When Microsoft’s security feed labeled CVE-2026-23347 around the Fintek F81604 USB CAN driver, the underlying bug looked deceptively small: a missing call to usb_anchor_urb() in the read bulk callback. In kernel terms, though, that small omission matters because an anchored URB is what lets the driver keep track of in-flight USB requests and clean them up reliably when I/O must stop. The Linux stable patch shows the fix plainly: anchor the URB before submitting it, or it can be leaked if usb_kill_anchored_urbs() is invoked later. (docs.kernel.org)
The Linux USB stack has long relied on URBs, or USB Request Blocks, as the core unit of asynchronous I/O. A driver fills in a URB, submits it, and later receives a completion callback when the transfer finishes or fails. That model is powerful, but it also creates a cleanup problem: once a driver starts queueing multiple URBs, it needs a disciplined way to cancel, drain, or reuse them without losing track of which requests are still alive.
That is where USB anchors come in. The kernel documentation describes an anchor as a bookkeeping structure that keeps track of submitted URBs and lets the driver stop them all at once when disconnect, close, or error handling requires it. The anchor pattern is explicitly designed for cases where a driver needs to cease all I/O to an interface without leaving stranded transfers behind. (docs.kernel.org)
CVE-2026-23347 sits inside that design pattern, not outside it. The bug is not that the driver lacked anchors altogether, but that one code path in f81604_read_bulk_callback() failed to attach the URB to the anchor before resubmitting it. The stable patch notes that the driver already handled this correctly elsewhere, which is why the issue is so interesting: it is a consistency bug in an otherwise established lifecycle pattern, not a wholesale design failure.
That distinction matters because kernel resource leaks often emerge from the seams between “correct in one path” and “forgotten in another.” In this case, the seam is the read bulk callback, which is exactly the kind of hot-path, reentrant code where a tiny sequencing error can survive for a long time. The practical effect is especially relevant when the device is unplugged, reset, or torn down while URBs are still pending. (kernel.org)
There is also a broader ecosystem angle. Microsoft’s Security Update Guide now regularly catalogs Linux kernel CVEs because enterprise defenders increasingly want one place to track vulnerabilities across mixed fleets. So even though the flaw lives in the Linux kernel, the CVE record becomes part of a cross-platform patch-management workflow that includliances, containers, and embedded devices. That is one reason a small USB-driver issue can acquire real operational weight very quickly.
That sequencing rule is the heart of the CVE. It is not a use-after-free or an obvious memory corruption flaw. It is a lifecycle bookkeeping flaw, which is why it is easy to underestimate and also easy to miss in code review. But in kernel land, lifecycle mistakes can still become security-relevant when they keep hardware access, buffers, or privileged paths alive longer than intended. (docs.kernel.org)
The patch also shows a second important pattern: if usb_submit_urb() returns an error, the code now calls usb_unanchor_urb() before handling the failure. That mirrors the general kernel expectation that bookkeeping must remain accurate even when the I/O path does not succeed. The result is cleaner state, fewer leaks, and a teardown path that behaves the way the USB anchor API was designed to behave. (docs.kernel.org)
This is why the commit message explicitly references usb_kill_anchored_urbs(). The whole point of anchoring is to make that kill path complete. If one URB slips through the cracks, the kill operation can no longer guarantee the driver has truly stopped all I/O. That is a correctness problem first, but it can become an operational and defensive problem if the leaked request remains connected to privileged kernel state.
The fact that the patch is already moving through stable review is another signal that maintainers considered the issue concrete enough to backport. Stable inclusion usually means the bug is not speculative. It indicates a fix that upstream maintainers want in maintained releases because the behavior is real, reproducible, and worth correcting rather than leaving to future cleanup.
That precision should not be mistaken for insignificance. Kernel security today is full of narrow defects that matter because they affect the kernel’s ability to recover, clean up, or enforce invariants. In a subsystem that is already handling asynchronous hardware events, a cleanup bug can become the kind of issue that matters only under stress—but when it does matter, it matters in exactly the scenarios operators care about most. (kernel.org)
Anchors reduce that burden by making the USB core part of the lifecycle model. A driver can ask the kernel to kill all anchored URBs, and the USB core will handle the unwinding in a defined order. The documentation even notes that anchored URBs are processed in reverse submission order, which helps preserve data ordering and teardown predictability. (docs.kernel.org)
That is why forgetting to anchor a resubmitted URB is such a precise bug. It does not break the whole system, but it bypasses the very abstraction the driver was supposed to rely on. The code still looks like it is participating in the anchor model, but one request is silently outside the net.
The USB core documentation also explains that usb_kill_urb() and related routines are meant to ensure completions have finished before the driver proceeds. But anchor-based management is what scales that discipline across multiple pending requests. In other words, the API is already telling the driver how to stay safe; CVE-2026-23347 is what happens when one callback takes a shortcut around that contract. (kernel.org)
That makes anchor discipline especially important. The driver may resubmit URBs continuously in a streaming loop, and teardown may happen at awkward times: unplug, reset, interface unbind, or device power management transitions. If any one resubmitted URB escapes the anchor, the bookkeeping bug can outlive the session that created it.
The upstream fix is notable because it applies not only to the bulk-read path but also mirrors the same pattern already present in the interrupt callback. That tells us the maintainers saw the issue as a consistency defect rather than an isolated typo. Consistency fixes are often the ones that quietly improve the robustness of an entire subsystem.
That is also why kernel stable maintainers pay close attention to these patches. The fix is small enough to backport safely, but important enough that leaving it unpatched would mean living with a subtle teardown flaw in a live driver. In the kernel world, that is usually enough to justify the CVE.
For enterprises and industrial users, the calculation is different. CAN-over-USB devices are more likely to appear in test benches, automation rigs, diagnostics stations, and specialized control environments where a hanging or uncleared device can interrupt workflows, skew logs, or complicate service recovery. In those environments, a cleanup bug can become a production issue even when it is not an obvious security exploit. (docs.kernel.org)
Enterprises also care because patch governance is based on identifiers, not on subjective severity alone. Once Microsoft publishes a CVE, it enters enterprise intake systems, asset-tagging workflows, and vulnerability management dashboards. That means the fix becomes part of a formal remediation process even if the practical exposure is limited to a subset of hardware.
The result is a familiar pattern: a niche kernel bug gets a broad administrative footprint because modern security operations are built to track everything first and sort risk second. That is a good thing overall. It means small driver bugs are less likely to fall through the cracks just because they do not headline a flashy exploit chain.
That also explains the timing. The CVE was published on March 25, 2026, and the stable patch references an upstream commit with explicit fixes metadata. In kernel-maintenance terms, that is the normal path: upstream fix, stable propagation, downstream vendor pickup, enterprise distribution.
The steady motion through the kernel pipeline is reassuring because the fix is narrow. There is no large refactor, no device behavior change beyond bookkeeping correctness, and no ambiguous semantic shift. That makes it a good stable candidate, which is exactly what operators want from a patch in this category.
That is an important distinction. Good kernel fixes often leave the user-visible behavior almost unchanged while tightening the hidden machinery that makes the system reliable. This is one of those cases: the change is small, but the operational confidence it buys is much larger than the diff suggests. (spinics.net)
Another opportunity is process-related. Stable review and vendor advisories are working together as intended: one upstream fix, one CVE, multiple distribution channels. That makes it easier for enterprises to absorb the change quickly, especially when the vulnerability affects a specialized hardware path rather than a universal subsystem.
A third issue is that enterprise patch teams may underestimate the CVE because the headline does not scream “critical.” That would be a mistake. Not every important kernel CVE is loud. Some are quiet because they involve correctness guarantees, and those guarantees are exactly what keep device stacks stable under pressure. (docs.kernel.org)
Finally, there is the usual risk of overfitting security language to a reliability problem. The public description currently frames this as a leaked URB due to incorrect anchoring, and that is accurate, but it should not be inflated into claims about remote exploitability without evidence. For defenders, the right response is disciplined patching, not speculation.
Another thing to watch is how security teams classify the impact. Some will treat it as a reliability-only issue and move on; others will see any kernel-managed resource leak as worthy of immediate patching. In mixed environments, the second view is usually the more practical one, because security operations rarely get to separate “reliability” from “defense” as cleanly as engineers would like.
In the end, CVE-2026-23347 is a reminder that kernel security is often about precision, sequencing, and teardown discipline, not just dramatic memory corruption. A single missing anchor call in a read callback is enough to create a leak path, and a leak path is enough to earn a CVE when the kernel community decides the fix belongs in the public record. That may not be the loudest kind of vulnerability, but it is exactly the sort of bug that separates robust systems from merely working ones.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Background
Background
The Linux USB stack has long relied on URBs, or USB Request Blocks, as the core unit of asynchronous I/O. A driver fills in a URB, submits it, and later receives a completion callback when the transfer finishes or fails. That model is powerful, but it also creates a cleanup problem: once a driver starts queueing multiple URBs, it needs a disciplined way to cancel, drain, or reuse them without losing track of which requests are still alive.That is where USB anchors come in. The kernel documentation describes an anchor as a bookkeeping structure that keeps track of submitted URBs and lets the driver stop them all at once when disconnect, close, or error handling requires it. The anchor pattern is explicitly designed for cases where a driver needs to cease all I/O to an interface without leaving stranded transfers behind. (docs.kernel.org)
CVE-2026-23347 sits inside that design pattern, not outside it. The bug is not that the driver lacked anchors altogether, but that one code path in f81604_read_bulk_callback() failed to attach the URB to the anchor before resubmitting it. The stable patch notes that the driver already handled this correctly elsewhere, which is why the issue is so interesting: it is a consistency bug in an otherwise established lifecycle pattern, not a wholesale design failure.
That distinction matters because kernel resource leaks often emerge from the seams between “correct in one path” and “forgotten in another.” In this case, the seam is the read bulk callback, which is exactly the kind of hot-path, reentrant code where a tiny sequencing error can survive for a long time. The practical effect is especially relevant when the device is unplugged, reset, or torn down while URBs are still pending. (kernel.org)
There is also a broader ecosystem angle. Microsoft’s Security Update Guide now regularly catalogs Linux kernel CVEs because enterprise defenders increasingly want one place to track vulnerabilities across mixed fleets. So even though the flaw lives in the Linux kernel, the CVE record becomes part of a cross-platform patch-management workflow that includliances, containers, and embedded devices. That is one reason a small USB-driver issue can acquire real operational weight very quickly.
What the Fix Actually Changes
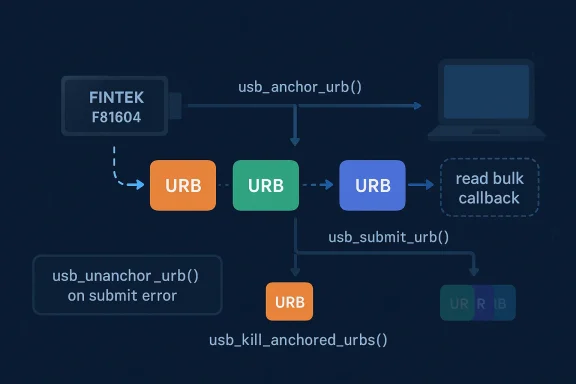
The fix is straightforward but important: before calling usb_submit_urb(), the callback now calls usb_anchor_urb(urb, &priv->urbs_anchor). If the submission fails, the code immediately unanchors the URB again. That preserves the intended lifecycle, which is: anchor first, submit second, and only leave the URB associated with the anchor if the kernel accepted the request.Why the order matters
The kernel documentation is clear that anchors are used to keep track of submitted URBs so they can be killed together later. If a URB is submitted without being attached to the anchor first, a later usb_kill_anchored_urbs() call cannot account for it, which creates the possibility of a leak or a stranded request during teardown. In other words, the cleanup mechanism only works if the request was registered with it before the race begins. (docs.kernel.org)That sequencing rule is the heart of the CVE. It is not a use-after-free or an obvious memory corruption flaw. It is a lifecycle bookkeeping flaw, which is why it is easy to underestimate and also easy to miss in code review. But in kernel land, lifecycle mistakes can still become security-relevant when they keep hardware access, buffers, or privileged paths alive longer than intended. (docs.kernel.org)
The patch also shows a second important pattern: if usb_submit_urb() returns an error, the code now calls usb_unanchor_urb() before handling the failure. That mirrors the general kernel expectation that bookkeeping must remain accurate even when the I/O path does not succeed. The result is cleaner state, fewer leaks, and a teardown path that behaves the way the USB anchor API was designed to behave. (docs.kernel.org)
Sequentially, the corrected flow is simple
- Obtain the URB in the completion callback.
- Anchor it to the driver’s URB list.
- Submit it back to the USB core.
- If submission succeeds, leave it anchored.
- If submission fails, unanchor it immediately and handle the error.
Why This Became a CVE
At first glance, a missed anchor call sounds like a reliability bug rather than a security issue. But CVE assignment in the Linux ecosystem has steadily expanded to include narrow kernel correctness defects when they affect resource lifetime, cleanup guarantees, or the integrity of kernel-managed state. In practice, those flaws can be security-adjacent because they interfere with the kernel’s ability to enforce orderly shutdown and bounded resource use.Resource leaks in kernel paths are not trivial
A leaked URB is not just “one more object in memory.” It is a live request tied to a hardware endpoint, a driver callback chain, and a teardown contract that the kernel expects to honor. If the leak survives a disconnect or restart sequence, the driver may not cleanly reclaim state, which can lead to stale transfers, unexpected callbacks, or failure to fully stop device activity. (kernel.org)This is why the commit message explicitly references usb_kill_anchored_urbs(). The whole point of anchoring is to make that kill path complete. If one URB slips through the cracks, the kill operation can no longer guarantee the driver has truly stopped all I/O. That is a correctness problem first, but it can become an operational and defensive problem if the leaked request remains connected to privileged kernel state.
The fact that the patch is already moving through stable review is another signal that maintainers considered the issue concrete enough to backport. Stable inclusion usually means the bug is not speculative. It indicates a fix that upstream maintainers want in maintained releases because the behavior is real, reproducible, and worth correcting rather than leaving to future cleanup.
What the CVE is not
It is not, based on the current public description, a remote code execution flaw. It is not obviously a privilege escalation. It is not even a classic memory-safety vulnerability in the usual sense. Instead, it is a missing bookkeeping step in a USB CAN driver that can leak URBs if teardown happens at the wrong moment. That is why the language in the advisory is so precise and so limited.That precision should not be mistaken for insignificance. Kernel security today is full of narrow defects that matter because they affect the kernel’s ability to recover, clean up, or enforce invariants. In a subsystem that is already handling asynchronous hardware events, a cleanup bug can become the kind of issue that matters only under stress—but when it does matter, it matters in exactly the scenarios operators care about most. (kernel.org)
The USB Anchor Pattern, Explained
The anchor pattern is one of the kernel’s neatest mechanisms for managing multiple asynchronous requests. It gives the driver a reference point for every URB it has submitted, so the driver can later kill, wait on, or scuttle the whole set in a controlled way. The kernel docs even emphasize that anchor-based cleanup is meant for scenarios where a driver must stop all I/O to an interface. (docs.kernel.org)Why anchors are safer than ad hoc tracking
Without an anchor, a driver has to maintain its own list of in-flight URBs and ensure every path updates that list correctly. That is error-prone, especially when requests are being resubmitted from completion callbacks. A missed list update, a race in teardown, or a forgotten removal path can leave the driver with a phantom URB that no longer fits the state machine. (docs.kernel.org)Anchors reduce that burden by making the USB core part of the lifecycle model. A driver can ask the kernel to kill all anchored URBs, and the USB core will handle the unwinding in a defined order. The documentation even notes that anchored URBs are processed in reverse submission order, which helps preserve data ordering and teardown predictability. (docs.kernel.org)
That is why forgetting to anchor a resubmitted URB is such a precise bug. It does not break the whole system, but it bypasses the very abstraction the driver was supposed to rely on. The code still looks like it is participating in the anchor model, but one request is silently outside the net.
Where the risk lives
The risk appears in disconnect, shutdown, or error-recovery paths. That is where usb_kill_anchored_urbs() gets called and where the driver expects the queue to drain completely. If the missing URB was never anchored, the driver can believe cleanup is complete while one request still exists in the system, which is exactly the kind of mismatch that kernel maintainers try to eliminate with anchor-based APIs. (kernel.org)The USB core documentation also explains that usb_kill_urb() and related routines are meant to ensure completions have finished before the driver proceeds. But anchor-based management is what scales that discipline across multiple pending requests. In other words, the API is already telling the driver how to stay safe; CVE-2026-23347 is what happens when one callback takes a shortcut around that contract. (kernel.org)
The Fintek F81604 Driver in Context
The Fintek F81604 driver is part of the Linux CAN-over-USB ecosystem, where reliability and orderly teardown are particularly important. CAN devices often operate in environments where low-latency device communication, error handling, and reconnect behavior all matter. A bug in the read callback is therefore not just a generic coding oversight; it affects the path that keeps the device responsive under real traffic.Why CAN-over-USB drivers are sensitive
CAN stacks tend to be used in embedded, industrial, automotive, and lab environments, where a dropped request or sloppy cleanup may disrupt telemetry or controller behavior. In those settings, the driver’s ability to stop and restart cleanly is not a nice-to-have. It is part of the operational contract between the operating system and the hardware. (spinics.net)That makes anchor discipline especially important. The driver may resubmit URBs continuously in a streaming loop, and teardown may happen at awkward times: unplug, reset, interface unbind, or device power management transitions. If any one resubmitted URB escapes the anchor, the bookkeeping bug can outlive the session that created it.
The upstream fix is notable because it applies not only to the bulk-read path but also mirrors the same pattern already present in the interrupt callback. That tells us the maintainers saw the issue as a consistency defect rather than an isolated typo. Consistency fixes are often the ones that quietly improve the robustness of an entire subsystem.
What this says about driver maturity
Mature drivers often accumulate just such inconsistencies over time. One callback gets hardened, another callback gets added later, and the cleanup contract is assumed rather than rechecked. The vulnerability is a reminder that even when a driver “uses anchors,” it still has to use them in every resubmission path. Partial compliance is not compliance. (spinics.net)That is also why kernel stable maintainers pay close attention to these patches. The fix is small enough to backport safely, but important enough that leaving it unpatched would mean living with a subtle teardown flaw in a live driver. In the kernel world, that is usually enough to justify the CVE.
Enterprise Impact vs. Consumer Impact
For consumers, the visible symptom is likely to be modest: a USB CAN device that behaves oddly during unplug, replug, or driver restart scenarios, or a system that fails to cleanly reclaim device state. Most desktop users will never notice a bug like this directly unless they are actively using CAN hardware.For enterprises and industrial users, the calculation is different. CAN-over-USB devices are more likely to appear in test benches, automation rigs, diagnostics stations, and specialized control environments where a hanging or uncleared device can interrupt workflows, skew logs, or complicate service recovery. In those environments, a cleanup bug can become a production issue even when it is not an obvious security exploit. (docs.kernel.org)
Why defenders should still care
A kernel bug that leaks URBs may not sound alarming until you consider what the kernel is protecting on behalf of the device. If shutdown paths are not fully reliable, the system may fail to release hardware resources or may keep stale I/O state around longer than expected. That can widen the blast radius of other failures and make incident response harder. (kernel.org)Enterprises also care because patch governance is based on identifiers, not on subjective severity alone. Once Microsoft publishes a CVE, it enters enterprise intake systems, asset-tagging workflows, and vulnerability management dashboards. That means the fix becomes part of a formal remediation process even if the practical exposure is limited to a subset of hardware.
The result is a familiar pattern: a niche kernel bug gets a broad administrative footprint because modern security operations are built to track everything first and sort risk second. That is a good thing overall. It means small driver bugs are less likely to fall through the cracks just because they do not headline a flashy exploit chain.
Patch Lineage and Stable Kernel Relevance
The stable patch record shows that the fix has already been pulled into the 6.18 stable review stream. That matters because stable review is where maintainers decide which upstream fixes are safe and important enough for maintained branches. A patch reaching that stage is typically a strong sign that the issue is reproducible and worth shipping broadly.Why backporting matters here
Backports are how most users actually receive kernel security and reliability fixes. Very few systems run mainline; most rely on distro kernels, vendor kernels, or OEM-provided builds that ingest stable patches. So when this URB anchor fix lands in stable review, that is the channel through which the bug will disappear for most affected systems.That also explains the timing. The CVE was published on March 25, 2026, and the stable patch references an upstream commit with explicit fixes metadata. In kernel-maintenance terms, that is the normal path: upstream fix, stable propagation, downstream vendor pickup, enterprise distribution.
The steady motion through the kernel pipeline is reassuring because the fix is narrow. There is no large refactor, no device behavior change beyond bookkeeping correctness, and no ambiguous semantic shift. That makes it a good stable candidate, which is exactly what operators want from a patch in this category.
What the fix leaves unchanged
The patch does not alter the CAN device’s functional behavior in the steady state. The driver still resubmits URBs and still processes read completions as before. What changes is the lifecycle bookkeeping around those resubmissions, which is where the kernel needs strict accounting to keep teardown safe and predictable.That is an important distinction. Good kernel fixes often leave the user-visible behavior almost unchanged while tightening the hidden machinery that makes the system reliable. This is one of those cases: the change is small, but the operational confidence it buys is much larger than the diff suggests. (spinics.net)
Strengths and Opportunities
The fix is a good example of kernel engineering done right: it is narrow, it is easy to reason about, and it restores the intended API contract without dragging in unnecessary complexity. It also strengthens the broader USB anchor model by ensuring the driver uses it consistently in every relevant path. In a world full of overengineered security patches, this is the kind of surgical correction maintainers prefer.- Minimal code change, maximal lifecycle benefit
- Restores consistency across callback paths
- Improves teardown reliability during disconnect and error handling
- Reduces the chance of stranded URBs and cleanup mismatches
- Fits the kernel’s established anchor pattern cleanly
- Easy for downstream maintainers to backport
- Low risk of behavior regression compared with a broader redesign
Another opportunity is process-related. Stable review and vendor advisories are working together as intended: one upstream fix, one CVE, multiple distribution channels. That makes it easier for enterprises to absorb the change quickly, especially when the vulnerability affects a specialized hardware path rather than a universal subsystem.
Risks and Concerns
The obvious risk is that the bug existed in a live driver path long enough to merit a CVE, which means some deployed kernels may have been carrying the flaw before the fix propagated. Because the issue is in a resubmission callback, it could remain dormant until the wrong unplug, reset, or disconnect sequence happens. That makes it the kind of bug that can evade casual testing but still show up in real operations.- A missed anchor can leave cleanup incomplete
- The issue may only surface under unplug or teardown conditions
- Leaked URBs can complicate driver recovery and device reset
- Specialized CAN hardware may be deployed in environments where reliability is critical
- Downstream kernel branches may absorb the fix at different speeds
- The bug is subtle enough to be missed in code review
- Partial adherence to the anchor model creates a false sense of safety
A third issue is that enterprise patch teams may underestimate the CVE because the headline does not scream “critical.” That would be a mistake. Not every important kernel CVE is loud. Some are quiet because they involve correctness guarantees, and those guarantees are exactly what keep device stacks stable under pressure. (docs.kernel.org)
Finally, there is the usual risk of overfitting security language to a reliability problem. The public description currently frames this as a leaked URB due to incorrect anchoring, and that is accurate, but it should not be inflated into claims about remote exploitability without evidence. For defenders, the right response is disciplined patching, not speculation.
Looking Ahead
The most likely near-term outcome is straightforward: downstream Linux vendors will continue to pull in the stable fix, and enterprise distributions will fold it into kernel maintenance releases. Because the patch is tiny and the behavior change is confined to URB bookkeeping, it should be one of the easier fixes for maintainers to absorb. That said, the actual time to protection will vary by distribution, kernel branch, and hardware certification cycle.What to watch next
- Whether downstream distros backport the fix into long-term-supported kernels
- Whether additional CAN-over-USB drivers receive similar cleanup reviews
- Whether related URB resubmission paths are audited for anchor consistency
- Whether Microsoft’s advisory gains fuller metadata as NVD enrichment continues
- Whether the stable series picks up follow-on housekeeping patches in the same driver
Another thing to watch is how security teams classify the impact. Some will treat it as a reliability-only issue and move on; others will see any kernel-managed resource leak as worthy of immediate patching. In mixed environments, the second view is usually the more practical one, because security operations rarely get to separate “reliability” from “defense” as cleanly as engineers would like.
In the end, CVE-2026-23347 is a reminder that kernel security is often about precision, sequencing, and teardown discipline, not just dramatic memory corruption. A single missing anchor call in a read callback is enough to create a leak path, and a leak path is enough to earn a CVE when the kernel community decides the fix belongs in the public record. That may not be the loudest kind of vulnerability, but it is exactly the sort of bug that separates robust systems from merely working ones.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
Last edited: