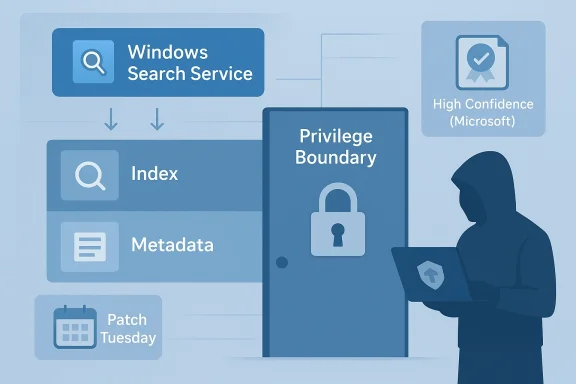
Microsoft’s CVE-2026-27909 entry for the Windows Search Service Elevation of Privilege Vulnerability is a reminder that not every serious Windows flaw arrives with a dramatic exploit narrative attached. The advisory’s confidence-oriented language matters because it is designed to tell defenders how certain Microsoft is that the vulnerability exists and how credible the known technical details are, even when the public record is sparse. In practice, that makes this the kind of issue security teams should treat as real, actionable, and worth prioritizing, not as a theoretical footnote. Microsoft’s broader 2026 guidance around elevation-of-privilege flaws has consistently framed these entries as meaningful local attack surfaces that can turn a foothold into system-level control, which is why the surrounding pattern is important even when individual CVEs remain thinly described oose components that users barely notice until it breaks, yet attackers love to study because it sits close to file indexing, metadata handling, and system integration. A privilege-escalation issue in that layer can be especially valuable because local search services often interact with other trusted Windows subsystems and user data in ways that enlarge the blast radius of a bug. That is why a CVE like CVE-2026-27909 deserves more attention than its sparse public description might suggest.
Microsoft’s confidence metric is intended to express two things at once: how certain the vendor is that a vulnerability exists, and how much technical detail is available to would-be attackers. That distinction matters because it helps defenders separate confirmed issues from tentative research leads. It also explains why the public wording around the advisory can be operationally useful even when Microsoft is not publishing a full exploit path or a deep root-cause analysis.
The Windows Search Service has historically been part of a wider class of Windows components that are easy to underestimate because they feel mundane. Yet mundane Windows services frequently become privilege-boundary chokepoints, especially when they touch indexing, stored content, background processing, or shared system state. When Microsoft assigns one of these services a public elevation-of-privilege advisory, the safest assumption is that the bug can be turned into practical attack value by an authenticated local actor.
This is also part of a larger pattern in Microsoft’s 2026 security messaging. Across multiple advisories, Microsoft has used sparse but confident entries to signal that defenders should patch first and analyze later. That philosophy reflects a reality of modern Windows defense: attackers do not need a full academic write-up to weaponize a local privilege-escalation flaw if the vulnerable surface is stable, common, and widely deployed.
The broader Windows secur rivilege bugs as among the most operationally important classes of Windows vulnerabilities. Unlike remote code execution flaws, which may be exploitable from afar, local privilege escalation issues often become the second stage of a compromise. Once an attacker lands a foothold through phishing, a malicious script, stolen credentials, or another bug, an EoP flaw can be the difference between limited access and full machine control.
Windows Search fits naturally into that landscape because it is deeply embedded in everyday Windows activity. Search indexing, content discovery, and metadata handling are all things that happen quietly in the background, but they can involve privileged code paths, kernel-assisted operations, or service-to-service communication that is hard to harden perfectly. That makes the service a plausible target for bugs that are subtle, local, and difficult to spot from the outside.
Microsoft’s Security Update Guide has become more transparent in recent years, but transparency does not always mean full technical disclosure. The company has increasingly used machine-readable vulnerability data and confidence-oriented guidance to help customers automate response and triage. That is a welcome shift for enterprise defenders because it improves prioritization, even if it leaves some public fields intentionally vague. Microsoft’s own security communications explicitly describe the confidence signal as a measure of certainty about the vulnerability and the credibility of the technical details, which helps explain the urgency around entries that may not yet have much public narrative attached .
At the same time, Microsoft has continued to release large Patch Tuesday batches thacal privilege-escalation issues across Windows subsystems. The April 2026 wave, for example, included numerous Windows security advisories across different components, reinforcing the point that attackers benefit from any overlooked local boundary they can chain into broader access. In that environment, Search Service should be viewed less as an isolated bug and more as part of a broader Windows attack-surface map.
The absence of rich technical detail is not a reason to dismiss the issue. If anything, the opposite is often true: when Microsoft assigns a CVE and uses confidence language, it is usually saying the problem is concrete enough to track, patch, and expect adversarial interest. That is especially true for service-class bugs, where defenders are often better served by patching quickly than by waiting for a perfect root-cause explanation.
For defenders, that distinction is useful because it helps answer a practical question: is this a speculative disclosure, or is it a real bug Microsoft is already prepared to stand behind? In the latter case, the correct response is to move the issue into normal patching and containment workflows rather than waiting for more proof. When confidence is high, the risk is not just that the bug exists, but that a determined attacker may already have enough context to begin working toward exploitation.
That matters because local privilege escalation is one of the most common ways attackers turn a limited compromise into durable control. Once code is running on a machine under a standard user account, the remaining obstacle is often an EoP flaw in a trusted Windows component. Search services, like other brokered system features, are attractive because they often perform privileged work on behalf of unprivileged users.
The likely enterprise implication is straightforward: even if the issue cannot be triggered remotely, it still matters in real-world intrusion chains. Phishing, malicious downloads, browser exploits, and post-exploitation toolsets all benefit from a second-stage escalation primitive. Windows Search Service, by virtue of being built into the platform, becomes part of the surface attackers can aim at after initial access.
The upside is obvious: customers get a signal that the issue is real without waiting for a full postmortem. The downside is that security teams must make decisions with less technical specificity than they would like. That creates a tension between transparency and operational safety, and it is one that Microsoft seems to manage by emphasizing confidence, impact, and patch guidance over deep exploit detail.
This model has become more prominent as Microsoft has expanded its vulnerability data channels, including machine-readable CSAF support and richer update-guide content. The goal is not just disclosure for disclosure’s sake, but faster remediation across a large and diverse customer base. In other words, the company is trying to scale security communications for an ecosystem where the audience includes home users, managed enterprises, and third-party tooling vendors.
Enterprises face a more complicated problem. Search-related flaws can matter across virtual desktops, managed endpoints, kiosks, shared workstations, and developer machines where users routinely run untrusted code or open untrusted content. An attacker who gets any initial access in that environment may find a local escalation bug far more valuable than a flashy remote exploit because it helps them evade standard user restrictions and security tooling.
Microsoft’s update cadence also increasingly reflects the reality that not all important fixes are equal, even when they share a Patch Tuesday. Some are urgent because they are already in active exploitation. Others are urgent because they close off a stable local escalation route that could be weaponized soon. CVE-2026-27909 appears to belong to that second category, where the lack of public exploit drama should not be mistaken for a lack of operational importance.
This is one reason modern patch management has become more analytic. Administrators can no longer rely on the headline alone. They have to weigh component criticality, lipnfidence signals all at once. That is tedious, but it is also more realistic than a blanket “critical only” mindset.
This matters because the ecosystem around Microsoft vulnerabilities is massive. Enterprises do not read every advisory directly. They often rely on dashboards, scanners, ticketing integrations, and security service providers to translate vendor language into action. A clear confidence signal can improve that translation, especially when the vulnerability description itself is brief.
Another concern is that organizations may not have a clean inventory of where the vulnerable service is deployed or how quickly it is updated. In Windows environments, patch compliance is often uneven across departments, device classes, and support tiers. A service-level EoP can remain quietly exploitable long after the headline has faded.
It will also be worth watching whether third-party researchers later publish technical analysis that fills in the public gaps. That would not make the original advisory less important; it would simply turn a credibla more fully understood attack model. For defenders, that is a reminder to patch early and study the details afterward.
CVE-2026-27909 is a classic modern Windows security story: the surface sounds ordinary, the public details are restrained, and the real danger lies in how a local bug can become a decisive escalation path after the first compromise. Microsoft’s confidence-driven framing makes the advisory more useful, not less, because it tells defenders the company believes the flaw is credible enough to act on now. In a patching environment as crowded as April 2026, that is exactly the kind of signal security teams should learn to trust.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Microsoft’s confidence metric is intended to express two things at once: how certain the vendor is that a vulnerability exists, and how much technical detail is available to would-be attackers. That distinction matters because it helps defenders separate confirmed issues from tentative research leads. It also explains why the public wording around the advisory can be operationally useful even when Microsoft is not publishing a full exploit path or a deep root-cause analysis.
The Windows Search Service has historically been part of a wider class of Windows components that are easy to underestimate because they feel mundane. Yet mundane Windows services frequently become privilege-boundary chokepoints, especially when they touch indexing, stored content, background processing, or shared system state. When Microsoft assigns one of these services a public elevation-of-privilege advisory, the safest assumption is that the bug can be turned into practical attack value by an authenticated local actor.
This is also part of a larger pattern in Microsoft’s 2026 security messaging. Across multiple advisories, Microsoft has used sparse but confident entries to signal that defenders should patch first and analyze later. That philosophy reflects a reality of modern Windows defense: attackers do not need a full academic write-up to weaponize a local privilege-escalation flaw if the vulnerable surface is stable, common, and widely deployed.
 Background
Background
The broader Windows secur rivilege bugs as among the most operationally important classes of Windows vulnerabilities. Unlike remote code execution flaws, which may be exploitable from afar, local privilege escalation issues often become the second stage of a compromise. Once an attacker lands a foothold through phishing, a malicious script, stolen credentials, or another bug, an EoP flaw can be the difference between limited access and full machine control.Windows Search fits naturally into that landscape because it is deeply embedded in everyday Windows activity. Search indexing, content discovery, and metadata handling are all things that happen quietly in the background, but they can involve privileged code paths, kernel-assisted operations, or service-to-service communication that is hard to harden perfectly. That makes the service a plausible target for bugs that are subtle, local, and difficult to spot from the outside.
Microsoft’s Security Update Guide has become more transparent in recent years, but transparency does not always mean full technical disclosure. The company has increasingly used machine-readable vulnerability data and confidence-oriented guidance to help customers automate response and triage. That is a welcome shift for enterprise defenders because it improves prioritization, even if it leaves some public fields intentionally vague. Microsoft’s own security communications explicitly describe the confidence signal as a measure of certainty about the vulnerability and the credibility of the technical details, which helps explain the urgency around entries that may not yet have much public narrative attached .
At the same time, Microsoft has continued to release large Patch Tuesday batches thacal privilege-escalation issues across Windows subsystems. The April 2026 wave, for example, included numerous Windows security advisories across different components, reinforcing the point that attackers benefit from any overlooked local boundary they can chain into broader access. In that environment, Search Service should be viewed less as an isolated bug and more as part of a broader Windows attack-surface map.
The absence of rich technical detail is not a reason to dismiss the issue. If anything, the opposite is often true: when Microsoft assigns a CVE and uses confidence language, it is usually saying the problem is concrete enough to track, patch, and expect adversarial interest. That is especially true for service-class bugs, where defenders are often better served by patching quickly than by waiting for a perfect root-cause explanation.
What the Confidence Metric Really Means
Microsoft’s confidence metric is easy to misunderstand if yousot simply a measure of how dangerous a vulnerability is; it is a signal about the vendor’s confidence that the flaw exists and about the credibility of the known technical details. That makes it a hybrid of research certainty and attack readiness.For defenders, that distinction is useful because it helps answer a practical question: is this a speculative disclosure, or is it a real bug Microsoft is already prepared to stand behind? In the latter case, the correct response is to move the issue into normal patching and containment workflows rather than waiting for more proof. When confidence is high, the risk is not just that the bug exists, but that a determined attacker may already have enough context to begin working toward exploitation.
Why This Matters Operationally
Security teams often triage issues using CVSS alone, but CVSS does not tell the whole story. A medium-scoring issue with high-confidence vendor data may deserve faster action than a higher-scoring issue with limited technical certainty. That is why Microsoft’s metadata should be read as a decision-making aid rather than as a footnote.- It helps separate confirmed flaws from uncertain leads.
- It informs how much attacker knowledge may already be available.
- It can justify earlier patch deployment, even without exploit proof.
- It reduces the temptation to over-prioritize only the loudest advisories.
- It gives enterprise teams a way to sort issues by credibility as well as impact.
Why Windows Search Is a Sensitive Target
Windows Search is not glamorous, but it sits in a high-value part of the operating system. Search infrastructure interacts with files, indexing databases, shell integration, and user-facing discovery paths, which means mistakes can ripple into privileges that ordinary users never see. A flaw here may not need to be remotely reachable to matter; a local attacker with any foothold could still use it to cross a boundary that should have stayed closed.That matters because local privilege escalation is one of the most common ways attackers turn a limited compromise into durable control. Once code is running on a machine under a standard user account, the remaining obstacle is often an EoP flaw in a trusted Windows component. Search services, like other brokered system features, are attractive because they often perform privileged work on behalf of unprivileged users.
The likely enterprise implication is straightforward: even if the issue cannot be triggered remotely, it still matters in real-world intrusion chains. Phishing, malicious downloads, browser exploits, and post-exploitation toolsets all benefit from a second-stage escalation primitive. Windows Search Service, by virtue of being built into the platform, becomes part of the surface attackers can aim at after initial access.
The Local Foothold Problem
A lot of defenders still subconsciously rank local vulnerabilities below remote ones. That instinct is understandable but incomplete. Modern intrusions frequently begin with a low-privilege foothold, and local escalation is what converts that foothold into a serious incident.- Local EoP bugs are often the real post-compromise payoff.
- Core services offer broad deployment and repeatable exploit conditions.
- Service-based vulnerabilities can persist across many Windows editions.
- Attackers value them because they chain well with phishing and malware.
- Enterprise environments amplify their impact through lateral movement.
The Strategic Value of Sparse Disclosures
Microsoft’s sparse advisories may feel frustrating, but they also reflect a defensive philosophy. The company increasingly prefers to disclose enough to let customers patch and prioritize without giving attackers a clean exploit blueprint. That approach is especially visible in entries where the confidence metric does most of the informational work.The upside is obvious: customers get a signal that the issue is real without waiting for a full postmortem. The downside is that security teams must make decisions with less technical specificity than they would like. That creates a tension between transparency and operational safety, and it is one that Microsoft seems to manage by emphasizing confidence, impact, and patch guidance over deep exploit detail.
This model has become more prominent as Microsoft has expanded its vulnerability data channels, including machine-readable CSAF support and richer update-guide content. The goal is not just disclosure for disclosure’s sake, but faster remediation across a large and diverse customer base. In other words, the company is trying to scale security communications for an ecosystem where the audience includes home users, managed enterprises, and third-party tooling vendors.
Why Defenders Should Not Overreact to the Missing Details
A thin advisory is not a weak advisory. It may simply mean Microsoft has chosen not to nics that could help attackers. If the vendor has attached confidence language and a public CVE, the operational message is still clear: trust the advisory, patch the component, and validate exposure in your environment.- Sparse detail does not equal low risk.
- Public CVE assignment means the issue is tracked and real enough to matter.
- Confidence language suggests Microsoft has enough evidence to act.
- Attackers often need less detail than defenders imagine.
- The safest response is disciplined remediation, not speculation.
Enterprise Exposure Versus Consumer Exposure
For consumer Windows systems, a Search Service EoP is mainly a question of whether the machine receives timely patching. Home users are usually protected or exposed in broad strokes: if Windows Update is current, they are better off; if it is not, they may be sitting on a useful privilege-escalation primitive without knowing it. Consumers also face a lower likelihood of targeted exploitation, but they remain vulnerable to opportunistic malware chains.Enterprises face a more complicated problem. Search-related flaws can matter across virtual desktops, managed endpoints, kiosks, shared workstations, and developer machines where users routinely run untrusted code or open untrusted content. An attacker who gets any initial access in that environment may find a local escalation bug far more valuable than a flashy remote exploit because it helps them evade standard user restrictions and security tooling.
Where Enterprise Risk Becomes Amplified
The enterprise threat is not just about the vulnerability itself. It is about how quickly a standard-user compromise can become a domain-level incident when the attacker can escape the first security boundary.- Shared endpoints increase the chance of an initial foothold.
- Developer and admin workstations can be especially attractive targets.
- Endpoint detection may miss low-noise privilege escalation.
- Patch lag creates a long tail of exposure across fleets.
- Search-related services often run in default configurations, widening uniform risk.
How This Fits the April 2026 Patch Story
April 2026 has already illustrated how large and varied Microsoft’s update surface has become. The month’s security changes include a wide mix of Windows components, service-level fixes, and new defensive controls. That breadth matters because it shows how many avenues an attacker can exploit once they are inside a Windows environment.Microsoft’s update cadence also increasingly reflects the reality that not all important fixes are equal, even when they share a Patch Tuesday. Some are urgent because they are already in active exploitation. Others are urgent because they close off a stable local escalation route that could be weaponized soon. CVE-2026-27909 appears to belong to that second category, where the lack of public exploit drama should not be mistaken for a lack of operational importance.
This is one reason modern patch management has become more analytic. Administrators can no longer rely on the headline alone. They have to weigh component criticality, lipnfidence signals all at once. That is tedious, but it is also more realistic than a blanket “critical only” mindset.
The Broader Trend
Microsoft’s approach suggests a future where vulnerability metadata matters as much as raw severity.- Confidence signals are becoming part of triage decisions.
- Core Windows services are being disclosed with varying degrees of detail.
- Local EoP issues remain high-value post-compromise tools.
- Enterprise patching needs to account for chaining, not just CVSS.
- Security teams benefit from treating metadata as actionable intelligence.
Microsoft’s Security Messaging and the Market Signal
Microsoft’s vulnerability disclosures do more than inform customers; they shape expectations across the security market. When the company publicly labels a flaw and attaches a confidence metric, it tells third-party vendors, researchers, and defenders that the issue belongs in operational planning. That can influence how vulnerability management platforms score the issue, how managed service providers escalate it, and how threat intel teams frame it for customers.This matters because the ecosystem around Microsoft vulnerabilities is massive. Enterprises do not read every advisory directly. They often rely on dashboards, scanners, ticketing integrations, and security service providers to translate vendor language into action. A clear confidence signal can improve that translation, especially when the vulnerability description itself is brief.
Why Rivals and Integrators Care
Microsoft’s approach also creates pressure on adjacent vendors. Security platforms that ingest Microsoft advisories may need to treat confidence as a first-class field rather than as a minor note. That can alter patch-ranking logic, compliance reporting, and automated response workflows.- Vulnerability management tools can better rank what to fix first.
- MSSPs can justify faster escalation to clients.
- Threat intel teams can calibrate risk more accurately.
- Asset owners can avoid overfocusing on sensational but lower-confidence bugs.
- Security budgets can be tied more closely to real exposure.
Strengths and Opportunities
Microsoft’s handling of issues like CVE-2026-27909 has several strengths, especially for organizations that know how to use the advisory data properly. The main opportunity is not merely to patch faster, but to use the signal to sharpen operational discipline across the whole Windows estate.- Better prioritization through the confidence metric instead of relying only on CVSS.
- Earlier remediation for local escalation paths that are often underestimated.
- Improved tooling integration as vulnerability platforms ingest richer Microsoft data.
- Reduced ambiguity when advisories are sparse but still actionable.
- Stronger enterprise playbooks for endpoint, server, and workstation patching.
- Better analyst focus on real exploitation potential rather than headline noise.
- More scalable response for large fleets with many overlapping advisories.
Risks and Concerns
The central risk with advisories like CVE-2026-27909 is that sparse detail can create a false sense of safety. If defenders do not see a clear exploit story, they may down-rank the issue, even though local privilege escalation is often exactly what attackers need after initial compromise. That gap between perceived and practical urgency is where breaches are born.Another concern is that organizations may not have a clean inventory of where the vulnerable service is deployed or how quickly it is updated. In Windows environments, patch compliance is often uneven across departments, device classes, and support tiers. A service-level EoP can remain quietly exploitable long after the headline has faded.
- Patch lag can leave exposed machines vulnerable for weeks or months.
- False confidence can lead teams to treat local bugs as low priority.
- Tooling gaps may prevent accurate exposure mapping across the estate.
- Attack chaining can make a “local-only” flaw highly valuable to intruders.
- Shared devices can amplify practical risk in enterprise settings.
- Limited disclosure may slow some teams that prefer detailed root-cause analysis.
- Alert fatigue can cause administrators to miss the significance of the advisory.
Looking Ahead
The next thing to watch is how Microsoft continues to annotate vulnerability records with confidence and related metadata. If that trend continues, defenders will have more useful signals for triage, but only if they adapt their processes to use them. CVE-2026-27909 may end up being remembered less for a dramatic exploit than for what it says about the future of Windows security communication.It will also be worth watching whether third-party researchers later publish technical analysis that fills in the public gaps. That would not make the original advisory less important; it would simply turn a credibla more fully understood attack model. For defenders, that is a reminder to patch early and study the details afterward.
Practical watch list
- The next Microsoft update guide refresh for any added technical detail.
- Whether the advisory’s confidence signal changes over time.
- Any third-party reverse engineering of the Search Service flaw.
- Evidence of active exploitation or chaining with other Windows bugs.
- Enterprise patch compliance timelines for Windows endpoints and servers.
CVE-2026-27909 is a classic modern Windows security story: the surface sounds ordinary, the public details are restrained, and the real danger lies in how a local bug can become a decisive escalation path after the first compromise. Microsoft’s confidence-driven framing makes the advisory more useful, not less, because it tells defenders the company believes the flaw is credible enough to act on now. In a patching environment as crowded as April 2026, that is exactly the kind of signal security teams should learn to trust.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: