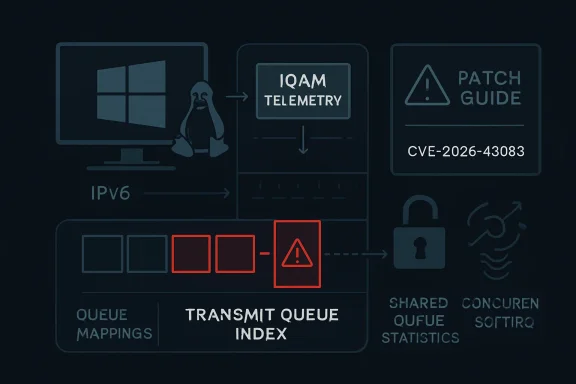
Microsoft’s Security Update Guide listed CVE-2026-43083 on May 6, 2026, after kernel.org assigned the Linux kernel flaw to an IPv6 IOAM networking bug involving an out-of-bounds transmit-queue access and a missing lock in shared queue-statistics handling. The dry wording undersells the point: this is not the next headline-grabbing Linux catastrophe, but it is exactly the kind of kernel defect that modern infrastructure keeps tripping over. It lives where packet metadata, queue mappings, and concurrency rules meet — a place most administrators never look until the crash dump says they should have. For WindowsForum readers, the lesson is not “panic about IOAM6”; it is that Linux risk has become a normal part of Windows estate management.
There was a time when a Linux kernel CVE could be treated as somebody else’s problem by a Windows-heavy shop. That era ended quietly, and then all at once. Windows Subsystem for Linux, Hyper-V guests, Azure images, container hosts, Kubernetes nodes, firewalls, appliances, storage arrays, and developer workstations have made Linux an operating-system dependency even in organizations that still describe themselves as “Microsoft shops.”
CVE-2026-43083 is a good example because it arrived through channels that many Windows administrators now watch by habit. The CVE is sourced to kernel.org, appears in the National Vulnerability Database as awaiting enrichment, and is surfaced by Microsoft’s Security Update Guide. That combination tells us something about the shape of modern patch intelligence: the vendor boundary is no longer the same thing as the operational boundary.
The vulnerability itself sits in the Linux kernel’s IPv6 IOAM implementation. IOAM, or In-situ Operations, Administration, and Maintenance, is a telemetry mechanism that lets network devices add operational data to packets as those packets traverse a path. That makes it useful in tightly controlled environments that care about path visibility and diagnostics, but it also means the code lives in a highly privileged part of the network stack.
This is not a remote-code-execution banner moment, at least not from the information currently public. NVD had not yet assigned CVSS scoring in the record provided, and the description does not claim active exploitation. But the absence of a score should not be mistaken for the absence of importance. Kernel CVEs often begin their public life as terse commit messages, and administrators have to decide what to do before the scoring bureaucracy catches up.
The dangerous case appears when the ingress device has more receive queues than the egress device has transmit queues. The packet’s queue mapping can then point beyond the bounds of the egress device’s transmit queue array. The helper used by the code,
That is the out-of-bounds part. It is the sort of defect that kernel programmers fear because it turns a mismatch between two otherwise legitimate devices into undefined memory access. In kernel land, “out of bounds” is never just a bookkeeping error. It is a potential crash, a corruption path, and sometimes the beginning of something worse, depending on reachability, memory layout, and exploitability.
The second part of the fix is a missing lock around queue-statistics access. The vulnerable path can be called from both soft interrupt context and process context, which means the kernel must respect concurrency rules that are easy to miss when code is written for the common case. The fix uses bottom-half-aware locking, a detail that matters because networking code spends much of its life under interrupt-driven pressure.
The important point is that the two issues are related by more than proximity in the patch. They both reflect the same uncomfortable reality: code that reports network visibility can end up depending on assumptions about queue identity, queue lifetime, and execution context. Telemetry code is still kernel code. It does not get a pass because it is “just” measuring the network.
But observability becomes a different proposition when it moves from user space into the kernel’s packet path. A collector agent can crash, restart, and leave logs behind. A kernel path that mishandles packet metadata can take the host with it. The privilege level changes the risk calculus.
IOAM is especially interesting because it tries to make the network describe itself while traffic is in motion. That is elegant, but elegance does not remove the burden of state. The code has to know whether it is looking at ingress or egress context, whether queue mappings correspond to the current device, and whether the statistics it reads are protected against concurrent mutation.
CVE-2026-43083’s description includes an unusually revealing sentence: the issue showed that per-queue visibility cannot be accurate and will be replaced later as a new feature. That is a quiet but significant admission. The bug fix is not merely plugging a missing bounds check; it is acknowledging that the model behind the visibility feature was not reliable enough.
That should make infrastructure teams cautious about enabling kernel features simply because they sound operationally useful. The Linux kernel has an enormous surface area, and many subsystems are compiled into distribution kernels whether or not an individual organization uses them directly. Risk is not only a matter of whether you intentionally deployed IOAM. It is also a matter of whether the affected code is present, reachable, and exposed by your configuration.
This delay is not merely bureaucratic noise. It affects prioritization systems that depend on severity scores, dashboards that sort by CVSS, and ticket queues that wait for enrichment before escalating work. If a vulnerability has no score, many tools treat it as lower priority by default. That is convenient for dashboards and dangerous for engineering judgment.
Linux kernel CVEs are particularly awkward because exploitability depends heavily on configuration, hardware, namespace boundaries, loaded modules, and whether a code path is reachable by unprivileged users, local containers, privileged network peers, or only administrative configuration. A single global score often hides more than it reveals. CVE-2026-43083 may be irrelevant to one estate and important to another, not because the bug changes, but because the deployment model does.
The better approach is to read the record like a kernel engineer, not like a compliance bot. The phrases that matter here are “out-of-bounds access,” “RX path,” “TX queues,” and “called from both softirq and process contexts.” Those phrases tell you where the risk lives. They point toward networking-heavy hosts, virtualized environments, multiqueue NIC configurations, and kernels with IPv6 IOAM support.
This is why security teams increasingly need kernel-literate triage. You do not need every administrator to read C, but someone in the patch chain must be able to translate a terse commit message into operational exposure. Otherwise, the organization waits for a severity label that may arrive too late or be too generic to help.
Microsoft’s publication of the CVE in its Security Update Guide makes that reality visible. The guide is no longer just a Patch Tuesday digest for Windows desktops and servers. It is part of a broader vulnerability intelligence layer that customers use to track risk across products, dependencies, and cloud-connected infrastructure.
For a Windows-first organization, CVE-2026-43083 should trigger an inventory question before it triggers a remediation panic. Where do we run Linux kernels? Which are vendor-managed? Which are appliance-managed? Which are cloud images? Which are containers sitting on someone else’s host kernel? Which are WSL instances that never appear in the traditional server inventory?
The hardest category is the “hidden Linux” estate. Network appliances and security products may embed Linux kernels but expose only a vendor firmware version. Hypervisor hosts may run Linux guests that are owned by application teams rather than infrastructure teams. Developers may run WSL distributions that update independently of Windows Update. None of these fit neatly into the old patch model.
CVE-2026-43083 is therefore a governance story masquerading as a kernel bug. The vulnerability is specific; the lesson is systemic. If your security process cannot answer where Linux kernels exist in your Microsoft-centered environment, it cannot reliably answer whether this CVE matters.
Administrators sometimes ask whether they should apply an upstream patch manually. In almost every enterprise case, the answer is no. Kernel patching should flow through your distribution or vendor unless you are already in the business of building, signing, testing, and supporting custom kernels. The commit tells you what fixed code looks like; the vendor update tells you what you can safely deploy.
That distinction is especially important for networking bugs. Kernel networking changes can have side effects that only appear under load, with offloads enabled, on particular NICs, or inside virtualized network paths. A bounds check and lock addition may look small in source form, but the kernel you deploy is a contract with drivers, modules, hypervisors, and security tooling.
For home-lab users and enthusiasts, the calculus is different but not reckless. If your distribution has already published a kernel update containing the fix, take it. If you are running release candidates, custom kernels, or rolling distributions, verify whether the fix has landed in your branch rather than assuming newer always means patched. Newer kernels often receive fixes first, but “newer” and “fixed” are not synonyms.
For enterprises, the right motion is correlation. Match the CVE to vendor advisories, map advisories to packages, map packages to assets, and then prioritize hosts where IPv6, advanced networking, multiqueue NICs, or IOAM-related configurations are plausible. If that sounds slower than simply patching everything, it is. But it is also how large fleets avoid turning a low-observed-risk kernel fix into a high-impact outage.
The function at issue can be reached from both softirq and process contexts. That means the same data can be touched under different scheduling and interrupt conditions. Without proper locking, even a read of queue statistics can become unsafe if the underlying state changes at the wrong moment.
The fix’s use of
Administrators do not need to understand every locking primitive to appreciate the operational signal. If a bug involves both out-of-bounds access and a missing lock in the networking stack, treat it as a stability risk even before exploitability is proven. A denial-of-service condition on a critical network host can be as damaging as a cleaner security compromise, particularly when the host is a router, gateway, load balancer, or container node.
That framing matters because vulnerability management programs often over-index on attacker narratives. They ask whether the bug can be exploited remotely, whether exploit code exists, and whether ransomware crews are using it. Those are valid questions. But kernel bugs also deserve an availability lens, and CVE-2026-43083 sits squarely in that category until more specific exploit data emerges.
The vulnerability’s trigger condition involves a mismatch between receive queues on one device and transmit queues on another. That is not exotic in modern systems. Multiqueue NICs, virtual interfaces, bridges, tunnels, namespaces, veth pairs, and offload-heavy configurations create plenty of opportunities for packet metadata to cross device boundaries.
The record specifically describes an RX-path packet whose queue mapping belongs to the ingress device while the code indexes into the egress device’s transmit queues. That is a subtle bug because the queue mapping is not inherently invalid. It is valid in one context and unsafe in another. Context bugs are often harder to reason about than obviously bad input.
This is why the phrase “skb_get_tx_queue() does not clamp the index” matters. Kernel helper functions do exactly what their contracts say, not what a tired reader hopes they do. If a caller passes a mapping from the wrong device context, the helper will not rescue the design. The bug is not merely an absent guardrail; it is a mismatch between assumptions.
For operators, the lesson is to be careful with dismissals based on feature names. “We do not use IOAM” is useful but incomplete. Better questions include whether the affected code is compiled into your kernel, whether untrusted traffic can influence the path, whether IOAM sysctls or routes are configured, and whether vendor kernels have carried the vulnerable code into supported releases.
This is not necessarily inflation. It is a more honest view of kernel risk. The kernel is a large, memory-unsafe, privilege-rich codebase where small correctness bugs can become security issues depending on reachability. Assigning CVEs to resolved kernel bugs gives downstream vendors and users a common handle, even when exploitability is not yet fully characterized.
The downside is noise. Security teams are flooded with records that say “the following vulnerability has been resolved” and little more. Some will be critical in a given estate. Some will be irrelevant. Some will never be exploited. Some will become obvious only after a researcher connects the dots.
CVE-2026-43083 sits in the middle of that new reality. It has enough technical detail to justify attention, not enough public scoring to automate prioritization, and a subsystem that many administrators will have to research before deciding exposure. That is not a failure of the CVE system so much as a sign that kernel vulnerability management is now an engineering discipline.
Windows administrators have seen a similar evolution in Microsoft’s own ecosystem. Patch Tuesday used to be a relatively bounded monthly ritual. Now it includes cloud services, firmware-adjacent updates, browser channels, Office components, identity systems, and third-party dependencies. Linux kernel CVEs appearing in Microsoft-facing workflows are another step in the same direction.
Start with exposure. Identify Linux kernels in servers, cloud workloads, WSL environments, network appliances, and container hosts. Then separate systems you patch directly from systems patched by a vendor or cloud provider. A managed appliance may require firmware, not a package update. A container image update may do nothing if the vulnerable code is in the host kernel.
Next, look for distribution advisories and package versions. Upstream stable commits are a map, not a deployment artifact. If your vendor has not yet published guidance, track the issue but resist unsupported kernel surgery unless your risk model demands it and you have the capability to test.
Finally, prioritize by role. A lightly used lab VM and a production network gateway do not deserve the same urgency. Hosts doing advanced IPv6 networking, packet processing, routing, virtualization, or container networking should move higher in the queue than generic single-purpose systems with minimal network exposure.
This approach is not glamorous, but it avoids the two classic errors of vulnerability management: treating every CVE as a five-alarm fire, and treating every unscored CVE as background noise. CVE-2026-43083 deserves a middle lane: investigate promptly, patch through supported channels, and watch for downstream scoring or exploitability updates.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Linux CVE Lands in Microsoft’s Front Yard
A Linux CVE Lands in Microsoft’s Front Yard
There was a time when a Linux kernel CVE could be treated as somebody else’s problem by a Windows-heavy shop. That era ended quietly, and then all at once. Windows Subsystem for Linux, Hyper-V guests, Azure images, container hosts, Kubernetes nodes, firewalls, appliances, storage arrays, and developer workstations have made Linux an operating-system dependency even in organizations that still describe themselves as “Microsoft shops.”CVE-2026-43083 is a good example because it arrived through channels that many Windows administrators now watch by habit. The CVE is sourced to kernel.org, appears in the National Vulnerability Database as awaiting enrichment, and is surfaced by Microsoft’s Security Update Guide. That combination tells us something about the shape of modern patch intelligence: the vendor boundary is no longer the same thing as the operational boundary.
The vulnerability itself sits in the Linux kernel’s IPv6 IOAM implementation. IOAM, or In-situ Operations, Administration, and Maintenance, is a telemetry mechanism that lets network devices add operational data to packets as those packets traverse a path. That makes it useful in tightly controlled environments that care about path visibility and diagnostics, but it also means the code lives in a highly privileged part of the network stack.
This is not a remote-code-execution banner moment, at least not from the information currently public. NVD had not yet assigned CVSS scoring in the record provided, and the description does not claim active exploitation. But the absence of a score should not be mistaken for the absence of importance. Kernel CVEs often begin their public life as terse commit messages, and administrators have to decide what to do before the scoring bureaucracy catches up.
The Bug Is Small, but the Boundary It Crosses Is Not
The core failure is almost disappointingly mechanical. When a specific IOAM trace type bit is set, the kernel code tries to fetch a transmit queue from an egress network device using a queue mapping stored in the packet buffer. That is fine when the mapping actually belongs to the egress device. It is not fine when the packet is on the receive path and the mapping reflects an ingress device instead.The dangerous case appears when the ingress device has more receive queues than the egress device has transmit queues. The packet’s queue mapping can then point beyond the bounds of the egress device’s transmit queue array. The helper used by the code,
skb_get_tx_queue(), does not clamp the index, so the caller has to ensure the mapping is valid before indexing into dev->_tx[].That is the out-of-bounds part. It is the sort of defect that kernel programmers fear because it turns a mismatch between two otherwise legitimate devices into undefined memory access. In kernel land, “out of bounds” is never just a bookkeeping error. It is a potential crash, a corruption path, and sometimes the beginning of something worse, depending on reachability, memory layout, and exploitability.
The second part of the fix is a missing lock around queue-statistics access. The vulnerable path can be called from both soft interrupt context and process context, which means the kernel must respect concurrency rules that are easy to miss when code is written for the common case. The fix uses bottom-half-aware locking, a detail that matters because networking code spends much of its life under interrupt-driven pressure.
The important point is that the two issues are related by more than proximity in the patch. They both reflect the same uncomfortable reality: code that reports network visibility can end up depending on assumptions about queue identity, queue lifetime, and execution context. Telemetry code is still kernel code. It does not get a pass because it is “just” measuring the network.
IOAM6 Shows the Cost of Kernel-Level Observability
The industry has spent the last decade telling itself that more telemetry is always better. In general, that is true. You cannot operate what you cannot see, and distributed systems have made packet path visibility a serious operational need rather than a luxury for hyperscalers.But observability becomes a different proposition when it moves from user space into the kernel’s packet path. A collector agent can crash, restart, and leave logs behind. A kernel path that mishandles packet metadata can take the host with it. The privilege level changes the risk calculus.
IOAM is especially interesting because it tries to make the network describe itself while traffic is in motion. That is elegant, but elegance does not remove the burden of state. The code has to know whether it is looking at ingress or egress context, whether queue mappings correspond to the current device, and whether the statistics it reads are protected against concurrent mutation.
CVE-2026-43083’s description includes an unusually revealing sentence: the issue showed that per-queue visibility cannot be accurate and will be replaced later as a new feature. That is a quiet but significant admission. The bug fix is not merely plugging a missing bounds check; it is acknowledging that the model behind the visibility feature was not reliable enough.
That should make infrastructure teams cautious about enabling kernel features simply because they sound operationally useful. The Linux kernel has an enormous surface area, and many subsystems are compiled into distribution kernels whether or not an individual organization uses them directly. Risk is not only a matter of whether you intentionally deployed IOAM. It is also a matter of whether the affected code is present, reachable, and exposed by your configuration.
The CVE Record Is Sparse Because Kernel Security Moves Faster Than Scoring
The NVD entry for CVE-2026-43083 is marked as awaiting enrichment. That phrase has become familiar to anyone who tracks Linux kernel CVEs in real time. A record appears with a kernel.org description, references to stable commits, and little else. CVSS vectors, CWE mappings, and downstream vendor advisories arrive later, sometimes after administrators have already made their patch decisions.This delay is not merely bureaucratic noise. It affects prioritization systems that depend on severity scores, dashboards that sort by CVSS, and ticket queues that wait for enrichment before escalating work. If a vulnerability has no score, many tools treat it as lower priority by default. That is convenient for dashboards and dangerous for engineering judgment.
Linux kernel CVEs are particularly awkward because exploitability depends heavily on configuration, hardware, namespace boundaries, loaded modules, and whether a code path is reachable by unprivileged users, local containers, privileged network peers, or only administrative configuration. A single global score often hides more than it reveals. CVE-2026-43083 may be irrelevant to one estate and important to another, not because the bug changes, but because the deployment model does.
The better approach is to read the record like a kernel engineer, not like a compliance bot. The phrases that matter here are “out-of-bounds access,” “RX path,” “TX queues,” and “called from both softirq and process contexts.” Those phrases tell you where the risk lives. They point toward networking-heavy hosts, virtualized environments, multiqueue NIC configurations, and kernels with IPv6 IOAM support.
This is why security teams increasingly need kernel-literate triage. You do not need every administrator to read C, but someone in the patch chain must be able to translate a terse commit message into operational exposure. Otherwise, the organization waits for a severity label that may arrive too late or be too generic to help.
Windows Administrators Are Now Linux Patch Managers
The reason this CVE belongs on WindowsForum is not that Windows itself is affected. It is that Windows administrators increasingly own platforms that contain Linux whether they asked for them or not. WSL instances run on developer laptops. Linux containers run in CI pipelines. Linux appliances terminate VPNs and inspect traffic. Azure workloads often mix Windows Server with Linux nodes behind the same identity, logging, and patch-management processes.Microsoft’s publication of the CVE in its Security Update Guide makes that reality visible. The guide is no longer just a Patch Tuesday digest for Windows desktops and servers. It is part of a broader vulnerability intelligence layer that customers use to track risk across products, dependencies, and cloud-connected infrastructure.
For a Windows-first organization, CVE-2026-43083 should trigger an inventory question before it triggers a remediation panic. Where do we run Linux kernels? Which are vendor-managed? Which are appliance-managed? Which are cloud images? Which are containers sitting on someone else’s host kernel? Which are WSL instances that never appear in the traditional server inventory?
The hardest category is the “hidden Linux” estate. Network appliances and security products may embed Linux kernels but expose only a vendor firmware version. Hypervisor hosts may run Linux guests that are owned by application teams rather than infrastructure teams. Developers may run WSL distributions that update independently of Windows Update. None of these fit neatly into the old patch model.
CVE-2026-43083 is therefore a governance story masquerading as a kernel bug. The vulnerability is specific; the lesson is systemic. If your security process cannot answer where Linux kernels exist in your Microsoft-centered environment, it cannot reliably answer whether this CVE matters.
The Stable Kernel References Matter More Than the CVSS Blank
The CVE record points to stable kernel commits, which is where the practical work begins. Linux kernel security remediation is often a matter of mapping a fix to the version streams used by distributions and vendors. The mainline or stable commit is not the same thing as a patched Ubuntu, Debian, Red Hat, SUSE, Oracle, Amazon Linux, Azure Linux, or appliance firmware build.Administrators sometimes ask whether they should apply an upstream patch manually. In almost every enterprise case, the answer is no. Kernel patching should flow through your distribution or vendor unless you are already in the business of building, signing, testing, and supporting custom kernels. The commit tells you what fixed code looks like; the vendor update tells you what you can safely deploy.
That distinction is especially important for networking bugs. Kernel networking changes can have side effects that only appear under load, with offloads enabled, on particular NICs, or inside virtualized network paths. A bounds check and lock addition may look small in source form, but the kernel you deploy is a contract with drivers, modules, hypervisors, and security tooling.
For home-lab users and enthusiasts, the calculus is different but not reckless. If your distribution has already published a kernel update containing the fix, take it. If you are running release candidates, custom kernels, or rolling distributions, verify whether the fix has landed in your branch rather than assuming newer always means patched. Newer kernels often receive fixes first, but “newer” and “fixed” are not synonyms.
For enterprises, the right motion is correlation. Match the CVE to vendor advisories, map advisories to packages, map packages to assets, and then prioritize hosts where IPv6, advanced networking, multiqueue NICs, or IOAM-related configurations are plausible. If that sounds slower than simply patching everything, it is. But it is also how large fleets avoid turning a low-observed-risk kernel fix into a high-impact outage.
The Missing Lock Is the Part Sysadmins Should Not Skip
Out-of-bounds access is the phrase that gets attention, but the missing lock may be the more instructive part of the story. Concurrency bugs in the kernel are not glamorous. They rarely come with a clean exploit narrative at first. Yet they are the kind of defects that produce intermittent crashes, hard-to-reproduce corruption, and support cases that bounce between vendors.The function at issue can be reached from both softirq and process contexts. That means the same data can be touched under different scheduling and interrupt conditions. Without proper locking, even a read of queue statistics can become unsafe if the underlying state changes at the wrong moment.
The fix’s use of
spin_lock_bh() is a reminder that kernel locking is context-sensitive. It is not enough to lock; you must lock in a way that accounts for bottom halves, soft interrupts, and the execution model of the network stack. This is the sort of detail that separates “works in a lab” from “survives production traffic at 40 Gbps.”Administrators do not need to understand every locking primitive to appreciate the operational signal. If a bug involves both out-of-bounds access and a missing lock in the networking stack, treat it as a stability risk even before exploitability is proven. A denial-of-service condition on a critical network host can be as damaging as a cleaner security compromise, particularly when the host is a router, gateway, load balancer, or container node.
That framing matters because vulnerability management programs often over-index on attacker narratives. They ask whether the bug can be exploited remotely, whether exploit code exists, and whether ransomware crews are using it. Those are valid questions. But kernel bugs also deserve an availability lens, and CVE-2026-43083 sits squarely in that category until more specific exploit data emerges.
The Networking Edge Is Where “Niche” Stops Being Niche
It is tempting to dismiss IOAM6 as a niche feature. Many environments do not knowingly use IPv6 IOAM, and most desktop Linux users will never configure it. But niche kernel features can become relevant in specialized places that are disproportionately important: cloud networks, labs, telecom systems, observability platforms, network-function virtualization, and high-density hosts with complex queue layouts.The vulnerability’s trigger condition involves a mismatch between receive queues on one device and transmit queues on another. That is not exotic in modern systems. Multiqueue NICs, virtual interfaces, bridges, tunnels, namespaces, veth pairs, and offload-heavy configurations create plenty of opportunities for packet metadata to cross device boundaries.
The record specifically describes an RX-path packet whose queue mapping belongs to the ingress device while the code indexes into the egress device’s transmit queues. That is a subtle bug because the queue mapping is not inherently invalid. It is valid in one context and unsafe in another. Context bugs are often harder to reason about than obviously bad input.
This is why the phrase “skb_get_tx_queue() does not clamp the index” matters. Kernel helper functions do exactly what their contracts say, not what a tired reader hopes they do. If a caller passes a mapping from the wrong device context, the helper will not rescue the design. The bug is not merely an absent guardrail; it is a mismatch between assumptions.
For operators, the lesson is to be careful with dismissals based on feature names. “We do not use IOAM” is useful but incomplete. Better questions include whether the affected code is compiled into your kernel, whether untrusted traffic can influence the path, whether IOAM sysctls or routes are configured, and whether vendor kernels have carried the vulnerable code into supported releases.
The Kernel CNA Era Has Made CVEs More Numerous and More Honest
Linux kernel CVE handling has changed in recent years, and administrators are still adjusting. Kernel.org’s role as a CVE Numbering Authority has made the relationship between bug fixes and vulnerability identifiers more direct. That means more kernel fixes become CVEs, and many of those CVEs look underwhelming to anyone trained on the old model of named bugs and dramatic vendor advisories.This is not necessarily inflation. It is a more honest view of kernel risk. The kernel is a large, memory-unsafe, privilege-rich codebase where small correctness bugs can become security issues depending on reachability. Assigning CVEs to resolved kernel bugs gives downstream vendors and users a common handle, even when exploitability is not yet fully characterized.
The downside is noise. Security teams are flooded with records that say “the following vulnerability has been resolved” and little more. Some will be critical in a given estate. Some will be irrelevant. Some will never be exploited. Some will become obvious only after a researcher connects the dots.
CVE-2026-43083 sits in the middle of that new reality. It has enough technical detail to justify attention, not enough public scoring to automate prioritization, and a subsystem that many administrators will have to research before deciding exposure. That is not a failure of the CVE system so much as a sign that kernel vulnerability management is now an engineering discipline.
Windows administrators have seen a similar evolution in Microsoft’s own ecosystem. Patch Tuesday used to be a relatively bounded monthly ritual. Now it includes cloud services, firmware-adjacent updates, browser channels, Office components, identity systems, and third-party dependencies. Linux kernel CVEs appearing in Microsoft-facing workflows are another step in the same direction.
Patch Strategy Beats Patch Theater
The wrong response to CVE-2026-43083 is performative urgency. The equally wrong response is to ignore it because NVD has no score yet. The right response is boring, disciplined, and asset-driven.Start with exposure. Identify Linux kernels in servers, cloud workloads, WSL environments, network appliances, and container hosts. Then separate systems you patch directly from systems patched by a vendor or cloud provider. A managed appliance may require firmware, not a package update. A container image update may do nothing if the vulnerable code is in the host kernel.
Next, look for distribution advisories and package versions. Upstream stable commits are a map, not a deployment artifact. If your vendor has not yet published guidance, track the issue but resist unsupported kernel surgery unless your risk model demands it and you have the capability to test.
Finally, prioritize by role. A lightly used lab VM and a production network gateway do not deserve the same urgency. Hosts doing advanced IPv6 networking, packet processing, routing, virtualization, or container networking should move higher in the queue than generic single-purpose systems with minimal network exposure.
This approach is not glamorous, but it avoids the two classic errors of vulnerability management: treating every CVE as a five-alarm fire, and treating every unscored CVE as background noise. CVE-2026-43083 deserves a middle lane: investigate promptly, patch through supported channels, and watch for downstream scoring or exploitability updates.
The Practical Signal Hidden in a Queue-Mapping Bug
For all the kernel detail, this CVE reduces to a few operational truths. It is a Linux kernel networking flaw, it involves IPv6 IOAM, it has upstream stable fixes referenced, and its public record began without NVD severity scoring. That is enough to act intelligently without pretending to know more than the record currently proves.- Administrators should not wait for a CVSS score before determining whether their Linux kernels include the affected IOAM6 code path.
- Windows-first teams should treat Linux hosts, WSL distributions, appliances, and container nodes as part of the same vulnerability-management inventory.
- Distribution and appliance vendor updates are the right remediation path for most organizations, even when upstream stable commits are already visible.
- Systems involved in routing, packet processing, virtualization, container networking, or advanced IPv6 telemetry deserve earlier review than ordinary low-exposure hosts.
- The missing lock makes this a stability concern as well as a security concern, particularly for network-heavy systems where intermittent kernel faults can cause real outages.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center