 Overview
Overview
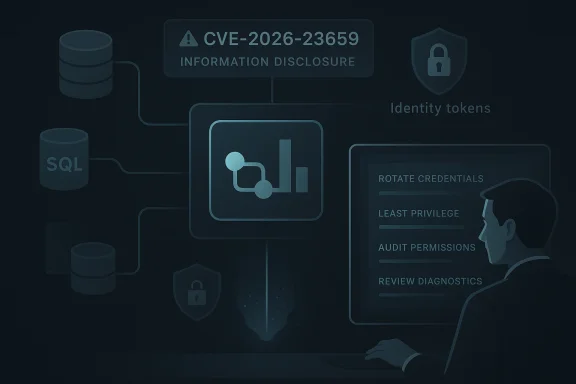
Microsoft’s CVE-2026-23659 is labeled an Azure Data Factory Information Disclosure Vulnerability, and that alone is enough to put it on the radar of any team running cloud analytics pipelines at scale. The phrasing matters: information disclosure bugs do not always sound as dramatic as remote code execution flaws, but in a managed cloud service they can still expose credentials, pipeline secrets, or operational metadata that attackers can chain into bigger compromises. Microsoft’s own vulnerability-confidence metric is designed to tell customers not just how severe a flaw may be, but how certain the vendor is that the issue exists and how much technical detail is available to adversaries.That distinction is especially important in Azure Data Factory, which sits at the center of many organizations’ data movement workflows. A flaw in the service can have consequences that extend far beyond a single pipeline, because Data Factory is often used to connect databases, SaaS platforms, storage accounts, and downstream analytics platforms. In other words, even a “read-only” disclosure issue can become an enterprise security event if it reveals the wrong token, configuration value, or internal endpoint.
Microsoft has been increasingly transparent about cloud-service CVEs in recent years, and this case fits that broader pattern. The company now treats cloud vulnerabilities as disclosure-worthy even when customers may not need to install a traditional patch, because the security value lies in making risk visible and actionable. That transparency is good for defenders, but it also means administrators need to understand how to interpret the confidence and impact language behind these advisories.
Background
Azure Data Factory is Microsoft’s managed data integration and orchestration service, built for ETL and ELT workflows, cross-service movement, scheduled transformations, and hybrid integration scenarios. It is widely used in enterprise environments because it can coordinate data movement across on-premises systems and cloud services without forcing customers to build the plumbing themselves. That convenience is also why the service attracts careful security scrutiny: it often becomes the traffic controller for some of the most sensitive data in the organization.Historically, cloud-service vulnerabilities in Azure have often involved token exposure, cross-tenant boundaries, connector behavior, or information leakage from managed infrastructure. Microsoft has previously documented issues in Azure Data Factory and related Synapse pipeline components, including the 2022 third-party Data Connector vulnerability that could have enabled attackers to acquire service certificates and execute commands in another tenant’s Integration Runtime. That incident showed how one weakness in the data plane can rapidly escalate into broader cloud abuse if identity and isolation controls are compromised.
Microsoft’s current disclosure approach reflects a shift in how the industry thinks about cloud security. Rather than waiting for customer-visible patches, Microsoft now publishes CVEs for important cloud service issues even when the remediation happens entirely in the backend. The rationale is straightforward: customers still need to know what happened, even if they do not apply a KB update. That shift has made security operations more transparent, but it has also increased the importance of reading advisories carefully.
The company’s Security Update Guide has also evolved to better describe vulnerabilities with structured fields, including titles, impact types, and confidence-related information. Microsoft has emphasized that the goal is to help customers understand not only the technical classification, but also the certainty of the report and the usefulness of the details to would-be attackers. In practice, that means a CVE like CVE-2026-23659 should be read as part of a larger security narrative rather than as a standalone line item.
Why confidence matters
A confidence metric is not a severity score. It is a measure of how sure the vendor is that the vulnerability exists and how credible the technical details are. A high-confidence advisory usually means Microsoft has confirmed the issue, mitigated it, and is comfortable publishing a public CVE with meaningful guidance.- High confidence generally means the flaw is verified.
- Medium confidence can mean the existence is plausible but details are incomplete.
- Lower confidence may indicate the issue is reported, but not fully substantiated.
What the CVE Label Tells Us
The title Azure Data Factory Information Disclosure Vulnerability is intentionally broad. Microsoft often uses concise CVE titles that summarize the effect rather than exposing the full technical root cause, and that is a clue in itself. A broad title can mean the vendor is limiting public detail for safety reasons, or simply that the disclosure is meant to guide defenders without arming attackers.An information disclosure issue in a service like Azure Data Factory could involve accidental exposure of secrets, unauthorized retrieval of metadata, leakage of request content, or a flaw in how the service returns contextual data. In a managed cloud environment, the most dangerous disclosure bugs are rarely about one obvious secret; they are often about small pieces of data that unlock more of the platform. Those fragments can include runtime tokens, internal URLs, tenant identifiers, or connection strings.
The practical meaning for defenders
Even without a detailed exploit path, the label should trigger a review of what Data Factory workloads can access. Teams should assume that any service-level disclosure might expose values that are useful for lateral movement, privilege escalation, or persistence. That is particularly true if the service is used to orchestrate access to sensitive storage, SQL endpoints, or identity providers.- Review secret storage patterns.
- Confirm that no critical credentials are embedded in pipeline definitions.
- Check whether managed identities have broader-than-necessary permissions.
- Revalidate logging and diagnostic retention settings.
- Treat any disclosed metadata as potentially chainable into a larger attack.
Microsoft’s Cloud Disclosure Strategy
Microsoft’s cloud CVE disclosures have become more explicit over the past two years. The company has said that it will issue CVEs for critical cloud service vulnerabilities even when no customer patch is required, because transparency improves risk management and helps defenders understand what changed. That approach is a meaningful departure from the older cloud assumption that if customers do not install software, customers do not need detailed advisories.This matters because managed services blur the line between vendor responsibility and customer responsibility. Microsoft may fix a backend issue without customer action, but customers still own identity hygiene, access boundaries, and the downstream consequences of exposed data. In that sense, a cloud CVE is not just a vendor bug report; it is a signal to reassess trust assumptions inside the customer environment.
The Security Update Guide and the newer Security Advisory mechanisms are part of that transparency push. Microsoft has made those systems more structured so that cloud events can be tracked alongside traditional software vulnerabilities. That is helpful for SOC teams and vulnerability managers, who increasingly need a single place to monitor both patchable and non-patchable issues.
Why cloud CVEs are different
Traditional desktop or server vulnerabilities usually map to a clear remediation step: install the update, reboot, verify. Cloud-service vulnerabilities are different because the fix may happen invisibly, while the customer’s response is more about verification and containment than patch deployment. That can create a dangerous false sense of safety if administrators assume backend mitigation means no further work is necessary.- Cloud CVEs can still affect customer data.
- Backend fixes do not eliminate the need for access reviews.
- Diagnostics and logs may preserve evidence of exposure.
- Identity and secret hygiene become the primary defense.
- Monitoring often matters more than patching.
Azure Data Factory’s Attack Surface
Azure Data Factory has a broad operational footprint because it must reach into many other services to do its job. That means its attack surface is not confined to one portal page or one API; it spans linked services, integration runtimes, managed identities, private endpoints, self-hosted runtimes, and connection credentials. The service’s flexibility is a strength, but it also multiplies the places where an information disclosure issue can matter.A disclosure issue here could affect an analyst, a pipeline author, a platform engineer, or an attacker who has only partial access to the environment. The most concerning scenario is one in which the disclosed information helps bridge a gap between least-privilege design and actual operational exposure. In cloud security, attackers rarely need a perfect breach; they need a usable fragment.
Where sensitive data can surface
Data Factory environments often carry sensitive operational material even when administrators think the service itself is innocuous. Pipeline definitions can encode endpoints, linked services can reference credential stores, and monitoring outputs can reveal data flow patterns. If a vulnerability leaks even part of that information, the risk can extend beyond the service boundary.- Linked service configuration details.
- Managed identity or service principal context.
- Pipeline names that reveal business processes.
- Internal storage or database endpoints.
- Runtime and environment metadata.
How Information Disclosure Becomes a Bigger Incident
Information disclosure vulnerabilities are often underestimated because they do not always yield immediate code execution or direct privilege escalation. But in cloud environments, small leaks are often the first step in bigger attacks. A secret token may unlock a storage account, a tenant identifier may assist phishing or enumeration, and a runtime certificate may become a foothold for deeper access.Microsoft’s own past cloud disclosures show this pattern clearly. In earlier Azure cases, service-specific exposure led to concern about certificates, tokens, or internal trust relationships rather than merely the exposed string itself. That is why a CVE like CVE-2026-23659 should be treated as a potential chain-builder, not just a standalone data leak.
A mature response therefore includes both technical and procedural actions. Teams should assume that any disclosed object may have secondary implications, and they should verify whether logs, caches, or connected systems retained copies of the exposed information. The goal is not panic; it is containment.
Common escalation paths
Here is how a disclosure bug in a service like Data Factory can snowball:- A service or user retrieves data they should not see.
- The exposed material includes a credential, endpoint, or token.
- The attacker uses that material to access a related resource.
- Access to the related resource reveals more sensitive data.
- The attack expands into persistence, exfiltration, or lateral movement.
Enterprise Impact
For enterprise customers, the main concern is not just whether Data Factory is exposed, but whether the service sits near regulated or business-critical data. In many organizations, Data Factory connects ERP systems, customer databases, finance systems, and data lakes, which means an information leak can have compliance consequences almost immediately. Even if Microsoft has already mitigated the issue in the cloud service, enterprise teams still need to verify downstream exposure.This is especially important in environments with shared platform teams and broad delegation. If one Data Factory instance or workspace has access to multiple resource domains, a disclosure issue may reveal more than the owning team realizes. The risk compounds when central data engineering groups manage connectors on behalf of multiple business units.
What enterprise administrators should check
Security teams should assess whether their Data Factory deployments rely on secrets that would be high value if exposed. They should also confirm whether any linked services or self-hosted integration runtimes have elevated trust relationships that could magnify a leak. In many cases, the right response is a focused access and secret review rather than a broad service shutdown.- Rotate sensitive credentials if there is any chance they were exposed.
- Re-evaluate managed identity permissions.
- Audit recent pipeline modifications and diagnostics.
- Validate private endpoint and firewall configurations.
- Review whether any secrets are stored in plain text or weakly protected formats.
Consumer and Small Business Relevance
Consumers generally do not interact with Azure Data Factory directly, but small businesses and startups often do through managed IT providers, analytics consultants, or SaaS integrations. That makes this vulnerability relevant to organizations that do not think of themselves as “enterprise” in the traditional sense. If their data stack relies on cloud orchestration, they are exposed to the same class of risk.Smaller organizations also tend to have thinner security staffing, which means cloud-service CVEs can go unnoticed even when they are operationally important. A backend mitigation from Microsoft is helpful, but if the business used shared credentials, temporary tokens, or over-privileged service accounts, the residual risk may remain. That is the hidden cost of convenience-driven cloud architecture.
Why smaller teams can be more exposed
Small organizations often build fast, then harden later. In the context of a disclosure vulnerability, that delay can be risky because secrets may already be spread across pipelines, scripts, and integration layers. The answer is usually not to abandon cloud data integration, but to tighten how trust is granted.- Use least-privilege identities.
- Keep secrets out of pipeline code.
- Prefer centralized secret management.
- Enable logging only where needed.
- Review third-party connector permissions regularly.
Historical Context: Azure Data Factory and Related CVEs
Microsoft has a visible history of addressing Azure Data Factory and adjacent service vulnerabilities. The 2022 third-party connector issue is a useful precedent because it showed that attackers may be able to pivot from one integration component into broader service impact. That earlier incident was not just about a connector bug; it was about trust boundaries inside the managed data stack.The broader Azure cloud portfolio has also seen repeated classes of issues involving SSRF, credential exposure, and service-specific leakage. This repetition does not imply systemic failure, but it does show how complicated cloud trust models have become. The more services share underlying platform features, the more important it is to isolate and monitor each service boundary carefully.
What the pattern suggests
The recurring lesson is that cloud service vulnerabilities rarely stay neatly inside one product team. A flaw in a data connector, runtime, or control-plane feature can quickly implicate identity, networking, and multi-tenant isolation. That is why cloud security disclosures deserve the same urgency as traditional OS patches, even when remediation happens server-side.- Service boundaries are only as strong as the weakest shared component.
- Connectors are often the most sensitive integration point.
- Identity and transport protections must be validated together.
- Backend fixes still leave customer configuration risk.
- Cloud security is a system, not a single product.
Technical Confidence and What It Implies
Microsoft’s confidence metric is useful because it hints at how much the public should trust the label and how much attackers might already understand. If a vulnerability is listed with a high confidence score, that usually means Microsoft has enough evidence to validate the issue internally. If details are sparse, it may be because the company is limiting the technical breadcrumbs that could help copycat researchers or attackers.That said, a lack of detail is not the same as a lack of seriousness. In cloud advisories, sparse public detail often reflects a balance between disclosure and harm reduction. The more a service issue can be generalized into an attacker playbook, the more carefully Microsoft tends to word the advisory.
How security teams should read the signal
Defenders should think of the confidence metric as a prioritization clue, not a verdict. A highly confident but vague information disclosure can still be operationally significant if the service handles secrets, tokens, or metadata. Conversely, a lower-confidence report may deserve monitoring but not emergency action.- High confidence means take the issue seriously.
- Limited detail means assume some attacker knowledge is already possible.
- Context determines whether a disclosure is benign or dangerous.
- Treat advisory language as a starting point for internal review.
- Align response intensity with the sensitivity of your deployment.
Competitive and Market Implications
Microsoft’s handling of cloud CVEs has become part of a broader competitive story in enterprise cloud. Customers increasingly compare providers not only on features and pricing, but also on how quickly and transparently they disclose security issues. In that market, the existence of a clear CVE and a structured advisory can be a trust signal, even when the underlying event is unpleasant.At the same time, transparency creates scrutiny. Azure Data Factory users will expect a concrete explanation of impact, timelines, and mitigations. Competing cloud platforms are likely watching how Microsoft balances disclosure with security hygiene, because every public cloud provider faces the same tension: say too little and you lose trust; say too much and you may increase exploitation risk.
Why this matters beyond Microsoft
Cloud buyers increasingly ask how vendors handle backend vulnerabilities, not just how they patch them. Public CVEs for managed services are now part of procurement, compliance, and vendor-risk discussions. That means the way Microsoft frames CVE-2026-23659 influences expectations across the market.- Transparency is becoming a competitive differentiator.
- Security posture affects enterprise procurement decisions.
- Clear advisories can reduce ambiguity in risk reviews.
- Vague advisories can create operational uncertainty.
- Faster disclosure can improve trust if paired with mitigation.
Strengths and Opportunities
Microsoft’s approach to CVE disclosure for cloud services has several strengths, and CVE-2026-23659 highlights why mature customers benefit from that model. The main opportunity is to use the disclosure as a catalyst for better secret hygiene, tighter identity controls, and more disciplined cloud governance. This is one of those cases where a vendor advisory can improve customer security even when the flaw itself is already fixed.- Transparent cloud CVE publication helps security teams track real risk rather than guess.
- Backend mitigation reduces the chance that customers must wait for a traditional patch cycle.
- Data Factory hardening can improve adjacent services, especially linked identities and connectors.
- Access review opportunities often uncover over-permissioned service principals.
- Secret rotation triggered by advisories can reduce long-term exposure.
- Security program maturity improves when cloud and endpoint processes are aligned.
- Executive visibility increases when a named CVE exists for the risk.
Risks and Concerns
The biggest concern is that many organizations will read “information disclosure” and assume the issue is minor or fully abstracted away by Microsoft’s backend mitigation. That would be a mistake. In cloud platforms, the consequence of a disclosure bug depends less on the category label and more on what the service could expose and how that exposure intersects with the customer’s architecture. The danger is not the word “disclosure”; it is the thing disclosed.- Credential leakage could give attackers a bridge into adjacent Azure services.
- Metadata exposure may aid tenant mapping or targeted intrusion.
- Operational complacency can set in when no patch is required.
- Poor secret hygiene makes even small leaks dangerous.
- Overly broad permissions magnify the blast radius of any exposure.
- Log retention and diagnostics may preserve sensitive artifacts longer than expected.
- Third-party integrations may retain copies of exposed values outside Microsoft’s control.
Looking Ahead
The next step for defenders is not waiting for more public detail; it is acting on the fact that a real vulnerability has been acknowledged. In a cloud service like Azure Data Factory, the practical response is usually to validate identities, rotate secrets where necessary, and review whether any service relationships are broader than intended. The earlier teams do this, the less likely a backend disclosure becomes a downstream breach.Microsoft will likely continue publishing cloud CVEs in this more transparent style, and that trend is broadly positive for customers. But it also means security teams need better processes for distinguishing between patchable workstation bugs and cloud service disclosures that require identity, logging, and configuration work. The organizations that adapt fastest will get the most value from Microsoft’s transparency.
What to watch next
- Whether Microsoft provides additional clarification on CVE-2026-23659 in the Security Update Guide.
- Whether related Azure data services receive follow-on advisories or variant hunting.
- Whether security vendors publish guidance on likely exposure patterns in Data Factory.
- Whether enterprises use the disclosure to trigger broader cloud secret rotation.
- Whether Microsoft’s cloud advisory model becomes even more structured across Azure services.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: