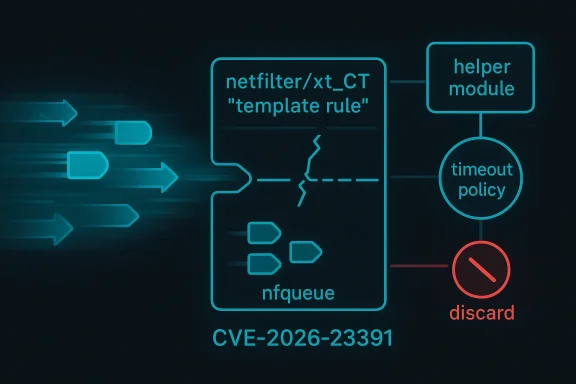
Linux kernel maintainers have assigned CVE-2026-23391 to a netfilter / xt_CT race condition fix that drops packets still sitting in nfqueue when a template rule is removed. The issue matters because the template can reference stateful objects such as a helper module or a timeout policy, and those objects may disappear before the queued packets are processed. In practical terms, the kernel patch closes a window where delayed packet handling could dereference stale configuration, so the safe behavior is to flush those enqueued packets as soon as the template disappears.
The Linux networking stack has spent years tightening the edges around netfilter, conntrack, and packet queuing because these subsystems combine mutable state with asynchronous packet flow. That combination is powerful, but it is also fragile: one kernel object may outlive another only by a few microseconds, and that is enough to create a security bug or crash path. The kernel project’s own CVE documentation makes clear that CVEs are routinely assigned to fixes once they land in stable trees, even when exploitation is not fully proven, because the kernel wants to preserve the bug-fix trail rather than speculate about attacker skill.
The xt_CT target is part of the iptables netfilter world, where connection tracking can be steered through helper modules and timeout policies. That flexibility is useful for protocols that need special handling, but it also means the packet’s eventual processing depends on kernel objects that can be removed independently. When packets are queued, the system is no longer fully synchronous, so a configuration that existed when the packet was enqueued may no longer exist when the packet is finally resumed.
This is not a new pattern for Linux security work. Netfilter has seen repeated fixes for races involving lifetime management, pending work queues, and packet state that outlives the rules that created it. A familiar theme runs through many of these CVEs: the kernel is not simply filtering traffic, it is also maintaining references to objects that may be torn down under load, during module unload, or while userspace is reconfiguring firewall rules.
In that context, CVE-2026-23391 reads less like a one-off bug and more like another example of the same architectural pressure point. The vulnerable condition is not exotic code execution logic; it is the ordinary and dangerous act of letting stateful packet processing continue after the state has been invalidated. In kernel terms, that is exactly the kind of edge case that can turn into a use-after-free, a crash, or a subtle policy bypass depending on timing.
The description is careful to note that templates using zone and event cache filter are safe because those uses only copy values. That distinction is important because it separates value capture from object reference. The former is stable; the latter is only safe if the referenced object cannot be removed out from under the queue. In a firewall subsystem, that difference is the line between ordinary configuration and a race-prone state machine.
The patch’s approach is conservative, and that is the right instinct here. Dropping enqueued packets is not glamorous, but it preserves kernel integrity and avoids making packet completion depend on torn-down template state. In security terms, fail closed is the correct answer when the alternative is continuing a flow through potentially dead references.
This also explains why the issue got a CVE even before NVD enrichment completed. The kernel community’s CVE process is intentionally broad, and it routinely tags fixes in stable trees so that vendors can map them to their own advisory pipelines. In other words, the upstream label is not a statement that exploitation is proven; it is a statement that the bug belongs on the security radar.
Enterprise environments are a different story. Firewalls, IDS/IPS appliances, SD-WAN edges, container hosts, and custom packet-processing platforms are much more likely to depend on nfqueue, conntrack helpers, and policy automation. On those systems, the ability to remove or reload a helper module while packets are still queued is not theoretical; it is part of normal operations, and that makes lifecycle bugs operationally relevant.
That pattern matters because it tells defenders how to think about the CVE. This is not just a single vulnerable line; it is evidence that stateful packet inspection remains a high-risk area for lifetime bugs. Whenever a packet can be paused and later resumed, the kernel has to guarantee that every object the packet might touch is still valid, or else stop the packet from continuing.
The practical challenge is that many organizations do not inventory firewall helper use very well. A system can appear to be “just running Linux” while actually serving as a packet processor, NAT gateway, or appliance with custom conntrack logic. That is why the safest response is often to review the actual firewall rule set and module usage rather than assume that a generic Linux host is unaffected.
For fleet operators, the key question is not whether the upstream fix exists, but whether the distribution kernel in use has absorbed it. Enterprises often run kernels with vendor backports, extended support lifecycles, or custom appliance builds, so the presence of a CVE in public databases is only the starting point. The real work is mapping that CVE to a concrete package version, especially when the CVSS score is still pending.
The second item is whether the fix gets mirrored cleanly across enterprise kernels. Backports can be straightforward for a small change like this, but the broader netfilter ecosystem has enough moving parts that kernel vendors sometimes stage related fixes at different times. In other words, the first patch is not always the last patch, especially in long-term support trees.
CVE-2026-23391 is therefore less a headline-grabbing exploit than a reminder that stateful packet processing is only as safe as the objects it depends on. The fix is modest, but the lesson is large: if a packet cannot be processed with confidence, it should not be processed at all. For Linux administrators, that is both the good news and the warning — a narrow patch today may prevent a much messier incident tomorrow.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Background
Background
The Linux networking stack has spent years tightening the edges around netfilter, conntrack, and packet queuing because these subsystems combine mutable state with asynchronous packet flow. That combination is powerful, but it is also fragile: one kernel object may outlive another only by a few microseconds, and that is enough to create a security bug or crash path. The kernel project’s own CVE documentation makes clear that CVEs are routinely assigned to fixes once they land in stable trees, even when exploitation is not fully proven, because the kernel wants to preserve the bug-fix trail rather than speculate about attacker skill.The xt_CT target is part of the iptables netfilter world, where connection tracking can be steered through helper modules and timeout policies. That flexibility is useful for protocols that need special handling, but it also means the packet’s eventual processing depends on kernel objects that can be removed independently. When packets are queued, the system is no longer fully synchronous, so a configuration that existed when the packet was enqueued may no longer exist when the packet is finally resumed.
This is not a new pattern for Linux security work. Netfilter has seen repeated fixes for races involving lifetime management, pending work queues, and packet state that outlives the rules that created it. A familiar theme runs through many of these CVEs: the kernel is not simply filtering traffic, it is also maintaining references to objects that may be torn down under load, during module unload, or while userspace is reconfiguring firewall rules.
In that context, CVE-2026-23391 reads less like a one-off bug and more like another example of the same architectural pressure point. The vulnerable condition is not exotic code execution logic; it is the ordinary and dangerous act of letting stateful packet processing continue after the state has been invalidated. In kernel terms, that is exactly the kind of edge case that can turn into a use-after-free, a crash, or a subtle policy bypass depending on timing.
Why this matters now
The record was published on March 25, 2026, and NVD had not yet assigned a severity score at the time of the entry. That means defenders should treat the advisory as actionable but still somewhat pre-enrichment, with the kernel fix and downstream vendor advisories providing the clearest operational guidance. Microsoft’s update guide already lists the CVE, which is a useful signal that this issue is being tracked for ecosystem visibility rather than remaining purely upstream trivia.What the bug is actually doing
At the heart of the issue is a mismatch between packet lifetime and template lifetime. A packet can be enqueued in nfqueue while an xt_CT template points to a helper or timeout policy that later disappears, leaving the packet in limbo with an invalid dependency chain. The patch’s stated remedy is straightforward: if the template rule is removed, flush the enqueued packets rather than let them continue toward a now-invalid target.The description is careful to note that templates using zone and event cache filter are safe because those uses only copy values. That distinction is important because it separates value capture from object reference. The former is stable; the latter is only safe if the referenced object cannot be removed out from under the queue. In a firewall subsystem, that difference is the line between ordinary configuration and a race-prone state machine.
The dangerous path
The unsafe path is the one that combines queued packets with a template whose backing object can vanish. That can happen during module removal, or when nfnetlink_cttimeout removes a timeout policy. If the queued packet is resumed after either event, the kernel may be forced to consult state that is no longer valid, which is exactly the sort of scenario that kernel hardening tries to eliminate preemptively.The patch’s approach is conservative, and that is the right instinct here. Dropping enqueued packets is not glamorous, but it preserves kernel integrity and avoids making packet completion depend on torn-down template state. In security terms, fail closed is the correct answer when the alternative is continuing a flow through potentially dead references.
- Queued packets can outlive the rule that queued them.
- Helper modules can be unloaded while packets are still waiting.
- Timeout policies can be deleted by userspace management.
- Value-only templates are not the problem; object-backed templates are.
- Flushing on removal is the least surprising and safest behavior.
How the Linux kernel is framing the fix
The upstream kernel description is terse, but the security philosophy behind it is easy to read: if a packet depends on a template that can disappear, then the packet should not remain in the queue once that template is gone. That is a classic lifecycle fix, the same kind of reasoning Linux has applied in other networking subsystems when delayed work outlived the objects it was supposed to consume.This also explains why the issue got a CVE even before NVD enrichment completed. The kernel community’s CVE process is intentionally broad, and it routinely tags fixes in stable trees so that vendors can map them to their own advisory pipelines. In other words, the upstream label is not a statement that exploitation is proven; it is a statement that the bug belongs on the security radar.
Why “drop” is the right verb
In networking, “drop” often sounds severe, but here it is more about containment than denial. The packet is already in a state where it cannot safely continue through the original rule path, so keeping it around creates more risk than value. A clean drop avoids stale object access, avoids undefined behavior, and gives administrators a deterministic failure mode that they can reason about.- The fix is aimed at object lifetime safety.
- It prefers predictable packet loss over kernel ambiguity.
- It reduces the chance of post-removal stale references.
- It aligns with Linux’s broader fail-closed networking posture.
Enterprise impact versus consumer impact
For most consumer desktops, xt_CT and related conntrack template behavior will be invisible. Typical home systems do not load custom firewall helpers, manage nfqueue-based packet inspection pipelines, or dynamically remove timeout policies while queued traffic is pending. So while the CVE is real, the day-to-day exposure for a default laptop or workstation is likely limited unless the machine is repurposed into a gateway, lab host, or security appliance.Enterprise environments are a different story. Firewalls, IDS/IPS appliances, SD-WAN edges, container hosts, and custom packet-processing platforms are much more likely to depend on nfqueue, conntrack helpers, and policy automation. On those systems, the ability to remove or reload a helper module while packets are still queued is not theoretical; it is part of normal operations, and that makes lifecycle bugs operationally relevant.
Operational reality
The enterprise risk is less about a single dramatic exploit and more about the disruption caused by a fragile firewall state machine. A dropped packet at the wrong moment can mean a broken session, a failed handoff, or a cascade of troubleshooting noise that obscures the underlying kernel defect. In environments with strict availability targets, even a “safe” drop can have real costs if it lands during traffic spikes or rule updates. That is the tradeoff kernel engineers are balancing here.- Consumer systems are likely to be low exposure unless they run advanced firewall tooling.
- Enterprise gateways are likely to be higher exposure because they use mutable netfilter state.
- Automation-heavy shops should treat the fix as operationally relevant, not merely theoretical.
- Packet drops during rule removal are a controlled failure, but still a service event.
Why this belongs to a broader netfilter pattern
Netfilter has a long history of bugs that arise when rules, objects, and background work do not agree on who owns what. Recent kernel fixes have addressed races around pending work queues, set destruction, expectation handling, and reference counting in conntrack-related code. The common denominator is not one specific API, but the challenge of maintaining correctness while packets, userspace, and kernel teardown all move at different speeds.That pattern matters because it tells defenders how to think about the CVE. This is not just a single vulnerable line; it is evidence that stateful packet inspection remains a high-risk area for lifetime bugs. Whenever a packet can be paused and later resumed, the kernel has to guarantee that every object the packet might touch is still valid, or else stop the packet from continuing.
A security engineering lesson
The recurring lesson is simple: asynchronous packet handling plus dynamic rule mutation creates fertile ground for race conditions. Linux keeps improving the subsystem with targeted fixes, but each fix also reminds operators that the most powerful firewall setups are the ones most likely to need careful patch discipline. In practice, the more dynamic the ruleset, the more important the kernel update cadence becomes.- Netfilter bugs often involve lifetime mismatches.
- Conntrack helpers add stateful complexity.
- Queues and work items introduce timing windows.
- Repeated fixes suggest an area that deserves extra patch vigilance.
What administrators should do
Administrators should first determine whether they actually use xt_CT, nfqueue-based inspection, or conntrack helpers in production. If they do, this CVE should be treated like other stateful netfilter lifetime fixes: apply the kernel update quickly, verify that firewall reload behavior remains stable, and test any automation that unloads or replaces helper modules. If they do not use these features, the issue may still be worth tracking as part of the normal kernel maintenance cycle, but it is less likely to be urgent.The practical challenge is that many organizations do not inventory firewall helper use very well. A system can appear to be “just running Linux” while actually serving as a packet processor, NAT gateway, or appliance with custom conntrack logic. That is why the safest response is often to review the actual firewall rule set and module usage rather than assume that a generic Linux host is unaffected.
Triage checklist
- Confirm whether the host loads xt_CT or related conntrack helper modules.
- Check whether packets are being routed through nfqueue in production.
- Identify any automation that removes timeout policies or reloads firewall rules.
- Apply the vendor kernel update that includes the fix.
- Test rule teardown under realistic traffic before and after the patch.
Patch cadence and vendor response
The CVE record already links multiple stable kernel commits, which strongly suggests the fix has moved through the normal upstream-to-stable pipeline. That is important because Linux security response is usually less about a single announcement date and more about when the relevant stable branches pick up the patch. Microsoft’s listing of the CVE also shows that downstream vendors are already indexing the issue for their own update workflows.For fleet operators, the key question is not whether the upstream fix exists, but whether the distribution kernel in use has absorbed it. Enterprises often run kernels with vendor backports, extended support lifecycles, or custom appliance builds, so the presence of a CVE in public databases is only the starting point. The real work is mapping that CVE to a concrete package version, especially when the CVSS score is still pending.
What to verify in your environment
- Whether your kernel vendor has shipped the fix.
- Whether the fix is in a backported stable branch or a newer major release.
- Whether your firewall automation depends on helper teardown.
- Whether your appliances run a hardened or vendor-customized netfilter stack.
Strengths and Opportunities
This fix is a good example of Linux security engineering at its best: small, surgical, and conservative. It does not try to make queued packets magically safe after their dependencies vanish; it simply removes the unsafe path. That kind of restraint is boring in the best possible way, because it prioritizes predictability over cleverness.- Clear containment strategy by flushing packets that can no longer be processed safely.
- Minimal behavior change for safe template types that only copy values.
- Better lifecycle hygiene for netfilter stateful objects.
- Reduced risk of stale-reference bugs during module removal.
- Easier vendor backporting because the fix concept is narrow.
- Useful precedent for other conntrack and nfqueue lifecycle patches.
- Strong operational clarity: drop now, rather than guess later.
Risks and Concerns
The immediate technical risk is that any environment relying on queued packet inspection may have been depending on undefined behavior without realizing it. If packet queues are flushed during rule removal, administrators may see short-lived traffic interruption, which is preferable to memory corruption but still needs to be understood and tested. The broader concern is that this CVE fits into a pattern of netfilter lifetime bugs, which means similar edge cases may still exist elsewhere in the stack.- Packet loss during teardown may surprise automation and monitoring.
- Helper/module unload workflows may need retesting after patching.
- Hidden dependency chains can make affected systems hard to inventory.
- Backport variation may create inconsistent behavior across distributions.
- Sibling race conditions elsewhere in netfilter may still be undiscovered.
- NVD enrichment lag can delay confidence in severity and scope.
- Operational complacency is risky because many hosts will look unaffected until traffic patterns change.
What to Watch Next
The next thing to watch is downstream severity assignment. NVD had not yet published a base score when the record appeared, so vendors and operators will likely rely first on the kernel commit history and their own distro advisories. That makes patch availability more important than the initial scoring label, at least in the short term.The second item is whether the fix gets mirrored cleanly across enterprise kernels. Backports can be straightforward for a small change like this, but the broader netfilter ecosystem has enough moving parts that kernel vendors sometimes stage related fixes at different times. In other words, the first patch is not always the last patch, especially in long-term support trees.
Watch list
- Distribution kernel advisories and backport notes.
- NVD’s eventual CVSS enrichment for CVE-2026-23391.
- Whether adjacent conntrack fixes appear in the same stable cycle.
- Any reports of packet drops or rule-reload regressions after patching.
- Whether appliance vendors issue coordinated firmware updates.
CVE-2026-23391 is therefore less a headline-grabbing exploit than a reminder that stateful packet processing is only as safe as the objects it depends on. The fix is modest, but the lesson is large: if a packet cannot be processed with confidence, it should not be processed at all. For Linux administrators, that is both the good news and the warning — a narrow patch today may prevent a much messier incident tomorrow.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center