CVE-2026-23327 is one of those kernel security bugs that looks small at first glance and then turns out to be a revealing case study in how modern driver code fails. The issue sits in the Linux CXL mailbox path, where the
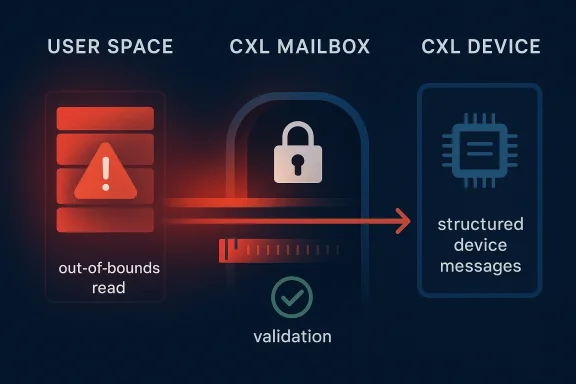
The vulnerability d classic mistake in low-level parsing logic: the code trusts a payload format before proving that the buffer is large enough. In kernel terms, this is the sort of bug that can lead to out-of-bounds reads, information disclosure, or crashes depending on exactly how the malformed message is shaped and what surrounding memory looks like. Even when the immediate impact is “only” a read-side defect, the security significance is real because kernel memory is not ordinary application memory.
There is also a larger architectural sto not assigning CVEs to CXL code in a vacuum; it is doing so as CXL becomes relevant to the same class of servers, memory expansion systems, and composable infrastructure that enterprises increasingly want to manage at scale. Recent CXL work in the ecosystem shows how quickly the technology is being operationalized, including public discussion of CXL memory expansion in cloud environments and next-generation memory platforms. That momentum helps explain why a payload-validation flaw in a CXL driver deserves attention now rather than later.
For security teams, this kind of issue is particularly important because driver and mailbox bugs often sit below the visibility threshold of routine application security scanning. You do not discover them by testing web forms or checking package manifests. You discover them by watching the kernel’s trust boundary between user space, message tsemantics. That makes the fix surface small, but the operational lesson large.
At its core, CVE-2026-23327 is about input validation in the CXL mailbox subsystem. The helper named in the advisory,
That sounds pedestrian, but it is a surprisingly common kernel pattern: a buffer arrives, code peeks at a field inside it, and only later does a size check confirm the assumption. The danger is not hypothetical. If the payload is shorter than expected, the kernel may read beyond the valid portion of the message, and in a mailbox path that can mean spilling structured device or kernel data into places it should not go. The patch’s title tells us the maintainer emphasis check must happen first, not after.
This is why “payload size before contents” is more than a coding style preference. It is a boundary rule. The kernel should not rely on the contents of a message to determine whether the message is safe to inspect unless the size has already established that the contents are fully present. In other words, the validator must win the race against the parser. That is especially important in code that can be exercised by device-ohe defect lives in the CXL mailbox path.
The reason this vulnerability matters is thato be written by engineers who are optimizing for correctness under protocol assumptions, not just for hostile input. That is understandable, but it is also where attackers look. A malformed message is the security equivalent of a boundary test: it asks whether the driver really knows where its payload ends and where undefined behavior begins.
There is also a subtle engineering pressure here: driver developers often try to reducee fast path compact. That makes sense for performance, but it can lead to validation being deferred until after some initial parsing has already happened. In a control path, that tradeoff is dangerous. The safe choice is to make the size check boring, explicit, and early. Boring is good in security-critical parsing.
CXL is newer than most kethat does not buy it immunity. New subsystems often have to move fast while the standards and implementation details are still evolving. As the ecosystem grows, code that was once written for controlled environments starts encountering more diverse hardware, more vendor behavior, and more aggressive operational use. That is the moment when edge cases stop being edge cases.
The less obvious risk is that a malformed payload can desynchronize assumptions within the mailbox path. Once code has peeked at invalid contents, later control flow may proceed as though the payload had already been vetted. In kernel code, a bad assumption made early can ripple far beyond the immediatey early validation is not just about preventing one bad dereference; it is about preserving the integrity of the entire path.
This is also where CXL’s future importance becomes a security problem. As operators use CXL for memory expansion and composable infrastructure, the sensitivity of mailbox defects rises. The same code path that once handled limited management traffic may now be part of platforms that carry critical data and high-value workloads. Context changes severity.
The second group is OEMs and system integrators who ship platforms with CXL features enabled in firmware or kernel configurations. If the affected code is present in their downstream tree, they need to know whether the fix has been backported, whether the vulnerablein shipped builds, and whether any vendor-specific wrappers alter the risk profile. In practice, that means version numbers alone are not enough.
There is also a procurement implication. Organizations investing in CXL-capable systems should ask more pointed questions about kernel support maturity, vendor patch cadence, and how mailbox-path fixes are validated across stable branches. Hardware innovation does not end with the silicon launch; it continues in firmware, kernel integration, and security response.
Microsoft’s publication of the CVE through the Security Update Guide reinforces the idea that security transparency is part of the market story. When a company is pushing new infrastructure capabilities, the credibility of its vulnerability handling matters almost as much as the features themselves. Buyers increasingly want to know not just whether the hardware works, but whether the management stack can withstand messy real-world input.
The same is true for cloud operators evaluating CXL-backed services. If the industry wants customers to trust disaggregated memory and composable infrastructure, the kernel security story has to be as disciplined as the hardware roadmap. That means strong validation, stable support, and clear advisories when the inevitable defects appear.
It also provides an opportunity for maintainers and vendors to strengthen adjacent code paths. Bugs like this are often a cue to re-audit nearby mailbox handlers, message decoders, and protocol helpers. If one parser made an ordering mistake, neighboring code may be following disciplined review now could prevent the next CVE later.
Another concern is visibility. Many organizations will not know whether they are affected unless they have accurate inventories of kernel branches, vendor backports, and CXL feature usage. That makes remediation harder than it should be, especially in large fleets where teams who own the hardware may not be the same teams who own the kernel patch cadence. That gap is where vulnerabilities linger.
-entories can delay remediation.
The broader question is whether this CVE nudges maintainers to audit the rest of the CXL memore aggressively. That would be the right outcome. Emerging infrastructure layers are most secure when the industry treats early defects as prompts for structural hardening rather than isolated cleanup chores. A single fixed bug should trigger a wider review, not a sigh of relief.
Source: MSRC Security Update Guide - Microsoft Security Response Center
cxl_payload_from_user_allowed() helper can reach into message contents before it has confirmed that the payload is actually large enough to be safe. The fix is conceptually simple — validate the payload size before inspecting the body — but the broader implication is more important: CXL is moving quickly from niche interconnect to mainstream infrastructure, and that means even “just a bounds check” now matters to cloud operators, OEMs, and enterprise buyers. The upstream patch title, surfaced through Linux stable, is explicit about the remedy: “validate payload size before accessing contents.” e Express Link, or CXL, is not an abstract research project anymore. It is a memory-and-coherency fabric that is increasingly tied to server design, accelerator attachment, and memory pooling strategies in high-end systems. That matters because every new control surface in the kernel becomes a potential attack surface, especially when the code is handling structured device messages from hardware that may not always behave ideally. The CXL mailbox layer is precisely such a surface, mediating requests and responses between software and CXL devices.The vulnerability d classic mistake in low-level parsing logic: the code trusts a payload format before proving that the buffer is large enough. In kernel terms, this is the sort of bug that can lead to out-of-bounds reads, information disclosure, or crashes depending on exactly how the malformed message is shaped and what surrounding memory looks like. Even when the immediate impact is “only” a read-side defect, the security significance is real because kernel memory is not ordinary application memory.
There is also a larger architectural sto not assigning CVEs to CXL code in a vacuum; it is doing so as CXL becomes relevant to the same class of servers, memory expansion systems, and composable infrastructure that enterprises increasingly want to manage at scale. Recent CXL work in the ecosystem shows how quickly the technology is being operationalized, including public discussion of CXL memory expansion in cloud environments and next-generation memory platforms. That momentum helps explain why a payload-validation flaw in a CXL driver deserves attention now rather than later.
For security teams, this kind of issue is particularly important because driver and mailbox bugs often sit below the visibility threshold of routine application security scanning. You do not discover them by testing web forms or checking package manifests. You discover them by watching the kernel’s trust boundary between user space, message tsemantics. That makes the fix surface small, but the operational lesson large.
 What CVE-2026-23327 Actually Targets
What CVE-2026-23327 Actually Targets
At its core, CVE-2026-23327 is about input validation in the CXL mailbox subsystem. The helper named in the advisory, cxl_payload_from_user_allowed(), is the point where a CXL message is being examined to determine whether a user-originated payload is acceptable. The problem is that the code can access contents before ig that the payload is long enough to contain them safely.That sounds pedestrian, but it is a surprisingly common kernel pattern: a buffer arrives, code peeks at a field inside it, and only later does a size check confirm the assumption. The danger is not hypothetical. If the payload is shorter than expected, the kernel may read beyond the valid portion of the message, and in a mailbox path that can mean spilling structured device or kernel data into places it should not go. The patch’s title tells us the maintainer emphasis check must happen first, not after.
Why mailbox code is a sensitive boundary
CXL mailbox code is not generic parsing glue. It is part of the control plane for hardware management, which means malformed requests can influence how the kernel interprets device state. When the kernel is deciding whether to accept a payload, it is effectively enforcing the protocol contract between software and the device. If that contract is checked too late, the entire security assumptin it should be.This is why “payload size before contents” is more than a coding style preference. It is a boundary rule. The kernel should not rely on the contents of a message to determine whether the message is safe to inspect unless the size has already established that the contents are fully present. In other words, the validator must win the race against the parser. That is especially important in code that can be exercised by device-ohe defect lives in the CXL mailbox path.
- The named helper is
cxl_payload_from_user_allowed(). - The bug is a size-validation ordering problem.
- The fix is to check payload length before dereferencing contents.
- The likely risk class is out-of-bounds read or related memory-safety fallout.
n if exploitation is not obvious
A lot of kernel bugs are not immediately labeled “remote code execution” or “privilege escalation,” and this one appears to be in the more subtle category. That does not make it unimportant. In kernel land, an information disclosure can still help an attacker defeat mitigations, map memory layout, or prepare a second-stage exploit chain. That is why precise bounds checking matters even in subsystems that do not look especially glamorous.The CXL Mailbox
The CXL mailbox is where software asks hardware questions and receives structured answers. That is a deceptively simple description for a layer that must simultaneously understand protocol semantics, device state, message framing, and validation logic. Once a platform starts depending on CXL for memory expansion, pooling, or composability, the mailbox becomes part of the operational nervous system.The reason this vulnerability matters is thato be written by engineers who are optimizing for correctness under protocol assumptions, not just for hostile input. That is understandable, but it is also where attackers look. A malformed message is the security equivalent of a boundary test: it asks whether the driver really knows where its payload ends and where undefined behavior begins.
Why ordering bugs are easy to miss
Ordering flaws are sneaky n looks like it validates something. A reader scanning the function name may assume thatcxl_payload_from_user_allowed() is the gatekeeper and therefore safe by definition. But if the routine inspects data before it has checked the length, the gatekeeper becomes part of the problem. That kind of false confidence is exactly why security review has to look at control flow, not just function names.There is also a subtle engineering pressure here: driver developers often try to reducee fast path compact. That makes sense for performance, but it can lead to validation being deferred until after some initial parsing has already happened. In a control path, that tradeoff is dangerous. The safe choice is to make the size check boring, explicit, and early. Boring is good in security-critical parsing.
- Mailbox parsing is a control-plane task, not just a data-copy task.
- CXL messages may arrive from hars the kernel should not trust blindly.
- Small ordering mistakes can become security boundary failures.
- Validation should happen at the earliest possible point.
- Performance concerns should not outrank memory safety in parser code.
Device code is now enterprise code
The strategic significance of CXL is that it is moving from “interesting hardware featureastructure primitive.” That evolution tends to pull kernel bugs into the spotlight because the blast radius widens. A defect that might have affected only a small class of experimental systems five years ago now touches the kind of platforms that are expected to carry production workloads, including memory-hungry analytics and AI-adjacent deployments.Historical Context: Why This Bug Class Keeps Appearing
This vulnerability sits in a very old category of software flaw: check after use instead of before use. Kernel developers have fought this class of issue for decades across networking, filesystems, device drivers, and protocol stacks. The reason it keeps coming back is simple: low-level code is full of compact assumptions, and compact assumptions are where input validation mistakes breed.CXL is newer than most kethat does not buy it immunity. New subsystems often have to move fast while the standards and implementation details are still evolving. As the ecosystem grows, code that was once written for controlled environments starts encountering more diverse hardware, more vendor behavior, and more aggressive operational use. That is the moment when edge cases stop being edge cases.
The pattern repeats across emerging hardwaen this movie before with other layers of the kernel. The first generation of bugs usually comes from assuming that protocol peers behave perfectly. The second generation comes from trying to optimize or simplify the code without rethinking the trust boundary. The third comes when the subsystem gets deployed at scale and malformed inputs become routine adversarial tests rather than theoretical ones. CXL appears to be entering that second and third phase at once.
The fact that Linux stable picked this up is another sign that the bug is not being treated as an academic cleanup item. Stable-tree inclusion usually means maintainers want the fix propagated broadly and consistently, not left to vendor discretion alone. When a validation bug appears ine message is clear: this is a real hardening issue, not a stylistic nit.- New hardware features do not eliminate old vulnerability classes.
- Emerging subsystems often have thinner margins for error.
- Wider deployment tends to uncover assumptions that never got stress-tested.
- Stable backports usually indicate the issue is operationally relevant.
- The kernel’s tr, not easier, as hardware becomes more composable.
Why this matters to Microsoft customers
Microsoft’s decision to track this as a CVE through its update guide shows that CXL security is now part of the Windows ecosystem conversation, even when the vulnerable code lives in kernel-originated infrastructure rather than in a Windows UI surface. That is consistent with the broader reality of modern enterprise platforms: the management plane for advanced hardware is as important as the visible OS shell.Technical Risk: What Could Go Wrong
The obvious risk is an out-of-bounds read. If the kernel attempts to inspect fields in a payload that is shorter than expected, it may access memory beyond the valid bounds of the message bhat sits adjacent to the buffer, that can expose stale data, trigger a fault, or create undefined behavior in the logic that consumes the message.The less obvious risk is that a malformed payload can desynchronize assumptions within the mailbox path. Once code has peeked at invalid contents, later control flow may proceed as though the payload had already been vetted. In kernel code, a bad assumption made early can ripple far beyond the immediatey early validation is not just about preventing one bad dereference; it is about preserving the integrity of the entire path.
Information disclosure is never trivial in kernel space
Even if the flaw only leaks a small amount of data, kernel memory disclosure can be valuable to an attacker. It may reveal addresses, structure contents, or timing-sensitive state. On hardened systems, small leaks can become the glue that makes a larger exploit is why the right response to a bounds bug is not “the leak seems tiny,” but “the trust boundary failed.”This is also where CXL’s future importance becomes a security problem. As operators use CXL for memory expansion and composable infrastructure, the sensitivity of mailbox defects rises. The same code path that once handled limited management traffic may now be part of platforms that carry critical data and high-value workloads. Context changes severity.
- Potential impact includes out-of-bounds read behavior.
- Kernel memory disclon attacks.
- Faulting on malformed input can reduce system reliability.
- Misparsed mailbox data can distort management decisions.
- The more widely CXL is deployed, the larger the practical exposure becomes.
Why this is a hardening win, not just a bug fix
Patches like this do more than remove one defect. They force the subsystem to honor a stricter contract about input shape and parsing order. That matters because kernel hardening iclosing off the small, adjacent cracks that attackers can chain together. The best kernel fixes often look unexciting because they simply make the obvious invariant impossible to violate.Enterprise Impact: Who Should Care First
The first group that should pay attention is anyone operating systems with CXL-capable servers or planning to adopt memory expansion and composable infrastructure. These organizations are the ones most likely to encounn a meaningful way. They also tend to run the workloads where even low-probability kernel bugs get treated seriously because the business cost of instability is high.The second group is OEMs and system integrators who ship platforms with CXL features enabled in firmware or kernel configurations. If the affected code is present in their downstream tree, they need to know whether the fix has been backported, whether the vulnerablein shipped builds, and whether any vendor-specific wrappers alter the risk profile. In practice, that means version numbers alone are not enough.
Enterprise versus consumer exposure
For consumer Windows users, this is unlikely to be an immediate day-to-day concern because the issue is rooted in Linux kernel CXL code rather than a mainstream desktop application path. For enterprise users, the situation is different. Any environment that consumes kernel-driven CXL functionality in data-center hardware has to treat the advisory as parthing discipline. That distinction matters because the same CVE can be low visibility and high importance at the same time.There is also a procurement implication. Organizations investing in CXL-capable systems should ask more pointed questions about kernel support maturity, vendor patch cadence, and how mailbox-path fixes are validated across stable branches. Hardware innovation does not end with the silicon launch; it continues in firmware, kernel integration, and security response.
- Data-center operators should map CXL ex.
- OEMs should verify downstream backports, not just upstream commits.
- Buyers should ask how mailbox and parser paths are tested.
- Security teams should include CXL in kernel risk reviews.
- Procurement should consider patch cadence as part of platform maturity.
The governance problem behind the technical bug
The real enterprise challenge is not only whether the bug can be exploited. It is whether the organization has enough visibility into where CXL is enabled, how the kernel is configured, and whether the vendor’s update story is fast enough for a subsystem that is still evolving. In other words, this CVE is as much about platform governance as it is about memory safety.Competitive and Market Implications
CXL is becoming a competitive battleground because it sits at the intersection of server architecture, memory economics, and AI infrastructure. Any security flaw in the kernel layer can slow adoption if customers perceive the ecosystem as immature. That does not mean one CVE derails the standard, but it does mean vendors have an incentive to prove that issues are being found and fixed quickly.Microsoft’s publication of the CVE through the Security Update Guide reinforces the idea that security transparency is part of the market story. When a company is pushing new infrastructure capabilities, the credibility of its vulnerability handling matters almost as much as the features themselves. Buyers increasingly want to know not just whether the hardware works, but whether the management stack can withstand messy real-world input.
Why rivals should watch this closely
Competitors in the CXL and advanced-memory space should not treat this as someone else’s problem. Bugs like this often influence buyer perception of subsystem readiness. If one vendor appears to surface and fix mailbox issues promptly, while another is opaque or slow to backport, that can become part of the sales conversation for enterprise platform deals. Security maturity sells.The same is true for cloud operators evaluating CXL-backed services. If the industry wants customers to trust disaggregated memory and composable infrastructure, the kernel security story has to be as disciplined as the hardware roadmap. That means strong validation, stable support, and clear advisories when the inevitable defects appear.
- Security response speed influences platform trust.
- Transparent advisories can become a competitive advantage.
- Early patching builds confidence in emerging hardware stacks.
- Opaque backporting creates procurement friction.
- Kernel hardening becomes part of product differentiation.
The wider mesThe market signal here is subtle but important: CXL is no longer being evaluated only as a performance technology. It is being evaluated as a secure, supportable, enterprise-grade subsystem. That shift raises the bar for everyone in the ecosystem, because the conversation has moved from “Can it accelerate workloads?” to “Can it be trusted in production atresslink.org](https://computeexpresslink.org/wp-c...0_2024October2_evalcopy.pdf?utm_source=openai))
Strengths and Opportunities
This CVE may be a problem, but it also highlights some encouraging signs in the Linux and CXL security process. The fix is narrow, understandable, and directly aligned with the defect: validate the payload before touching its contents. That kind of surgical correction is exo see in a mature kernel subsystem, because it reduces the chance of collateral damage while closing the actual flaw.It also provides an opportunity for maintainers and vendors to strengthen adjacent code paths. Bugs like this are often a cue to re-audit nearby mailbox handlers, message decoders, and protocol helpers. If one parser made an ordering mistake, neighboring code may be following disciplined review now could prevent the next CVE later.
- Minimal fix surface means lower regression risk.
- Clear validation rule makes the patch easy to reason about.
- Stable-tree adoption can improve fleet-wide consistency.
- Audit opportunity exists across adjacent CXL mailbox handlers.
- Enterprise hardening can benefit from a broader parser review.
- Vendor transparency around CXL fixes mat.
- Security education can reinforce safer kernel parsing patterns.
A good sign for maintainability
One strength of this kind of patch is that it teaches future readers what the invariant should be. When fixes are compact and obvious, they become part of the subsystem’s institutional memory. That is valuable in a fast-moving area like CXL, where maintainers will be balancing feature growths, and security hardening at the same time.Risks and Concerns
The biggest concern is that CXL security will increasingly be exposed to the same pressures that have long plagued networking and storage subsystems: fast evolution, heterogeneous hardware, and a steady stream of edge cases. A mailbox validation bug today may be a one-off; tomorrow it could be one example of a pattern. The risk ist the normalization of bugs of this shape.Another concern is visibility. Many organizations will not know whether they are affected unless they have accurate inventories of kernel branches, vendor backports, and CXL feature usage. That makes remediation harder than it should be, especially in large fleets where teams who own the hardware may not be the same teams who own the kernel patch cadence. That gap is where vulnerabilities linger.
-entories can delay remediation.
- Vendor backports may differ from mainline versions.
- CXL exposure may be hidden inside broader server configurations.
- Similar validation bugs may exist in adjacent code.
- Feature growth can outpace security review.
- Operational teams may underestimate low-severity-looking CVEs.
- Dependence on emerging hardware can complicate patch planning.
Why “just a read” still deserves attention
A read-side defect can be easy to dismiss because it do dramatic as a write primitive. That is a mistake. Kernel reads can leak just enough information to be valuable, and in a composable hardware stack, information about message structure, state, or memory layout can be surprisingly sensitive. The safer response is to treat the trust boundary as broken and patch accordingly.Looking Ahead
The immediate question is whether downstream Linuy folded the fix into their CXL-enabled kernel branches. Stable-tree publication is helpful, but enterprise reality depends on how quickly distributions and OEMs translate the patch into consumable updates. In a fast-moving hardware ecosystem, the timeline from upstream fix to broadly deployed remediation is often the difference between a theoretical issue and a practical exposure window.The broader question is whether this CVE nudges maintainers to audit the rest of the CXL memore aggressively. That would be the right outcome. Emerging infrastructure layers are most secure when the industry treats early defects as prompts for structural hardening rather than isolated cleanup chores. A single fixed bug should trigger a wider review, not a sigh of relief.
What to watch next
- Whether major Linux vendors backport the fix into their enterprise kernels quickly.
- Whether related CXL mailbox helpers receive follow-on validation patches.
- Whether security advisories begin to frame CXL bugs as a broader class rather than isolated exceptions.
- Whether OEM firmware and kernel bundles document CXL security posture more clearly.
- Whether additional findings appear as CXL deployments expand in data-center environments.
The strategic takeaway
CVE-2026-23327 is not the kind of issue that will dominate headlines for weeks, but it is the kind of issue that tells you where the industry is headed. As CXL becomes more central to memory expansion and composable infrastructure, the security expectations surrounding its control paths will rise sharply. The organizations that treat this as an early warning — not a footnote — will be better prepared for the more complex kernel security stories that are surely coming next.Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: