Microsoft’s security entry for CVE‑2026‑26125 identifies an elevation‑of‑privilege flaw in the Payment Orchestrator Service and places special emphasis on the vendor’s confidence metric — a critical signal for defenders about how much technical detail and exploitability information is actually available. The immediate headline is simple: Microsoft has acknowledged a privilege‑escalation weakness in a payment‑orchestration component, but the public technical details remain limited; defenders must treat the vendor advisory and published mitigations as the authoritative source, prioritize inventory and isolation of any Payment Orchestrator instances, and apply compensating controls until a vendor‑approved patch or definitive guidance is in place. (msrc.microsoft.com)
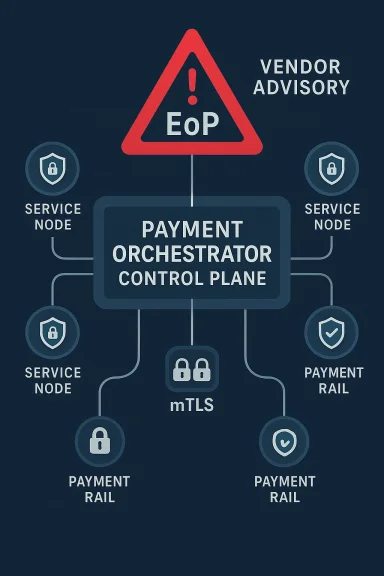
Payment orchestration platforms have become core infrastructure for modern commerce: they route authorization requests, normalize disparate provider APIs, manage reconciliation, and host sensitive tokenized payment data. A compromise in an orchestrator can therefore let an attacker manipulate routing, intercept or alter authorization flows, and — in worst cases — gain administrative control over merchant payment pipelines. Vendors and large merchants increasingly rely on orchestration platforms from niche orchestrators, independent SaaS vendors, and enterprise packages; this concentration increases the blast radius of bugs that allow privilege escalation. For context on how payment orchestrators are positioned in enterprise stacks and why they are high‑value targets, see vendor and market descriptions of payment orchestrator products and services.
Microsoft’s Security Update Guide entry for CVE‑2026‑26125 lists the vulnerability and provides the vendor’s exploitability / confidence rating — an indicator that the vendor may or may not have published deep technical details (proof‑of‑concepts, exploitability notes, or root‑cause explanations). When MSRC publishes a CVE page without extensive public technical detail, that often means the vendor has confirmed the bug and provided at least a high‑level description and remediation, but has not (yet) published a full technical write‑up or public PoC. Defenders should therefore assume the vulnerability is real and actionable, but exercise caution about third‑party PoCs or exploit claims until they can be corroborated. (msrc.microsoft.com)
Plausible technical vectors include:
Caveat: Because Microsoft’s published technical detail is minimal, the specific root cause (CWE class, exploitable API, code path) is not definitively public at this writing. Treat the above attack models as probable scenarios to prioritize detection and mitigation — not as confirmed exploitation steps. (msrc.microsoft.com)
Actionable priorities for operators are straightforward: take inventory of all orchestrator instances, restrict administrative interfaces, enable rigorous logging and detection, apply vendor patches as soon as they’re available, and treat any anomalous orchestration behavior as a potential incident. The financial and compliance stakes are high — so act decisively, follow vendor guidance, and escalate to incident response the moment you see suspicious signs.
For payment operators, service providers, and security teams, the time to act is now: assume the vulnerability is real, assume motivated adversaries will attempt to weaponize it, and harden the orchestration control plane accordingly. (msrc.microsoft.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Payment orchestration platforms have become core infrastructure for modern commerce: they route authorization requests, normalize disparate provider APIs, manage reconciliation, and host sensitive tokenized payment data. A compromise in an orchestrator can therefore let an attacker manipulate routing, intercept or alter authorization flows, and — in worst cases — gain administrative control over merchant payment pipelines. Vendors and large merchants increasingly rely on orchestration platforms from niche orchestrators, independent SaaS vendors, and enterprise packages; this concentration increases the blast radius of bugs that allow privilege escalation. For context on how payment orchestrators are positioned in enterprise stacks and why they are high‑value targets, see vendor and market descriptions of payment orchestrator products and services.Microsoft’s Security Update Guide entry for CVE‑2026‑26125 lists the vulnerability and provides the vendor’s exploitability / confidence rating — an indicator that the vendor may or may not have published deep technical details (proof‑of‑concepts, exploitability notes, or root‑cause explanations). When MSRC publishes a CVE page without extensive public technical detail, that often means the vendor has confirmed the bug and provided at least a high‑level description and remediation, but has not (yet) published a full technical write‑up or public PoC. Defenders should therefore assume the vulnerability is real and actionable, but exercise caution about third‑party PoCs or exploit claims until they can be corroborated. (msrc.microsoft.com)
What Microsoft has (and has not) said: the Exploitability / Confidence dimension
Microsoft’s advisory model includes an explicit “Exploitability / Confidence” metric that communicates two things at once:- the vendor’s confidence that the vulnerability exists and is accurately described, and
- how much actionable, technical detail is available to would‑be exploiters (for example, whether a PoC exists, whether the root cause is public, or whether only a high‑level impact statement was provided).
- High confidence, high technical detail — vendor has published specifics and/or a PoC; urgency is elevated because attackers can replicate the issue.
- High confidence, low technical detail — vendor confirms the flaw but withholds deep technical details (common during coordinated disclosures); still treat as actionable because the vendor’s confirmation implies the bug is real.
- Lower confidence / preliminary reports — public chatter or third‑party claims without vendor confirmation; treat cautiously and prioritize verification and inventory before action.
Why Payment Orchestrators are uniquely sensitive to privilege escalation
Payment orchestrators sit at the intersection of several high‑risk factors:- They handle or route authorization messages containing tokens, cryptograms, and sometimes the cardholder data environment (CDE) boundary. A privilege escalation to service or system level can expose cryptographic keys, tokens, and reconciliation data.
- Orchestrators often integrate with dozens of PSPs and acquirers; a compromised orchestration control plane can change routing logic to favor attacker‑controlled rails or to siphon refunds and payouts.
- Many orchestrators provide administrative consoles and API keys for merchants; elevated privileges inside the orchestration service can allow creation of backdoored merchant records or suppression of fraud alerts.
- Payment systems are tightly regulated; a compromise produces both technical and compliance/legal consequences.
Technical implications and likely attack models (based on public signals)
Microsoft’s CVE entry describes an Elevation of Privilege (EoP) in the Payment Orchestrator Service. Because public technical detail is limited, we must reason from likely implementation patterns to derive plausible attack models — and flag these as inferred, not proven.Plausible technical vectors include:
- Improper access control on privileged APIs: many orchestration services expose local management APIs or RPC endpoints that assume caller identity or a combination of network and service‑level protections. If an API fails to validate caller identity, a low‑privileged process or authenticated but limited user could call privileged functions to elevate rights.
- Serialization / deserialization bugs in admin workflows: orchestrators often import configuration bundles or project files. An untrusted or malformed configuration import may deserialize attacker‑controlled data and gain code execution or privilege changes in the orchestration process.
- Insecure inter‑service authentication: if cross‑service tokens or mutual TLS are misconfigured, a compromised adjacent component could impersonate the orchestrator’s management role.
- Local privilege escalation via service misconfiguration: weak file permissions, misapplied ACLs on service folders, or executable service binaries writable by lower‑privileged accounts can permit an attacker to replace or modify orchestrator components and attain higher privileges.
Caveat: Because Microsoft’s published technical detail is minimal, the specific root cause (CWE class, exploitable API, code path) is not definitively public at this writing. Treat the above attack models as probable scenarios to prioritize detection and mitigation — not as confirmed exploitation steps. (msrc.microsoft.com)
Immediate action plan for administrators and security teams
If you operate or are responsible for any Payment Orchestrator Service, treat CVE‑2026‑26125 as high priority for triage even in the absence of public PoCs. Follow this structured playbook:- Inventory (minutes–hours)
- Identify all instances of Payment Orchestrator software in your environment (SaaS tenants, on‑prem appliances, containers, and engineering workstations). Include orchestration connectors and reconciliation services.
- Record version numbers, service account identities, and network exposure (publicly routable, internal only, exposed to partner networks).
- Isolate and restrict (hours)
- Immediately restrict network access to orchestration management ports and APIs to only known administration IPs and service ranges.
- If the orchestrator exposes an administrative console on the public internet, put it behind multi‑factor authentication, a VPN, or zero‑trust access controls.
- Patch and apply vendor guidance (days)
- Check the orchestrator vendor for an official patch or hotfix. If the vendor has released updates, apply them first in a test environment, then roll out per change‑control. For Microsoft‑managed components, follow the Microsoft update guide advisory as primary authority. (msrc.microsoft.com)
- If a vendor patch is not yet available, apply recommended mitigations (restrict ports, tighten ACLs, disable unneeded management interfaces). National incident response recommendations for payment switches emphasize two‑factor administrative access and logical segregation of CDE components — follow these controls.
- Detect and hunt (1–7 days, ongoing)
- Add monitoring and EDR rules for anomalous orchestration behavior: new admin account creation, unusual config import, unexpected outbound connections to PSP endpoints, changes to routing tables, and file integrity changes to orchestrator binaries.
- Search logs for signs of suspicious activity during the exposure window: authentication failures followed by success, abruptly changed routing or settlement entries, or service restarts coincident with config imports. Historical incident reviews show attackers often use legitimate scripts and shared libraries to blend in.
- Prepare containment and recovery playbooks (1–14 days)
- Define rollback steps (restore known‑good configs and backups), revocation plans for any keys or tokens used by orchestration services, and customer‑notification templates.
- For SaaS vendors, request proof of remediation and ask for a detailed disclosure of the root cause and any indicators of compromise. Maintain an evidence chain for compliance reporting.
- Hardening and long‑term controls (weeks–months)
- Enforce least privilege for all orchestration service accounts; apply just‑in‑time elevation for high‑risk operations.
- Require mutual TLS and certificate pinning for internal service communications where possible; rotate credentials and keys.
- Add supply‑chain hygiene: require SBOMs for orchestrator components and rebuilds for any statically linked libraries that process signed artifacts. These steps reduce long‑term supply‑chain risk.
Detection signatures and what to hunt for
Based on industry patterns for payment switch compromises and privilege escalation vectors, prioritize the following telemetry sources and indicators:- Authentication logs: new admin API tokens, logins from unfamiliar IP ranges, or elevated session creation events.
- Process and file integrity: sudden replacement or modification of orchestrator binaries, new DLLs or shared objects loaded into the orchestration process, or new scheduled tasks invoking orchestrator utilities. Past payment switch intrusions showed adversaries launching shared objects from temporary directories to inject behavior.
- Network flows: unexpected outbound connections to unknown PSPs, sudden torrenting of reconciliation data to third‑party hosts, or unusual spikes in settlement traffic.
- Configuration changes: unexpected routing rules, new PSP endpoints, new merchant accounts, or changes to settlement windows. Logging of config imports should be immutable and time‑stamped for forensic reconstruction.
- Anomalous transactions: spikes in chargebacks, refunds, or high‑value transfers inconsistent with business baselines. These business‑level signals are often the first real indicator of a stealthy payment‑orchestrator compromise.
Assessment of risk: likelihood, impact, and prioritization
- Likelihood: Moderately high for targeted adversaries that profile payment ecosystems. Payment orchestration code paths and admin APIs are frequently targeted because of their high value. The absence of a public PoC lowers the immediate opportunistic exploitation risk, but motivated attackers (state actors or financially motivated cybercrime groups) will often reverse‑engineer vendor updates or exploit configuration mistakes.
- Impact: High. A successful EoP in a payment orchestrator can lead to fraudulent transactions, route hijacking, data theft of tokens or keys, and cascading regulatory and reputational harm. Even limited unauthorized access can enable persistent fraud.
- Prioritization: Organizations running payment orchestration services — or services adjacent to them (reconciliation, settlement engines, vaults) — should triage CVE‑2026‑26125 ahead of routine, lower‑impact vulnerabilities. Use defensive signals (infrastructure exposure, publicly accessible admin consoles, service account privileges) to refine urgency.
Communication: how to inform stakeholders and regulators
When payment infrastructure is implicated, timely and accurate communication is essential:- Prepare an executive summary for business leadership that explains risk, immediate mitigation steps taken (inventory, isolation, vendor patch status), and expected customer impact (if any).
- Notify internal compliance and legal teams early; payment incidents often trigger mandatory reporting to regulators or acquiring banks.
- If you operate as a service provider to merchants, prepare a coordinated disclosure template and a timed Q&A for customers; emphasize what you control (patching, isolation) and what customers must do (rotate API keys, monitor payouts).
- Maintain a single source of technical truth for incident details; avoid leaks or speculative public statements until you confirm technical facts. Historical vendor and agency guidance underscores the legal and reputational costs of inconsistent messaging.
Broader lessons for architects and vendors
CVE‑2026‑26125 — regardless of its detailed technical root cause — exposes recurring themes for payment and critical‑service vendors:- Treat orchestrators as CDE‑adjacent infrastructure: apply the same strict controls used for card‑holder data stores to management APIs and process/service accounts.
- Design for minimal privileged surface area: administrative functions should require multi‑factor, just‑in‑time elevation and should never be callable by local user processes without explicit privilege checks.
- Improve telemetry for signed artifacts and config imports: log per‑signer verification results and configuration provenance to prevent silent acceptance of crafted packages. Past cryptographic verification failures in other projects show how dangerous silent verification results can be.
- Shift left on security for file and config parsers: file parsing and import flows are common exploit entry points — expand fuzzing, static analysis, and provenance checks during CI/CD.
- Demand SBOMs and rebuilds for patched cryptographic libraries: when a fix is published for a library used in payment flows, downstream vendors must rebuild and reissue artifacts (especially when static linking is common). This reduces long‑tail exposure in embedded and appliance deployments.
Where public detail is thin: transparency, caution, and next steps
Microsoft’s advisory model communicates vendor confirmation and a confidence level — but when public technical details are scarce, defenders must rely on these steps:- Treat vendor advisory text as authoritative and act on it. Microsoft’s update guide is the canonical reference for CVE remediation and the exploitability/confidence metric. (msrc.microsoft.com)
- Use sector best practices for payment switches (segregation, 2FA, mutual TLS, tokenization) as immediate mitigations while awaiting vendor patches.
- Be cautious about third‑party claims or PoCs that emerge in unvetted venues; verify technical claims against vendor advisories and reputable CVE/NVD records before acting on exploit code. If a PoC appears, treat it as a rapid escalation signal and accelerate patching and detection.
Conclusion
CVE‑2026‑26125 is a reminder that the control plane of payments infrastructure is an attractive, high‑impact target. Microsoft’s advisory confirms the vulnerability and presents an exploitability/confidence signal that defenders must respect: the vendor confirmation makes the issue real, but limited public technical detail means defenders must prioritize inventory, isolation, and vendor‑driven remediation over chasing unverified PoCs.Actionable priorities for operators are straightforward: take inventory of all orchestrator instances, restrict administrative interfaces, enable rigorous logging and detection, apply vendor patches as soon as they’re available, and treat any anomalous orchestration behavior as a potential incident. The financial and compliance stakes are high — so act decisively, follow vendor guidance, and escalate to incident response the moment you see suspicious signs.
For payment operators, service providers, and security teams, the time to act is now: assume the vulnerability is real, assume motivated adversaries will attempt to weaponize it, and harden the orchestration control plane accordingly. (msrc.microsoft.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center