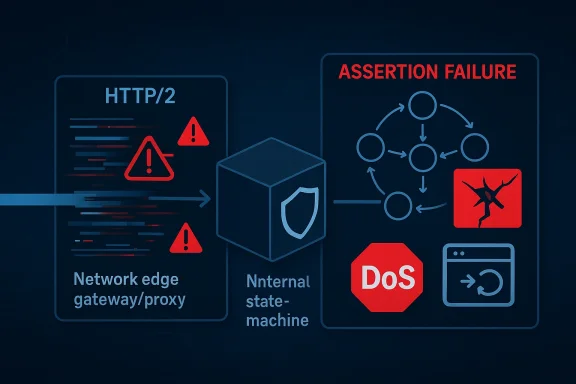
The Microsoft Security Response Center entry for CVE-2026-27135 is currently unavailable, but the vulnerability title alone tells an important story: this is an nghttp2 denial-of-service issue tied to an assertion failure caused by missing state validation. In practical terms, that points to a protocol-handling bug in HTTP/2 session logic, where malformed or unexpected traffic can drive the library into a code path it was never meant to reach. Because nghttp2 is widely used as a low-level HTTP/2 implementation, even a crash-only flaw can ripple into proxies, clients, gateways, and embedded services that depend on it. nghttp2’s own security history shows that the project has repeatedly had to harden protocol edge cases after real-world abuse of HTTP/2 behavior, which makes this latest issue part of a familiar and still highly relevant class of risk. /github.com/nghttp2/nghttp2/security)
nghttp2 is one of the most important C libraries in the HTTP/2 ecosystem, used directly by applications and indirectly through stacks that embed it for transport handling. Its role is deceptively simple on paper: parse frames, track session state, and keep a connection aligned with the HTTP/2 specification. In reality, that means it sits on the front line of hostile network input, which is exactly where logic mistakes and missing validations become security issues. The fact that the CVE description explicitly calls out an assertion failure suggests the bug is not a memory-safety corruption in the classic sense, but rather a fail-fast condition that can still be weaponized into service disruption.
That distinction matters. An assertion failure often indicates a code path where the developer assumed the input or the internal state machine could never reach a certain condition, and then the network proved otherwise. In a protocol library, that can be enough to take down a process, restart containers, or knock a reverse proxy out of rotation. For enterprises, the operational impact can be just as serious as a more obviously dangerous memory bug, especially if the affected component is shared across many services.
There is also an important historical context here. nghttp2 has previously shipped fixes for protocol-level denial of service, including excessive CPU usage from unbounded CONTINUATION frames in CVE-2024-28182, and the project’s security pages show a pattern of hardening around invalid frame handling, stream errors, and “glitch” conditions. That history tells us the project is not new to adversarial HTTP/2 traffic; rather, it is part of a long-running battle to make the implementation more defensive without breaking compatibility. CVE-2026-27135 fits squarely into that story.
nghttp2’s public documentation and release history show a steady evolution toward stricter input handling. The project has introduced logic such as invalid-frame callbacks, state-aware error handling, and protections against suspicious “glitch” behavior, including cases where frames arrive for streams that no longer exist. Those changes are a clue that the library’s maintainers understand how fragile protocol state can be under malicious input, and they have been steadily tightening those guardrails over time.
The broader industry has also learned, repeatedly, that HTTP/2 abuse is not theoretical. Over the last few years, attackers have shown how to exploit protocol assumptions to force excessive resource use, trigger abnormal state transitions, or overwhelm servers with malformed traffic. nghttp2’s own CVE-2024-28182 is a good example: a limit problem became a CPU exhaustion vulnerability because the library kept reading frames longer than it should have. CVE-2026-27135 appears to belong to the same family of “the protocol engine trusted the state too much” weaknesses.
This is typically not the kind of bug that requires elaborate exploit chains. The attacker’s job is to shape traffic until the parser or callback handler crosses the invalid boundary. If the assertion fires, the result is often immediate process termination. For servers, that can translate into dropped connections, autoscaling churn, and service interruptions that are visible long before anyone identifies the exact CVE.
The second question is whether the crash is ephemeral or persistent. In many modern deployments, automatic restarts blur that line. A service that crashes repeatedly under attack can be just as bad as one that stays down, because it consumes orchestration resources, triggers alert fatigue, and may create cascading instability elsewhere in the stack. That is why even “mere” denial-of-service issues in foundational libraries deserve immediate attention.
That matters because attackers tend to reuse successful classes of bugs. Once they know a particular protocol stack can be driven into abnormal behavior with malformed sequences, they will keep probing for the next validation gap. Security work in libraries like nghttp2 is therefore cumulative: every fix closes one route, but it also teaches the ecosystem what kinds of assumptions are dangerous.
Because Microsoft’s page is unavailable, operators should not wait for a polished summary before taking action. In security operations, missing metadata is not the same as missing risk. If the upstream project or downstream vendor has released patched binaries, they should be prioritized just as aggressively as a more fully documented bulletin.
This is also a reminder that network libraries deserve the same operational respect as kernel components. A flaw in the packet-processing layer can be every bit as disruptive as a memory-safety issue if it sits on a critical traffic path. In modern software stacks, availability is security, and denial-of-service bugs in shared protocol code should be treated accordingly.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
nghttp2 is one of the most important C libraries in the HTTP/2 ecosystem, used directly by applications and indirectly through stacks that embed it for transport handling. Its role is deceptively simple on paper: parse frames, track session state, and keep a connection aligned with the HTTP/2 specification. In reality, that means it sits on the front line of hostile network input, which is exactly where logic mistakes and missing validations become security issues. The fact that the CVE description explicitly calls out an assertion failure suggests the bug is not a memory-safety corruption in the classic sense, but rather a fail-fast condition that can still be weaponized into service disruption.That distinction matters. An assertion failure often indicates a code path where the developer assumed the input or the internal state machine could never reach a certain condition, and then the network proved otherwise. In a protocol library, that can be enough to take down a process, restart containers, or knock a reverse proxy out of rotation. For enterprises, the operational impact can be just as serious as a more obviously dangerous memory bug, especially if the affected component is shared across many services.
There is also an important historical context here. nghttp2 has previously shipped fixes for protocol-level denial of service, including excessive CPU usage from unbounded CONTINUATION frames in CVE-2024-28182, and the project’s security pages show a pattern of hardening around invalid frame handling, stream errors, and “glitch” conditions. That history tells us the project is not new to adversarial HTTP/2 traffic; rather, it is part of a long-running battle to make the implementation more defensive without breaking compatibility. CVE-2026-27135 fits squarely into that story.
Why “missing state validation” is a big deal
State validation is the difference between a parser and a panic. In a mature protocol stack, every inbound frame should be checked against the current session state, stream state, and connection lifecycle before any action is taken. If that validation is incomplete, an attacker can feed the library a sequence that looks absurd to a human but still traverses a code path that was assumed unreachable. That is the sort of bug that turns edge cases into outages.Why an assertion can still be a security issue
It is tempting to dismiss assertion failures as “just crashes,” but that underestimates their operational impact. In daemonized infrastructure, a crash often means automatic restart loops, failed health checks, degraded failover, and cascading load on the remaining fleet. In some environments, repeated process restarts are enough to create a denial-of-service even without memory corruption or code execution. This is especially true when a shared service like a proxy or ingress controller is the crash target.Background
HTTP/2’s architecture is powerful, but its state machine is also complicated. It multiplexes streams, tracks flow control, and allows extensions and callback-driven handling at several layers. That design makes it efficient, but it also creates many opportunities for subtle validation bugs. Libraries like nghttp2 have to interpret malformed or adversarial traffic without falling into inconsistent internal states, and every added callback or error path increases the surface area.nghttp2’s public documentation and release history show a steady evolution toward stricter input handling. The project has introduced logic such as invalid-frame callbacks, state-aware error handling, and protections against suspicious “glitch” behavior, including cases where frames arrive for streams that no longer exist. Those changes are a clue that the library’s maintainers understand how fragile protocol state can be under malicious input, and they have been steadily tightening those guardrails over time.
The broader industry has also learned, repeatedly, that HTTP/2 abuse is not theoretical. Over the last few years, attackers have shown how to exploit protocol assumptions to force excessive resource use, trigger abnormal state transitions, or overwhelm servers with malformed traffic. nghttp2’s own CVE-2024-28182 is a good example: a limit problem became a CPU exhaustion vulnerability because the library kept reading frames longer than it should have. CVE-2026-27135 appears to belong to the same family of “the protocol engine trusted the state too much” weaknesses.
What makes nghttp2 especially important
Unlike a consumer-facing app where a crash affects only a single endpoint, a protocol library can sit deep inside an entire software stack. It may be embedded in load balancers, API gateways, language runtimes, command-line tools, and security appliances. That means a single library-level flaw can propagate to many products, each with different patch cycles and deployment constraints. In other words, the exposure is often much larger than the vulnerability’s headline description suggests.Why Microsoft’s listing matters even when the page is missing
A Microsoft Security Update Guide entry usually means the vulnerability has been recognized as relevant to Microsoft’s products or packaged dependencies, even if Microsoft is not the upstream author. When a page is unavailable, the practical task becomes correlating the CVE with upstream release notes, advisories, and package metadata. That is why upstream sources such as nghttp2’s own security pages remain the most useful anchor for understanding risk.Likely Technical Shape of the Bug
The wording “assertion failure due to the missing state validation” strongly suggests a code path where a received frame or event was not checked against the current session state before a downstream assumption was made. In protocol libraries, that often means a condition like “this stream must exist,” “this frame type must be legal here,” or “this transition should only happen after X.” If the guard is missing, a crafted input sequence can force the library into an impossible branch.This is typically not the kind of bug that requires elaborate exploit chains. The attacker’s job is to shape traffic until the parser or callback handler crosses the invalid boundary. If the assertion fires, the result is often immediate process termination. For servers, that can translate into dropped connections, autoscaling churn, and service interruptions that are visible long before anyone identifies the exact CVE.
State machine bugs are often low-complexity, high-leverage
The most dangerous thing about a state machine bug is how ordinary it can look from the outside. There may be no heap spray, no buffer overflow, and no obvious memory corruption. Instead, the attacker uses legal-looking frames in the wrong order, or legally formatted frames after a terminal state, to trigger a code path that should have been rejected. That is why protocol state validation is so critical in every layer of the HTTP/2 stack.Assertions as a design smell
Assertions are valuable during development, but in security-sensitive network code they can also be a warning sign. They often reflect invariants that are expected, not enforced. If malformed traffic can reach them, then the implementation has trusted a state transition too much. The broader lesson is that protocols need explicit rejection paths, not just debug-time assumptions.Impact on Servers and Infrastructure
For operators, the first question is simple: can a remote attacker knock over a service that depends on nghttp2? Based on the description, the answer is very likely yes, at least for affected versions and configurations. If the vulnerable code runs in a network-facing process, a single crash may be enough to interrupt traffic, especially if the process is not isolated behind a robust failover layer.The second question is whether the crash is ephemeral or persistent. In many modern deployments, automatic restarts blur that line. A service that crashes repeatedly under attack can be just as bad as one that stays down, because it consumes orchestration resources, triggers alert fatigue, and may create cascading instability elsewhere in the stack. That is why even “mere” denial-of-service issues in foundational libraries deserve immediate attention.
Enterprise exposure
Enterprises are most exposed when nghttp2 is embedded in shared infrastructure. Reverse proxies, service meshes, API gateways, and custom middleware can all magnify the blast radius of a library crash. In those environments, a single malformed connection may not just affect one application; it can disrupt whole segments of traffic.Consumer exposure
Consumers are less likely to notice nghttp2 by name, but they may still be affected through apps that embed it. Command-line tools, desktop clients, and update mechanisms can all rely on HTTP/2 libraries under the hood. For those users, the impact is usually indirect: failed downloads, aborted connections, or an app that suddenly exits when handling a hostile endpoint.Why This Vulnerability Looks Familiar
nghttp2 has dealt with security issues that show a recurring pattern: protocol-level edge cases become denial-of-service vectors when the implementation cannot fully constrain parser behavior. CVE-2024-28182, for example, involved excessive CPU usage from unbounded CONTINUATION frames, and the project’s later releases added more defensive logic around invalid frames and suspicious stream behavior. CVE-2026-27135 feels like the next step in that same progression, only this time the problem seems to be a missing state gate rather than a volume issue.That matters because attackers tend to reuse successful classes of bugs. Once they know a particular protocol stack can be driven into abnormal behavior with malformed sequences, they will keep probing for the next validation gap. Security work in libraries like nghttp2 is therefore cumulative: every fix closes one route, but it also teaches the ecosystem what kinds of assumptions are dangerous.
A pattern of defensive evolution
The nghttp2 project’s documentation shows an implementation that has steadily grown more defensive, with improved invalid-frame handling and clearer semantics around terminal states. That is exactly what you would expect from a mature protocol library responding to real-world adversarial traffic. The downside is that every new guard can reveal a neighboring guard that was still missing.Why old lessons still apply
The lesson from earlier HTTP/2 incidents is that “valid enough to parse” is not the same as “valid enough to process.” State transition enforcement must happen before the rest of the stack touches the input. Otherwise, the parser becomes the attacker’s control surface.What Administrators Should Do Now
The immediate action is to identify whether any deployed software ships nghttp2 directly or bundles it transitively. That includes proxies, application servers, client tools, and language runtime packages. If the library is present, the next step is to check vendor advisories, distro backports, and package changelogs for a fixed release or patched build.Because Microsoft’s page is unavailable, operators should not wait for a polished summary before taking action. In security operations, missing metadata is not the same as missing risk. If the upstream project or downstream vendor has released patched binaries, they should be prioritized just as aggressively as a more fully documented bulletin.
Practical triage steps
- Inventory every application and appliance that depends on nghttp2 directly or indirectly.
- Check package manager changelogs and vendor advisories for a CVE-2026-27135 fix.
- Patch or rebuild affected systems as soon as a fixed release is available.
- Restart network-facing services to ensure the patched library is actually in memory.
- Monitor for connection resets, process crashes, and unusual HTTP/2 traffic during rollout.
When to treat it as urgent
If nghttp2 sits on the edge of your environment, behind a public load balancer, or inside a service that processes untrusted client traffic, this should be treated as urgent. If the component is only used in a controlled internal toolchain, the exposure is lower, but patching should still follow the next standard maintenance window.Strengths and Opportunities
The upside of a vulnerability disclosure like this is that it gives defenders a clear forcing function. Libraries such as nghttp2 are foundational enough that one fix can lift the security baseline across many products at once. It also reminds vendors that protocol code needs relentless validation, not just correctness under ideal conditions.- Better hardening of HTTP/2 state machines across the stack.
- Clearer vendor patch cycles for downstream products that embed nghttp2.
- Improved fuzzing and regression testing around invalid frame sequences.
- Stronger separation between debug assumptions and runtime safety checks.
- Opportunity for operators to inventory hidden dependencies in network services.
- More defensive defaults in future nghttp2 releases and related libraries.
- A chance to reduce crash-only failure modes in exposed services.
Risks and Concerns
The biggest concern is that a crash-only bug can still have wide operational impact, especially in containerized environments that auto-restart services and amplify failure loops. A second concern is that users may underestimate the issue because it sounds less severe than a memory corruption flaw. That would be a mistake, because availability attacks can be devastating when they hit the right infrastructure layer.- Remote denial of service against exposed services.
- Restart loops that create repeated outages rather than a single failure.
- Transitive exposure through third-party software bundles and distro packages.
- Slow patch adoption in appliances and long-lived enterprise systems.
- Hidden blast radius when a shared library supports many services.
- False confidence if teams assume an assertion failure is “only a crash.”
- Potentially incomplete vendor visibility while the Microsoft page remains unavailable.
Looking Ahead
The next few days will likely determine how broad the impact becomes. The key signals to watch are upstream release notes from nghttp2, downstream distro advisories, and any Microsoft or partner update that fills in the missing detail on the CVE record. If the issue is already patched upstream, the real story may shift quickly from “what happened?” to “who has not yet deployed the fix?”This is also a reminder that network libraries deserve the same operational respect as kernel components. A flaw in the packet-processing layer can be every bit as disruptive as a memory-safety issue if it sits on a critical traffic path. In modern software stacks, availability is security, and denial-of-service bugs in shared protocol code should be treated accordingly.
What to watch next
- A fixed nghttp2 release or confirmed downstream backport.
- Updated Microsoft advisory content replacing the unavailable page.
- Distro package advisories for Debian, Ubuntu, Red Hat, SUSE, and others.
- Reports from proxy and gateway vendors that bundle nghttp2.
- Evidence of active exploitation, if any, in public telemetry or incident reports.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: