page for a Linux kernel CVE does not automatically mean Windows itself is vulnerable. It means Microsoft has enough product or service exposure to track the vulnerability in its update guide ecosystem. In 2026, that is normal. The Windows administrator who ignores Linux CVEs because “we do Windows” is often ignoring the Linux kernel in WSL, the Linux image in a build agent, the Linux node pool in a Kubernetes cluster, or the Linux-based appliance sitting in the same rack.
This is the quiet cultural change behind CVE-2026-31729. The most important security boundary in many organizations is no longer Windows versus Linux. It is managed versus unmanaged. A fully inventoried Ubuntu server may be less risky than a forgotten developer workstation running WSL images, old containers, and vendor tools no one has updated since the last project shipped.
MSRC’s presence should therefore be read less as a Windows panic flag and more as a nudge toward hybrid inventory discipline. If Microsoft is tracking a Linux kernel UCSI flaw, enterprise IT should assume the vendor ecosystem is more cross-platform than its ticket queues suggest.
The Affected Ranges Tell a Story About Kernel Branches
NVD’s initial analysis lists affected Linux kernel configurations including 7.0 release candidates rc1 through rc6, versions from 6.13 up to but excluding 6.18.22, versions from 6.19 up to but excluding 6.19.12, and versions from 5.5 up to but excluding 6.12.81. Ubuntu’s advisory also points to the mainline fix landing in 7.0-rc7.Those ranges are useful because they make clear this was not a one-off mistake in a single experimental snapshot. The vulnerable code spans multiple maintained and development branches. Stable fixes landed in several kernel lines, which is why administrators should think in terms of distribution-provided kernel updates rather than cherry-picking one commit from kernel.org.
There is also a versioning trap here. Raw upstream kernel numbers rarely map neatly to what enterprises actually run. Ubuntu, Debian, Red Hat-family distributions, SUSE, Android-derived systems, appliance vendors, hypervisor hosts, and embedded platforms all backport fixes differently. A system may report a kernel version that appears older than the fixed upstream version while still containing the backported patch.
That means the right question is not simply “is my kernel lower than 6.12.81?” The right question is whether the distribution or vendor has marked the CVE fixed for the specific package stream you run. Kernel security management is a package provenance exercise, not a numerology contest.
For WindowsForum readers, that distinction should sound familiar. Windows build numbers, cumulative updates, and servicing baselines have trained administrators not to judge security state by marketing version alone. Linux kernel security needs the same habit: identify the vendor kernel package, check the advisory state, apply the update, and reboot into the fixed kernel.
The Patch Is Small Because the Trust Boundary Was in the Wrong Place
The most tempting mistake in reading this CVE is to equate small patch with small lesson. A bounds check does not feel dramatic. But the architectural lesson is larger: hardware-originated values are untrusted input, even when they arrive through an expected firmware protocol.Operating systems have always had to trust hardware at some level. Without trust, there is no boot, no storage, no network, no display, and no power management. But modern kernel design increasingly tries to treat device-provided data as hostile until validated, especially when the device is removable, externally supplied, or mediated through firmware that may vary wildly by vendor.
USB-C multiplies that pressure. It is not merely a port for serial data. It negotiates power delivery, alternate modes, roles, orientation, and device identity across a chain of controllers, firmware, cables, docks, and operating-system drivers. Every place where that chain converts a hardware field into a software index is a potential fault line.
In CVE-2026-31729, the fault line was narrow: a connector value could exceed the array sized for actual connectors. The fixed design places the check in
ucsi_notify_common(), before the number propagates to ucsi_connector_change(). That is the difference between validating at the border and hoping internal code remembers the border exists.The broader industry has spent years learning this lesson in network stacks, file parsers, browser engines, and media codecs. Kernel hardware paths deserve the same skepticism. A peripheral is not automatically benign because it is physically close to the machine.
CVSS 7.8 Is a Warning, Not a Full Threat Model
The CVSS score gives CVE-2026-31729 enough gravity to demand attention, but it should not be mistaken for a complete operational ranking. A 7.8 high rating reflects the theoretical impact of a local, low-complexity flaw that can affect confidentiality, integrity, and availability. It does not prove that reliable exploitation is public, widespread, or equally practical on every affected system.NVD had not provided a CVSS 4.0 assessment at the time of its listed analysis, and the vulnerability’s public description is focused on the memory-safety condition rather than a weaponized exploit chain. That matters. Many kernel memory bugs sit somewhere between “crashable under controlled conditions” and “turnkey privilege escalation,” and public advisories often do not settle the point.
The safer editorial line is to avoid both extremes. It is not responsible to dismiss a high-scoring kernel out-of-bounds access in a hardware-facing subsystem. It is also not responsible to imply that every Linux laptop with USB-C is one malicious dongle away from instant compromise unless evidence supports that.
For administrators, that nuance does not change the action. Kernel updates that fix high-severity memory safety bugs should move through normal expedited patch lanes. The nuance changes the messaging: this is a patch-and-reboot issue, not a reason to rip out every dock in the building tomorrow morning.
The Real Exposure May Be Hiding in Developer Workstations
The obvious targets for a Linux kernel CVE are Linux servers and Linux laptops. The less obvious targets are developer workstations, CI systems, local virtualization environments, and WSL-heavy Windows machines. Those are exactly the places where security ownership can blur.WSL is not automatically implicated by every Linux kernel CVE in the same way a native Linux install is; its kernel is delivered through Microsoft’s servicing path rather than a distribution’s normal kernel package. But WSL has made Linux kernel presence on Windows endpoints ordinary. That changes the inventory conversation, even when a particular vulnerability’s hardware path may not map cleanly to every WSL scenario.
The broader developer stack is even messier. A Windows laptop may host WSL distributions, Docker Desktop, virtual machines, USB-attached test hardware, Android tools, embedded boards, serial adapters, and local Kubernetes clusters. Some of those components rely on Microsoft-maintained layers, some on vendor images, and some on distributions the user installed once and never touched again.
CVE-2026-31729 is a useful excuse to audit that sprawl. Which machines run Linux kernels? Which of those kernels can see physical USB-C hardware directly? Which are updated by Windows Update, which by a Linux package manager, and which by a vendor appliance firmware process? If the answer is “we do not know,” the real vulnerability is not just the missing bounds check.
Developer endpoints are also culturally prone to exception. They are where policy bends because work must continue, debugging requires privileges, and hardware experiments are part of the job. That makes local kernel bugs more interesting than they would be on a locked-down kiosk.
Docks, Dongles, and Firmware Have Joined the Attack Surface
The CVE description’s phrase “malicious or malfunctioning device” deserves attention. It puts deliberate attack and accidental bad behavior in the same operational bucket. Security teams often separate those worlds, but kernel drivers do not have the luxury; a bogus connector number is a bogus connector number whether it comes from hostile hardware, broken firmware, or an edge-case controller state.USB-C docking stations have become little ecosystems. They may contain firmware, multiple controllers, network chips, audio devices, display paths, storage interfaces, and power negotiation logic. Enterprise fleets often standardize on a dock model, but users still bring in personal adapters, travel hubs, monitors with built-in docks, and chargers of unknown provenance.
This does not mean every adapter is suspicious. It means the OS-facing driver stack must assume the adapter can be wrong. In this case, the Linux UCSI code now performs the check it should perform: if the connector number exceeds the number of known connectors, reject the event before it can index outside the array.
There is a subtle availability angle too. Even if exploitation never progresses beyond a crash, kernel panics on machines attached to common docks are still operationally painful. A bug that can be triggered by malformed hardware state can become a support nightmare in offices where every laptop is tethered to the same class of docking station.
That is why administrators should resist treating USB and Type-C bugs as consumer-edge curiosities. The modern office desk is a peripheral bus with a monitor attached.
Distribution Advisories Matter More Than Upstream Romance
Kernel.org patch links are invaluable for engineers, but most organizations should not run their Linux security program from raw upstream commits. The fix for CVE-2026-31729 appears in several stable branches, and Ubuntu’s advisory shows the familiar distribution posture: priority rating, package status, release status, and patch details. That is the language administrators should operate in.The reason is backporting. Enterprise and LTS distributions often take a fix from a newer upstream kernel and apply it to an older supported package. The package version may not resemble the upstream fixed version, yet the vulnerability may be remediated. Conversely, a kernel that looks numerically close to safety may still be vulnerable if it is a custom build without the relevant patch.
This is also where container thinking can mislead people. Containers share the host kernel. Updating a container image does not patch a host kernel vulnerability unless the host itself is updated. If CVE-2026-31729 is relevant to a container host’s kernel and hardware exposure, the remediation lives on the host, not inside the application image.
Cloud systems complicate the picture in the opposite direction. Some managed services abstract kernel patching away from the customer, while infrastructure-as-a-service instances leave the guest OS kernel squarely in the customer’s lap. The same CVE can be vendor-managed in one environment and customer-managed in another.
The operational rule is simple even if the estate is not: follow the advisory for the platform that supplied the kernel you are actually booting. Upstream commit IDs are evidence. Vendor packages are the remediation vehicle.
Windows Administrators Need a Linux Kernel Inventory
For Windows-focused teams, CVE-2026-31729 is a nudge to build or update a Linux kernel inventory without turning it into an ideological debate. The question is not whether Linux is “in scope” for a Windows team. The question is whether the team is responsible for machines, services, or developer workflows that include Linux kernels.Start with the obvious: Linux servers, hypervisor hosts, appliances, NAS devices, security sensors, and cloud instances. Then move to the less obvious: WSL deployments, developer VMs, container hosts, lab machines, build runners, kiosks, and embedded systems connected to Windows-managed networks. Finally, ask which of those systems have direct or indirect exposure to USB-C hardware.
The last question matters because CVE-2026-31729 sits in a hardware notification path. A headless cloud VM with no relevant hardware path may carry a vulnerable source lineage but have very different practical exposure from a Linux laptop used with random docks. Risk is not just version number; it is version number plus reachable code path plus threat model.
Still, patching should not become paralyzed by perfect exploitability analysis. If a supported distribution ships a kernel update for this CVE, install it through normal security maintenance. If a vendor appliance is affected, track the firmware or OS update. If a system is unsupported, this is one more data point in the argument to replace or isolate it.
A mature Windows shop already understands monthly cumulative updates, driver servicing, firmware updates, and reboot coordination. Linux kernel patching requires the same muscles, just with different tooling and sometimes less centralized governance.
The CPE Question Is a Symptom of a Larger Metadata Problem
The NVD entry includes a familiar prompt: “Are we missing a CPE here?” That line is easy to ignore, but it points to one of the chronic weaknesses in vulnerability management. CPE data is often incomplete, late, too broad, or too narrow, especially for ecosystems like the Linux kernel where vendors backport patches and package names differ.For CVE-2026-31729, NVD’s listed CPE configurations are useful because they identify upstream kernel ranges and release candidates. But they are not the whole map. They do not automatically tell you which exact distribution kernels, cloud images, vendor appliances, or custom builds in your environment are exposed.
This is why scanners sometimes produce both false comfort and false panic. A scanner that keys too aggressively on upstream version numbers may flag backported kernels as vulnerable. A scanner that lacks product coverage may miss vendor-maintained kernels entirely. Both errors are common enough that administrators should treat vulnerability metadata as input to judgment, not a substitute for it.
The best remediation records tie together several things: CVE ID, vendor advisory, installed package, fixed package version, reboot state, and asset role. Without reboot state, kernel patch reporting is especially treacherous. A package can be updated while the machine is still running the old kernel.
That last detail is where Windows and Linux administrators can find common ground. Patch installed is not the same as patch active. On kernel bugs, the reboot is part of the fix.
The Security Lesson Is Older Than USB-C
At its core, CVE-2026-31729 is a classic memory-safety lesson dressed in modern hardware clothes. Validate indices before using them. Do not let external fields select internal array elements without checking the array’s real bounds. Put validation at the central parsing point, not scattered downstream.What makes the bug contemporary is the path it took. It came through a USB-C subsystem designed to mediate complex hardware and firmware behavior. It was assigned a public CVE by the kernel ecosystem, enriched by NVD, surfaced by MSRC, tracked by distributions, and absorbed into the patch calendars of organizations that may not think of themselves as Linux shops.
That is the security world WindowsForum readers now inhabit. The Windows endpoint is still important, but it sits in a mesh of kernels, hypervisors, firmware, controllers, and developer runtimes. A single laptop may be a Windows client, a Linux development host, a container platform, a USB hardware lab, and a cloud admin console before lunch.
The old platform silos made vulnerability management look cleaner than it was. The new reality makes the mess visible. CVE-2026-31729 is not the largest kernel bug of the year, but it is a neat specimen of how small driver assumptions propagate into enterprise risk conversations.
The Patch Is Straightforward, but the Inventory Work Is Not
CVE-2026-31729 should not send administrators into emergency theater, but it should move through disciplined kernel maintenance. The advisory trail identifies fixed upstream branches and distribution tracking is already underway. The remaining work is knowing where the affected kernels are, how they are serviced, and whether the fixed kernel is actually running.- Systems running affected Linux kernel lines should receive vendor-provided kernel updates rather than hand-applied upstream commits unless the organization already maintains custom kernels.
- Linux laptops, workstations, and hardware test systems deserve particular attention because the vulnerable path involves USB Type-C/UCSI connector notifications.
- Windows environments should include WSL, developer VMs, container hosts, and Linux-based appliances in vulnerability inventory, even when the primary endpoint fleet is Windows.
- Kernel package updates should be followed by a reboot or other verified kernel activation process, because installing the fix is not the same as running it.
- Scanner results should be checked against distribution advisories because upstream kernel version ranges can misrepresent backported fixes.
- Unsupported systems that cannot receive a fixed kernel should be isolated, retired, or have their exposure reduced, especially where removable peripherals are part of normal use.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center