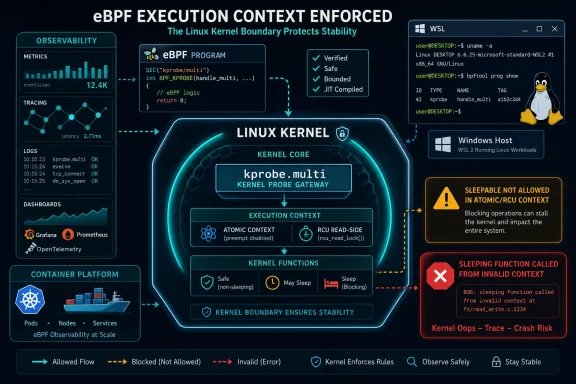
CVE-2026-43010 is a Linux kernel BPF vulnerability published by NVD on May 1, 2026, affecting kprobe.multi attachment handling where sleepable BPF programs could be accepted in atomic/RCU context and trigger a kernel availability failure. The bug is not a glamorous remote code execution headline, but it is exactly the kind of kernel boundary mistake that matters in modern Linux and Windows-adjacent infrastructure. It sits at the intersection of observability, security tooling, container platforms, WSL, and the growing reliance on eBPF as a privileged instrumentation layer. The lesson is simple: when BPF becomes infrastructure, BPF correctness becomes availability engineering.
The National Vulnerability Database rates CVE-2026-43010 as a medium-severity issue under CVSS 3.1, with local access, low attack complexity, low privileges, no user interaction, unchanged scope, no confidentiality impact, no integrity impact, and high availability impact. That scoring tells administrators almost everything they need to know and almost nothing they need to feel comfortable.
This is not a bug that lets an unauthenticated attacker spray packets at a server and seize control. It is also not a harmless warning in a dusty subsystem. It lives in the Linux kernel’s BPF machinery, and BPF is now one of the places where production Linux systems concentrate power: tracing, telemetry, network policy, runtime security, profiling, sandboxing, and increasingly container observability.
The core failure is narrow. A BPF program type intended to attach to multiple kprobes could be marked sleepable, even though the execution context for those probes cannot sleep. When such a program invoked helpers that may sleep, such as copying from user memory, the kernel could hit the classic “sleeping function called from invalid context” warning path.
That may sound like an implementation detail, but kernel context rules are not etiquette. They are survival rules. If code that must run atomically tries to sleep, the kernel has caught itself in a contradiction.
The Linux kernel already has different expectations for different BPF attachment points. Some BPF programs may run in contexts where sleeping is allowed. Others are triggered from sensitive execution paths where blocking would break kernel assumptions. The vulnerability existed because the attach path did not enforce that distinction early enough for kprobe.multi.
The problem was not that a sleeping helper suddenly became unsafe. It was always unsafe in that context. The failure was that the kernel allowed a program with the wrong execution contract to be attached in the first place.
That distinction matters operationally. If the failure were buried deep in helper behavior, administrators might worry about every user of a particular helper. Instead, the fix aligns the front door with the room behind it: if the probe context cannot sleep, a sleepable program does not get in.
Modern security agents use BPF to watch process behavior. Observability stacks use it to profile services with low overhead. Kubernetes networking and policy projects use it to accelerate packet paths and enforce rules. Developers use it to ask production systems questions that were previously impractical without custom kernel modules.
That success changes the risk model. A BPF bug no longer affects only kernel developers and tracing enthusiasts. It can affect the software agents administrators install precisely because they want better security, better monitoring, or better visibility.
CVE-2026-43010 is a useful reminder that BPF is powerful because it crosses boundaries that ordinary user-space code cannot cross. The verifier, program types, helper restrictions, and attach-time checks are the layered guardrails that make that power tolerable. When one of those guardrails is missing, the bug may be small in code but large in principle.
Local kernel availability bugs matter in multi-user systems, development hosts, CI runners, container platforms, and shared research machines. They matter wherever “local user” does not mean “trusted human sitting at a keyboard.” In contemporary infrastructure, a local execution context may belong to a build job, a containerized workload, a plugin, a compromised service account, or a developer toolchain.
The interesting question is not whether the bug is remotely exploitable in the classical sense. The interesting question is who can load or attach the relevant BPF program on your systems. That answer varies dramatically by distribution, kernel configuration, sysctl policy, container runtime settings, capabilities, and security posture.
Many hardened systems already restrict unprivileged BPF. Some environments require capabilities such as CAP_BPF, CAP_PERFMON, or CAP_SYS_ADMIN for sensitive BPF operations. Others have legacy settings or developer-friendly configurations that make experimentation easier. The practical exposure is therefore less about the CVE name and more about your BPF access model.
The NVD vector gives availability a high impact while leaving confidentiality and integrity untouched. That is an honest description of this bug’s shape. The attacker is not reading secrets through this path, and the fix does not describe arbitrary write primitives or privilege escalation.
But “only availability” can still be expensive. On a Kubernetes node, a kernel-level availability failure does not politely affect one pod. On a developer workstation, it can cost unsaved work and corrupt state. On a CI runner, it can turn into flaky infrastructure that teams waste hours diagnosing as an application problem.
Kernel availability failures also carry a psychological cost for operations teams. A user-space service crash is annoying. A kernel complaint involving atomic context, RCU nesting, and BPF helpers is the kind of event that makes administrators wonder what else is lurking below the waterline.
Microsoft ships and supports Linux in several ways. WSL 2 uses a real Linux kernel inside a lightweight virtual machine. Azure customers run countless Linux VMs. Microsoft maintains Linux-related components and publishes vulnerability guidance for customers who manage mixed estates. Seeing a Linux kernel CVE in an MSRC context does not mean the Windows kernel suddenly inherited a BPF flaw.
For ordinary Windows users who do not run WSL 2, Linux virtual machines, containers, or Linux hosts, CVE-2026-43010 is not a Windows desktop emergency. For power users and administrators who do run WSL 2, Docker Desktop backends, Linux dev environments, Azure Linux workloads, or security tooling that relies on BPF, it belongs on the patch radar.
The Windows angle is therefore not “Windows is vulnerable.” It is that Windows environments increasingly include Linux kernels as first-class operational components. The boundary between Windows administration and Linux kernel hygiene is thinner than it used to be.
Microsoft’s WSL documentation describes a separate Linux kernel update path and notes that WSL 2’s kernel is serviced apart from the Windows image. In practice, many users never think about this distinction because WSL feels like a feature rather than a VM-like Linux environment. CVEs like this make the abstraction leak in useful ways.
If a WSL 2 kernel line includes the vulnerable code and exposes the relevant BPF functionality, the remediation path is not to uninstall Windows updates randomly or hunt through Ubuntu packages alone. The relevant component is the kernel WSL is actually running. Checking
That does not mean every WSL user is at meaningful risk. BPF capabilities, kernel configuration, Microsoft’s WSL kernel branch, and local privilege boundaries all affect exploitability. But it does mean Windows developers should stop treating the Linux kernel inside WSL as invisible plumbing.
Mainline, stable, long-term, vendor, cloud, and distribution kernels do not move in lockstep. A fix can land upstream, then appear in stable branches, then be backported by distributions into kernels whose version numbers do not obviously match the upstream range. Enterprise distributions may carry patches without changing the base kernel version in the way a casual
That is why kernel CVE management often frustrates teams that rely only on raw version comparison. A server running a “5.15” or “6.1” branded kernel may contain hundreds or thousands of backported fixes. Conversely, a custom-built or fast-moving kernel can sit closer to upstream and require more direct attention to stable patch levels.
The safest operational answer is vendor-specific. For Ubuntu, Red Hat, SUSE, Debian, Microsoft, cloud-provider kernels, and appliance kernels, administrators should follow the vendor advisory and package status rather than improvising from NVD CPE strings alone.
Attach-time rejection is better than relying on a later failure. It makes the invalid configuration impossible, or at least much harder to reach. It also gives developers clearer feedback: the program does not belong at that hook point.
That is how kernel security should age. Not every fix needs to be a dramatic mitigation or a sprawling rewrite. Sometimes the durable answer is to make the kernel say “no” earlier, closer to the user’s request, before the system has constructed a dangerous state.
For BPF developers, this is a signal to test attachment compatibility as deliberately as verifier compatibility. Passing the verifier is not the same as being valid for every hook. Helper availability, sleepability, execution context, and attach type are part of the contract.
If an organization deploys BPF-heavy tooling across fleets, CVE-2026-43010 deserves a look even if no hostile user is present. A tool bug, misconfiguration, experimental probe, or incompatible agent version could trip the same kernel warning path that an attacker would abuse deliberately.
This is a recurring pattern in security infrastructure. The agent installed to improve visibility often holds privileges and kernel touchpoints ordinary software never receives. That does not make such agents bad; it makes their compatibility matrix part of the risk surface.
Administrators should ask vendors whether their BPF programs use kprobe.multi and whether they request sleepable mode. Good vendors should be able to answer. Better vendors should already be testing against kernels with the fix, because the correct behavior after patching is rejection rather than mysterious kernel noise.
In well-hardened clusters, untrusted workloads should not be able to load arbitrary BPF programs. In real clusters, exceptions exist. Privileged containers, node agents, CNI components, observability DaemonSets, and debugging pods often receive elevated access for practical reasons. Those exceptions are where kernel bugs become cluster reliability issues.
The right response is not to rip out every BPF-based tool. That would be self-defeating. The right response is to narrow who can attach BPF programs, audit privileged workloads, and treat node kernel updates as part of application-platform maintenance rather than a separate dark art.
CVE-2026-43010 is especially useful as a policy review prompt because its exploit preconditions are not exotic. If an entity can attach the wrong kind of BPF program, the kernel must enforce the boundary. If your platform allows too many entities to try, you have a broader governance problem.
This distinction matters for support desks and platform teams. A developer may report that a tracing tool stopped working after a kernel update. The temptation will be to blame the patch and seek a workaround. The correct interpretation is more likely that the tool was relying on a combination the kernel should not have accepted.
Healthy tooling should adapt by choosing a compatible hook, avoiding sleepable helpers in non-sleepable context, or restructuring the probe. A kernel that rejects invalid attachment is easier to reason about than one that accepts it and later emits frightening scheduler complaints under load.
There is a broader cultural lesson here. Security fixes often expose latent bugs in tools that were skating along undefined or under-enforced behavior. The resulting breakage is real, but it should be treated as forced correctness rather than arbitrary vendor hostility.
But NVD entries for kernel CVEs are often rough at the edges, especially early in their lifecycle. The weakness field may say insufficient information. CPE mapping may lag or overgeneralize. Version ranges may not reflect every vendor backport or downstream patch.
That is not a reason to ignore NVD. It is a reason to avoid treating it as a substitute for kernel stable notes, distribution advisories, and vendor patch status. CVE triage is strongest when NVD is the index, not the judge and jury.
The MSRC entry adds visibility for Microsoft customers, but it does not change the underlying technical ownership. This is a Linux kernel issue resolved in the Linux kernel. Microsoft’s relevance is in the environments where Microsoft delivers, hosts, documents, or supports Linux components.
Linux distributions and kernels have evolved their controls around unprivileged BPF because BPF has repeatedly proven both useful and security-sensitive. Some systems disable unprivileged BPF entirely. Others gate features behind capabilities. Some development environments loosen restrictions because engineers need tracing tools to work.
That variability means fleet owners need facts rather than assumptions. On a hardened production host, the vulnerable code path may be reachable only by root-equivalent actors or trusted agents. On a shared lab machine or permissive dev server, the reachable population may be larger.
This is where local availability bugs become governance tests. If every developer, build job, or container can exercise complex kernel instrumentation features, CVE-2026-43010 is only one example of a larger exposure. The long-term mitigation is not just patching this bug; it is defining who gets to ask the kernel these questions.
But it should move faster in environments that rely heavily on BPF, permit shared local access, run multi-tenant Linux workloads, or use privileged observability and security agents. It should also move quickly on systems where kernel crashes or node instability carry high operational cost.
For home Linux users and Windows users with occasional WSL sessions, the practical advice is boring and correct: take normal kernel updates, update WSL, and avoid running random privileged tracing tools from the internet. For enterprise administrators, the advice is to align the fix with the next kernel maintenance window unless exposure analysis says it needs to jump the queue.
Live patching may or may not be available depending on vendor support and kernel branch. Where it is not, reboot planning remains the unglamorous heart of kernel security. A kernel fix that is installed but not booted is an artifact, not protection.
That creates a dependency chain many customers do not fully see. A SaaS-branded agent running on your node may depend on BPF program types, helpers, verifier behavior, kernel configuration, and attach semantics. A kernel patch that tightens those semantics can change the agent’s behavior overnight.
The better vendors will treat this as routine. They will test across stable kernels, detect unsupported attachment modes, fail gracefully, and document required capabilities. The weaker vendors will ask customers to loosen kernel controls, run privileged containers, or pin older kernels.
CVE-2026-43010 is another small vote for choosing vendors that understand the kernel surface they consume. BPF is not just an API. It is a negotiated privilege boundary with the operating system.
CVE-2026-43010 will not be remembered as the kernel bug that changed the industry, and that is precisely why it is useful. It shows how modern infrastructure risk often arrives as a small missing validation check in a powerful subsystem that everyone else has quietly learned to depend on. The future of BPF will be more enforcement, more explicit attach-time rules, and more friction for tools that relied on permissive behavior; administrators should welcome that direction, because the alternative is discovering context violations only after the kernel starts shouting.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Medium CVE With a Very Kernel-Shaped Blast Radius
A Medium CVE With a Very Kernel-Shaped Blast Radius
The National Vulnerability Database rates CVE-2026-43010 as a medium-severity issue under CVSS 3.1, with local access, low attack complexity, low privileges, no user interaction, unchanged scope, no confidentiality impact, no integrity impact, and high availability impact. That scoring tells administrators almost everything they need to know and almost nothing they need to feel comfortable.This is not a bug that lets an unauthenticated attacker spray packets at a server and seize control. It is also not a harmless warning in a dusty subsystem. It lives in the Linux kernel’s BPF machinery, and BPF is now one of the places where production Linux systems concentrate power: tracing, telemetry, network policy, runtime security, profiling, sandboxing, and increasingly container observability.
The core failure is narrow. A BPF program type intended to attach to multiple kprobes could be marked sleepable, even though the execution context for those probes cannot sleep. When such a program invoked helpers that may sleep, such as copying from user memory, the kernel could hit the classic “sleeping function called from invalid context” warning path.
That may sound like an implementation detail, but kernel context rules are not etiquette. They are survival rules. If code that must run atomically tries to sleep, the kernel has caught itself in a contradiction.
The Bug Is a Permission Check Wearing a Scheduler Hat
The fix for CVE-2026-43010 is conceptually modest: reject sleepable kprobe.multi programs at attach time. That is the kind of patch that looks obvious after the fact, which is often the mark of a good security fix rather than a trivial one.The Linux kernel already has different expectations for different BPF attachment points. Some BPF programs may run in contexts where sleeping is allowed. Others are triggered from sensitive execution paths where blocking would break kernel assumptions. The vulnerability existed because the attach path did not enforce that distinction early enough for kprobe.multi.
The problem was not that a sleeping helper suddenly became unsafe. It was always unsafe in that context. The failure was that the kernel allowed a program with the wrong execution contract to be attached in the first place.
That distinction matters operationally. If the failure were buried deep in helper behavior, administrators might worry about every user of a particular helper. Instead, the fix aligns the front door with the room behind it: if the probe context cannot sleep, a sleepable program does not get in.
BPF Has Become Too Important to Treat as Exotic
A decade ago, many administrators could look at a BPF flaw and reasonably decide it was someone else’s problem. That is no longer true. eBPF has moved from niche packet filtering and tracing into the nervous system of Linux operations.Modern security agents use BPF to watch process behavior. Observability stacks use it to profile services with low overhead. Kubernetes networking and policy projects use it to accelerate packet paths and enforce rules. Developers use it to ask production systems questions that were previously impractical without custom kernel modules.
That success changes the risk model. A BPF bug no longer affects only kernel developers and tracing enthusiasts. It can affect the software agents administrators install precisely because they want better security, better monitoring, or better visibility.
CVE-2026-43010 is a useful reminder that BPF is powerful because it crosses boundaries that ordinary user-space code cannot cross. The verifier, program types, helper restrictions, and attach-time checks are the layered guardrails that make that power tolerable. When one of those guardrails is missing, the bug may be small in code but large in principle.
Local Privilege Is Not a Comfort Blanket
The CVSS vector marks the attack as local and requiring low privileges. That should reduce panic. It should not induce dismissal.Local kernel availability bugs matter in multi-user systems, development hosts, CI runners, container platforms, and shared research machines. They matter wherever “local user” does not mean “trusted human sitting at a keyboard.” In contemporary infrastructure, a local execution context may belong to a build job, a containerized workload, a plugin, a compromised service account, or a developer toolchain.
The interesting question is not whether the bug is remotely exploitable in the classical sense. The interesting question is who can load or attach the relevant BPF program on your systems. That answer varies dramatically by distribution, kernel configuration, sysctl policy, container runtime settings, capabilities, and security posture.
Many hardened systems already restrict unprivileged BPF. Some environments require capabilities such as CAP_BPF, CAP_PERFMON, or CAP_SYS_ADMIN for sensitive BPF operations. Others have legacy settings or developer-friendly configurations that make experimentation easier. The practical exposure is therefore less about the CVE name and more about your BPF access model.
The Availability Impact Is the Point, Not a Consolation Prize
Security teams often rank confidentiality and integrity above availability because stolen data and unauthorized modification are easier to explain to executives. Kernel availability bugs resist that neat hierarchy. If a local actor can reliably trigger a kernel splat or panic-like failure mode, the business consequence may be downtime, noisy nodes, evicted workloads, failed builds, or reduced trust in a shared platform.The NVD vector gives availability a high impact while leaving confidentiality and integrity untouched. That is an honest description of this bug’s shape. The attacker is not reading secrets through this path, and the fix does not describe arbitrary write primitives or privilege escalation.
But “only availability” can still be expensive. On a Kubernetes node, a kernel-level availability failure does not politely affect one pod. On a developer workstation, it can cost unsaved work and corrupt state. On a CI runner, it can turn into flaky infrastructure that teams waste hours diagnosing as an application problem.
Kernel availability failures also carry a psychological cost for operations teams. A user-space service crash is annoying. A kernel complaint involving atomic context, RCU nesting, and BPF helpers is the kind of event that makes administrators wonder what else is lurking below the waterline.
Microsoft’s Appearance in the Story Is About Linux, Not Windows Panic
The user-facing source here is Microsoft’s Security Response Center entry, but the vulnerability itself is a Linux kernel CVE sourced from kernel.org. That distinction is important for a WindowsForum audience because it separates Windows risk from Linux-in-Microsoft-ecosystem risk.Microsoft ships and supports Linux in several ways. WSL 2 uses a real Linux kernel inside a lightweight virtual machine. Azure customers run countless Linux VMs. Microsoft maintains Linux-related components and publishes vulnerability guidance for customers who manage mixed estates. Seeing a Linux kernel CVE in an MSRC context does not mean the Windows kernel suddenly inherited a BPF flaw.
For ordinary Windows users who do not run WSL 2, Linux virtual machines, containers, or Linux hosts, CVE-2026-43010 is not a Windows desktop emergency. For power users and administrators who do run WSL 2, Docker Desktop backends, Linux dev environments, Azure Linux workloads, or security tooling that relies on BPF, it belongs on the patch radar.
The Windows angle is therefore not “Windows is vulnerable.” It is that Windows environments increasingly include Linux kernels as first-class operational components. The boundary between Windows administration and Linux kernel hygiene is thinner than it used to be.
WSL Makes Kernel Servicing Visible to Windows People
WSL 2 changed the mental model for Windows users by putting a full Linux kernel behind a familiar command-line experience. That design is a triumph of usability, but it also means kernel servicing is now part of the Windows developer story.Microsoft’s WSL documentation describes a separate Linux kernel update path and notes that WSL 2’s kernel is serviced apart from the Windows image. In practice, many users never think about this distinction because WSL feels like a feature rather than a VM-like Linux environment. CVEs like this make the abstraction leak in useful ways.
If a WSL 2 kernel line includes the vulnerable code and exposes the relevant BPF functionality, the remediation path is not to uninstall Windows updates randomly or hunt through Ubuntu packages alone. The relevant component is the kernel WSL is actually running. Checking
uname -r inside WSL and making sure WSL itself is updated is more useful than staring at the Windows build number in isolation.That does not mean every WSL user is at meaningful risk. BPF capabilities, kernel configuration, Microsoft’s WSL kernel branch, and local privilege boundaries all affect exploitability. But it does mean Windows developers should stop treating the Linux kernel inside WSL as invisible plumbing.
The Version List Is Messy Because Kernel Reality Is Messy
The NVD configuration data for CVE-2026-43010 lists Linux kernel 7.0 release candidates and ranges covering 6.19 and 5.18-era branches up to fixed releases. As with many kernel CVEs, the affected-version story should be read carefully rather than mechanically.Mainline, stable, long-term, vendor, cloud, and distribution kernels do not move in lockstep. A fix can land upstream, then appear in stable branches, then be backported by distributions into kernels whose version numbers do not obviously match the upstream range. Enterprise distributions may carry patches without changing the base kernel version in the way a casual
uname reader expects.That is why kernel CVE management often frustrates teams that rely only on raw version comparison. A server running a “5.15” or “6.1” branded kernel may contain hundreds or thousands of backported fixes. Conversely, a custom-built or fast-moving kernel can sit closer to upstream and require more direct attention to stable patch levels.
The safest operational answer is vendor-specific. For Ubuntu, Red Hat, SUSE, Debian, Microsoft, cloud-provider kernels, and appliance kernels, administrators should follow the vendor advisory and package status rather than improvising from NVD CPE strings alone.
The Patch Teaches Better BPF Hygiene Than the CVE Score Does
The patch message says the important thing plainly: kprobe.multi programs run in atomic/RCU context and cannot sleep. The attach path now rejects sleepable programs before further processing. That is both the fix and the engineering philosophy.Attach-time rejection is better than relying on a later failure. It makes the invalid configuration impossible, or at least much harder to reach. It also gives developers clearer feedback: the program does not belong at that hook point.
That is how kernel security should age. Not every fix needs to be a dramatic mitigation or a sprawling rewrite. Sometimes the durable answer is to make the kernel say “no” earlier, closer to the user’s request, before the system has constructed a dangerous state.
For BPF developers, this is a signal to test attachment compatibility as deliberately as verifier compatibility. Passing the verifier is not the same as being valid for every hook. Helper availability, sleepability, execution context, and attach type are part of the contract.
Observability Agents Sit Closest to the Fault Line
The most likely legitimate users of the affected BPF paths are not random desktop applications. They are tools that instrument kernel behavior: profilers, tracers, security agents, performance monitors, and debugging frameworks. That is where administrators should start their mental inventory.If an organization deploys BPF-heavy tooling across fleets, CVE-2026-43010 deserves a look even if no hostile user is present. A tool bug, misconfiguration, experimental probe, or incompatible agent version could trip the same kernel warning path that an attacker would abuse deliberately.
This is a recurring pattern in security infrastructure. The agent installed to improve visibility often holds privileges and kernel touchpoints ordinary software never receives. That does not make such agents bad; it makes their compatibility matrix part of the risk surface.
Administrators should ask vendors whether their BPF programs use kprobe.multi and whether they request sleepable mode. Good vendors should be able to answer. Better vendors should already be testing against kernels with the fix, because the correct behavior after patching is rejection rather than mysterious kernel noise.
Containers Complicate the Meaning of “Local”
Container platforms turn “local attacker” into a policy question. A container process is local to the kernel. Whether it can perform sensitive BPF operations depends on capabilities, seccomp, LSM policy, runtime configuration, and the choices made by platform administrators.In well-hardened clusters, untrusted workloads should not be able to load arbitrary BPF programs. In real clusters, exceptions exist. Privileged containers, node agents, CNI components, observability DaemonSets, and debugging pods often receive elevated access for practical reasons. Those exceptions are where kernel bugs become cluster reliability issues.
The right response is not to rip out every BPF-based tool. That would be self-defeating. The right response is to narrow who can attach BPF programs, audit privileged workloads, and treat node kernel updates as part of application-platform maintenance rather than a separate dark art.
CVE-2026-43010 is especially useful as a policy review prompt because its exploit preconditions are not exotic. If an entity can attach the wrong kind of BPF program, the kernel must enforce the boundary. If your platform allows too many entities to try, you have a broader governance problem.
Developers Will See This as an Error, Operators Will See It as a Save
After patched kernels reject sleepable kprobe.multi programs at attach time, some developers may experience failures where previously a program attached successfully. That is not a regression in the meaningful sense. It is the kernel refusing an invalid program before it can produce worse behavior.This distinction matters for support desks and platform teams. A developer may report that a tracing tool stopped working after a kernel update. The temptation will be to blame the patch and seek a workaround. The correct interpretation is more likely that the tool was relying on a combination the kernel should not have accepted.
Healthy tooling should adapt by choosing a compatible hook, avoiding sleepable helpers in non-sleepable context, or restructuring the probe. A kernel that rejects invalid attachment is easier to reason about than one that accepts it and later emits frightening scheduler complaints under load.
There is a broader cultural lesson here. Security fixes often expose latent bugs in tools that were skating along undefined or under-enforced behavior. The resulting breakage is real, but it should be treated as forced correctness rather than arbitrary vendor hostility.
The CVE Database Is Useful, but It Is Not the Whole Story
NVD’s role is to normalize vulnerability data, attach severity, and map affected software. For CVE-2026-43010, it provides the publication date, last-modified date, CVSS vector, weakness placeholder, affected CPE ranges, and kernel.org patch references. That is valuable scaffolding.But NVD entries for kernel CVEs are often rough at the edges, especially early in their lifecycle. The weakness field may say insufficient information. CPE mapping may lag or overgeneralize. Version ranges may not reflect every vendor backport or downstream patch.
That is not a reason to ignore NVD. It is a reason to avoid treating it as a substitute for kernel stable notes, distribution advisories, and vendor patch status. CVE triage is strongest when NVD is the index, not the judge and jury.
The MSRC entry adds visibility for Microsoft customers, but it does not change the underlying technical ownership. This is a Linux kernel issue resolved in the Linux kernel. Microsoft’s relevance is in the environments where Microsoft delivers, hosts, documents, or supports Linux components.
The Practical Risk Hides in Who Can Load BPF
For administrators, the most important question is not whether CVE-2026-43010 sounds scary. It is whether untrusted or semi-trusted users can attach BPF programs on systems you care about.Linux distributions and kernels have evolved their controls around unprivileged BPF because BPF has repeatedly proven both useful and security-sensitive. Some systems disable unprivileged BPF entirely. Others gate features behind capabilities. Some development environments loosen restrictions because engineers need tracing tools to work.
That variability means fleet owners need facts rather than assumptions. On a hardened production host, the vulnerable code path may be reachable only by root-equivalent actors or trusted agents. On a shared lab machine or permissive dev server, the reachable population may be larger.
This is where local availability bugs become governance tests. If every developer, build job, or container can exercise complex kernel instrumentation features, CVE-2026-43010 is only one example of a larger exposure. The long-term mitigation is not just patching this bug; it is defining who gets to ask the kernel these questions.
Patch Timing Should Follow Exposure, Not Headline Drama
Because this is a medium CVSS local availability issue, it should not automatically outrank actively exploited remote flaws, internet-facing authentication bypasses, or privilege escalations in core identity infrastructure. Patch management is triage, not theater.But it should move faster in environments that rely heavily on BPF, permit shared local access, run multi-tenant Linux workloads, or use privileged observability and security agents. It should also move quickly on systems where kernel crashes or node instability carry high operational cost.
For home Linux users and Windows users with occasional WSL sessions, the practical advice is boring and correct: take normal kernel updates, update WSL, and avoid running random privileged tracing tools from the internet. For enterprise administrators, the advice is to align the fix with the next kernel maintenance window unless exposure analysis says it needs to jump the queue.
Live patching may or may not be available depending on vendor support and kernel branch. Where it is not, reboot planning remains the unglamorous heart of kernel security. A kernel fix that is installed but not booted is an artifact, not protection.
BPF’s Security Model Is Becoming a Product Dependency
One reason this CVE deserves more than a database blurb is that BPF has become a product dependency for companies that do not market themselves as kernel companies. Cloud security platforms, performance vendors, endpoint tools, developer observability services, and network stacks build on it.That creates a dependency chain many customers do not fully see. A SaaS-branded agent running on your node may depend on BPF program types, helpers, verifier behavior, kernel configuration, and attach semantics. A kernel patch that tightens those semantics can change the agent’s behavior overnight.
The better vendors will treat this as routine. They will test across stable kernels, detect unsupported attachment modes, fail gracefully, and document required capabilities. The weaker vendors will ask customers to loosen kernel controls, run privileged containers, or pin older kernels.
CVE-2026-43010 is another small vote for choosing vendors that understand the kernel surface they consume. BPF is not just an API. It is a negotiated privilege boundary with the operating system.
The Small Attach-Time Check That Should Guide Your Response
The practical response to CVE-2026-43010 is compact, but it should be deliberate. This is not a vulnerability that rewards panic; it rewards inventory.- Administrators should identify Linux systems, WSL 2 environments, and container nodes running kernels or vendor kernel builds that include the affected BPF attach behavior.
- Teams should prioritize patching where untrusted users, CI jobs, privileged containers, or third-party agents can load or attach BPF programs.
- Windows users should treat this as relevant mainly when they run WSL 2, Linux VMs, Docker-backed Linux workloads, or Azure-hosted Linux systems, not as a native Windows kernel flaw.
- BPF-based tooling that breaks after the fix should be treated as relying on an invalid attachment combination until proven otherwise.
- Version checks should be tied to vendor advisories and backport status rather than raw upstream kernel numbers alone.
- Kernel updates should be completed with the required reboot or live-patch confirmation, because an installed package does not protect a running old kernel.
CVE-2026-43010 will not be remembered as the kernel bug that changed the industry, and that is precisely why it is useful. It shows how modern infrastructure risk often arrives as a small missing validation check in a powerful subsystem that everyone else has quietly learned to depend on. The future of BPF will be more enforcement, more explicit attach-time rules, and more friction for tools that relied on permissive behavior; administrators should welcome that direction, because the alternative is discovering context violations only after the kernel starts shouting.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center