CVE-2026-34032 is a newly published Apache HTTP Server flaw in
The reported failure on Microsoft’s MSRC page — a dynamic JavaScript module refusing to load — is the kind of browser-side shrug that makes vulnerability management feel absurd. An admin goes looking for a CVE record, gets a
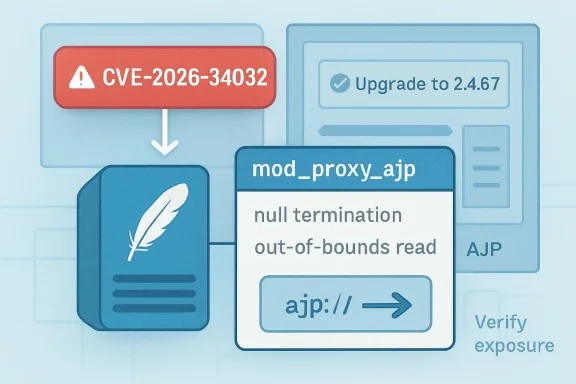
CVE-2026-34032 itself is not the kind of vulnerability that should cause emergency all-hands calls. Apache classifies it as low severity, and the public description points to an improper null-termination check leading to an out-of-bounds read in
But low severity is not the same thing as irrelevant. The affected range is broad — Apache HTTP Server through 2.4.66 — and the fix lands in 2.4.67. That matters because Apache remains deeply embedded in estates where Windows is only part of the story: reverse proxies in front of Java applications, load balancers terminating TLS, developer workstations, lab servers, appliances, bundled stacks, and third-party products that ship their own copy of httpd.
The headline lesson is not that Apache has another memory-safety blemish. The lesson is that modern Windows operations teams are often accountable for software supply chains they do not think of as “Windows,” and the tooling they use to track those chains is still more brittle than it should be.
That is the optimistic version. In the real world, AJP has a history of being enabled because a deployment guide once said so, left reachable because a firewall rule was copied forward, or buried inside a vendor appliance where the admin sees only a management GUI. That does not make every AJP flaw a fire drill, but it does mean “we don’t use that” is not a sufficient control.
CVE-2026-34032 is about string parsing. The phrase “missing null-termination check” sounds dry because it is dry, but it points to one of the oldest classes of C-language failure: code expects a string to be terminated in a safe, conventional way, and an input path fails to enforce that expectation before memory is read. The result, in this case, is described as a heap buffer over-read.
An over-read is not the same thing as a heap overflow. It typically means software reads beyond the intended boundary rather than writing attacker-controlled data past it. That distinction is why the vulnerability is being treated as low severity rather than a neat remote-code-execution story.
Still, confidentiality bugs have a way of becoming operationally annoying even when they are not spectacular. Depending on path, state, and surrounding code, an out-of-bounds read may leak adjacent memory, crash a process, or simply behave unpredictably. The public record for CVE-2026-34032 does not justify breathless claims of mass compromise, but it does justify a quiet maintenance window and a search through configurations.
This is why treating CVEs one at a time can be a trap. If a scanner highlights only CVE-2026-34032, an organization might decide to defer because the score is modest. If the same host is vulnerable to a cluster of Apache issues fixed in the same release, the patch decision looks different.
Security teams have become fluent in CVSS arithmetic, but package updates rarely arrive as single-CVE events. They arrive as bundles of parser fixes, module-specific hardening, regression repairs, and behavior changes. Apache 2.4.67 is not “the CVE-2026-34032 patch” so much as the current upstream corrective release for a web server branch that many organizations continue to rely on.
That distinction matters for WindowsForum readers because Apache on Windows often lives outside Microsoft’s neat update channels. If Apache was installed via a vendor package, XAMPP-like stack, developer toolchain, reverse proxy product, or custom service wrapper, Windows Update is not coming to save it. Microsoft’s portal may surface the CVE, but it will not patch a third-party Apache binary you dropped into
There is a narrow reading and a broader reading. The narrow reading is that a website broke, and refreshing later may fix it. The broader reading is that vulnerability data has become too important to be trapped behind fragile single-page-app behavior.
For individual users, that fragility is irritating. For security operations teams, it is a workflow hazard. Patch Tuesday already involves juggling vendor advisories, CVE records, scanner plugins, package repositories, and exceptions. If one of the major portals becomes intermittently unusable because of front-end asset loading, the process becomes less about risk and more about page archaeology.
To Microsoft’s credit, the MSRC Security Update Guide has become a central clearinghouse for Windows and Microsoft ecosystem security information. But CVE-2026-34032 shows the awkward edge of that model: a third-party Apache vulnerability can appear in the same search-and-triage universe as Windows flaws, while the authoritative remediation still lives upstream with Apache and downstream with operating system distributors.
That is not a reason to ignore MSRC. It is a reason not to make it your only source of truth.
The missing nuance is exposure. A vulnerable Apache build that does not load
This is where many vulnerability programs still stumble. They ingest the CVE, map it to a package version, assign a deadline, and only later ask whether the vulnerable code path is active. That order is understandable at scale, but it produces poor prioritization when the flaw sits in an optional module.
The better approach is not to dismiss the CVE because it is low severity. The better approach is to enrich it. Is
The uncomfortable truth is that many organizations cannot answer those questions quickly. They know they have Apache because a scanner says so. They do not know why it is there, who owns it, or what module set it is running. CVE-2026-34032 is modest, but it is a useful test of whether your asset inventory understands applications or merely recognizes version strings.
Low-severity memory bugs in infrastructure software are debt. One is manageable. Ten become a pattern. Fifty become the reason a routine upgrade turns into a brittle migration project because nobody has touched the stack in years.
Apache HTTP Server is particularly prone to this effect because it is stable, familiar, and often invisible when it works. It may sit in front of applications whose owners have changed twice. It may be pinned because a rewrite rule depends on old behavior. It may be bundled into a product where the vendor’s update cadence lags upstream.
That is why the right operational posture is boring but firm. If you are on Apache 2.4.66 or earlier, plan the move to 2.4.67 through your normal change process. If you cannot move because a vendor has not shipped an update, document the exposure and apply compensating controls around AJP. If the server does not need AJP, disable the module rather than merely accepting the version finding.
Patching low-severity infrastructure bugs is less about panic than hygiene. The organizations that handle these quietly are the same ones that move faster when a genuinely critical Apache issue arrives.
Apache HTTP Server sits firmly in the “everything else” bucket on Windows. It may run as a Windows service, but it is not serviced like IIS. It may protect Microsoft-hosted workloads, but Microsoft does not own its release cadence. It may appear in MSRC search results, but the fix is not a cumulative update.
That mismatch matters because Windows-centric organizations sometimes underestimate the amount of non-Microsoft code in their server estate. A Java application behind Apache, a PHP application on a legacy intranet host, a monitoring tool with embedded httpd, or a developer-installed stack can all create exposure that does not look like a Windows vulnerability at first glance.
The same is true in hybrid environments. A vulnerability may be discovered upstream, packaged by Debian, Ubuntu, Red Hat, Alpine, or another distributor, mirrored into containers, consumed by a vendor, and finally detected by an enterprise scanner. Somewhere in that chain, a Windows team may be asked why a Microsoft portal page is broken for an Apache CVE.
That is the state of enterprise IT in 2026: the operating system boundary is no longer the operational boundary. Windows admins do not need to become Apache core developers, but they do need to know where Apache exists, how it is updated, and whether AJP is part of the design.
The protocol’s history has already made admins wary. The 2020 “Ghostcat” vulnerability in Apache Tomcat’s AJP connector turned a once-obscure backend protocol into a board-level remediation item for some organizations. CVE-2026-34032 is not Ghostcat, and it should not be treated as though it is. But it benefits from the same lesson: backend protocols are only backend protocols if the network still treats them that way.
Apache’s
The danger is inertia. Once deployed, AJP configurations may persist through application migrations, firewall redesigns, virtualization moves, and cloud lift-and-shift projects. A server that began life as a carefully segmented reverse proxy may end up with broader reachability simply because nobody revisited the connector assumptions.
CVE-2026-34032 gives teams a reason to revisit those assumptions without the pressure of an active mass-exploitation crisis. That is a gift. It is much easier to remove an unnecessary AJP path during a low-severity patch cycle than during a weekend incident bridge.
But disabling a module is not a substitute for keeping Apache current. The same 2.4.67 release addresses more than this one AJP parsing bug. A server that remains on an older branch because today’s highlighted CVE is avoidable by configuration may still carry other flaws in modules that are active.
The practical sequence is straightforward. First, identify Apache instances and version levels. Second, determine whether
That final step is important because patching restores the known-good baseline, but attack-surface reduction improves the future baseline. If a server never needed AJP, leaving the module loaded after patching merely preserves the next AJP advisory as future work. If AJP is required, network controls should make that dependency explicit.
In security operations, the best remediation closes the ticket and reduces the odds of reopening a similar one later. CVE-2026-34032 is tailor-made for that kind of cleanup.
MSRC is useful when Microsoft products are involved or when an organization’s workflow is built around Microsoft’s update taxonomy. NVD is useful for normalized metadata, weaknesses, CVSS vectors, and CPE mappings. Apache’s advisory is useful because it is upstream and tells you what the project itself says is affected and fixed. Distribution trackers are useful because they tell you when your actual package stream has been updated.
The mistake is expecting all of those sources to be interchangeable. A CVE record can tell you the affected upstream version but not whether your Linux distribution has backported the fix without changing the visible version string. A Microsoft portal can index a vulnerability but not patch an Apache deployment. A scanner can flag a binary but not always know whether the module is loaded.
When the MSRC page fails, it is annoying. When the organization has a redundant source model, it is not blocking. That is the difference between a mature vulnerability process and a portal-driven scramble.
A low confidentiality impact on a public-facing reverse proxy may matter more than a higher theoretical score on an isolated lab host. A vulnerable Apache build inside a regulated application path may carry compliance obligations regardless of exploit glamour. A vendor-bundled copy may be harder to patch and therefore more important to track early.
This is where the industry’s obsession with severity labels becomes counterproductive. “Low” can mean “routine maintenance.” It should not mean “never.” The right question is not whether CVE-2026-34032 deserves panic; it does not. The right question is whether your organization has a reliable path to bring Apache to 2.4.67 across every place it exists.
For many teams, the answer will be yes. For others, the CVE will expose an orphaned server, an abandoned application, or a vendor dependency nobody has budgeted time to update. Those discoveries are valuable even when the original flaw is modest.
Security maturity often looks boring from the outside. It is the team that patches low-severity infrastructure bugs in cadence, deletes unused modules, and documents exceptions before the critical advisory arrives. CVE-2026-34032 is a good opportunity to practice that discipline.
Source: MSRC Security Update Guide - Microsoft Security Response Center
mod_proxy_ajp, disclosed on May 4, 2026, affecting Apache HTTP Server versions through 2.4.66 and fixed in Apache HTTP Server 2.4.67. The bug is not a Microsoft vulnerability, despite surfacing through Microsoft’s Security Update Guide URL, and the broken MSRC page is almost more revealing than the flaw itself. For Windows admins, the practical answer is simple: if you run Apache with AJP proxying, patch; if you do not, verify that assumption rather than letting a low-severity CVE become inventory theater.
 A Small Apache Bug Exposes a Bigger Dependency Problem
A Small Apache Bug Exposes a Bigger Dependency Problem
The reported failure on Microsoft’s MSRC page — a dynamic JavaScript module refusing to load — is the kind of browser-side shrug that makes vulnerability management feel absurd. An admin goes looking for a CVE record, gets a TypeError, and is told to clear cookies, log out, or wait a few hours. That is not the end of the world, but it is a bad look for the system enterprises increasingly use as their first stop in a patch cycle.CVE-2026-34032 itself is not the kind of vulnerability that should cause emergency all-hands calls. Apache classifies it as low severity, and the public description points to an improper null-termination check leading to an out-of-bounds read in
ajp_msg_get_string, a function used by the AJP proxy module. NVD’s record associates it with CWE-125, out-of-bounds read, and CWE-170, improper null termination.But low severity is not the same thing as irrelevant. The affected range is broad — Apache HTTP Server through 2.4.66 — and the fix lands in 2.4.67. That matters because Apache remains deeply embedded in estates where Windows is only part of the story: reverse proxies in front of Java applications, load balancers terminating TLS, developer workstations, lab servers, appliances, bundled stacks, and third-party products that ship their own copy of httpd.
The headline lesson is not that Apache has another memory-safety blemish. The lesson is that modern Windows operations teams are often accountable for software supply chains they do not think of as “Windows,” and the tooling they use to track those chains is still more brittle than it should be.
The AJP Edge Case Is Narrow, but the Blast Radius Is Not Always Obvious
AJP, the Apache JServ Protocol, is old plumbing with a stubbornly long tail. It is most commonly encountered when Apache HTTP Server fronts a Java application server such as Tomcat, passing requests across a backend connector rather than speaking plain HTTP to the application tier. In a cleanly segmented design, AJP is internal, constrained, and boring.That is the optimistic version. In the real world, AJP has a history of being enabled because a deployment guide once said so, left reachable because a firewall rule was copied forward, or buried inside a vendor appliance where the admin sees only a management GUI. That does not make every AJP flaw a fire drill, but it does mean “we don’t use that” is not a sufficient control.
CVE-2026-34032 is about string parsing. The phrase “missing null-termination check” sounds dry because it is dry, but it points to one of the oldest classes of C-language failure: code expects a string to be terminated in a safe, conventional way, and an input path fails to enforce that expectation before memory is read. The result, in this case, is described as a heap buffer over-read.
An over-read is not the same thing as a heap overflow. It typically means software reads beyond the intended boundary rather than writing attacker-controlled data past it. That distinction is why the vulnerability is being treated as low severity rather than a neat remote-code-execution story.
Still, confidentiality bugs have a way of becoming operationally annoying even when they are not spectacular. Depending on path, state, and surrounding code, an out-of-bounds read may leak adjacent memory, crash a process, or simply behave unpredictably. The public record for CVE-2026-34032 does not justify breathless claims of mass compromise, but it does justify a quiet maintenance window and a search through configurations.
The Important Number Is 2.4.67
Apache’s guidance is uncomplicated: upgrade to Apache HTTP Server 2.4.67. CVE-2026-34032 affects versions through 2.4.66, and the upstream project records the fix as part of the May 4, 2026, 2.4.67 release train. That same release also addresses multiple other Apache HTTP Server issues, including additional low-severity bugs and at least one moderate issue.This is why treating CVEs one at a time can be a trap. If a scanner highlights only CVE-2026-34032, an organization might decide to defer because the score is modest. If the same host is vulnerable to a cluster of Apache issues fixed in the same release, the patch decision looks different.
Security teams have become fluent in CVSS arithmetic, but package updates rarely arrive as single-CVE events. They arrive as bundles of parser fixes, module-specific hardening, regression repairs, and behavior changes. Apache 2.4.67 is not “the CVE-2026-34032 patch” so much as the current upstream corrective release for a web server branch that many organizations continue to rely on.
That distinction matters for WindowsForum readers because Apache on Windows often lives outside Microsoft’s neat update channels. If Apache was installed via a vendor package, XAMPP-like stack, developer toolchain, reverse proxy product, or custom service wrapper, Windows Update is not coming to save it. Microsoft’s portal may surface the CVE, but it will not patch a third-party Apache binary you dropped into
C:\Apache24 three years ago.Microsoft’s Broken Page Is a Symptom, Not the Story
The MSRC error message in the user report is oddly specific: the page failed to fetch a dynamically imported module namedSugBreadcrumbUx.D7cXLvz5.js. That smells like a front-end deployment or caching issue rather than a missing vulnerability record. The browser is trying to assemble the Security Update Guide interface, one JavaScript chunk does not load, and the user gets troubleshooting boilerplate.There is a narrow reading and a broader reading. The narrow reading is that a website broke, and refreshing later may fix it. The broader reading is that vulnerability data has become too important to be trapped behind fragile single-page-app behavior.
For individual users, that fragility is irritating. For security operations teams, it is a workflow hazard. Patch Tuesday already involves juggling vendor advisories, CVE records, scanner plugins, package repositories, and exceptions. If one of the major portals becomes intermittently unusable because of front-end asset loading, the process becomes less about risk and more about page archaeology.
To Microsoft’s credit, the MSRC Security Update Guide has become a central clearinghouse for Windows and Microsoft ecosystem security information. But CVE-2026-34032 shows the awkward edge of that model: a third-party Apache vulnerability can appear in the same search-and-triage universe as Windows flaws, while the authoritative remediation still lives upstream with Apache and downstream with operating system distributors.
That is not a reason to ignore MSRC. It is a reason not to make it your only source of truth.
The Scanner Will Say “Remote,” but the Architecture Decides the Risk
NVD’s vector for CVE-2026-34032 indicates network attack vector, low complexity, no privileges required, no user interaction, unchanged scope, low confidentiality impact, and no integrity or availability impact. In plain English, the record describes something remotely reachable in principle, not something that necessarily matters equally on every host.The missing nuance is exposure. A vulnerable Apache build that does not load
mod_proxy_ajp is not the same as one that proxies AJP traffic to a backend application server. A host where AJP is reachable only from localhost is not the same as one where backend connector traffic is exposed across a flat internal network. A production reverse proxy terminating public traffic is not the same as a developer VM used twice a month.This is where many vulnerability programs still stumble. They ingest the CVE, map it to a package version, assign a deadline, and only later ask whether the vulnerable code path is active. That order is understandable at scale, but it produces poor prioritization when the flaw sits in an optional module.
The better approach is not to dismiss the CVE because it is low severity. The better approach is to enrich it. Is
mod_proxy_ajp loaded? Are there ProxyPass or ProxyPassMatch rules using ajp://? Is the backend connector reachable from untrusted networks? Is Apache serving internet-facing traffic, internal line-of-business applications, or both? Those answers determine whether this is a routine patch or a more urgent cleanup of legacy architecture.The uncomfortable truth is that many organizations cannot answer those questions quickly. They know they have Apache because a scanner says so. They do not know why it is there, who owns it, or what module set it is running. CVE-2026-34032 is modest, but it is a useful test of whether your asset inventory understands applications or merely recognizes version strings.
Low Severity Still Deserves a Maintenance Window
The security industry has overcorrected around critical vulnerabilities. After Log4Shell, ProxyShell, MOVEit, and a long list of name-brand emergencies, it became fashionable to say that only exploited, internet-facing, high-severity bugs deserve immediate attention. There is wisdom in that, but taken too far it becomes an excuse for letting known defects accumulate indefinitely.Low-severity memory bugs in infrastructure software are debt. One is manageable. Ten become a pattern. Fifty become the reason a routine upgrade turns into a brittle migration project because nobody has touched the stack in years.
Apache HTTP Server is particularly prone to this effect because it is stable, familiar, and often invisible when it works. It may sit in front of applications whose owners have changed twice. It may be pinned because a rewrite rule depends on old behavior. It may be bundled into a product where the vendor’s update cadence lags upstream.
That is why the right operational posture is boring but firm. If you are on Apache 2.4.66 or earlier, plan the move to 2.4.67 through your normal change process. If you cannot move because a vendor has not shipped an update, document the exposure and apply compensating controls around AJP. If the server does not need AJP, disable the module rather than merely accepting the version finding.
Patching low-severity infrastructure bugs is less about panic than hygiene. The organizations that handle these quietly are the same ones that move faster when a genuinely critical Apache issue arrives.
The Windows Angle Is Third-Party Software in a Microsoft World
Windows admins have long lived with a split-brain patching model. Microsoft updates arrive through Windows Update, WSUS, Configuration Manager, Intune, Autopatch, or whatever blend the organization has standardized on. Everything else arrives through vendor portals, package managers, scripts, appliances, golden images, container rebuilds, and tribal knowledge.Apache HTTP Server sits firmly in the “everything else” bucket on Windows. It may run as a Windows service, but it is not serviced like IIS. It may protect Microsoft-hosted workloads, but Microsoft does not own its release cadence. It may appear in MSRC search results, but the fix is not a cumulative update.
That mismatch matters because Windows-centric organizations sometimes underestimate the amount of non-Microsoft code in their server estate. A Java application behind Apache, a PHP application on a legacy intranet host, a monitoring tool with embedded httpd, or a developer-installed stack can all create exposure that does not look like a Windows vulnerability at first glance.
The same is true in hybrid environments. A vulnerability may be discovered upstream, packaged by Debian, Ubuntu, Red Hat, Alpine, or another distributor, mirrored into containers, consumed by a vendor, and finally detected by an enterprise scanner. Somewhere in that chain, a Windows team may be asked why a Microsoft portal page is broken for an Apache CVE.
That is the state of enterprise IT in 2026: the operating system boundary is no longer the operational boundary. Windows admins do not need to become Apache core developers, but they do need to know where Apache exists, how it is updated, and whether AJP is part of the design.
AJP’s Long Tail Keeps Creating Security Work
AJP is not inherently reckless. In the right network model, it is a specialized connector between trusted components. But specialized connectors have a way of becoming security liabilities when the original architecture fades from memory.The protocol’s history has already made admins wary. The 2020 “Ghostcat” vulnerability in Apache Tomcat’s AJP connector turned a once-obscure backend protocol into a board-level remediation item for some organizations. CVE-2026-34032 is not Ghostcat, and it should not be treated as though it is. But it benefits from the same lesson: backend protocols are only backend protocols if the network still treats them that way.
Apache’s
mod_proxy_ajp is often deployed because it solved a practical problem. It let Apache do what Apache does well — TLS termination, virtual hosting, request routing, authentication integration, logging, and policy enforcement — while a Java application server handled the application. That pattern is legitimate.The danger is inertia. Once deployed, AJP configurations may persist through application migrations, firewall redesigns, virtualization moves, and cloud lift-and-shift projects. A server that began life as a carefully segmented reverse proxy may end up with broader reachability simply because nobody revisited the connector assumptions.
CVE-2026-34032 gives teams a reason to revisit those assumptions without the pressure of an active mass-exploitation crisis. That is a gift. It is much easier to remove an unnecessary AJP path during a low-severity patch cycle than during a weekend incident bridge.
The Right Fix Is Patch First, Then Shrink the Attack Surface
There is always a temptation to solve module-specific vulnerabilities with configuration-only mitigations. Ifmod_proxy_ajp is the affected component, why not just disable it and call the job done? In some environments, that is exactly the correct immediate move.But disabling a module is not a substitute for keeping Apache current. The same 2.4.67 release addresses more than this one AJP parsing bug. A server that remains on an older branch because today’s highlighted CVE is avoidable by configuration may still carry other flaws in modules that are active.
The practical sequence is straightforward. First, identify Apache instances and version levels. Second, determine whether
mod_proxy_ajp is loaded and whether ajp:// proxying is configured. Third, patch to 2.4.67 or consume the relevant distributor/vendor update. Fourth, remove AJP where it is no longer required, and restrict it tightly where it remains.That final step is important because patching restores the known-good baseline, but attack-surface reduction improves the future baseline. If a server never needed AJP, leaving the module loaded after patching merely preserves the next AJP advisory as future work. If AJP is required, network controls should make that dependency explicit.
In security operations, the best remediation closes the ticket and reduces the odds of reopening a similar one later. CVE-2026-34032 is tailor-made for that kind of cleanup.
The MSRC Error Should Push Teams Toward Redundant Sources
The broken Microsoft page also offers a procedural lesson: vulnerability programs should not depend on a single web interface. MSRC, NVD, CVE.org, Apache’s own advisory page, Linux distribution trackers, scanner vendor writeups, and package repositories all answer slightly different questions. None of them is perfect alone.MSRC is useful when Microsoft products are involved or when an organization’s workflow is built around Microsoft’s update taxonomy. NVD is useful for normalized metadata, weaknesses, CVSS vectors, and CPE mappings. Apache’s advisory is useful because it is upstream and tells you what the project itself says is affected and fixed. Distribution trackers are useful because they tell you when your actual package stream has been updated.
The mistake is expecting all of those sources to be interchangeable. A CVE record can tell you the affected upstream version but not whether your Linux distribution has backported the fix without changing the visible version string. A Microsoft portal can index a vulnerability but not patch an Apache deployment. A scanner can flag a binary but not always know whether the module is loaded.
When the MSRC page fails, it is annoying. When the organization has a redundant source model, it is not blocking. That is the difference between a mature vulnerability process and a portal-driven scramble.
The CVSS Score Is Not a Business Decision
CVE-2026-34032 has been scored around the low-to-medium boundary depending on the source presentation, with the NVD vector emphasizing low confidentiality impact and no integrity or availability impact. That is useful information, but it is not the whole decision.A low confidentiality impact on a public-facing reverse proxy may matter more than a higher theoretical score on an isolated lab host. A vulnerable Apache build inside a regulated application path may carry compliance obligations regardless of exploit glamour. A vendor-bundled copy may be harder to patch and therefore more important to track early.
This is where the industry’s obsession with severity labels becomes counterproductive. “Low” can mean “routine maintenance.” It should not mean “never.” The right question is not whether CVE-2026-34032 deserves panic; it does not. The right question is whether your organization has a reliable path to bring Apache to 2.4.67 across every place it exists.
For many teams, the answer will be yes. For others, the CVE will expose an orphaned server, an abandoned application, or a vendor dependency nobody has budgeted time to update. Those discoveries are valuable even when the original flaw is modest.
Security maturity often looks boring from the outside. It is the team that patches low-severity infrastructure bugs in cadence, deletes unused modules, and documents exceptions before the critical advisory arrives. CVE-2026-34032 is a good opportunity to practice that discipline.
The Patch Note That Should Change the Runbook
The concrete operational response to CVE-2026-34032 should be measured, not theatrical. The bug is real, the fix is available upstream, and the affected range is broad enough to justify a deliberate search. The MSRC page problem should not slow that work because Apache’s own advisory and the public CVE ecosystem already provide the essentials.- Apache HTTP Server versions through 2.4.66 are affected by CVE-2026-34032, and Apache recommends upgrading to 2.4.67.
- The vulnerable area is
mod_proxy_ajp, so teams should verify whether the AJP proxy module is loaded and whetherajp://proxy rules exist. - The flaw is described as an improper null-termination and out-of-bounds read issue, not as a confirmed remote-code-execution vulnerability.
- Windows Update will not remediate standalone or bundled Apache installations on Windows, so owners must use upstream, distributor, or vendor-supplied updates.
- The broken MSRC page is a reminder to validate CVEs against multiple sources rather than depending on a single portal.
- If AJP is not required, removing or disabling it is a better long-term control than simply patching and leaving unnecessary code exposed.
Source: MSRC Security Update Guide - Microsoft Security Response Center