Microsoft’s latest Security Update Guide entry for CVE-2026-26150 is a reminder that cloud-era vulnerabilities are increasingly about privilege boundaries, not just code execution. The issue is listed as a Microsoft Purview eDiscovery Elevation of Privilege Vulnerability, which means the risk is not simply that an attacker might reach data, but that they may be able to gain more control inside an environment than their intended role should allow. Microsoft’s own guidance around Purview shows why that matters: eDiscovery is a highly privileged compliance function, built on role-based access control and case-specific permissions, and those privileges can expose sensitive organizational content if misused or bypassed.
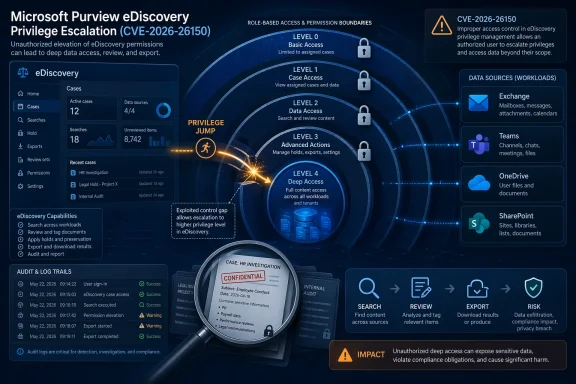
Microsoft Purview eDiscovery sits at the intersection of compliance, legal hold, records retention, and investigative access. In practice, it is one of the most sensitive administrative surfaces in Microsoft 365 because it can be used to identify, review, export, and manage content across services such as Exchange Online, Teams, OneDrive, and SharePoint. Microsoft documents eDiscovery as a controlled workflow governed by role-based access control, with case access and portal permissions managed through specific role groups rather than broad tenant-wide rights.
That is why an elevation of privilege flaw in this area deserves attention even before all technical details are public. A vulnerability in a compliance workflow can be especially serious because the attacker does not necessarily need to break encryption or exploit a browser. Instead, they may be trying to cross from a lower-privileged persona into a role that can search, review, or export material that would otherwise remain out of reach. Microsoft’s permissions guidance makes clear that eDiscovery access is intentionally gated, and that the least-privilege model is central to the service’s design.
The public wording for CVE-2026-26150 is also notable for what it does not yet say. At the time of writing, the advisory label provides a product area, a vulnerability type, and a CVE identifier, but not a full attack narrative. That means defenders should treat the issue as real but still partially opaque, with the confidence level anchored in Microsoft’s assignment of a CVE and the technical category rather than in a detailed exploit chain. Microsoft’s own security update program increasingly uses CVE descriptions to communicate the vulnerability class and affected surface, even when the root cause is not fully exposed in public-facing language.
There is also a broader strategic context here. Microsoft has spent the last few years becoming more transparent about cloud-service vulnerabilities, including a new class of Cloud Service CVEs and machine-readable advisory formats. That evolution matters because it reflects a recognition that SaaS incidents and cloud administrative flaws are now every bit as important as classic Windows patch Tuesday bugs. In other words, a Purview eDiscovery elevation issue is not an edge case; it is part of the normal modern attack surface.
That operational reach is the reason eDiscovery permissions are so tightly managed. Microsoft instructs organizations to assign users to the proper role groups, and notes that users must be granted the right permissions before they can perform eDiscovery tasks in the Purview portal. The platform also uses roles such as Compliance Administrator, Case Management, and eDiscovery Manager to keep privileges scoped to specific tasks.
The likely value of such access is not theoretical. eDiscovery content can include executive communications, HR issues, litigation materials, incident response evidence, and business-confidential records. A privilege escalation in that layer could produce the kind of quiet but deep compromise that organizations often detect late, especially if the attacker behaves like a legitimate compliance user.
Key implications include:
In this case, the most defensible conclusion is that Microsoft has acknowledged enough to assign a CVE and classify it as a privilege escalation issue in Purview eDiscovery. That is stronger than rumor, but weaker than a fully documented exploitation advisory. For defenders, certainty about existence is what matters first; full exploit mechanics come second.
This is not unusual in cloud security. Microsoft’s newer transparency efforts around cloud-service CVEs and CSAF files indicate that the company is trying to communicate more quickly and more formally, but there is still a gap between initial acknowledgment and technical detail. That gap is where defenders must make decisions.
The confidence metric is therefore doing double duty:
That distinction matters because the consequences are not measured only in endpoint compromise. An eDiscovery privilege escalation could expose regulated data, protected investigations, and legal correspondence. In sectors such as finance, healthcare, public sector, and critical infrastructure, that can create both security and governance exposure.
Organizations should also remember that the Purview portal is designed around careful permission scoping, which means the weakest link is often administrative sprawl. The more users who hold broad compliance roles, the more dangerous any privilege bug becomes. Microsoft explicitly recommends using roles with the fewest permissions possible.
If CVE-2026-26150 weakens that separation, the issue is not simply an administrative nuisance. It could allow a user to move into a more powerful compliance identity, or bypass some portion of the intended authorization logic. In a system built to expose only specific legal-relevant information, any boundary break can have severe consequences.
That is why this bug should be viewed as more than an internal service defect. It touches compliance process integrity, and that is often as important to a business as raw confidentiality. The legal defensibility of an investigation can be damaged if case access controls are compromised.
Notable permission realities include:
That distinction changes the defensive playbook. Endpoint patching is still essential, but cloud-service privilege bugs often require tenant-side hardening, role review, monitoring, and procedural controls. Microsoft’s own documentation around Purview leans heavily on role design, access settings, and proper assignment of permissions.
For security teams, the lesson is clear: a SaaS bug may not be visible in the same way a desktop patch is visible, but it can still be just as important. In fact, because SaaS platforms concentrate sensitive data and privileged workflows, the impact can be broader. That is especially true in compliance systems, where the attacker does not need to own the endpoint to cause damage.
For rivals, the incident is a reminder that compliance platforms are high-value targets. Any vendor that offers searchable, exportable access to sensitive collaboration data must prove that its authorization model is resilient. If Microsoft demonstrates quick remediation and enough detail for customers to assess exposure, it may ultimately reinforce the credibility of its broader security posture.
The broader market implication is that customers may demand more granular proof of isolation, role enforcement, and auditability. That in turn rewards vendors that can clearly show how access is segmented and monitored. Microsoft’s move toward richer advisory formats suggests it knows the market is watching.
The second step is to watch for unusual eDiscovery actions. In a privilege-abuse scenario, suspicious behavior may look like normal compliance work at first: case creation, role changes, export requests, or access to content outside a person’s typical remit. That means audit visibility and change tracking are critical.
Longer term, CVE-2026-26150 may become another example of how cloud security is increasingly about authorization integrity. Microsoft’s broader transparency push suggests the company understands that customers need more than a CVE title; they need a usable story about risk, exposure, and remediation. That is a good direction for the industry, but it also raises expectations that future cloud-service vulnerabilities will be explained with greater speed and precision.
What to watch next:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
Microsoft Purview eDiscovery sits at the intersection of compliance, legal hold, records retention, and investigative access. In practice, it is one of the most sensitive administrative surfaces in Microsoft 365 because it can be used to identify, review, export, and manage content across services such as Exchange Online, Teams, OneDrive, and SharePoint. Microsoft documents eDiscovery as a controlled workflow governed by role-based access control, with case access and portal permissions managed through specific role groups rather than broad tenant-wide rights.That is why an elevation of privilege flaw in this area deserves attention even before all technical details are public. A vulnerability in a compliance workflow can be especially serious because the attacker does not necessarily need to break encryption or exploit a browser. Instead, they may be trying to cross from a lower-privileged persona into a role that can search, review, or export material that would otherwise remain out of reach. Microsoft’s permissions guidance makes clear that eDiscovery access is intentionally gated, and that the least-privilege model is central to the service’s design.
The public wording for CVE-2026-26150 is also notable for what it does not yet say. At the time of writing, the advisory label provides a product area, a vulnerability type, and a CVE identifier, but not a full attack narrative. That means defenders should treat the issue as real but still partially opaque, with the confidence level anchored in Microsoft’s assignment of a CVE and the technical category rather than in a detailed exploit chain. Microsoft’s own security update program increasingly uses CVE descriptions to communicate the vulnerability class and affected surface, even when the root cause is not fully exposed in public-facing language.
There is also a broader strategic context here. Microsoft has spent the last few years becoming more transparent about cloud-service vulnerabilities, including a new class of Cloud Service CVEs and machine-readable advisory formats. That evolution matters because it reflects a recognition that SaaS incidents and cloud administrative flaws are now every bit as important as classic Windows patch Tuesday bugs. In other words, a Purview eDiscovery elevation issue is not an edge case; it is part of the normal modern attack surface.
What Microsoft Purview eDiscovery Actually Controls
eDiscovery is a legal and investigative workflow, not a consumer feature. Microsoft defines it as the process of identifying and delivering electronically stored information that can be used as evidence in investigations and legal cases. It spans multiple Microsoft 365 workloads, and the platform can search mailboxes and sites together, then export results into case workflows.That operational reach is the reason eDiscovery permissions are so tightly managed. Microsoft instructs organizations to assign users to the proper role groups, and notes that users must be granted the right permissions before they can perform eDiscovery tasks in the Purview portal. The platform also uses roles such as Compliance Administrator, Case Management, and eDiscovery Manager to keep privileges scoped to specific tasks.
Why a privilege flaw matters here
If an attacker can subvert eDiscovery authorization, they may gain access to content that has both operational and legal sensitivity. That is especially concerning because eDiscovery is designed to surface material that would otherwise be difficult to locate across a sprawling Microsoft 365 tenant. A small weakness in permission enforcement can therefore become a disproportionate exposure event.The likely value of such access is not theoretical. eDiscovery content can include executive communications, HR issues, litigation materials, incident response evidence, and business-confidential records. A privilege escalation in that layer could produce the kind of quiet but deep compromise that organizations often detect late, especially if the attacker behaves like a legitimate compliance user.
Key implications include:
- Cross-workload reach across Exchange, Teams, OneDrive, and SharePoint.
- Role-based gating that depends on correct enforcement.
- Export and review workflows that can reveal sensitive content.
- Case-level access controls that must remain intact.
Why the Confidence Metric Matters
The description provided with CVE-2026-26150 focuses on the degree of confidence in the vulnerability’s existence and the credibility of known technical details. That language is important because Microsoft’s public CVE entries do not always expose the same level of detail at the same moment. Sometimes the vendor has a confirmed issue and a patch, but only limited public explanation. Other times, the industry learns of a vulnerability class before the exact failure mode is fully described.In this case, the most defensible conclusion is that Microsoft has acknowledged enough to assign a CVE and classify it as a privilege escalation issue in Purview eDiscovery. That is stronger than rumor, but weaker than a fully documented exploitation advisory. For defenders, certainty about existence is what matters first; full exploit mechanics come second.
How defenders should read the signal
There is a practical difference between a title-only disclosure and a public postmortem. A title-only CVE tells you where to focus, but not necessarily how the boundary was crossed. A postmortem tells you what to instrument, what to detect, and what specific behaviors to hunt for. Until Microsoft publishes more, the safer assumption is that the issue could affect any deployment that exposes the relevant eDiscovery control path.This is not unusual in cloud security. Microsoft’s newer transparency efforts around cloud-service CVEs and CSAF files indicate that the company is trying to communicate more quickly and more formally, but there is still a gap between initial acknowledgment and technical detail. That gap is where defenders must make decisions.
The confidence metric is therefore doing double duty:
- It signals that the issue is not purely speculative.
- It hints that the technical root cause may still be under controlled disclosure.
- It tells customers to prioritize response even before every exploit detail is public.
- It implies attackers may also be working with limited public information rather than a turnkey recipe.
Enterprise Exposure vs Consumer Impact
This vulnerability is overwhelmingly an enterprise concern. Microsoft Purview eDiscovery is a compliance and legal platform used by organizations to manage evidence and investigations; it is not a feature that ordinary home users encounter. The practical blast radius therefore concentrates inside Microsoft 365 tenants, particularly those with compliance-heavy workflows and large administrative teams.That distinction matters because the consequences are not measured only in endpoint compromise. An eDiscovery privilege escalation could expose regulated data, protected investigations, and legal correspondence. In sectors such as finance, healthcare, public sector, and critical infrastructure, that can create both security and governance exposure.
Consumer relevance is indirect
There may be little or no direct consumer impact in the ordinary sense. However, consumers can still be affected indirectly when their data is held by an organization that uses Microsoft 365 eDiscovery. If a company’s compliance boundary is weakened, personal data stored in corporate mailboxes or collaboration systems may become more accessible than intended. That is an enterprise vulnerability with downstream privacy consequences.Organizations should also remember that the Purview portal is designed around careful permission scoping, which means the weakest link is often administrative sprawl. The more users who hold broad compliance roles, the more dangerous any privilege bug becomes. Microsoft explicitly recommends using roles with the fewest permissions possible.
How Microsoft Purview Permissions Shape the Risk
Microsoft’s documentation repeatedly emphasizes that eDiscovery access depends on assigned roles and case permissions. Users need the appropriate portal roles, and in many workflows they must also be added to the eDiscovery Manager role group before they can access a case. That means the security model assumes a clean separation between ordinary users, compliance operators, and case reviewers.If CVE-2026-26150 weakens that separation, the issue is not simply an administrative nuisance. It could allow a user to move into a more powerful compliance identity, or bypass some portion of the intended authorization logic. In a system built to expose only specific legal-relevant information, any boundary break can have severe consequences.
The role model is the security model
Microsoft’s own explanation of Purview permissions makes clear that roles are not decorative labels. They are the enforcement mechanism that determines who can see cases, who can manage them, and who can handle content. If a vulnerability crosses that enforcement boundary, the attacker may inherit the full operational value of the role rather than a single narrow capability.That is why this bug should be viewed as more than an internal service defect. It touches compliance process integrity, and that is often as important to a business as raw confidentiality. The legal defensibility of an investigation can be damaged if case access controls are compromised.
Notable permission realities include:
- Global Administrator or Role Management access is required to manage role groups in the Purview portal.
- Case access can be separately controlled inside eDiscovery.
- Reviewer access may be granted to guest users in certain scenarios.
- Least privilege is Microsoft’s recommended posture.
What Makes This Different From Classic Windows Vulnerabilities
Traditional Windows vulnerabilities often focus on local privilege escalation, remote code execution, or sandbox escapes in operating-system components. CVE-2026-26150 is different because it lives in a cloud service designed around trust, workflow, and administrative authorization. The attack surface is not merely code; it is policy enforcement.That distinction changes the defensive playbook. Endpoint patching is still essential, but cloud-service privilege bugs often require tenant-side hardening, role review, monitoring, and procedural controls. Microsoft’s own documentation around Purview leans heavily on role design, access settings, and proper assignment of permissions.
Why cloud-service CVEs deserve their own attention
Microsoft has acknowledged this shift by formalizing Cloud Service CVEs and publishing them with increasing transparency. That means customers should expect more bugs to show up in services that are continuously updated rather than only in installable binaries. The result is a security model where some fixes happen silently in Microsoft’s infrastructure, while customers must still adapt policies and review exposure.For security teams, the lesson is clear: a SaaS bug may not be visible in the same way a desktop patch is visible, but it can still be just as important. In fact, because SaaS platforms concentrate sensitive data and privileged workflows, the impact can be broader. That is especially true in compliance systems, where the attacker does not need to own the endpoint to cause damage.
Competitive and Market Implications
Microsoft Purview competes in a market where compliance, data governance, and eDiscovery platforms are judged on trust as much as features. A privilege escalation disclosure in this space does not automatically erase confidence, but it does raise the bar for transparency and remediation speed. Enterprise buyers increasingly compare not only capability, but also how clearly vendors explain security issues and how fast they respond.For rivals, the incident is a reminder that compliance platforms are high-value targets. Any vendor that offers searchable, exportable access to sensitive collaboration data must prove that its authorization model is resilient. If Microsoft demonstrates quick remediation and enough detail for customers to assess exposure, it may ultimately reinforce the credibility of its broader security posture.
Trust, not just features, is the battleground
This matters because eDiscovery is often purchased as part of a larger Microsoft 365 governance stack. In that environment, buyers are not comparing a single feature; they are deciding whether the platform can safely hold the keys to internal investigations. A flaw in eDiscovery authorization can therefore become a sales and renewal talking point, even if it affects only a subset of tenants.The broader market implication is that customers may demand more granular proof of isolation, role enforcement, and auditability. That in turn rewards vendors that can clearly show how access is segmented and monitored. Microsoft’s move toward richer advisory formats suggests it knows the market is watching.
Operational Response for Security Teams
Even without a full exploit narrative, security teams should treat CVE-2026-26150 as a prompt to audit Purview access. The first step is to confirm who can administer role groups, who can access cases, and whether any accounts have accumulated excessive privileges over time. Microsoft’s own documentation makes this kind of review straightforward in principle, even if it can be tedious in practice.The second step is to watch for unusual eDiscovery actions. In a privilege-abuse scenario, suspicious behavior may look like normal compliance work at first: case creation, role changes, export requests, or access to content outside a person’s typical remit. That means audit visibility and change tracking are critical.
A practical checklist
A careful response plan should include at least the following:- Review all users with eDiscovery Administrator, eDiscovery Manager, and related compliance roles.
- Verify that only necessary personnel can manage role groups in Purview.
- Audit recent case access, role membership changes, and exports.
- Confirm whether guest reviewers or delegated users have been added to sensitive cases.
- Tighten permissions to the fewest necessary users.
- Preserve logs that may help reconstruct unauthorized access patterns.
- Track Microsoft’s advisory updates for technical detail and remediation guidance.
Strengths and Opportunities
Microsoft’s handling of Purview-related security issues has several strengths, and CVE-2026-26150 also exposes opportunities for better customer readiness. The biggest opportunity is that organizations can use this moment to harden compliance access before an exploit narrative matures. The strongest security programs will use the advisory as a catalyst for role hygiene rather than waiting for a confirmed intrusion.- Microsoft has already built a role-based access control model for eDiscovery.
- The service clearly documents case-level access controls.
- Purview guidance encourages least privilege.
- Microsoft’s newer advisory transparency can improve customer response speed.
- The issue gives enterprises a reason to clean up dormant or overbroad compliance roles.
- Security teams can align legal, IT, and compliance stakeholders around a common access review.
- Better logging and review now can pay off well beyond this single CVE.
Risks and Concerns
The main concern is that privilege escalation issues in compliance systems can be hard to spot and even harder to prove after the fact. Unlike a crash or obvious malware infection, an authorization flaw may leave behind only subtle traces of behavior that looks legitimate on paper. That is why auditability matters as much as patching or configuration changes.- Attackers could potentially pivot from limited access to broader eDiscovery visibility.
- Sensitive litigation, HR, and incident-response content could be exposed.
- Excessive role assignments may magnify the impact.
- Guest reviewer or delegated access paths can complicate investigations.
- Organizations may underestimate the bug if they assume it is “just compliance software.”
- The lack of early technical detail can delay precise detection engineering.
- Misconfigured permissions may create confusion about whether a tenant is actually exposed.
Looking Ahead
The next meaningful milestone will be whether Microsoft expands the CVE entry with more technical detail, mitigation guidance, or evidence of exploitation. If that happens, defenders will be able to move from broad privilege review to specific hunting queries and detection logic. Until then, the best posture is to assume that the issue could matter anywhere the Purview eDiscovery permission model is in active use.Longer term, CVE-2026-26150 may become another example of how cloud security is increasingly about authorization integrity. Microsoft’s broader transparency push suggests the company understands that customers need more than a CVE title; they need a usable story about risk, exposure, and remediation. That is a good direction for the industry, but it also raises expectations that future cloud-service vulnerabilities will be explained with greater speed and precision.
What to watch next:
- An updated Microsoft advisory with fuller technical details.
- Any mention of affected Purview roles or specific access paths.
- Detection guidance for suspicious eDiscovery case activity.
- Confirmation of whether exploitation requires authenticated access.
- Follow-on hardening recommendations for Purview administrators.
Source: MSRC Security Update Guide - Microsoft Security Response Center