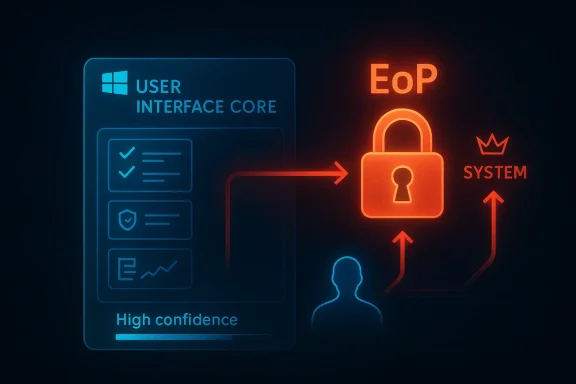
User Interface Core vulnerabilities occupy a strange place in Windows security: they are often invisible to most users, but highly consequential for defenders because they can turn a minor local foothold into a full system compromise. CVE-2026-27911, labeled by Microsoft as a Windows User Interface Core Elevation of Privilege Vulnerability, sits squarely in that category. The disclosure appears in Microsoft’s update guidance as a confidence-focused signal about the certainty and credibility of the flaw, which makes it especially important for patch prioritization, even when the public technical detail is thin.
Microsoft’s naming convention matters here. A title like Windows User Interface Core Elevation of Privilege Vulnerability usually points to a bug in the privileged plumbing that underpins parts of the Windows shell and UI stack, not a simple app crash. In practice, that means the bug is likely to matter most after an attacker has already gained a foothold on a machine, because local privilege escalation is often the step that turns malware from annoying to catastrophic.
The published description attached to CVE-2026-27911 emphasizes confidence in the existence of the vulnerability and the credibility of the technical details. That framing is important because not every CVE emerges from the same level of certainty. Some are fully confirmed by Microsoft or a researcher, while others begin as strong indicators that later solidify into definitive technical findings.
Microsoft has used similar UI-related labels before, including older entries such as Tablet Windows User Interface Application Core Elevation of Privilege Vulnerability and other Windows UI component issues. That historical pattern suggests the company continues to treat the UI stack as security-critical infrastructure, not just a cosmetic layer. When UI code runs with elevated privileges or interacts with sensitive kernel or session boundaries, flaws can have outsized impact.
In the current Windows ecosystem, this kind of issue is more than an endpoint curiosity. Enterprise environments are increasingly flattened by remote work, virtualization, and layered identity controls, but local escalation bugs still matter because they are the bridge from phishing, browser exploitation, or insider access to domain-wide damage. That is why even “important” EoP flaws frequently trigger broad operational attention.
Microsoft’s security documentation has repeatedly described EoP bugs in terms of what an attacker can do after successful exploitation: install programs, view or change data, or create new accounts with full rights. That pattern shows up across many Windows advisories and remains a useful shorthand for the practical consequence of privilege escalation. The bug may be local, but the outcome is often total machine control.
A key theme in Microsoft’s disclosure language is that exploitability is not only about what can be done, but about how much is known. The confidence metric attached to CVE-2026-27911 reflects the vendor’s assessment of certainty, not just severity. In other words, Microsoft is signaling that the issue is not speculative noise; it is considered real enough to warrant serious attention.
This is part of a broader evolution in how security advisories are consumed. Years ago, many users focused almost exclusively on whether a flaw was “Critical” or “Important.” Today, defenders also weigh the maturity of the technical detail, the likelihood of weaponization, and the reliability of the source. That is especially true for local EoP bugs, where exploit chains often depend on chaining another vulnerability first.
Historically, Windows UI and kernel-adjacent issues have been fertile ground for post-compromise persistence and sandbox escape. A UI subsystem bug can be especially valuable because attackers often encounter those components in broad, real-world attack paths. Browsers, document viewers, and messaging apps can all become launch points, and a privileged UI flaw can serve as the final rung in the ladder.
That makes the metric more useful than it might first appear. Security teams often need to decide what to patch first, and a high-confidence bug in a core Windows component is generally more actionable than a vague report with little corroboration. The confidence signal tells you that the issue should be treated as real operational risk, not just an abstract advisory.
There is also a practical reason this matters to enterprises. Patch queues are always finite, and every month brings a stack of competing issues. A credible EoP in Windows User Interface Core is the kind of item that can move up the list because its payoff to attackers is high even if the initial exploit path is local.
In older Microsoft advisories, the company often separated public disclosure, exploitability, and mitigation guidance into distinct sections. The broader lesson remains the same: exploit certainty increases operational urgency, and urgency is often the difference between a routine patch and an emergency rollout.
A flaw in UI Core can be attractive because many applications interact with it indirectly. A browser or desktop app may not be the vulnerable surface itself, but it can help deliver the conditions needed for exploitation. That layered relationship is one reason Windows UI bugs continue to show up in serious security bulletins.
That is especially dangerous in managed enterprise environments where standard users are common but administrative workflows still exist. If an attacker can land a low-privilege execution foothold and then chain to elevated privileges, the gap between detection and full compromise shrinks dramatically. That is the part defenders cannot afford to ignore.
The history of Windows security shows that seemingly mundane subsystems can become high-value escalation paths. That is why Microsoft’s naming scheme, while terse, carries substantial meaning. The label alone tells defenders the bug belongs to a category that has repeatedly produced serious post-compromise damage.
The practical risk is highest in environments with heavy use of remote access, shared systems, or automation accounts. Attackers often exploit one weakness to reach a foothold, then use a second flaw to obtain SYSTEM or similarly elevated privileges. Once that happens, defensive controls such as application whitelisting, endpoint telemetry, and some user-mode protections become far less effective.
Enterprises should also think beyond the workstation. A privileged local compromise can lead to cached credentials, access tokens, browser sessions, or signed-in service contexts that ripple into cloud identity platforms. In a hybrid environment, the local desktop is often just the entrance to something much larger.
For IT administrators, this means patching should be paired with validation. It is not enough to deploy the update; teams should confirm fleet coverage, watch for failed installations, and ensure vulnerable builds are not lingering in remote offices or disconnected laptops. Patch success is only real if the vulnerable version actually disappears.
Consumers often think of Windows patches as feature updates or stability fixes. This is one of the clearest reminders that security updates are part of basic hygiene. If a standard user-level compromise can be promoted to elevated access, then malware can more easily disable protections, install persistence, and hide from the user.
The consumer risk is amplified by the way people use Windows today. Many systems are always connected, always signed into cloud services, and synchronized across browsers, email, and productivity apps. That means a privilege escalation on the desktop can quickly spill into passwords, authentication prompts, and stored session data.
A second scenario involves fake software installers or game cheats. These are common delivery mechanisms for malware that tries to survive reboots or evade simple removal. If an attacker can move from a standard account to higher privilege, the cleanup burden rises sharply.
Consumers should treat patching as immediate maintenance rather than optional housekeeping. They should also keep browser, document, and security software current, because privilege escalation bugs are rarely the only weakness in the chain. One clean patch does not erase the value of layered protection.
There is also a broader market implication. Security vendors, managed service providers, and enterprise patch-management teams now operate in a climate where monthly Windows updates can contain multiple high-value items. That means defenders need to evaluate not just whether a flaw is serious, but how it interacts with the rest of the month’s patch set and with real-world exposure.
Microsoft’s naming also suggests that User Interface Core remains a live security surface in Windows 11-era builds. That is not surprising. Modern Windows has accumulated layers of backward compatibility, accessibility support, session architecture, and GUI integration that make the UI stack both essential and difficult to simplify.
That is why defenders should avoid treating the label as generic. A User Interface Core issue is not the same as a bug in a standalone desktop app. It is closer to a platform trust issue, and platform trust issues are the ones that tend to echo across products, versions, and deployment models.
Logging is especially important. When privilege escalation is involved, attackers often try to alter telemetry, disable protections, or clean up artifacts quickly. If security monitoring is weak or centralized logging is incomplete, post-exploitation investigation becomes much harder.
Memory and system integrity tools can also help, but only if they are already deployed and healthy before an incident starts. If a local EoP bug is chained with tampering or defense evasion, delayed deployment may be too late to help. That is why preparation matters more than emergency improvisation.
A disciplined response plan should also include rapid validation of patch state and a communication path for business owners. Some teams will need to prioritize high-value endpoints first, especially administrator workstations and systems used to access sensitive credentials. In a real incident, those are the machines that can do the most damage the fastest.
That matters because not all CVEs are equal in public maturity. Some arrive with detailed exploitation narratives, while others arrive with little more than a name and a risk category. The latter can still be dangerous if the underlying component is sensitive and the vendor has enough certainty to publish the issue.
For practitioners, the lesson is to focus on impact class, affected component, and confidence signal. If the vulnerability is a confirmed EoP in a core Windows subsystem, then the absence of exploit details should not be mistaken for low urgency. Unknown mechanics are still mechanics.
This is also where historical experience matters. Windows EoP bugs have repeatedly been chained into larger attacks, even when the initial advisory was not dramatic. The real-world risk lies in how the bug can be used, not just in how much technical prose accompanies the CVE page.
The opportunity for defenders is to use this disclosure as a reminder to harden the whole escalation path, not just the one CVE. That means tighter patch discipline, better logging, and more restraint around local admin rights. In other words, the vulnerability is also a chance to reduce the blast radius of any future flaw.
Another concern is detection lag. If the public technical details remain sparse, defenders may not have highly specific signatures to lean on. That can slow monitoring, especially in smaller environments that do not have deep behavioral analytics. The result is that the bug may be patched before defenders fully understand how it was abused.
The most useful response is disciplined, not theatrical. Patch quickly, verify coverage, watch for suspicious privilege changes, and reduce the number of places where a low-privilege compromise can matter. That approach will pay off whether CVE-2026-27911 is ever widely exploited or not.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
Microsoft’s naming convention matters here. A title like Windows User Interface Core Elevation of Privilege Vulnerability usually points to a bug in the privileged plumbing that underpins parts of the Windows shell and UI stack, not a simple app crash. In practice, that means the bug is likely to matter most after an attacker has already gained a foothold on a machine, because local privilege escalation is often the step that turns malware from annoying to catastrophic.The published description attached to CVE-2026-27911 emphasizes confidence in the existence of the vulnerability and the credibility of the technical details. That framing is important because not every CVE emerges from the same level of certainty. Some are fully confirmed by Microsoft or a researcher, while others begin as strong indicators that later solidify into definitive technical findings.
Microsoft has used similar UI-related labels before, including older entries such as Tablet Windows User Interface Application Core Elevation of Privilege Vulnerability and other Windows UI component issues. That historical pattern suggests the company continues to treat the UI stack as security-critical infrastructure, not just a cosmetic layer. When UI code runs with elevated privileges or interacts with sensitive kernel or session boundaries, flaws can have outsized impact.
In the current Windows ecosystem, this kind of issue is more than an endpoint curiosity. Enterprise environments are increasingly flattened by remote work, virtualization, and layered identity controls, but local escalation bugs still matter because they are the bridge from phishing, browser exploitation, or insider access to domain-wide damage. That is why even “important” EoP flaws frequently trigger broad operational attention.
Background
Windows has a long history of elevation-of-privilege vulnerabilities in components that are not obviously dangerous to end users. The reason is structural: the operating system delegates many privileged decisions to subsystems that must balance usability, compatibility, and hard security boundaries. The Windows UI stack is one of those places where complexity and trust interact in ways attackers love.Microsoft’s security documentation has repeatedly described EoP bugs in terms of what an attacker can do after successful exploitation: install programs, view or change data, or create new accounts with full rights. That pattern shows up across many Windows advisories and remains a useful shorthand for the practical consequence of privilege escalation. The bug may be local, but the outcome is often total machine control.
A key theme in Microsoft’s disclosure language is that exploitability is not only about what can be done, but about how much is known. The confidence metric attached to CVE-2026-27911 reflects the vendor’s assessment of certainty, not just severity. In other words, Microsoft is signaling that the issue is not speculative noise; it is considered real enough to warrant serious attention.
This is part of a broader evolution in how security advisories are consumed. Years ago, many users focused almost exclusively on whether a flaw was “Critical” or “Important.” Today, defenders also weigh the maturity of the technical detail, the likelihood of weaponization, and the reliability of the source. That is especially true for local EoP bugs, where exploit chains often depend on chaining another vulnerability first.
Historically, Windows UI and kernel-adjacent issues have been fertile ground for post-compromise persistence and sandbox escape. A UI subsystem bug can be especially valuable because attackers often encounter those components in broad, real-world attack paths. Browsers, document viewers, and messaging apps can all become launch points, and a privileged UI flaw can serve as the final rung in the ladder.
What the Confidence Metric Really Means
The user-facing description attached to CVE-2026-27911 is not the same thing as exploit proof. It is a signal about certainty, and that distinction matters. Microsoft is telling defenders that the vulnerability is credible, but the public record may still be thin on root cause, exploitation method, or proof-of-concept code.That makes the metric more useful than it might first appear. Security teams often need to decide what to patch first, and a high-confidence bug in a core Windows component is generally more actionable than a vague report with little corroboration. The confidence signal tells you that the issue should be treated as real operational risk, not just an abstract advisory.
Why certainty changes urgency
The more certain a vulnerability is, the more likely it is that attackers can reproduce it or that someone close to the issue already has a working exploit. That does not guarantee active exploitation, but it changes the risk calculus. For blue teams, it means patching, monitoring, and containment should be prioritized with greater urgency.There is also a practical reason this matters to enterprises. Patch queues are always finite, and every month brings a stack of competing issues. A credible EoP in Windows User Interface Core is the kind of item that can move up the list because its payoff to attackers is high even if the initial exploit path is local.
In older Microsoft advisories, the company often separated public disclosure, exploitability, and mitigation guidance into distinct sections. The broader lesson remains the same: exploit certainty increases operational urgency, and urgency is often the difference between a routine patch and an emergency rollout.
- Confidence affects how quickly defenders should move.
- EoP bugs are especially valuable after initial access.
- Core Windows components tend to justify broad patching.
- Thin public detail does not mean low risk.
- Attackers often care more about local escalation than flashy remote code execution.
Why Windows User Interface Core Matters
At first glance, “User Interface Core” sounds like a cosmetic subsystem. In reality, Windows UI code often sits close to the boundary between user sessions, privileged services, and kernel-facing components. That positioning makes it a powerful target for privilege escalation if trust is mishandled anywhere in the chain.A flaw in UI Core can be attractive because many applications interact with it indirectly. A browser or desktop app may not be the vulnerable surface itself, but it can help deliver the conditions needed for exploitation. That layered relationship is one reason Windows UI bugs continue to show up in serious security bulletins.
The attacker's perspective
From an attacker’s standpoint, a local EoP vulnerability is often the missing piece after a phishing success or endpoint compromise. Once code runs under a standard user account, the attacker wants to cross into elevated context as fast as possible. UI and session components are useful because they may expose trusted objects, messages, handles, or state transitions that can be manipulated.That is especially dangerous in managed enterprise environments where standard users are common but administrative workflows still exist. If an attacker can land a low-privilege execution foothold and then chain to elevated privileges, the gap between detection and full compromise shrinks dramatically. That is the part defenders cannot afford to ignore.
The history of Windows security shows that seemingly mundane subsystems can become high-value escalation paths. That is why Microsoft’s naming scheme, while terse, carries substantial meaning. The label alone tells defenders the bug belongs to a category that has repeatedly produced serious post-compromise damage.
- UI Core can sit near privileged Windows boundaries.
- Indirect exposure broadens the attack surface.
- Local EoP is a common second-stage objective.
- Standard-user environments do not make these bugs harmless.
- Session and handle handling often matter more than the visible interface.
Enterprise Impact
Enterprises should read CVE-2026-27911 as a patch-priority item, not merely a headline. Local elevation vulnerabilities are disproportionately important in managed fleets because they can turn one compromised workstation into a stepping stone for lateral movement, credential theft, or persistence. In modern incident response, the first foothold is rarely the final compromise.The practical risk is highest in environments with heavy use of remote access, shared systems, or automation accounts. Attackers often exploit one weakness to reach a foothold, then use a second flaw to obtain SYSTEM or similarly elevated privileges. Once that happens, defensive controls such as application whitelisting, endpoint telemetry, and some user-mode protections become far less effective.
Endpoint security implications
Endpoint detection and response tools can still help, but their job becomes harder when privilege escalation is used to disable logging, tamper with security services, or harvest secrets. If the vulnerability affects a core UI subsystem, exploit activity may also blend into normal desktop behavior. That makes behavioral detection important, but not always sufficient.Enterprises should also think beyond the workstation. A privileged local compromise can lead to cached credentials, access tokens, browser sessions, or signed-in service contexts that ripple into cloud identity platforms. In a hybrid environment, the local desktop is often just the entrance to something much larger.
For IT administrators, this means patching should be paired with validation. It is not enough to deploy the update; teams should confirm fleet coverage, watch for failed installations, and ensure vulnerable builds are not lingering in remote offices or disconnected laptops. Patch success is only real if the vulnerable version actually disappears.
Practical enterprise priorities
- Confirm whether affected builds are present in the fleet.
- Prioritize systems exposed to untrusted user activity.
- Monitor for unusual privilege escalation behavior.
- Validate patch installation across all managed endpoints.
- Review admin-account use on workstations.
- Reassess segmentation between user and privileged sessions.
Consumer Impact
For home users, the threat model is different but still serious. A local elevation flaw is often not something an average person can trigger alone, but it becomes highly relevant after a malicious download, browser exploit, fake installer, or bundled malware has already landed. In other words, the vulnerability may not be the first problem a consumer encounters, but it can be the one that turns a nuisance into a full machine takeover.Consumers often think of Windows patches as feature updates or stability fixes. This is one of the clearest reminders that security updates are part of basic hygiene. If a standard user-level compromise can be promoted to elevated access, then malware can more easily disable protections, install persistence, and hide from the user.
The consumer risk is amplified by the way people use Windows today. Many systems are always connected, always signed into cloud services, and synchronized across browsers, email, and productivity apps. That means a privilege escalation on the desktop can quickly spill into passwords, authentication prompts, and stored session data.
Common consumer scenarios
A user opens a malicious attachment and the initial payload runs under their account. If CVE-2026-27911 is chained into that attack path, the payload may be able to cross into elevated execution and entrench itself. That is why local vulnerabilities can have global consequences for the victim.A second scenario involves fake software installers or game cheats. These are common delivery mechanisms for malware that tries to survive reboots or evade simple removal. If an attacker can move from a standard account to higher privilege, the cleanup burden rises sharply.
Consumers should treat patching as immediate maintenance rather than optional housekeeping. They should also keep browser, document, and security software current, because privilege escalation bugs are rarely the only weakness in the chain. One clean patch does not erase the value of layered protection.
- Install Windows security updates promptly.
- Avoid running untrusted installers or cracks.
- Keep browser and email clients updated.
- Use standard accounts for daily work.
- Back up important files regularly.
- Treat suspicious attachments as hostile until proven otherwise.
How This Fits the Current Patch Landscape
Microsoft has been issuing a steady stream of Windows security updates that combine quality fixes with exploit-focused remediation. In that context, CVE-2026-27911 fits a familiar pattern: a component-level flaw with broad potential impact, even if the public description is deliberately sparse. That sparse disclosure is often normal for bugs where revealing details too early could help attackers.There is also a broader market implication. Security vendors, managed service providers, and enterprise patch-management teams now operate in a climate where monthly Windows updates can contain multiple high-value items. That means defenders need to evaluate not just whether a flaw is serious, but how it interacts with the rest of the month’s patch set and with real-world exposure.
Microsoft’s naming also suggests that User Interface Core remains a live security surface in Windows 11-era builds. That is not surprising. Modern Windows has accumulated layers of backward compatibility, accessibility support, session architecture, and GUI integration that make the UI stack both essential and difficult to simplify.
Historical comparison
Older Windows advisories often focused on kernel, driver, and COM-related privilege escalation. More recent cycles show continued attention to user-session and UI-adjacent components. The shift is less about one area replacing another and more about the attack surface simply moving with the platform as it evolves.That is why defenders should avoid treating the label as generic. A User Interface Core issue is not the same as a bug in a standalone desktop app. It is closer to a platform trust issue, and platform trust issues are the ones that tend to echo across products, versions, and deployment models.
- Monthly patch load remains operationally heavy.
- Sparse detail often reflects intentional disclosure discipline.
- UI Core is part of the platform trust chain.
- Enterprise patch triage must account for cumulative risk.
- Attackers value bugs that fit into exploitation chains.
Detection and Response Considerations
The best response to a credible local EoP issue is to assume it may be used in combination with another compromise. Security teams should therefore watch for suspicious parent-child process relationships, unauthorized privilege transitions, and unusual behavior from user-session processes. The point is not just to detect the CVE itself, but to notice the shape of the escalation attempt.Logging is especially important. When privilege escalation is involved, attackers often try to alter telemetry, disable protections, or clean up artifacts quickly. If security monitoring is weak or centralized logging is incomplete, post-exploitation investigation becomes much harder.
What defenders should watch
Process creation patterns can reveal the initial foothold and follow-on escalation. Look for common markers such as unexpected administrative activity from a standard-user session, odd spawned binaries, or repeated crashes in UI-related processes preceding compromise. Subtle anomalies matter more than dramatic ones here.Memory and system integrity tools can also help, but only if they are already deployed and healthy before an incident starts. If a local EoP bug is chained with tampering or defense evasion, delayed deployment may be too late to help. That is why preparation matters more than emergency improvisation.
A disciplined response plan should also include rapid validation of patch state and a communication path for business owners. Some teams will need to prioritize high-value endpoints first, especially administrator workstations and systems used to access sensitive credentials. In a real incident, those are the machines that can do the most damage the fastest.
- Monitor privilege transitions and admin-like behavior.
- Watch for suspicious process chains from user sessions.
- Centralize logs before an incident begins.
- Check patch status on high-value systems first.
- Preserve evidence before remediation destroys it.
- Assume chaining with another vulnerability is possible.
Why Microsoft’s Advisory Language Matters
Microsoft’s wording around vulnerability confidence is more than bureaucratic polish. It is one of the signals defenders use to judge whether a report is merely theoretical or practically actionable. A confidence-oriented description often means the company has enough internal evidence, researcher input, or corroboration to treat the issue as real.That matters because not all CVEs are equal in public maturity. Some arrive with detailed exploitation narratives, while others arrive with little more than a name and a risk category. The latter can still be dangerous if the underlying component is sensitive and the vendor has enough certainty to publish the issue.
The limits of public detail
Sparse disclosure creates a tension. On one hand, defenders want enough information to assess exposure and create detections. On the other hand, premature technical detail can help attackers reproduce the flaw. Microsoft often tries to balance those concerns, and that is one reason advisory language can seem deliberately restrained.For practitioners, the lesson is to focus on impact class, affected component, and confidence signal. If the vulnerability is a confirmed EoP in a core Windows subsystem, then the absence of exploit details should not be mistaken for low urgency. Unknown mechanics are still mechanics.
This is also where historical experience matters. Windows EoP bugs have repeatedly been chained into larger attacks, even when the initial advisory was not dramatic. The real-world risk lies in how the bug can be used, not just in how much technical prose accompanies the CVE page.
- Advisory wording helps estimate maturity.
- Sparse detail does not equal low priority.
- Component sensitivity drives risk.
- Confidence signals are actionable for triage.
- Chaining is the default attacker strategy.
Strengths and Opportunities
Microsoft’s handling of CVE-2026-27911 reflects a security model that is increasingly honest about uncertainty while still giving defenders something useful to act on. The clarity of the component name, the elevation-of-privilege classification, and the confidence framing all help professionals prioritize. That is a real strength, especially in a month where patch fatigue can cause teams to miss the most important issues.The opportunity for defenders is to use this disclosure as a reminder to harden the whole escalation path, not just the one CVE. That means tighter patch discipline, better logging, and more restraint around local admin rights. In other words, the vulnerability is also a chance to reduce the blast radius of any future flaw.
- Clear risk class helps teams understand operational importance.
- Core Windows component makes the issue relevant across many deployments.
- Confidence-based framing improves triage decisions.
- Patch prioritization can be aligned with high-value endpoints.
- Defense-in-depth improvements reduce future escalation risk.
- User-rights hygiene can limit attacker payoff.
- Incident readiness becomes easier when monitoring is already strong.
Risks and Concerns
The main concern is that local escalation bugs are often underestimated because they are not remote code execution flaws. That is a mistake. Once an attacker has a foothold, privilege escalation can be the difference between a contained event and a full breach, and the Windows UI/Core label suggests the affected surface is close to the system’s trust machinery.Another concern is detection lag. If the public technical details remain sparse, defenders may not have highly specific signatures to lean on. That can slow monitoring, especially in smaller environments that do not have deep behavioral analytics. The result is that the bug may be patched before defenders fully understand how it was abused.
- Local footholds can still become full compromises.
- Sparse details can delay precise detection.
- Shared workstations raise practical exposure.
- Unpatched laptops remain a recurring weak point.
- Administrative accounts increase attacker payoff.
- Chained attacks are harder to spot than standalone exploits.
- Overconfidence in “Important” rather than “Critical” labels can mislead teams.
Looking Ahead
What matters next is not whether CVE-2026-27911 sounds dramatic in isolation, but whether organizations treat it as part of a broader local escalation problem in Windows. If Microsoft’s confidence signal holds, then defenders should expect the flaw to be taken seriously by exploit researchers and threat actors alike, even if the public does not yet have a full teardown. That is the nature of high-value Windows EoP issues: they often look modest right up until they are chained into something bigger.The most useful response is disciplined, not theatrical. Patch quickly, verify coverage, watch for suspicious privilege changes, and reduce the number of places where a low-privilege compromise can matter. That approach will pay off whether CVE-2026-27911 is ever widely exploited or not.
- Confirm patch deployment across all supported builds.
- Review endpoints used by privileged users.
- Tighten monitoring around elevation events.
- Reduce standing admin rights where possible.
- Keep incident response playbooks ready for escalation cases.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: