Siemens Opcenter RDnL installations worldwide are affected by CVE-2026-27446, a high-severity Apache ActiveMQ Artemis authentication flaw republished by CISA on May 14, 2026, after Siemens ProductCERT’s May 12 advisory warned that all Opcenter RDnL versions are known affected. The bug is not a classic remote-code-execution headline-grabber, but it lands in a place industrial operators hate: the message broker. The practical risk is that an unauthenticated attacker on an adjacent network could coerce the broker into federating with a rogue broker, opening the door to disruption and message injection. Siemens’ answer is direct: update Apache Artemis to 2.52.0 or later, and harden the network path around the broker if patching cannot happen immediately.
The uncomfortable part of this advisory is that it does not depend on a flashy user-facing feature. CVE-2026-27446 lives in Apache ActiveMQ Artemis, the kind of middleware many organizations only think about when it stops working. In manufacturing environments, that makes it more dangerous, not less, because message brokers often sit between systems that assume the transport layer is boring, trusted, and already solved.
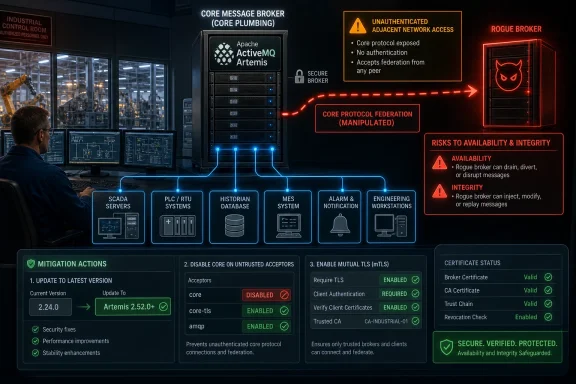
The flaw involves missing authentication around a critical function in the Core protocol. An attacker who can reach the broker from an adjacent network can use that protocol to force the target broker to establish an outbound Core federation connection to infrastructure the attacker controls. That rogue broker can then become part of the message flow in ways defenders did not intend.
In generic Apache terms, the issue can permit message injection into queues and, in some environments, message exfiltration. Siemens’ advisory narrows the impact for Opcenter RDnL, saying confidentiality impact is not present and integrity impact is low, partly because the affected message content does not contain confidential information and lacks automatic refresh behavior. But availability impact is rated high, and in industrial systems availability is rarely a secondary concern.
That distinction matters. A broker that can be manipulated into trusting the wrong peer may not expose secrets in this particular Siemens deployment, but it can still become an instrument for operational confusion. False or malformed messages do not need to contain confidential data to cause trouble; they only need to arrive where software expects meaningful operational state.
In office IT, “adjacent network” can sound reassuring. In industrial environments, it should not. Many manufacturing networks contain layered zones, jump hosts, vendor appliances, legacy segmentation, and plant-floor systems that have accumulated over years. Once an attacker has compromised a workstation, remote-access box, engineering station, or poorly isolated service, “adjacent” may be a much smaller leap than the network diagram suggests.
The advisory also says exploitation depends on two conditions. The broker must accept incoming Core protocol connections from untrusted sources, and it must be able to make outbound Core protocol connections to untrusted targets. That is more restrictive than a universal unauthenticated bug, but it is not exotic. Defaults matter here, and Siemens notes that incoming Core protocol connections are supported by default through the “artemis” acceptor listening on port 61616 unless protocols are explicitly constrained.
This is where industrial cybersecurity gets messy. A configuration that is technically “not exposed to the internet” can still be reachable from too many internal places. A protocol that was left enabled because it helped interoperability can become the path through which a trusted broker is made to trust the wrong counterpart.
Opcenter RDnL sits in Siemens’ broader manufacturing software portfolio, which means the affected environments are not hobbyist deployments or casual lab setups. These are systems used in critical manufacturing, deployed worldwide, with the predictable mix of uptime pressure, change-control requirements, and vendor coordination that makes patching slower than anyone likes to admit.
The temptation in these situations is to downgrade the urgency because the vendor says the integrity impact is low and confidentiality is not affected in this implementation. That would be a mistake. Availability impact is rated high, and the advisory’s own attack description involves a broker being forced into an outbound federation relationship. If the wrong messages can be injected or message handling can be disrupted, production systems may experience effects that do not map neatly to conventional data-loss language.
This is the recurring lesson of software supply chain risk in industrial environments. A vulnerability in a general-purpose open-source component becomes an ICS advisory because the component is embedded in a product that operators treat as part of the production stack. The flaw is not “in the factory” in the old embedded-controller sense, but the consequence can still arrive at the factory floor.
That is why the remediation language focuses so heavily on protocol exposure and federation packets. Siemens recommends, among other mitigations, implementing a Core interceptor to deny Core downstream federation connect packets. The advisory identifies those packets by type value, which is a useful operational clue for teams that need a compensating control before they can update.
The more strategic mitigation is to remove Core protocol support from any acceptor receiving connections from untrusted sources. That is the kind of hardening step that sounds simple until administrators inspect real configurations and discover how many clients, services, or scripts assumed that the acceptor would support everything. An acceptor URL without a protocols parameter supports all protocols by default, including Core, which is convenient during deployment and hazardous during an incident review.
The strongest network-level mitigation is two-way SSL with certificate-based client authentication. That changes the sequence of trust: a client must present the proper certificate before the message protocol handshake begins. In other words, the broker stops listening to anonymous protocol claims and starts requiring identity at the connection layer.
Many Opcenter RDnL deployments will sit inside environments where patch timing is bound to production schedules, validation requirements, and vendor support obligations. Administrators may need to determine whether Artemis is bundled, separately managed, or controlled through Siemens’ update process. That distinction matters because replacing a component manually can create support risk even when it addresses the security risk.
This is why the mitigations are more than boilerplate. Removing Core from untrusted acceptors, adding an interceptor, and enforcing mutual TLS are not replacements for patching, but they can narrow the exploit path while change control catches up. In many plants, the right answer will be phased: immediately restrict network paths and broker protocols, then apply the fixed component version during the next approved window.
The important operational move is to avoid treating the patch and the mitigations as mutually exclusive. A patched broker with excessive protocol exposure remains a future problem waiting for a different CVE. A hardened broker running a vulnerable version remains a temporary compromise. The mature response is to do both, in the order the plant can safely execute.
The advisory is also notable because CISA explicitly describes it as a verbatim republication of Siemens’ CSAF advisory. That matters because the most precise technical language comes from Siemens and Apache rather than from an independent CISA investigation. CISA’s role here is amplification, normalization, and distribution to the ICS community.
That amplification has real value. Industrial operators often miss vendor advisories buried in product portals, especially when a vulnerability originates in a third-party component. CISA republication turns the issue into something vulnerability managers can track through familiar channels, even if the remediation still requires Siemens-specific product knowledge.
It also raises the stakes for accurate scoping. Because all Opcenter RDnL versions are listed as known affected, administrators should assume exposure until they can prove otherwise through component version checks and configuration review. In industrial security, “we do not think we use that feature” is not the same as “the protocol is disabled and the broker cannot make outbound connections to untrusted destinations.”
For years, many internal systems have been configured as though the network perimeter would do the authentication work. If a client could reach the broker, it was probably supposed to be there. If a broker made an outbound connection, the network probably allowed it because internal egress controls were seen as optional complexity.
CVE-2026-27446 punishes that assumption. It shows how a feature designed for broker-to-broker federation can become a route for unauthorized influence when authentication and egress discipline are weak. The attacker does not need to own the whole plant; they need to be in the right network position and find a broker that will talk too freely.
This is especially relevant for Windows-heavy operations teams because the broker may not be the system they monitor most closely. Windows event logs, endpoint detection, domain telemetry, and patch management dashboards can all look healthy while a Java messaging component quietly exposes a protocol path. The defensive lens has to widen beyond the machines users log into.
Message injection can manifest as bad data, unexpected commands, duplicate work, queue pollution, or application-level errors. The precise effect depends on how Opcenter RDnL uses the broker and how downstream components validate messages. If receiving systems assume messages are trustworthy because they arrived through the broker, a rogue federation path can undermine that assumption.
Availability impact is the louder warning. Brokers are centralizing points by design. If they become unstable, overloaded, or semantically polluted, multiple dependent services can suffer at once. That is why the CVSS vector’s high availability impact deserves more attention than the absence of confidentiality impact.
In security programs shaped by breach notification law, data theft often gets the boardroom attention. In factories, loss of control, loss of visibility, or loss of confidence in system state can be just as urgent. CVE-2026-27446 belongs in that second category: it is a trust and availability problem in the nervous system of an industrial application.
This is not a call to scan a production network recklessly. ICS environments require care, and active scanning can have side effects. But passive flow analysis, firewall rule review, configuration inspection, and vendor-supported discovery can all provide meaningful answers without poking fragile systems unnecessarily.
The outbound side is easy to overlook. Many vulnerability checks focus on what can reach a service from the outside. Here, the forced federation scenario also depends on where the broker can go. Egress filtering, allowlists, and segmentation between production zones can turn a theoretical rogue-broker path into a blocked connection attempt.
Administrators should also review whether mutual TLS is already in place and whether certificates are actually required from clients. TLS without client authentication may protect traffic from casual observation, but it does not by itself prove that the connecting client is authorized to participate in broker operations. The advisory is clear that certificate-based authentication is the control that prevents unauthenticated exploitation before the message protocol handshake.
The dependency problem is not unique to Siemens. Open-source infrastructure components are everywhere in commercial software because they solve hard problems well. ActiveMQ Artemis is a serious message broker, not a fringe dependency. The issue is that when a component vulnerability appears, responsibility becomes distributed across Apache, the commercial vendor, the integrator, and the asset owner.
That distribution slows response. Apache can publish a fixed version, Siemens can issue guidance, CISA can republish the advisory, and the plant still has to execute the change safely. Each handoff introduces delay, and each delay creates a window in which attackers can read the same advisory defenders are reading.
A better program treats advisories like this as tests of operational muscle. Can the organization identify affected deployments? Can it determine whether Core is exposed to untrusted sources? Can it confirm outbound broker restrictions? Can it deploy a component update without breaking support? If the answer to any of those questions is “not quickly,” then the vulnerability has already taught a useful lesson.
The reason the advice repeats is that the same architectural weaknesses keep making product vulnerabilities worse. Flat networks magnify adjacent-network bugs. Permissive firewall rules magnify protocol bugs. Weak remote access turns a vulnerability that should require local positioning into one reachable through a contractor laptop or neglected appliance.
VPNs are not magic either. CISA’s reminder that VPNs must be updated and are only as secure as connected devices is especially relevant in manufacturing. A remote-access path used for maintenance can become the bridge that turns an external compromise into adjacent access near a broker.
The right posture is layered. Patch the vulnerable component, restrict the Core protocol, require mutual authentication, constrain outbound federation paths, monitor broker behavior, and review the segmentation that decides who can speak to the broker in the first place. None of those steps is individually glamorous; together, they are the difference between a product advisory and an incident.
That knowledge makes the advisory actionable. If a broker should never federate outbound, block it and alert on attempts. If it should federate only with named peers, enforce that in firewall policy and certificates. If Core is not required on an untrusted-facing acceptor, remove it rather than relying on obscurity.
For WindowsForum readers, there is a broader lesson in the Windows-adjacent reality of industrial IT. The visible endpoints may be Windows workstations, Windows servers, Active Directory accounts, and familiar management consoles. But the operational dependency graph often includes Java services, Linux appliances, broker clusters, and vendor-managed middleware. Security teams that stop at the Windows estate will miss the connective tissue.
This advisory is therefore less about one Siemens product than about the assumptions around internal messaging. Modern industrial software is distributed software. Distributed software needs authenticated, least-privilege communication between components. If a message broker is treated as a trusted room where anyone inside can speak, attackers will eventually learn to speak the protocol.
Siemens Opcenter RDnL operators should patch, but they should also use CVE-2026-27446 as a forcing function to re-check the architecture around messaging, federation, and industrial segmentation. The next serious flaw may not arrive through Artemis, and it may not carry the same clean mitigation language. Environments that know their brokers, constrain their protocols, and authenticate their internal traffic will be better positioned not only for this advisory, but for the next dependency bug that turns invisible middleware into the front line.
Source: CISA Siemens Opcenter RDnL | CISA
 The Vulnerability Is in the Plumbing, Not the Dashboard
The Vulnerability Is in the Plumbing, Not the Dashboard
The uncomfortable part of this advisory is that it does not depend on a flashy user-facing feature. CVE-2026-27446 lives in Apache ActiveMQ Artemis, the kind of middleware many organizations only think about when it stops working. In manufacturing environments, that makes it more dangerous, not less, because message brokers often sit between systems that assume the transport layer is boring, trusted, and already solved.The flaw involves missing authentication around a critical function in the Core protocol. An attacker who can reach the broker from an adjacent network can use that protocol to force the target broker to establish an outbound Core federation connection to infrastructure the attacker controls. That rogue broker can then become part of the message flow in ways defenders did not intend.
In generic Apache terms, the issue can permit message injection into queues and, in some environments, message exfiltration. Siemens’ advisory narrows the impact for Opcenter RDnL, saying confidentiality impact is not present and integrity impact is low, partly because the affected message content does not contain confidential information and lacks automatic refresh behavior. But availability impact is rated high, and in industrial systems availability is rarely a secondary concern.
That distinction matters. A broker that can be manipulated into trusting the wrong peer may not expose secrets in this particular Siemens deployment, but it can still become an instrument for operational confusion. False or malformed messages do not need to contain confidential data to cause trouble; they only need to arrive where software expects meaningful operational state.
A High-Severity Score Hides a Very Industrial Kind of Risk
The CVSS 3.1 score of 7.1 places the vulnerability in the high-severity band, with adjacent-network attack vector, low complexity, no privileges required, and no user interaction. That is a profile administrators should recognize immediately: not internet-wormable in the broadest sense, but dangerous once an attacker is inside or near the operational network.In office IT, “adjacent network” can sound reassuring. In industrial environments, it should not. Many manufacturing networks contain layered zones, jump hosts, vendor appliances, legacy segmentation, and plant-floor systems that have accumulated over years. Once an attacker has compromised a workstation, remote-access box, engineering station, or poorly isolated service, “adjacent” may be a much smaller leap than the network diagram suggests.
The advisory also says exploitation depends on two conditions. The broker must accept incoming Core protocol connections from untrusted sources, and it must be able to make outbound Core protocol connections to untrusted targets. That is more restrictive than a universal unauthenticated bug, but it is not exotic. Defaults matter here, and Siemens notes that incoming Core protocol connections are supported by default through the “artemis” acceptor listening on port 61616 unless protocols are explicitly constrained.
This is where industrial cybersecurity gets messy. A configuration that is technically “not exposed to the internet” can still be reachable from too many internal places. A protocol that was left enabled because it helped interoperability can become the path through which a trusted broker is made to trust the wrong counterpart.
Siemens’ Product Impact Is Broad Because the Dependency Is Broad
The affected product list is terse: Siemens Opcenter RDnL, all versions. That wording is significant. It means defenders should not waste time trying to find a minor release that escapes the advisory unless Siemens separately clarifies otherwise. The vulnerable component is inherited through the product’s dependency on Apache ActiveMQ Artemis, and the remediation points at the component version rather than a narrow application hotfix.Opcenter RDnL sits in Siemens’ broader manufacturing software portfolio, which means the affected environments are not hobbyist deployments or casual lab setups. These are systems used in critical manufacturing, deployed worldwide, with the predictable mix of uptime pressure, change-control requirements, and vendor coordination that makes patching slower than anyone likes to admit.
The temptation in these situations is to downgrade the urgency because the vendor says the integrity impact is low and confidentiality is not affected in this implementation. That would be a mistake. Availability impact is rated high, and the advisory’s own attack description involves a broker being forced into an outbound federation relationship. If the wrong messages can be injected or message handling can be disrupted, production systems may experience effects that do not map neatly to conventional data-loss language.
This is the recurring lesson of software supply chain risk in industrial environments. A vulnerability in a general-purpose open-source component becomes an ICS advisory because the component is embedded in a product that operators treat as part of the production stack. The flaw is not “in the factory” in the old embedded-controller sense, but the consequence can still arrive at the factory floor.
The Core Protocol Becomes the Trust Boundary
Apache ActiveMQ Artemis supports multiple protocols, and the Core protocol is its native wire protocol. Federation, meanwhile, is a legitimate feature that lets brokers exchange messages across deployments. The vulnerability turns that useful capability into a trust-boundary problem: if the broker can be induced to federate with an attacker-controlled broker without proper authentication, the attacker has found a way to insert themselves into a system designed for reliable message movement.That is why the remediation language focuses so heavily on protocol exposure and federation packets. Siemens recommends, among other mitigations, implementing a Core interceptor to deny Core downstream federation connect packets. The advisory identifies those packets by type value, which is a useful operational clue for teams that need a compensating control before they can update.
The more strategic mitigation is to remove Core protocol support from any acceptor receiving connections from untrusted sources. That is the kind of hardening step that sounds simple until administrators inspect real configurations and discover how many clients, services, or scripts assumed that the acceptor would support everything. An acceptor URL without a protocols parameter supports all protocols by default, including Core, which is convenient during deployment and hazardous during an incident review.
The strongest network-level mitigation is two-way SSL with certificate-based client authentication. That changes the sequence of trust: a client must present the proper certificate before the message protocol handshake begins. In other words, the broker stops listening to anonymous protocol claims and starts requiring identity at the connection layer.
The Patch Is Clear; the Change Window Is Not
Apache has released a fixed version, and Siemens recommends updating to Apache Artemis 2.52.0 or later. In a purely IT environment, the next step would be obvious: inventory, test, deploy, verify. In manufacturing, the same words apply, but every verb costs more.Many Opcenter RDnL deployments will sit inside environments where patch timing is bound to production schedules, validation requirements, and vendor support obligations. Administrators may need to determine whether Artemis is bundled, separately managed, or controlled through Siemens’ update process. That distinction matters because replacing a component manually can create support risk even when it addresses the security risk.
This is why the mitigations are more than boilerplate. Removing Core from untrusted acceptors, adding an interceptor, and enforcing mutual TLS are not replacements for patching, but they can narrow the exploit path while change control catches up. In many plants, the right answer will be phased: immediately restrict network paths and broker protocols, then apply the fixed component version during the next approved window.
The important operational move is to avoid treating the patch and the mitigations as mutually exclusive. A patched broker with excessive protocol exposure remains a future problem waiting for a different CVE. A hardened broker running a vulnerable version remains a temporary compromise. The mature response is to do both, in the order the plant can safely execute.
CISA’s Republication Turns a Vendor Advisory Into a Public Signal
CISA’s May 14 republication of Siemens ProductCERT SSA-085541 does not necessarily mean the vulnerability is being exploited in the wild. It does mean the issue has crossed the threshold for broad industrial-control visibility. For defenders, that changes the audience: what was a vendor advisory is now a public item that asset owners, auditors, insurers, and attackers can all read.The advisory is also notable because CISA explicitly describes it as a verbatim republication of Siemens’ CSAF advisory. That matters because the most precise technical language comes from Siemens and Apache rather than from an independent CISA investigation. CISA’s role here is amplification, normalization, and distribution to the ICS community.
That amplification has real value. Industrial operators often miss vendor advisories buried in product portals, especially when a vulnerability originates in a third-party component. CISA republication turns the issue into something vulnerability managers can track through familiar channels, even if the remediation still requires Siemens-specific product knowledge.
It also raises the stakes for accurate scoping. Because all Opcenter RDnL versions are listed as known affected, administrators should assume exposure until they can prove otherwise through component version checks and configuration review. In industrial security, “we do not think we use that feature” is not the same as “the protocol is disabled and the broker cannot make outbound connections to untrusted destinations.”
The Real Failure Mode Is Implicit Trust
The most revealing line in the advisory is not the CVSS score. It is the condition that the broker must allow incoming Core protocol connections from untrusted sources and outgoing Core protocol connections to untrusted targets. That sentence describes a broken trust model more than it describes a single software bug.For years, many internal systems have been configured as though the network perimeter would do the authentication work. If a client could reach the broker, it was probably supposed to be there. If a broker made an outbound connection, the network probably allowed it because internal egress controls were seen as optional complexity.
CVE-2026-27446 punishes that assumption. It shows how a feature designed for broker-to-broker federation can become a route for unauthorized influence when authentication and egress discipline are weak. The attacker does not need to own the whole plant; they need to be in the right network position and find a broker that will talk too freely.
This is especially relevant for Windows-heavy operations teams because the broker may not be the system they monitor most closely. Windows event logs, endpoint detection, domain telemetry, and patch management dashboards can all look healthy while a Java messaging component quietly exposes a protocol path. The defensive lens has to widen beyond the machines users log into.
Message Injection Is Not Harmless Just Because the Data Is Not Secret
Siemens’ note that the message content does not contain confidential information is important, but it should not lull operators into complacency. Confidentiality is only one leg of the security stool. Integrity and availability are often more consequential in manufacturing, where a bad state transition or delayed workflow can have business impact without leaking a single secret.Message injection can manifest as bad data, unexpected commands, duplicate work, queue pollution, or application-level errors. The precise effect depends on how Opcenter RDnL uses the broker and how downstream components validate messages. If receiving systems assume messages are trustworthy because they arrived through the broker, a rogue federation path can undermine that assumption.
Availability impact is the louder warning. Brokers are centralizing points by design. If they become unstable, overloaded, or semantically polluted, multiple dependent services can suffer at once. That is why the CVSS vector’s high availability impact deserves more attention than the absence of confidentiality impact.
In security programs shaped by breach notification law, data theft often gets the boardroom attention. In factories, loss of control, loss of visibility, or loss of confidence in system state can be just as urgent. CVE-2026-27446 belongs in that second category: it is a trust and availability problem in the nervous system of an industrial application.
The Default Port Is a Clue for Hunters
The advisory’s reference to the default “artemis” acceptor on port 61616 gives defenders a concrete place to start. Asset teams should identify systems listening on that port, determine whether those listeners are part of Opcenter RDnL deployments, and inspect whether the Core protocol is enabled. Network teams should also check whether those systems can initiate outbound Core connections beyond tightly defined broker peers.This is not a call to scan a production network recklessly. ICS environments require care, and active scanning can have side effects. But passive flow analysis, firewall rule review, configuration inspection, and vendor-supported discovery can all provide meaningful answers without poking fragile systems unnecessarily.
The outbound side is easy to overlook. Many vulnerability checks focus on what can reach a service from the outside. Here, the forced federation scenario also depends on where the broker can go. Egress filtering, allowlists, and segmentation between production zones can turn a theoretical rogue-broker path into a blocked connection attempt.
Administrators should also review whether mutual TLS is already in place and whether certificates are actually required from clients. TLS without client authentication may protect traffic from casual observation, but it does not by itself prove that the connecting client is authorized to participate in broker operations. The advisory is clear that certificate-based authentication is the control that prevents unauthenticated exploitation before the message protocol handshake.
Patch Management Needs a Dependency Map, Not a Spreadsheet Ritual
The Siemens advisory is another reminder that industrial software inventories need to capture embedded components, not just product names. “We run Opcenter RDnL” is useful, but insufficient. Defenders need to know which bundled libraries, brokers, runtimes, and services are inside the stack, and which team owns the process for updating them.The dependency problem is not unique to Siemens. Open-source infrastructure components are everywhere in commercial software because they solve hard problems well. ActiveMQ Artemis is a serious message broker, not a fringe dependency. The issue is that when a component vulnerability appears, responsibility becomes distributed across Apache, the commercial vendor, the integrator, and the asset owner.
That distribution slows response. Apache can publish a fixed version, Siemens can issue guidance, CISA can republish the advisory, and the plant still has to execute the change safely. Each handoff introduces delay, and each delay creates a window in which attackers can read the same advisory defenders are reading.
A better program treats advisories like this as tests of operational muscle. Can the organization identify affected deployments? Can it determine whether Core is exposed to untrusted sources? Can it confirm outbound broker restrictions? Can it deploy a component update without breaking support? If the answer to any of those questions is “not quickly,” then the vulnerability has already taught a useful lesson.
The ICS Advice Is Familiar Because It Still Has Not Been Fully Absorbed
CISA’s general recommendations are the usual ICS canon: minimize network exposure, avoid direct internet accessibility, put control systems behind firewalls, isolate them from business networks, and use secure remote access methods such as VPNs when needed. It is easy to skim past that language because it appears in so many advisories. That would be another mistake.The reason the advice repeats is that the same architectural weaknesses keep making product vulnerabilities worse. Flat networks magnify adjacent-network bugs. Permissive firewall rules magnify protocol bugs. Weak remote access turns a vulnerability that should require local positioning into one reachable through a contractor laptop or neglected appliance.
VPNs are not magic either. CISA’s reminder that VPNs must be updated and are only as secure as connected devices is especially relevant in manufacturing. A remote-access path used for maintenance can become the bridge that turns an external compromise into adjacent access near a broker.
The right posture is layered. Patch the vulnerable component, restrict the Core protocol, require mutual authentication, constrain outbound federation paths, monitor broker behavior, and review the segmentation that decides who can speak to the broker in the first place. None of those steps is individually glamorous; together, they are the difference between a product advisory and an incident.
The Siemens-Artemis Bug Rewards Teams That Know Their Message Flows
The most prepared organizations will not be the ones with the longest vulnerability spreadsheet. They will be the ones that understand how messages move through their environment. They will know which brokers exist, which applications publish and consume messages, which protocols are enabled, and which peer brokers are legitimate.That knowledge makes the advisory actionable. If a broker should never federate outbound, block it and alert on attempts. If it should federate only with named peers, enforce that in firewall policy and certificates. If Core is not required on an untrusted-facing acceptor, remove it rather than relying on obscurity.
For WindowsForum readers, there is a broader lesson in the Windows-adjacent reality of industrial IT. The visible endpoints may be Windows workstations, Windows servers, Active Directory accounts, and familiar management consoles. But the operational dependency graph often includes Java services, Linux appliances, broker clusters, and vendor-managed middleware. Security teams that stop at the Windows estate will miss the connective tissue.
This advisory is therefore less about one Siemens product than about the assumptions around internal messaging. Modern industrial software is distributed software. Distributed software needs authenticated, least-privilege communication between components. If a message broker is treated as a trusted room where anyone inside can speak, attackers will eventually learn to speak the protocol.
The Broker Fix That Should Move Before the Next Maintenance Window
The practical path is not mysterious, but it does require discipline. Teams should treat the Siemens advisory as both a patching task and a configuration audit, because the exploit path lives at the intersection of vulnerable code, enabled protocol support, and reachable network paths.- Organizations running Siemens Opcenter RDnL should assume all versions are affected until they verify the embedded Apache Artemis version and Siemens-supported remediation path.
- Administrators should plan an update to Apache Artemis 2.52.0 or later, while confirming whether Siemens packaging or support rules require a product-specific update process.
- Network and application teams should identify any Artemis acceptors exposed to untrusted or semi-trusted networks, especially services using the default port 61616.
- Broker configurations should be reviewed to remove Core protocol support where it is not required, particularly on acceptors that receive connections from less-trusted zones.
- Mutual TLS should be used where feasible so clients must authenticate with certificates before the broker processes message-protocol handshakes.
- Outbound broker connectivity should be restricted to known, approved peers so a forced federation attempt cannot reach an attacker-controlled system.
Siemens Opcenter RDnL operators should patch, but they should also use CVE-2026-27446 as a forcing function to re-check the architecture around messaging, federation, and industrial segmentation. The next serious flaw may not arrive through Artemis, and it may not carry the same clean mitigation language. Environments that know their brokers, constrain their protocols, and authenticate their internal traffic will be better positioned not only for this advisory, but for the next dependency bug that turns invisible middleware into the front line.
Source: CISA Siemens Opcenter RDnL | CISA