The kernel flaw identified as CVE-2026-23346 is a narrow but important arm64 I/O mapping issue in Linux: the
This CVE sits in a class of bugs that are easy to underestimate because the function name sounds mundane.
What makes this worth attention is the architectural specificity. A bug that only manifests on arm64 tends to be dismissed by some teams as niche, but that is a mistake in modern infrastructure. Arm64 is no longer just a mobile or embedded story; it is deeply present in cloud, hyperscale, client, and appliance deployments. So even if the visible blast radius is limited to a subset of systems, the operational impact can still be broad.
The phrasing “extract user memory type” suggests the vulnerability is about deriving the wrong memory type from a user-influenced input or state, then feeding that value into a mapping routine that expects the right attribute classification. That is the kind of bug that may not produce immediate crashes in every case. Instead, it can create mis-mapped pages, stale assumptions about cacheability or shareability, or protection mismatches that only surface under specific device, driver, or workload combinations.
There is also a bigger lesson here: kernel memory attribute bugs are frequently semantic bugs before they become obvious failures. They are not always dramatic buffer overflows. Sometimes they are quieter, more architectural mistakes that undermine the guarantees the rest of the system assumes are already true. That makes them harder to notice, harder to fuzz, and often harder to reason about during incident response.
The function name in the CVE title matters.
This kind of issue also fits a long-running pattern in kernel hardening work: the more precisely an architecture defines its memory behavior, the more important it becomes for helper functions to preserve those semantics faithfully. A bug that might be harmless on a more permissive architecture can become meaningful on arm64 because the platform’s rules are both stricter and more expressive. That is why a bug title that looks small can still justify a CVE.
Microsoft’s Security Update Guide often tracks Linux and open-source kernel vulnerabilities because enterprise environments are hybrid by default now. Even if a bug is not a Windows code issue, it can still matter to fleets managed from Microsoft-oriented security tooling, especially where virtualization, containers, or mixed OS infrastructure are involved. In that sense, Microsoft’s publication is a triage signal, not a claim of platform ownership.
A final point of context: mapping bugs are frequently evaluated less by raw exploitability and more by what they can destabilize. An incorrect memory type might lead to data corruption, improper cache behavior, or broken device interactions rather than a clean privilege escalation path. That does not make it benign. It makes it the sort of issue that belongs in the same remediation queue as other kernel correctness defects that can undermine system trust.
The danger is amplified by the fact that this is a kernel-internal decision point. Once the kernel commits to a mapping type, drivers and user workloads generally assume the mapping is trustworthy. That means a single bad inference in
At minimum, that means reliability risk. In worse cases, incorrect attribute handling can open the door to state corruption, data visibility issues, or platform-specific crashes that are hard to reproduce. Those are the bugs that make fleet operators nervous because they evade easy reproduction while still affecting the trustworthiness of the system.
Key implications of this class of bug:
The phrase user memory type hints that the bug may arise when the kernel tries to infer or translate the memory type from user-controlled or user-originated metadata. That is especially sensitive because the kernel generally treats attribute derivation as trusted logic. If the derivation is wrong, the resulting mapping could be exposed with the wrong semantics, and the failure may only appear in edge cases involving certain devices or memory regions.
That is why architecture-specific CVEs often matter even when they do not immediately read like exploitation bugs. They are about trust boundaries inside the kernel itself. The helper is supposed to preserve the boundary between intent and implementation; if it gets that boundary wrong, the rest of the stack inherits the error.
If the bug causes a user memory type to be extracted incorrectly, then the kernel may create a mapping that does not match the intended access model. That can surface as device misbehavior, unexpected faults, or inconsistent results in software that relies on precise memory semantics. For enterprise teams, that matters because low-level instability can look like unrelated application failure, making root cause analysis slower and more expensive.
There is also a compliance angle. A vulnerability tied to kernel mapping correctness can affect certification posture, especially if it touches device isolation or memory handling guarantees. Even when no exploit is known, security teams often treat these defects as high-priority due to the potential for downstream instability and the difficulty of proving that no sensitive workload is exposed.
Operationally, this is the kind of issue that deserves targeted verification:
The significance of
That combination creates a familiar pattern:
This is also one of those vulnerabilities where patch urgency should be based on exposure, not just headline severity. If your environment includes arm64 servers, appliances, or cloud instances with specialized I/O drivers, the issue deserves prompt review. If you are running a fleet that does not use the relevant code path, the operational priority may be lower—but it should still be tracked.
For enterprises, the best practice is to align patch timing with kernel vendor cadence while validating that the fixed build actually contains the relevant arm64 change. Vendor packaging can be confusing, and the same kernel version number does not always mean the same backport set. That is why build-specific confirmation matters more than generic version comparisons.
There is also a subtle competitive dimension. Memory-model bugs on arm64 affect cloud and infrastructure vendors that depend on kernel correctness for performance and isolation. When a platform-level helper like
The broader lesson is that platform boundaries have become operational, not technical. A Linux kernel bug can still be a Microsoft-tracked issue if it affects customers whose security posture depends on Microsoft’s advisory ecosystem. That is an important shift in how modern infrastructure risk is communicated.
It also creates an opportunity for better auditing. Bugs in mapping helpers often point to nearby code that has made similar assumptions, so this CVE can serve as a trigger for broader review of arm64 I/O mapping logic. That kind of follow-on hardening is often the real win.
Another concern is patch lag. Arm64 Linux is everywhere now, but not every deployment moves at the same speed, especially in appliances, embedded systems, or vendor-customized kernels. A bug like this can stay alive much longer than its short description suggests.
It is also worth watching for related arm64 memory-type corrections. When a bug appears in a helper as central as
The larger takeaway is simple: modern kernel security is often about preserving the meaning of low-level abstractions. When a helper like
Source: MSRC Security Update Guide - Microsoft Security Response Center
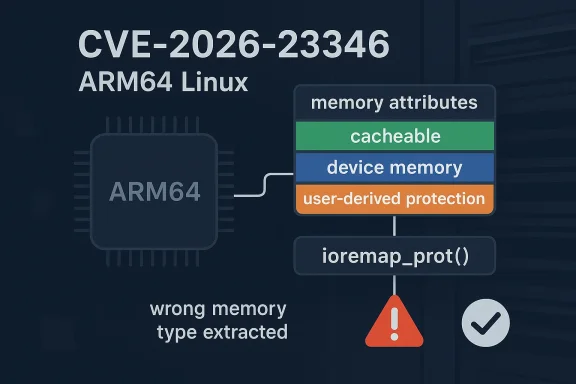
ioremap_prot() path can extract the wrong user memory type, which can lead to incorrect memory attribute selection when the kernel maps regions with user-derived protection semantics. In practical terms, that sort of bug lives at the intersection of page attributes, device memory behavior, and architecture-specific mapping rules—exactly the kind of place where a small logic error can quietly become a stability, isolation, or hardening problem. Microsoft’s advisory title makes clear that this is not a generic Windows issue; it is a Linux kernel vulnerability tracked in the Security Update Guide for enterprise visibility and remediation planning.
 Overview
Overview
This CVE sits in a class of bugs that are easy to underestimate because the function name sounds mundane. ioremap_prot() is part of the kernel’s machinery for mapping I/O or special memory ranges into a virtual address space with specific protection attributes. On arm64, those attributes matter a great deal because the platform’s memory model is more expressive than a simple “readable/writable” switch; it distinguishes between normal cached memory, device memory, and user-visible attribute combinations that must be preserved carefully. A misread or misclassification in that path can change how the CPU treats the mapped region, and that can ripple into correctness or security issues.What makes this worth attention is the architectural specificity. A bug that only manifests on arm64 tends to be dismissed by some teams as niche, but that is a mistake in modern infrastructure. Arm64 is no longer just a mobile or embedded story; it is deeply present in cloud, hyperscale, client, and appliance deployments. So even if the visible blast radius is limited to a subset of systems, the operational impact can still be broad.
The phrasing “extract user memory type” suggests the vulnerability is about deriving the wrong memory type from a user-influenced input or state, then feeding that value into a mapping routine that expects the right attribute classification. That is the kind of bug that may not produce immediate crashes in every case. Instead, it can create mis-mapped pages, stale assumptions about cacheability or shareability, or protection mismatches that only surface under specific device, driver, or workload combinations.
There is also a bigger lesson here: kernel memory attribute bugs are frequently semantic bugs before they become obvious failures. They are not always dramatic buffer overflows. Sometimes they are quieter, more architectural mistakes that undermine the guarantees the rest of the system assumes are already true. That makes them harder to notice, harder to fuzz, and often harder to reason about during incident response.
Background
Linux kernel memory mapping on arm64 is governed by a layered set of rules. The kernel must translate a requested mapping into a page table entry that reflects the intended behavior of that memory, whether that means normal RAM, MMIO, or something else entirely. On this architecture, the distinction is not decorative; it affects caching, ordering, speculative access, and device correctness. If a kernel path accidentally assigns a mapping the wrong memory type, the system may still “work” for a while, but the behavior can be subtly wrong.The function name in the CVE title matters.
ioremap_prot() is not a general-purpose allocator. It is one of the kernel’s controlled entry points for creating mappings with protection flags. That means any mistake in how it interprets or extracts a memory type is a trusted-path problem, not a userland nuisance. If the kernel is the component making the classification mistake, the downstream driver or subsystem usually has no independent way to compensate.This kind of issue also fits a long-running pattern in kernel hardening work: the more precisely an architecture defines its memory behavior, the more important it becomes for helper functions to preserve those semantics faithfully. A bug that might be harmless on a more permissive architecture can become meaningful on arm64 because the platform’s rules are both stricter and more expressive. That is why a bug title that looks small can still justify a CVE.
Microsoft’s Security Update Guide often tracks Linux and open-source kernel vulnerabilities because enterprise environments are hybrid by default now. Even if a bug is not a Windows code issue, it can still matter to fleets managed from Microsoft-oriented security tooling, especially where virtualization, containers, or mixed OS infrastructure are involved. In that sense, Microsoft’s publication is a triage signal, not a claim of platform ownership.
A final point of context: mapping bugs are frequently evaluated less by raw exploitability and more by what they can destabilize. An incorrect memory type might lead to data corruption, improper cache behavior, or broken device interactions rather than a clean privilege escalation path. That does not make it benign. It makes it the sort of issue that belongs in the same remediation queue as other kernel correctness defects that can undermine system trust.
What the Bug Class Usually Means
When a kernel helper extracts the wrong memory type, the consequences depend on what that type feeds into. On arm64, memory attributes influence whether the CPU treats a region as cacheable, strongly ordered, device-like, or shareable. If the wrong classification gets applied, the resulting mapping can violate the expectations of the hardware or the driver using it. That can produce symptoms ranging from silent misbehavior to obvious faults.The danger is amplified by the fact that this is a kernel-internal decision point. Once the kernel commits to a mapping type, drivers and user workloads generally assume the mapping is trustworthy. That means a single bad inference in
ioremap_prot() can contaminate many later operations. In security terms, this is the kind of bug that can become a foundation for more visible problems even if it is not itself a headline-grabbing exploit primitive.Why Memory-Type Mistakes Matter
A memory-type mismatch can affect several layers at once. It can cause a mapping to be cached when it should not be, or treated as device memory when it should behave like normal memory. It can also break assumptions about ordering, which is especially dangerous in I/O paths where writes must reach hardware in the correct sequence.At minimum, that means reliability risk. In worse cases, incorrect attribute handling can open the door to state corruption, data visibility issues, or platform-specific crashes that are hard to reproduce. Those are the bugs that make fleet operators nervous because they evade easy reproduction while still affecting the trustworthiness of the system.
Key implications of this class of bug:
- Mapping correctness is part of system integrity.
- Arm64 attribute rules are stricter than many teams assume.
- Driver behavior can be indirectly affected by a kernel helper error.
- Silent misconfiguration can be more dangerous than immediate crashes.
- Security impact may appear as corruption or instability rather than RCE.
Why arm64 Is a Special Case
Arm64 is not just “another CPU architecture.” It has a distinct memory model and a different set of expectations around page attributes, device mappings, and ordering semantics. That means code paths that are architecture-aware must be carefully tuned to preserve the intended type when moving between user-visible concepts and kernel mapping APIs. A subtle bug in this space is often architecturally real even if the same code looks harmless elsewhere.The phrase user memory type hints that the bug may arise when the kernel tries to infer or translate the memory type from user-controlled or user-originated metadata. That is especially sensitive because the kernel generally treats attribute derivation as trusted logic. If the derivation is wrong, the resulting mapping could be exposed with the wrong semantics, and the failure may only appear in edge cases involving certain devices or memory regions.
Architecture and Correctness
This is one of those cases where “it compiles” tells you almost nothing. A mapping helper can be syntactically valid and still be semantically wrong for a specific architecture. On arm64, the difference between the correct and incorrect mapping type can be enough to break DMA-like interactions, confuse access ordering, or alter how a region participates in the cache hierarchy.That is why architecture-specific CVEs often matter even when they do not immediately read like exploitation bugs. They are about trust boundaries inside the kernel itself. The helper is supposed to preserve the boundary between intent and implementation; if it gets that boundary wrong, the rest of the stack inherits the error.
- Arm64 memory handling is highly attribute-sensitive.
- Page type mistakes can affect ordering and caching.
- Device-facing mappings are especially vulnerable to semantic errors.
- User-derived attributes require strict validation and translation.
- Small architecture bugs can have outsized platform impact.
Security and Operational Impact
From a security operations standpoint, the first question is not “can an attacker pop a shell with this?” but rather “what can go wrong if this is left unpatched?” With a mapping bug like this, the answer is often a mixture of stability degradation, hardware interaction problems, and edge-case data integrity failures. The exact impact depends on how the affected path is used downstream.If the bug causes a user memory type to be extracted incorrectly, then the kernel may create a mapping that does not match the intended access model. That can surface as device misbehavior, unexpected faults, or inconsistent results in software that relies on precise memory semantics. For enterprise teams, that matters because low-level instability can look like unrelated application failure, making root cause analysis slower and more expensive.
Enterprise vs Consumer Exposure
Consumer systems may never hit the vulnerable path, or they may do so only under highly specific workloads. Enterprise fleets, by contrast, are more likely to include virtualization, specialized hardware, graphics stacks, device passthrough, or custom drivers that exercise uncommon kernel mapping behavior. That means the practical risk profile is often higher in enterprise than in a typical desktop environment.There is also a compliance angle. A vulnerability tied to kernel mapping correctness can affect certification posture, especially if it touches device isolation or memory handling guarantees. Even when no exploit is known, security teams often treat these defects as high-priority due to the potential for downstream instability and the difficulty of proving that no sensitive workload is exposed.
Operationally, this is the kind of issue that deserves targeted verification:
- Determine whether your kernel build includes the affected arm64 code path.
- Confirm whether any devices or drivers rely on
ioremap_prot()behavior. - Check vendor advisories for the exact fixed build, not just the CVE label.
- Prioritize systems with specialized hardware or virtualization layers.
- Track whether the issue appears in your platform’s backport stream.
Historical Context
Kernel memory attribute bugs are a recurring theme in architecture-specific security work. Each time a platform’s semantics get more precise, helper functions must carry more of that complexity safely. The Linux kernel has spent years refining how it maps memory on arm64 because the architecture is widely deployed and because correctness failures can be hard to localize once they leave the helper and propagate into drivers.The significance of
ioremap_prot() lies in the fact that it is part of a family of functions that sit close to hardware-facing code. That proximity matters. Bugs there can have fewer obvious user-visible cues than a crash in application code, but they can affect core system behavior at a much lower level. Those are precisely the defects that tend to linger until a sanitizer, a formal review, or a very specific workload flushes them out.Why These Bugs Keep Reappearing
There are several reasons this category repeats. First, architecture-specific memory rules are hard to abstract cleanly. Second, kernel APIs sometimes evolve over time, and assumptions made in older code can become fragile when the surrounding implementation changes. Third, the gap between a generic helper and a hardware-specific mapping can hide mistakes that only show up under unusual configurations.That combination creates a familiar pattern:
- A small helper assumes a valid memory type.
- A translation layer extracts or rewrites it.
- The architecture-specific behavior diverges from expectation.
- The bug survives ordinary testing.
- A CVE is eventually assigned when the issue is recognized as security-relevant.
What Administrators Should Care About
For system administrators, the practical question is whether the affected code path is present in production and whether the kernel vendor has shipped a fix. Because the bug lives in the arm64 I/O mapping layer, the answer will vary widely based on hardware generation, distribution kernel branch, and whether the environment uses custom mappings or device-heavy workloads.This is also one of those vulnerabilities where patch urgency should be based on exposure, not just headline severity. If your environment includes arm64 servers, appliances, or cloud instances with specialized I/O drivers, the issue deserves prompt review. If you are running a fleet that does not use the relevant code path, the operational priority may be lower—but it should still be tracked.
Triage Priorities
Security teams should focus on the following questions:- Is the fleet running arm64 Linux kernels?
- Does the platform use custom I/O mappings or driver stacks that hit
ioremap_prot()? - Has the vendor published a backported fix for the exact kernel stream?
- Are there symptoms of device instability or unexpected mapping behavior?
- Does the environment include appliance-style or embedded deployments where patch lag is common?
How This Affects Patch Strategy
Not all CVEs are equally urgent in every environment, and this one is a good example of why patch strategy should be exposure-aware. If the vulnerable logic is not exercised, the short-term risk may be limited. But because the issue is in a core mapping helper, the long-term assumption should be that eventual remediation is necessary, not optional.For enterprises, the best practice is to align patch timing with kernel vendor cadence while validating that the fixed build actually contains the relevant arm64 change. Vendor packaging can be confusing, and the same kernel version number does not always mean the same backport set. That is why build-specific confirmation matters more than generic version comparisons.
Practical Remediation Steps
A sensible response plan looks like this:- Inventory all arm64 Linux systems.
- Identify which ones rely on device mapping paths.
- Check the vendor’s advisory or package notes for the fix.
- Test the update in a controlled environment first.
- Roll out to the most exposed systems before the broader fleet.
Competitive and Ecosystem Implications
Although this is a Linux kernel vulnerability, it still matters in the broader ecosystem because Microsoft’s advisory platform is often used as a cross-platform intelligence layer. Enterprises running mixed environments want a single place to monitor issues even when the root cause is in an upstream Linux component. That is one reason this CVE appears in the Microsoft Security Update Guide at all.There is also a subtle competitive dimension. Memory-model bugs on arm64 affect cloud and infrastructure vendors that depend on kernel correctness for performance and isolation. When a platform-level helper like
ioremap_prot() is implicated, the issue is no longer just a distro patch problem; it is a reliability and trust issue for the entire stack. Vendors that ship faster and backport more cleanly will look better to enterprise buyers.Why This Matters Beyond Linux
In hybrid operations, a Linux kernel CVE can affect Windows-managed tooling, CI/CD pipelines, container hosts, and cloud images that live inside a Microsoft-centric operational environment. That is why security teams should think in terms of asset exposure, not vendor identity. The advisory path matters because it connects the vulnerability to remediation workflows already in use.The broader lesson is that platform boundaries have become operational, not technical. A Linux kernel bug can still be a Microsoft-tracked issue if it affects customers whose security posture depends on Microsoft’s advisory ecosystem. That is an important shift in how modern infrastructure risk is communicated.
- Hybrid estates need cross-platform vulnerability visibility.
- Backport speed is a competitive differentiator.
- Kernel correctness affects cloud trust models.
- Advisory integration matters as much as raw disclosure.
- Arm64 infrastructure now spans consumer, enterprise, and cloud.
Strengths and Opportunities
The best thing about a CVE like this is that it is usually fixable in a targeted way. Because the issue is tied to a specific helper and architecture path, maintainers can often address it without redesigning broader subsystems. That makes remediation more tractable for vendors and easier for downstream teams to validate.It also creates an opportunity for better auditing. Bugs in mapping helpers often point to nearby code that has made similar assumptions, so this CVE can serve as a trigger for broader review of arm64 I/O mapping logic. That kind of follow-on hardening is often the real win.
- Narrow fix surface compared with broader memory-management bugs.
- Architecture-specific review can catch adjacent mistakes.
- Vendor backports are usually straightforward for contained helper bugs.
- Enterprise visibility improves through centralized advisory tracking.
- Driver audits may uncover similar attribute-handling assumptions.
- Security hardening can be expanded to nearby mapping code.
- Operational clarity is better when the vulnerable path is well understood.
Risks and Concerns
The main concern with this CVE class is that the damage may be subtle and intermittent. A wrong memory type in a mapping path might not crash immediately; instead, it can produce behavior that looks like driver flakiness, storage oddities, or hardware instability. That makes diagnosis harder and increases the chance that the issue remains misunderstood in the field.Another concern is patch lag. Arm64 Linux is everywhere now, but not every deployment moves at the same speed, especially in appliances, embedded systems, or vendor-customized kernels. A bug like this can stay alive much longer than its short description suggests.
- Silent misbehavior may be more common than obvious failures.
- Patch lag can be severe in appliance and embedded fleets.
- Architecture-specific exposure complicates triage.
- Vendor backport variance can make version checks unreliable.
- Driver interactions may amplify the impact of the defect.
- Root-cause analysis can be time-consuming when symptoms are indirect.
- Residual related bugs may exist in neighboring mapping code.
Looking Ahead
The next thing to watch is vendor backporting. For most organizations, the fix will not arrive as a dramatic upstream event; it will arrive as a kernel package update with a backported patch and a terse changelog entry. That means the real work for administrators is to map the CVE to the fixed build they actually deploy, not just to note that the advisory exists.It is also worth watching for related arm64 memory-type corrections. When a bug appears in a helper as central as
ioremap_prot(), it often invites further scrutiny of surrounding code. That can be healthy: one bug often reveals a family of assumptions that deserve review.What to Watch Next
- Vendor advisories naming the exact fixed kernel builds.
- Backports landing in long-term support branches.
- Any follow-up patches touching arm64 memory attributes.
- Driver or platform-specific notes about mapping behavior.
- Reports of stability improvements after kernel updates.
The larger takeaway is simple: modern kernel security is often about preserving the meaning of low-level abstractions. When a helper like
ioremap_prot() gets the memory type wrong, the bug is not just technical noise—it is a breach in the assumptions that make the rest of the system reliable. Fixing those assumptions quickly is how operators keep small architectural mistakes from becoming enterprise-scale problems.Source: MSRC Security Update Guide - Microsoft Security Response Center