 Background
Background
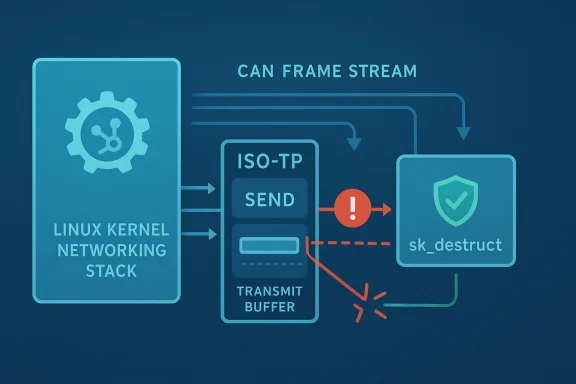
CVE-2026-31474 is a Linux kernel use-after-free in the CAN ISO-TP path, specifically in isotp_sendmsg, where the transmit buffer can be freed too early while the sender is still consuming it for the final CAN frame. The kernel record describes a race between isotp_sendmsg and isotp_release: the release side waits for the socket state to become idle, but a signal can interrupt that wait and let teardown continue while transmit still references so->tx.buf. The result is a classic lifetime bug in a highly timing-sensitive networking path. The vulnerability was published from kernel.org on April 22, 2026, and Microsoft’s update guide mirrors that disclosure, making it visible to enterprise patch-management workflows as well as kernel watchers. l, the problem is not that the buffer is always freed incorrectly; it is that the code assumes the state machine will serialize teardown and transmit in a way that signals can break. The record notes that so->tx.buf may be allocated once when the standard transmit buffer length needs to be extended, which makes the object even more important to keep alive until every user is done with it. That is why the fix moves the kfree of the potentially extended buffer to sk_destruct time, when both isotp_sendmsg and isotp_release are finished.This is exactly thehat looks narrow but deserves attention. ISO-TP is not a flashy desktop feature; it is the transport framing layer used with CAN, often in automotive, industrial, and embedded systems. In those environments, reliability matters as much as confidentiality, and a memory safety flaw in a protocol send path can become a crash, a hang, or a hard-to-diagnose communication failure. Even when an exploit path is unclear, a use-after-free in kernel networking code is serious because it can destabilize a system that is expected to keep running in real time.
The change history confirms the upstreamtion, with several stable-branch commit references attached to the CVE entry. That pattern is important because it means this is not just a theoretical bug report; it is a concrete patch lineage that downstream vendors can backport. For operators, the practical question is less “does the CVE exist?” and more “does my distro or appliance kernel include the fix yet?”
Overview
Linux CAN ISO-TP, short for ISO 15765-2 transpor carry messages larger than a single CAN frame can hold. The kernel documentation describes the stack as a socket-based transport that can block transmit operations until frames are sent, and it supports features such as extended addressing and waiting for TX completion. That makes it a stateful protocol layer, which in turn makes teardown and transmit lifetime management especially delicate.The vulnerability sits in that boundary between protocol state and object ownership.
isotp_sendmsg uses only cmpxchg on so->tx.state to serialize access to the transmit buffer, but that serialization is only as good as the assumptions around the rest of the socket lifecycle. If isotp_release can leave its wait early due to a signal and proceed to shutdown and free the buffer while the send path still references it, the buffer can disappear under active use. That is a lifetime mismatch, not a parsing bug or an arithmetic bug, and those are often the hardest kernel defects to reason about because every branch seems individually defensible.telling. Rather than trying to make the shutdown path “smarter” with more state checks, the fix defers the final free to
sk_destruct, which is the point where the socket object itself is guaranteed to be done. In other words, the kernel moves from “free when we think nobody is using it” to “free when the socket’s lifetime truly ends.” That is a conservative and usually effective way to close a race in a concurrent subsystem.This also fits a brot Linux kernel CVEs: many of the serious bugs are not giant buffer overflows anymore, but subtle synchronization and teardown issues in code that runs often enough to matter and rarely enough to evade casual testing. The fact that this CVE was assigned from kernel.org and immediately surfaced through Microsoft’s security feed shows how quickly a kernel maintenance fix now becomes enterprise-facing vulnerability intelligence.
The Race Condition at the Heart oause is a race between transmit completion and socket teardown. On one side, isotp_sendmsg is still reading so->tx.buf while assembling the final CAN frame in isotp_fill_dataframe. On the other side, isotp_release waits for the socket to reach ISOTP_IDLE, but if a signal interrupts wait_event_interruptible during close, teardown can continue early. That creates a window where the buffer is freed before transmit is done with it.
That window matters because cmpxchg on so->tx.state prot transaction. It can serialize one writer against another, but it does not magically solve the more general question of whether the backing storage still exists. The bug is therefore not “bad locking” in the simple sense; it is an incomplete lifetime model. The state machine says one thing, while the allocator says another.Why signals make this harder
Signals are the destabilizing ingredient here. Thays a signal interruptingwait_event_interruptible can cause close to exit its wait loop while the transmit state is still ISOTP_SENDING. That kind of interruption is normal behavior in Unix-like systems, which is why kernel code must treat interrupted waits as part of the design, not an edge case. If teardown assumes the wait always reaches the tidy state, it is one signal away from a use-after-free.In practical terms, this means the bug is most likely to show up under a pattern that real systems do hien close or teardown, then a signal or other interruption at the wrong moment. It is not the sort of issue that requires exotic input. That makes it more credible as a production problem even if exploitability remains uncertain.
- The send path still needs
so->tx.buffor the final frame. - The release path can be interrupted before the socket becomes proceed while transmit still holds a live reference.
- The result is a use-after-free, not just a harmless state mismatch.
Why the buffer’s allocation matters
The CVE text notes thatso->tx.buf can be allocated once when the standard TX buffer length needs to besubtle but important detail. A buffer that is larger than the default often exists because the protocol needs it for a special case, which means freeing it too early can break exactly the path that is already the least common and least frequently exercised. Those are often the paths where kernel bugs survive longest.A free at the wrong moment here is not just an abstract ownership error. If the sender continues reading memory after free, the result can be corrupted frame content, metadata corruption depending on timing and surrounding memory activity. The public advisory does not claim a specific exploit chain, but memory safety bugs in kernel networking code are never something to shrug off.
What ISO-TP Is and Why It Matters
ISO-TP is the transport mechanism that lets larger diagnostic or control messages ride over CAN’s small frame size. Linux documents it as an ISO ol with options for extended addressing, blocking transmit behavior, and message-framing semantics tailored to CAN. That puts it squarely in the “specialized but important” category: not universal, but critical in the environments that use it.Embedded and automotive relevance
This is the kind of code path that matters most in automotive ECUs, diagnostics tools, industrial controllers, and embedded gateways. In those environments, a crash in the transport layer is not merely a network annoyance; it can break diagnostics, halt communication with subsystems, or force a watchdog reset. The same small buffer-lifetime bug that looks academic on a desktop can be operationally expensive in a vehicle or machine controller.There is also a qualitative difference between consumer and embedded exposure. Most end-user systems are unlikely to use kerneat all, while embedded platforms may rely on them continuously. That means the installed base is smaller, but the dependency is deeper. Bugs in these stacks often have a higher per-system impact even if the total number of affected systems is lower.
- CAN transport is used for messages larger than a single frame.
- ISO-TP is common in diagnostics and control-plane communication.
- Embedded systt more heavily than consumer PCs.
- A teardown race can break functionality even without clear remote exploitation.
Lifecycle bugs in protocol code
Kernel protocol code has a habit of exposing bugs that are not obvious from the outside. A packet can look well-formed while still triggering a teardown path with stale state or a freed buffer. ISO-TP is particularly sensitive because it layers message segmentation and stateful transmission on top of a transport that was never designed for slack or confusion. That makes object lifetime just as important as packet contents.The lesson here is broader than CAN. Any kernel code that mixes asynchronous completion, wait qurruptible teardown has to assume that “waiting for idle” is not the same as “safe to free.” The safest lifetime boundary is often the destructor, not the release path. That is exactly the design change this fix makes.
The Fix: Move Freeing to Socket Destruction
The upstream remedy is elegant in its simplicity: move thekfrely extended transmit buffer tosk_destruct. That means the buffer is only released when the socket object itself is being destroyed, after bothisotp_sendmsgandisotp_release` have completed their work. It removes the race window rather than trying to narrow it.Why sk_destruct is the safer boundary
sk_destruct is a more trustworthy lifecycle event because it is tied to the actual end of t, not just a best-effort release sequence. In kernel terms, that is a stronger guarantee than “the socket looks idle right now.” The record’s rationale is clear: once the transmit path and release path are both done, the extended tx.buf can be freed without risking concurrent access.That also helps explain why the fix is likely to backport cleanly. It is narrowly scoped, local to the ISO-TP socket lifecycle, and does not alter the protocol semantics. The behavior change is internal and defensive, which is the sweet spot maintainers look for when deciding whether to carry a patch into stable trees.
Why not just add more locking?
More locking is not always the right answer. In this case, the underlying issue is that teardown can be interrupted and continue before transmituple more condition checks might reduce the odds, but it would not necessarily align the object’s memory lifetime with the socket’s true end-of-life. By deferring the free, the kernel sidesteps the problem at the ownership level rather than fighting it at the scheduling level.That is a pattern worth noting. When a bug is caused by an object still being in use, a better fix is often to move the release point, not to keep rechecking whether release is “probably” safe. The lto be fragile. The former usually closes the hole more decisively.
- The buffer is no longer freed in the risky release path.
sk_destructbecomes the single safer cleanup point.- The fix reduces dependence on timing and signal behavior.
- The protocol’s outward behavior remains unchaitability and Real-World Risk
What can happen if it is hit
At a minimum, the bug can cause a crash or instability during send/close operations. Depending on timing and allocator behavior, it could also lead to memory corruption, which is the reason kernel use-after-free issues are treatedvisory itself does not claim code execution, and that caution matters; but absence of a proven exploit is not the same thing as absence of risk.In environments that depend on ISO-TP for diagnostics or control traffic, even a non-exploitable crash can be operationally severe. If a single failure causes a controller, gateway, or test device to reset, the practical impact may be service interruption, failed diagnostics, or a chas. Those consequences are often more important to operators than the abstract exploit category.
Why kernel bugs like this are hard to dismiss
A lot of kernel bugs live in the uncomfortable middle ground between “simple bug” and “full-blown exploit.” This one is a good example. It is narrow, race-dependent, and tied to a specialized subsystem, but it still involves freed memory being accessed dut alone makes it worth patching quickly, especially in systems with real-time or always-on expectations.- The issue is race-driven rather than input-driven.
- The direct symptom may be crash or instability.
- The risk profile depends on timing and deployment.
- Embedded systems may care more than consumer desktops.
Enterprise vs Consumer Impact
For most consumers, the immediate exposure is probably low. Typical Windoystems do not use kernel CAN ISO-TP sockets in everyday workflows, and many users will never touch the affected code path. That said, low exposure does not mean no exposure, especially on workstations connected to dautomotive tools, or industrial test gear.Enterprise and embedded users are a different story. Fleets that include CAN-connected devices, gateways, manufacturing controllers, lab benches, or vehicle diagnostic systems should care much more, because those platforms may keep ISO-TP active for long periods and may be sensitive to a single socket teardown failure. A bug that lives in a niche protocol stack can sical if the enterprise depends on that stack for field service or manufacturing workflows.
Consumer profile
Most consumer systems are likely unaffected in practical terms. The bug exists in the kernel, but the feature set required to hit it is specialized. Unless a consumer system is being used for vehicle diagnostics, CAN experimentation, or embedded development, the vulnerable path may never be reachable in normal use.Enterprise profile
Enterprise risk is less a and more about concentration. If a small number of systems are essential to a production line, a telematics lab, or a fleet service workflow, then one kernel crash can have outsized impact. That is why niche kernel CVEs still deserve fleet-wide awareness in organizations that own hardware integration or automotive operations.- Consumerkely to use CAN ISO-TP.
- Development and lab systems are more likely to encounter it.
- Industrial and automotive environments may depend on it heavily.
- Operational continuity matters more than theoretical reachability.
Strengths and Opportunities
This fix has several strengths that make it a good example of kernel maintenance done well. It is narrow, understandable, and aligned with oundary of the socket. It also preserves protocol behavior while eliminating a hard-to-see race, which is exactly the kind of balance maintainers want in stable backports.- It removes a concrete use-after-free window.
- It keeps the patch surface small hifts cleanup to a stronger lifetime boundary.
- It avoids changing the protocol’s user-visible behavior.
- It should be straightforward to backport into stable trees.
- It reduces reliance on signal-sensitive release timing.
- It improves confidence in ISO-TP socket teardown.
Risks and Concerns
The biggest concern is that this bug could be underestimated be and the public record does not yet give it a final severity score. That would be a mistake. Kernel use-after-free flaws are never just bookkeeping mistakes, and a race in transmit teardown can have consequences that range from a clean crash to much uglier memory corruption.- The bug may look “small” because it is in a specialized protocol.
- Crash-only thinking can miss the me.
- Vendors may lag in backporting the fix.
- Timing dependence makes reproduction inconsistent.
- Signal interruptions are easy to overlook in testing.
- Systems with CAN dependence may see severe operational impact.
- Administrators may not realize they rely on ISO-TP at all.
Why timing bugs are especially dangerous
A race like this is hard to spot in ordinary testing because it interaction between send, close, and signal handling. That means some systems may look stable for months and still be vulnerable. Bugs like that are annoying precisely because they do not announce themselves until a rare combination of events lines up.The other risk is false confidence from partial mitigation. A release path that usually waits for idle may seem safe under light testing, but a signaanges the story. The fix acknowledges that reality by moving the free to a point where the kernel can make a stronger guarantee.
Looking Ahead
The immediate thing to watch is downstream backports. The upstream fix is already clear from the CVE record, but many organizations will not run mainline kernels. They will run vendor builds, long-term-support branches, or applianceal-world exposure window depends on how quickly those maintainers pull in the patch.The second thing to watch is whether distributions classify the issue primarily as an availability bug or as a broader memory-safety concern. That matters because patch urgency often tracks severity framing. Even wit score yet, security teams should treat a kernel UAF in a transport send path as something that deserves timely remediation, not just routine backlog placement.
What administrators should check
- Whether their kernel build includes the ISO-TP fix.
- Whether the distro has backported the
sk_destructcleanup change. - Whether CAN/ISO-TP is actually us.
- Whether any embedded or diagnostic systems depend on the vulnerable code path.
- Whether signal-interruptible teardown paths are exercised in testing.
In the end, CVE-2026-31474 is a reminder that the kernel’s hardest bugs are often not the loudest ones. A transmit buffer freed a little too early can be just as dangerous as a more dramatic parser flaw, especially when it lives in a stateful networking layer that depends on precise obatch is small, the reasoning is sound, and the lesson is durable: in kernel code, when you free something can matter as much as whether you free it at all.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center