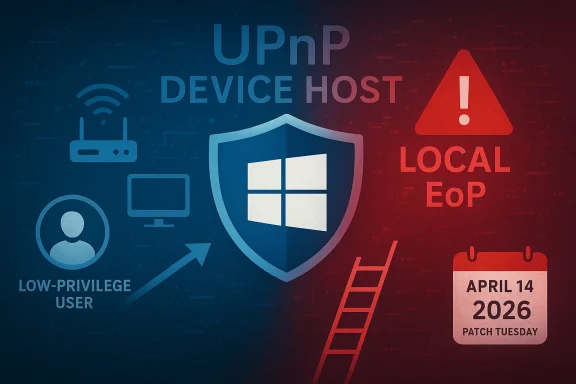
CVE-2026-27920 lands in familiar territory for Windows defenders: a local elevation-of-privilege flaw in the Windows UPnP Device Host service, with Microsoft’s April 14, 2026 update closing the hole across a wide range of client and server builds. Early technical summaries describe the issue as an untrusted pointer dereference, a class of bug that can be especially dangerous when it lives in a service reachable by local attackers with low privileges. The practical message for administrators is straightforward: this is the kind of vulnerability that turns a foothold into a full takeover, so patch timing matters. (feedly.com)
The Windows UPnP Device Host has been a recurring security theme for years, and CVE-2026-27920 fits a pattern Microsoft customers have seen before. UPnP-related flaws in Windows often sit at the junction of legacy device discovery, service privileges, and parser-style memory handling, which makes them a persistent target for privilege escalation. In other words, the component is old enough to be deeply embedded in the platform, but exposed enough to remain interesting to attackers.
What makes CVE-2026-27920 notable is not that it is remote or wormable, but that it is the kind of flaw attackers prize after they already have a beachhead. Microsoft and third-party vulnerability feeds describe the attack vector as local, with low attack complexity and low privileges required, which means an authenticated low-privilege user is the likely starting point. That profile is especially relevant in enterprise environments where one compromised endpoint can become the launchpad for broader lateral movement. (feedly.com)
The technical description also points to a long-standing class of Windows bugs: pointer handling failures. An untrusted pointer dereference often suggests that the service trusted memory references it should not have trusted, and that generally implies a path to memory corruption, privilege boundary abuse, or both. While the exact exploitation technique is not public in the sources reviewed here, the vulnerability class itself is well understood enough to inform defensive priority. (feedly.com)
Microsoft’s April 14, 2026 security update appears to be the authoritative fix point, and the affected footprint is broad. The published affected builds span Windows 10, Windows 11, and multiple server generations, which means this is not a niche workstation-only issue. It is a platform-wide hardening event for any organization that still has Windows systems running the UPnP Device Host service or related dependencies. (feedly.com)
Microsoft’s update cadence matters here. CVE-2026-27920 was published on April 14, 2026, alongside fixes that, according to the public vulnerability feed, shipped the same day. That puts the issue squarely in Patch Tuesday territory, meaning defenders should treat it as part of a broader monthly maintenance cycle rather than a one-off emergency bulletin. Still, local privilege escalation bugs are never merely routine when they touch a widely deployed service component. (feedly.com)
At the same time, the amount of exploit detail is limited. There is no public proof-of-concept noted in the feed reviewed here, and no evidence of exploitation in the wild at the time of publication. That combination usually means defenders should act on the risk model, not on observed abuse. Absence of public exploitation is not absence of danger, especially for local privilege escalation bugs that can be chained after phishing, malware, or stolen credentials. (feedly.com)
Older Microsoft security bulletins around UPnP provide useful context. They show that the platform has historically had to deal with UPnP memory corruption and network-facing attack surface concerns, including cases where Microsoft recommended disabling or restricting service exposure in specific circumstances. That history does not mean this year’s bug is identical, but it does explain why defenders should not dismiss UPnP as an obscure corner of the OS.
That is why privilege escalation flaws in such components often feel disproportionately important. They may not trigger a dramatic network-wide incident on their own, but they are the exact sort of bug attackers use to harden persistence and defeat least-privilege assumptions. In a modern intrusion chain, that step is often what separates “contained incident” from “environmental compromise.” (feedly.com)
For defenders, the key takeaway is that the bug lives in a privilege-bearing Windows service, not in a low-value helper process. That matters because the impact of a successful exploit is amplified by the service’s authority. If the attacker can steer execution or corrupt state in the right way, SYSTEM-level compromise becomes the logical end point rather than a theoretical possibility. (feedly.com)
The score, 7.8, is important but not the whole story. High-scoring local bugs are often underestimated because they lack the dramatic surface area of remote code execution, but their operational value to attackers can be enormous. A local bug is often a second-stage bug, and second-stage bugs are what make initial access durable. (feedly.com)
The broad product coverage also raises the stakes for patch management. Windows 10, Windows 11, and several server builds are listed as affected, which means mixed fleets will need coordinated remediation. Organizations with dormant or “forgotten” systems are often the ones most likely to miss this kind of update, especially when legacy server editions remain in service. (feedly.com)
Enterprises should also assume that once a workstation is compromised, local escalation opportunities will be actively searched for. Modern commodity malware, post-exploitation frameworks, and hands-on-keyboard attackers all look for ways to convert a user-session foothold into administrative control. CVE-2026-27920 belongs squarely in that category of “make the intruder much harder to evict” vulnerability. (feedly.com)
The consumer story is often about depth of compromise rather than initial infection. A successful attacker with standard-user access may use this bug to disable protections, install additional malware, or obtain access to browser data and stored credentials. That makes the flaw relevant even for households that are not targeted by sophisticated threat actors. (feedly.com)
This issue also underscores why “I only use this PC for browsing” is not a meaningful defense. A low-privilege foothold on a home PC is enough for local escalation to become relevant, especially if the user installs untrusted software or reuses credentials across services. As always, the right posture is layered: patching, account hygiene, and restraint around software provenance. (feedly.com)
Risk-based prioritization still matters. Systems with broad user access, internet-adjacent exposure, or frequent use by third-party support staff should move up the queue. Even though the exploit is local, the impact of a compromise on such systems can be disproportionate because they may contain cached credentials, sensitive documents, or tools that aid lateral movement. (feedly.com)
It is also worth reinforcing least privilege. While least privilege will not prevent the bug from existing, it reduces the blast radius of the initial foothold and may complicate exploitation chains. Security teams should think in terms of friction: every added constraint makes the attacker spend more time, leave more traces, and take more risks. (feedly.com)
The broader market implication is that defenders increasingly have to treat endpoint patching as a race against chaining behavior. Even if there is no public exploit today, local EoP bugs can become valuable once paired with phishing, browser compromise, macro abuse, or malicious installers. That is why vulnerability severity should be interpreted in the context of intruder workflow, not just initial access mechanics. (feedly.com)
That makes disclosure timing especially important. The more rapidly patches are installed after publication, the less opportunity attackers have to build exploit chains around the bug. Conversely, the longer organizations delay, the more time they give adversaries to test the waters even without a public proof-of-concept. Delay is a security decision, whether organizations want to frame it that way or not. (feedly.com)
There is also an opportunity for defenders to use this event as a governance check. If a local privilege escalation flaw in a legacy Windows service is present across a large fleet, that is a useful reminder to verify patch hygiene, remove unnecessary admin rights, and audit the systems that fall outside normal management. Security maturity often improves when a single CVE exposes process gaps. (feedly.com)
Another risk is patch incompleteness. Mixed Windows fleets, offline systems, and legacy servers often lag behind core desktop devices, and those are precisely the systems where hidden exposure can persist. The most dangerous vulnerabilities are sometimes the ones sitting quietly in unmanaged corners. (feedly.com)
It will also be worth watching whether additional UPnP-related bugs surface in subsequent updates or third-party analysis. Legacy Windows services often attract repeated scrutiny once one flaw is exposed, and that can lead to a cluster of related discoveries. In the meantime, the practical path is unglamorous but effective: patch, verify, reduce privileges, and assume compromised endpoints will seek exactly this kind of escalation opportunity. (feedly.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
The Windows UPnP Device Host has been a recurring security theme for years, and CVE-2026-27920 fits a pattern Microsoft customers have seen before. UPnP-related flaws in Windows often sit at the junction of legacy device discovery, service privileges, and parser-style memory handling, which makes them a persistent target for privilege escalation. In other words, the component is old enough to be deeply embedded in the platform, but exposed enough to remain interesting to attackers.What makes CVE-2026-27920 notable is not that it is remote or wormable, but that it is the kind of flaw attackers prize after they already have a beachhead. Microsoft and third-party vulnerability feeds describe the attack vector as local, with low attack complexity and low privileges required, which means an authenticated low-privilege user is the likely starting point. That profile is especially relevant in enterprise environments where one compromised endpoint can become the launchpad for broader lateral movement. (feedly.com)
The technical description also points to a long-standing class of Windows bugs: pointer handling failures. An untrusted pointer dereference often suggests that the service trusted memory references it should not have trusted, and that generally implies a path to memory corruption, privilege boundary abuse, or both. While the exact exploitation technique is not public in the sources reviewed here, the vulnerability class itself is well understood enough to inform defensive priority. (feedly.com)
Microsoft’s April 14, 2026 security update appears to be the authoritative fix point, and the affected footprint is broad. The published affected builds span Windows 10, Windows 11, and multiple server generations, which means this is not a niche workstation-only issue. It is a platform-wide hardening event for any organization that still has Windows systems running the UPnP Device Host service or related dependencies. (feedly.com)
What Microsoft Has Said
The available public description is concise but useful. The vulnerability is labeled a Windows Universal Plug and Play Device Host Elevation of Privilege Vulnerability, with the core failure described as an untrusted pointer dereference. The result, if exploited, is local privilege escalation to SYSTEM, which is the standard Windows benchmark for a catastrophic post-compromise outcome. (feedly.com)Microsoft’s update cadence matters here. CVE-2026-27920 was published on April 14, 2026, alongside fixes that, according to the public vulnerability feed, shipped the same day. That puts the issue squarely in Patch Tuesday territory, meaning defenders should treat it as part of a broader monthly maintenance cycle rather than a one-off emergency bulletin. Still, local privilege escalation bugs are never merely routine when they touch a widely deployed service component. (feedly.com)
Confidence and disclosure quality
The confidence metric attached to the CVE description is effectively about how certain we can be that the flaw exists and how much technical detail is known. In this case, the certainty is relatively high because the vulnerability has been formally assigned a CVE, described by Microsoft-linked sources, and accompanied by a patch. That is materially different from a rumor, a conjecture, or a third-party only finding. (feedly.com)At the same time, the amount of exploit detail is limited. There is no public proof-of-concept noted in the feed reviewed here, and no evidence of exploitation in the wild at the time of publication. That combination usually means defenders should act on the risk model, not on observed abuse. Absence of public exploitation is not absence of danger, especially for local privilege escalation bugs that can be chained after phishing, malware, or stolen credentials. (feedly.com)
- High confidence that the vulnerability exists.
- Moderate technical detail publicly available.
- No public exploit reported in the reviewed sources.
- Patch available immediately on April 14, 2026.
- Local attacker model makes internal compromise scenarios more likely. (feedly.com)
Why UPnP Bugs Keep Reappearing
UPnP remains a surprisingly durable source of security issues because it lives at the intersection of convenience and legacy complexity. The component was built to simplify device discovery and service exposure, but its history in Windows shows that any service doing network-adjacent parsing and device coordination can become a privilege boundary problem. Once a service holds elevated rights, the quality of its memory handling becomes a critical security property.Older Microsoft security bulletins around UPnP provide useful context. They show that the platform has historically had to deal with UPnP memory corruption and network-facing attack surface concerns, including cases where Microsoft recommended disabling or restricting service exposure in specific circumstances. That history does not mean this year’s bug is identical, but it does explain why defenders should not dismiss UPnP as an obscure corner of the OS.
Historical pattern
The broader pattern is familiar: a long-lived service accumulates multiple generations of code paths, compatibility logic, and privileged behavior. Over time, that creates a wide attack surface even when the feature is not actively used by most end users. For enterprises, the real issue is not whether UPnP is glamorous; it is whether the service remains present, running, and reachable enough to matter.That is why privilege escalation flaws in such components often feel disproportionately important. They may not trigger a dramatic network-wide incident on their own, but they are the exact sort of bug attackers use to harden persistence and defeat least-privilege assumptions. In a modern intrusion chain, that step is often what separates “contained incident” from “environmental compromise.” (feedly.com)
- Legacy platform services tend to accrete risk over time.
- Convenience features often outlive their original threat models.
- Privilege escalation bugs are especially dangerous after initial compromise.
- UPnP has a documented history of security scrutiny in Windows.
Technical Significance
An untrusted pointer dereference is not just a generic memory bug label. It usually signals that the service accepted a pointer value or pointer-like structure from an untrusted source without enough validation, then used it in a privileged context. In practical terms, that can produce crashes, memory corruption, or a controllable code execution pathway if the surrounding conditions are favorable. (feedly.com)For defenders, the key takeaway is that the bug lives in a privilege-bearing Windows service, not in a low-value helper process. That matters because the impact of a successful exploit is amplified by the service’s authority. If the attacker can steer execution or corrupt state in the right way, SYSTEM-level compromise becomes the logical end point rather than a theoretical possibility. (feedly.com)
What the CVSS profile tells us
The published CVSS vector shown in the feed is AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H, which is the classic signature of a local privilege escalation flaw with severe confidentiality, integrity, and availability consequences. Low attack complexity and low privileges required mean the vulnerability may be easier to weaponize once an attacker already has a standard user account. In enterprise terms, that is exactly the kind of bug that turns “one endpoint compromised” into “the box is effectively lost.” (feedly.com)The score, 7.8, is important but not the whole story. High-scoring local bugs are often underestimated because they lack the dramatic surface area of remote code execution, but their operational value to attackers can be enormous. A local bug is often a second-stage bug, and second-stage bugs are what make initial access durable. (feedly.com)
- Low attack complexity raises practical risk.
- Low privileges required means a basic user foothold can be enough.
- No user interaction reduces friction for chaining.
- High CIA impact suggests full compromise potential. (feedly.com)
Enterprise Exposure
Enterprises should treat CVE-2026-27920 as a post-exploitation enabler rather than an isolated endpoint bug. In a managed environment, the main question is how quickly an attacker can go from a standard account or lightly privileged service context to full local control. Once that happens, tampering with security agents, stealing credentials, or modifying scheduled tasks becomes much easier. (feedly.com)The broad product coverage also raises the stakes for patch management. Windows 10, Windows 11, and several server builds are listed as affected, which means mixed fleets will need coordinated remediation. Organizations with dormant or “forgotten” systems are often the ones most likely to miss this kind of update, especially when legacy server editions remain in service. (feedly.com)
Operational realities
From an operational standpoint, the biggest challenge is not understanding that the bug is dangerous; it is ensuring that all relevant systems actually receive the fix. Patch compliance reporting often looks clean until a server or workstation falls off the management plane, remains disconnected, or sits in a staging OU longer than intended. That is the sort of blind spot local privilege escalation bugs exploit indirectly. (feedly.com)Enterprises should also assume that once a workstation is compromised, local escalation opportunities will be actively searched for. Modern commodity malware, post-exploitation frameworks, and hands-on-keyboard attackers all look for ways to convert a user-session foothold into administrative control. CVE-2026-27920 belongs squarely in that category of “make the intruder much harder to evict” vulnerability. (feedly.com)
- Prioritize endpoint fleets with standard-user-heavy populations.
- Validate patch deployment on server editions, not just clients.
- Check for systems outside the normal management lifecycle.
- Assume intruders will chain this with credential theft or persistence tooling. (feedly.com)
Consumer Impact
For consumers, the risk profile is narrower but still real. Home users rarely think about UPnP Device Host as a security exposure, yet the service exists to support Windows networking features and related device interactions. If a consumer machine is already compromised by a malicious download, cracked software, or remote support scam, a local privilege escalation flaw can be the last step that hands the attacker full control. (feedly.com)The consumer story is often about depth of compromise rather than initial infection. A successful attacker with standard-user access may use this bug to disable protections, install additional malware, or obtain access to browser data and stored credentials. That makes the flaw relevant even for households that are not targeted by sophisticated threat actors. (feedly.com)
What users should think about
Most consumers do not need to understand the internals of UPnP Device Host to benefit from the fix. They need to make sure Windows Update is allowed to do its job promptly, and they should avoid delaying security updates for convenience. In the consumer world, patch lag is often the real vulnerability amplifier. (feedly.com)This issue also underscores why “I only use this PC for browsing” is not a meaningful defense. A low-privilege foothold on a home PC is enough for local escalation to become relevant, especially if the user installs untrusted software or reuses credentials across services. As always, the right posture is layered: patching, account hygiene, and restraint around software provenance. (feedly.com)
- Keep Windows fully updated.
- Avoid running daily activities under administrative accounts.
- Treat cracked or unsigned software as a major risk.
- Assume one compromise can become a full-system compromise. (feedly.com)
Patch and Mitigation Strategy
The most direct action is also the most important: install the April 14, 2026 Microsoft security update. The sources reviewed indicate a patch is available and that affected builds have specific version thresholds for remediation, covering both client and server operating systems. That makes this a classic “patch first, analyze later” vulnerability for most environments. (feedly.com)Risk-based prioritization still matters. Systems with broad user access, internet-adjacent exposure, or frequent use by third-party support staff should move up the queue. Even though the exploit is local, the impact of a compromise on such systems can be disproportionate because they may contain cached credentials, sensitive documents, or tools that aid lateral movement. (feedly.com)
Practical response steps
A sensible response plan is simple, but it must be executed carefully. First, inventory affected Windows versions. Second, confirm patch deployment through endpoint management or direct build checks. Third, watch for service anomalies or suspicious local privilege escalation behavior, especially on systems where the UPnP Device Host service is present and active. (feedly.com)It is also worth reinforcing least privilege. While least privilege will not prevent the bug from existing, it reduces the blast radius of the initial foothold and may complicate exploitation chains. Security teams should think in terms of friction: every added constraint makes the attacker spend more time, leave more traces, and take more risks. (feedly.com)
- Identify affected Windows client and server builds.
- Deploy the April 14, 2026 update broadly.
- Verify installation against build-number thresholds.
- Review local privilege and admin-rights policies.
- Monitor for suspicious service behavior or escalation attempts. (feedly.com)
- Patch deployment should be tracked at the device level.
- Server fleets need the same attention as desktops.
- Least privilege remains a valuable compensating control.
- Monitoring is a supplement, not a substitute, for patching. (feedly.com)
Threat Landscape Implications
CVE-2026-27920 is another reminder that the modern Windows threat landscape is layered. Attackers do not need every vulnerability to be remote, exploitable from the internet, or publicly weaponized to make progress. They need reliable stepping stones, and local privilege escalation flaws in common services are among the most reliable stepping stones available. (feedly.com)The broader market implication is that defenders increasingly have to treat endpoint patching as a race against chaining behavior. Even if there is no public exploit today, local EoP bugs can become valuable once paired with phishing, browser compromise, macro abuse, or malicious installers. That is why vulnerability severity should be interpreted in the context of intruder workflow, not just initial access mechanics. (feedly.com)
Why this matters beyond one CVE
For security teams, the lesson is not “panic over UPnP,” but “remember how modern intrusions work.” One low-privilege session can be enough to move sideways into persistence, to tamper with telemetry, or to open the door to domain credential theft. A flaw like this does not have to be famous to be useful; it only has to be dependable. (feedly.com)That makes disclosure timing especially important. The more rapidly patches are installed after publication, the less opportunity attackers have to build exploit chains around the bug. Conversely, the longer organizations delay, the more time they give adversaries to test the waters even without a public proof-of-concept. Delay is a security decision, whether organizations want to frame it that way or not. (feedly.com)
- Local EoP flaws are high-value chaining components.
- Attackers often arrive through less privileged footholds.
- Timely patching reduces the window for weaponization.
- Service bugs can matter more than their headline score suggests. (feedly.com)
Strengths and Opportunities
The strongest aspect of Microsoft’s handling here is clarity: the vulnerability has a named CVE, a clear impact statement, and an apparently immediate patch window. That gives administrators a concrete remediation target, which is often half the battle in real-world defense. The breadth of affected versions also gives organizations a chance to fold this into standard Patch Tuesday operations rather than treating it as a mystery issue. (feedly.com)There is also an opportunity for defenders to use this event as a governance check. If a local privilege escalation flaw in a legacy Windows service is present across a large fleet, that is a useful reminder to verify patch hygiene, remove unnecessary admin rights, and audit the systems that fall outside normal management. Security maturity often improves when a single CVE exposes process gaps. (feedly.com)
- Clear patch availability on the publication date.
- Broad vendor and platform coverage for remediation.
- Good fit for existing endpoint management workflows.
- Useful catalyst for least-privilege reviews.
- Opportunity to inventory exposed legacy systems.
- Chance to validate monitoring and patch compliance reporting.
- Better visibility into service-level attack surface. (feedly.com)
Risks and Concerns
The main concern is that local privilege escalation bugs are easy to underestimate in environments focused on perimeter defense. If a team assumes “local only” means low urgency, it may leave a highly actionable post-compromise path open long after initial access. That is a dangerous assumption in an era where commodity malware and targeted intrusions both commonly seek privilege escalation as a next step. (feedly.com)Another risk is patch incompleteness. Mixed Windows fleets, offline systems, and legacy servers often lag behind core desktop devices, and those are precisely the systems where hidden exposure can persist. The most dangerous vulnerabilities are sometimes the ones sitting quietly in unmanaged corners. (feedly.com)
- Organizations may under-prioritize a local flaw.
- Legacy servers may miss the update.
- Unmanaged endpoints can remain exposed.
- Attackers can chain the bug after initial access.
- Security teams may not have service-level telemetry ready.
- Least-privilege assumptions may be weaker than expected.
- Consumers may delay updates for convenience. (feedly.com)
Looking Ahead
The key thing to watch is whether more technical detail emerges about the root cause and exploitability. If researchers or Microsoft later release additional context, defenders will have a better sense of whether this was primarily a memory-safety issue, a logic flaw, or a service boundary failure with broader implications. For now, the prudent approach is to treat it as a confirmed, severe local escalation vector and act accordingly. (feedly.com)It will also be worth watching whether additional UPnP-related bugs surface in subsequent updates or third-party analysis. Legacy Windows services often attract repeated scrutiny once one flaw is exposed, and that can lead to a cluster of related discoveries. In the meantime, the practical path is unglamorous but effective: patch, verify, reduce privileges, and assume compromised endpoints will seek exactly this kind of escalation opportunity. (feedly.com)
- Monitor whether Microsoft updates the advisory with more technical detail.
- Verify patch deployment across all affected Windows versions.
- Watch for reports of in-the-wild exploitation or proof-of-concept code.
- Review whether UPnP-related services are necessary on every system.
- Strengthen local admin controls and endpoint monitoring. (feedly.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center