The Linux kernel’s CAN ISO-TP stack has a newly published security flaw, and while the CVE record is still being enriched, the underlying bug is already clear: a race in
The vulnerability description matters because it does not describe a vague “theoretical race.” It describes a concrete shutdown path:
This is also a good example of why kernel CVEs often look modest in isolation but still deserve attention. A use-after-free in a transport stack does not need to be spectacular to matter. In the kernel, small lifetime mistakes can lead to memory corruption, hard-to-debug crashes, or data integrity problems depending on timing, build options, and surrounding system load. The fact that the buffer can be allocated once when a standard transmit length must be extended makes the bug more subtle, not less: the buffer is not a disposable scratch object, but a stateful transmit asset whose lifetime must cover the whinux kernel community has long used CVEs as a way to track fixes once they are already available in stable trees, and the kernel’s own documentation says CVEs are assigned after a fix exists and is applied to a stable branch. It also emphasizes that applicability depends on how a system actually uses the kernel, which is especially relevant here because many systems will never touch CAN ISO-TP at all. Still, for embedded Linux, automotive stacks, diagnostic tools, and industrial gateways, this is exactly the kind of code path that can sit quietly in production for years.
CAN is a long-lived transport technology with an unusually broad footprint. It is ubiquitous in vehicles, manufacturing equipment, robotics, test benches, and other embedded environments where low-latency message exchange matters more than raw throughput. Linux’s CAN stack therefore carries a special kind of burden: it is not just maintaining networking code, it is maintaining software plumbing for whole classes of devices and tools that may be deployed in safety-sensitive environments.
ISO-TP sits above raw CAN frames and allows larger payloads to be segmented across multiple CAN packets. That segmentation introduces additional state, including transmit buffers, state transitions, frame pacing, and cleanup rules. In practical terms, the more the kernel has to remember about an in-flight message, the more careful it has to be when tearing that message down. The
The CVE description highlights a particularly thorny corner case: a signal can interrupt
Historically, bugs like this appear whenever a subsystem tries to make a release path do too much work. Cleanup code often becomes a magnet for edge cases because it has to reconcile partially completed operations, error handling, user interrupts, and concurrency all at once. In well-factored code, destruction is separated from release precisely so that a resource can survive long enough for all users to stop touching it. That is exactly the designy moving the
There is also a broader kernel-security lesson here. Linux security work in 2026 continues to focus on lifetime correctness, not just overtly dangerous parsing bugs. That trend is visible across networking, netfilter, and transport code: the most consequential issues often arise when one subsystem assumes another has already stopped using a shared object. In other words, ownership is a security boundary, not just a style concern.
The fact that the buffer may be allocated once when the standard transmit length needs to be extended makes the issue even more interesting. The code is not just dealing with a transient packet fragment; it is managing a potentially longer-lived heap allocation that outlives a single syscall. That changes the risk profile, because a free at the wrong moment no longer merely releases a scratch buffer — it invalidates live state.
The change also reflects a broader philosophy in kernel engineering: don’t try to prove that every caller will behave nicely when the object is already in a delicate transition. Instead, keep the resource alive long enough that the remaining users can exit cleanly. That reduces the number of timing assumptions in the code and makes future maintenance safer.
That split is important because vulnerability management is not only about severity scores. It is about relevance. The Linux kernel documentation is explicit that many CVEs are not relevant to every system, since each machine uses only a small subset of the source tree. That means administrators need to map this CVE to actual CAN usage rather than treat it as universally exploitable.
At the same time, “not relevant to everyone” is not a reason to ignore the issue. Embedded and industrial users often run older kernels, vendor-customized builds, or appliance images that lag upstream. Those environments may also be the hardest to reboot or patch quickly, which increases the operational cost of even a narrow bug. Small scope is not the same as small consequence.
This is why memory safety bugs often cluster around cleanup logic. Cleanup is where abstractions get stressed: partially built messages, pending references, interrupted waits, and shutdown transitions all collide. A bug in the steady-state path might be easy to reason about, but a bug in the release path can hide behind ordinary usage for a long time. Destructor bugs are nasty because they often lie dormant until someone closes the socket at exactly the wrong moment.
A useful way to think about this CVE is to compare it with other kernel lifetime fixes: if the object can still be observed by any valid path, then freeing it early is unsafe even if the “main” operation seems complete. That is why the patch moves the free later instead of trying to make the release path smarter in place. When the root problem is ownership ambiguity, the correct answer is to simplify ownership, not to add more branching.
There is also a subtle lesson for security teams that track mixed estates. Linux kernel CVEs increasingly appear alongside Windows and Microsoft-tracked vulnerabilities in the same enterprise dashboards, even when the underlying systems are very different. That can be useful because it normalizes patch triage across platforms, but it can also blur the difference between “globally urgent” and “relevant to a small deployment segment.” Good teams will use the CVE record as a signal, not as a substitute for environment knowledge.
This also reflects a broader truth about Linux security work in 2026: many of the best fixes are not glamorous. They are structural. They remove ambiguity, shrink race windows, and align cleanup with actual object lifetime. In a code base as large as the kernel, that kind of precision is often more valuable than a clever but brittle workaround.
Another concern is patch propagation. Kernel fixes often reach end users through vendor backports, and the version number alone may not show whether a given system is protected. That creates an audit problem for administrators who assume they can read a single release number and be done. In practice, security teams should verify the presence of the specific fix, not just the kernel family.
There is also a broader ecosystem risk: CAN stacks frequently exist in devices that are patched slowly, remotely, or not at all. If a vulnerability is published for such a subsystem, the threat window can remain open far longer than it would for consumer software. That makes responsible disclosure and rapid stable-tree backporting especially important in this part of the kernel.
For administrators, the takeaway is not fear but discipline. If your systems use CAN ISO-TP, this is a real maintenance item. If they do not, it is still a useful reminder that kernel security is often decided by the smallest details: who owns a buffer, when a wait can be interrupted, and exactly which point in the object lifecycle is truly safe to free memory.
CVE-2026-31474 is not the kind of bug that dominates headlines, but it is exactly the kind of bug that teaches the kernel’s most enduring lesson: in low-level code, lifetime is security. The fix is appropriately restrained, the risk is concentrated but real, and the right response is to patch, verify, and keep an eye on the systems that actually exercise this transport path.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
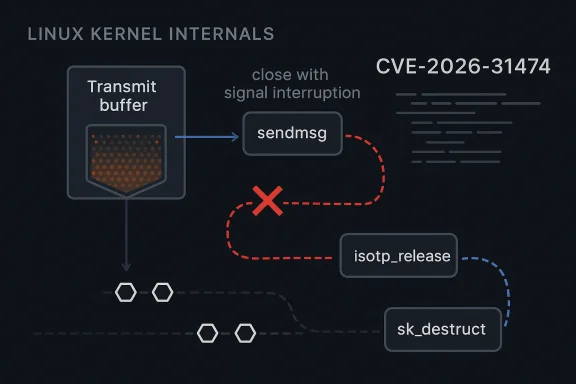
isotp_sendmsg can let so->tx.buf be freed while transmit code is still reading from it. Microsoft’s Security Update Guide has surfaced the issue as CVE-2026-31474, and the kernel-side description points to a narrow but serious use-after-free in a networking path that can be triggered during socket close under signal interruption. The fix is not a dramatic redesign; it is a lifetime correction, moving the free of the potentially extended transmit buffer to sk_destruct so the buffer survives until both send and release paths are truly finished. ortant thing to understand about this CVE is that it lives in a subsystem many administrators barely think about until they need it. ISO 15765-2, or ISO-TP, is the Linux implementation of a higher-level transport over CAN, and the kernel documentation shows that once a socket is created and bound, applications can use standard interfaces such as sendmsg and recvmsg to move payload data over the stack. That makes the code look conventional from userspace, but underneath, it is a specialized transport with its own state machine, flow-control behavior, and timing assumptions.The vulnerability description matters because it does not describe a vague “theoretical race.” It describes a concrete shutdown path:
isotp_sendmsg uses cmpxchg on so->tx.state to serialize access to so->tx.buf, while isotp_release waits for ISOTP_IDLE and then frees the buffer. If a signal interrupts the wait_event_interruptible inside close while transmission is still in progress, the release path can proceed too early and free the buffer while the send path is still reading from it for the final CAN frame. That is classic kernel lifetime trouble: one path assumes ownership has ended, anotherject is valid.This is also a good example of why kernel CVEs often look modest in isolation but still deserve attention. A use-after-free in a transport stack does not need to be spectacular to matter. In the kernel, small lifetime mistakes can lead to memory corruption, hard-to-debug crashes, or data integrity problems depending on timing, build options, and surrounding system load. The fact that the buffer can be allocated once when a standard transmit length must be extended makes the bug more subtle, not less: the buffer is not a disposable scratch object, but a stateful transmit asset whose lifetime must cover the whinux kernel community has long used CVEs as a way to track fixes once they are already available in stable trees, and the kernel’s own documentation says CVEs are assigned after a fix exists and is applied to a stable branch. It also emphasizes that applicability depends on how a system actually uses the kernel, which is especially relevant here because many systems will never touch CAN ISO-TP at all. Still, for embedded Linux, automotive stacks, diagnostic tools, and industrial gateways, this is exactly the kind of code path that can sit quietly in production for years.
 Background
Background
CAN is a long-lived transport technology with an unusually broad footprint. It is ubiquitous in vehicles, manufacturing equipment, robotics, test benches, and other embedded environments where low-latency message exchange matters more than raw throughput. Linux’s CAN stack therefore carries a special kind of burden: it is not just maintaining networking code, it is maintaining software plumbing for whole classes of devices and tools that may be deployed in safety-sensitive environments.ISO-TP sits above raw CAN frames and allows larger payloads to be segmented across multiple CAN packets. That segmentation introduces additional state, including transmit buffers, state transitions, frame pacing, and cleanup rules. In practical terms, the more the kernel has to remember about an in-flight message, the more careful it has to be when tearing that message down. The
sendmsg/close interplay is where that care becomes critical.The CVE description highlights a particularly thorny corner case: a signal can interrupt
wait_event_interruptible during socket close. That matters because interruptible waits are essential to responsive systems, but they also mean cleanup code has to handle partial progress gracefully. If the close path interprets “interrupted” as “safe to free now” while transmit still has a reference to the btes a race between teardown and the final data frame assembly.Historically, bugs like this appear whenever a subsystem tries to make a release path do too much work. Cleanup code often becomes a magnet for edge cases because it has to reconcile partially completed operations, error handling, user interrupts, and concurrency all at once. In well-factored code, destruction is separated from release precisely so that a resource can survive long enough for all users to stop touching it. That is exactly the designy moving the
kfree to sk_destruct.There is also a broader kernel-security lesson here. Linux security work in 2026 continues to focus on lifetime correctness, not just overtly dangerous parsing bugs. That trend is visible across networking, netfilter, and transport code: the most consequential issues often arise when one subsystem assumes another has already stopped using a shared object. In other words, ownership is a security boundary, not just a style concern.
What the Bug Actually Does
At the heart of CVE-2026-31474 is a narrow but dangerous sequence.isotp_sendmsg relies on cmpxchg over so->tx.state to coordinate access to the transmit buffer. That means state changes are being used as the gatekeeper for whether the buffer remains valid, but state alone is not enough if another thread or path can still be inside the final frame assembly logic. The bug appears when the teardown side makes a stronger assumption than tctually guarantee.The race window
The race opens whenclose or socket release is interrupted. If wait_event_interruptible returns early and the release path forces ISOTP_SHUTDOWN, the code can proceed to free so->tx.buf even though sendmsg is still using it for isotp_fill_dataframe. That final frame is precisely where the use-after-free becomes observable, because the kernel may dereference memory that has already been returnedhis is the kind of bug that can be hard to reproduce reliably because it depends on timing, signals, and the exact point at which the transmit state machine is interrupted. But hard-to-reproduce is not the same as harmless. Kernel bugs that depend on narrow interleavings can still be serious because they are often the ones that escape normal testing and surface only under load, fuzzing, or adversarial timing. Intermittent bugs are often the most expensive ones in production because they undermine confidence in the whole path.The fact that the buffer may be allocated once when the standard transmit length needs to be extended makes the issue even more interesting. The code is not just dealing with a transient packet fragment; it is managing a potentially longer-lived heap allocation that outlives a single syscall. That changes the risk profile, because a free at the wrong moment no longer merely releases a scratch buffer — it invalidates live state.
s the right home
Moving the free tosk_destruct shifts cleanup to the point where both isotp_sendmsg and isotp_release are truly done. That is a classic kernel lifetime fix: if multiple execution paths can still legitimately touch the object, then destruction must wait until all of them are finished. It is a conservative answer, but conservative is exactly what you want when memory safety is at stake.The change also reflects a broader philosophy in kernel engineering: don’t try to prove that every caller will behave nicely when the object is already in a delicate transition. Instead, keep the resource alive long enough that the remaining users can exit cleanly. That reduces the number of timing assumptions in the code and makes future maintenance safer.
Why This Matters for CAN and Embedded Systems
CAN-related vulnerabilities often get less public attention than desktop or browser bugs, but they can matter just as much operationally. Embedded Linux frequently ships in products that are hard to patch quickly, and CAN-oriented software often sits close to physical systems where uptime, reliability, and deterministic behavior are non-negotiable. A bug in the transport layer may not be an internet-scale issue, but it can still have real-world consequences in industrial and automotive environments.Enterprise versus embedded impact
For general enterprise desktops and servers, exposure is likely limited unless the system explicitly uses CAN and ISO-TP tooling. Many WindowsForum readers will never hit this path on a standard laptop or cloud VM. But the picture changes in embedded fleets, manufacturing controllers, vehicle test harnesses, gateway appliances, and diagnostic rigs, where ISO-TP is not an edge feature but a working part of the stack.That split is important because vulnerability management is not only about severity scores. It is about relevance. The Linux kernel documentation is explicit that many CVEs are not relevant to every system, since each machine uses only a small subset of the source tree. That means administrators need to map this CVE to actual CAN usage rather than treat it as universally exploitable.
At the same time, “not relevant to everyone” is not a reason to ignore the issue. Embedded and industrial users often run older kernels, vendor-customized builds, or appliance images that lag upstream. Those environments may also be the hardest to reboot or patch quickly, which increases the operational cost of even a narrow bug. Small scope is not the same as small consequence.
- Systems using
PF_CANandCAN_ISOTPdeserve immediate review. - Diagnostic tooling that opens and closes ISO-TP sockets repeatedly may surface the bug faster.
- Vendor kernels may carry the fix without obvious version-number changes.
- Long-lived embedded deployments are more likely to be exposed than general-purpose desktops.
- Signal-heavy shutdown paths increase the chance of hitting the race window.
- Patch verification matters more than version counting alone.
Practical meaning of the fix
The remedy suggests that maintainers are treating the buffer as part of the socket’s full lifecycle, not merely the send syscall’s lifecycle. That is a meaningful distinction. In protocol code, teardown often happens in a different context from the original data path, and if resource ownership is not clearly documented in code, future modifications can easily reintroduce the same bug in a different form. Lifecycle clarity is one of the cheapest security controls the kernel has.The Kernel Security Pattern Behind This CVE
CVE-2026-31474 fits a familiar Linux kernel pattern: one execution path believes a resource has reached the end of life, while another path is still using it. That pattern shows up in sockets, netfilter, file systems, drivers, and schedulers alike. The details change, but the core lesson stays the same: state transitions must be synchronized with actual resource ownership, not just with a flag that seems authoritative.State machines are not ownership guarantees
The transmit state machine here is helpful, but not sufficient.so->tx.state tells the code what phase it believes it is in, yet a state variable cannot fully express whether a caller still has a live read from a buffer. When a release path and a send path can overlap, the kernel needs a stronger guarantee than “the state says we’re done.” That is especially true when sigait and short-circuit the intended sequence.This is why memory safety bugs often cluster around cleanup logic. Cleanup is where abstractions get stressed: partially built messages, pending references, interrupted waits, and shutdown transitions all collide. A bug in the steady-state path might be easy to reason about, but a bug in the release path can hide behind ordinary usage for a long time. Destructor bugs are nasty because they often lie dormant until someone closes the socket at exactly the wrong moment.
A useful way to think about this CVE is to compare it with other kernel lifetime fixes: if the object can still be observed by any valid path, then freeing it early is unsafe even if the “main” operation seems complete. That is why the patch moves the free later instead of trying to make the release path smarter in place. When the root problem is ownership ambiguity, the correct answer is to simplify ownership, not to add more branching.
What This Means for Administrators
For most users, the actionable advice is straightforward: don’t panic, but do inventory. If your environment does not use CAN ISO-TP, this CVE is likely low practical risk. If you maintain embedded Linux systems, vehicle diagnostic infrastructure, industrial gateways, or any host withCAN_ISOTP enabled, you should verify whether your vendor kernel has picked up the upstream fix. The Linux kernel’s own CVE guidance is clear that applicability depends on the use case, not just the presence of the CVE identifier.A sensible triage sequence
- Confirm whether the affected systems actually use CAN ISO-TP.
- Check whether your vendor has backported the fix into your kernel build.
- Review whether socket close paths are exposed to signal interruptions in your workload.
- Prioritize patches on embedded and industrial systems first.
- Validate behavior under normal open/send/close cycles after updating.
- Avoid assuming a version number alone tells you the whole story.
There is also a subtle lesson for security teams that track mixed estates. Linux kernel CVEs increasingly appear alongside Windows and Microsoft-tracked vulnerabilities in the same enterprise dashboards, even when the underlying systems are very different. That can be useful because it normalizes patch triage across platforms, but it can also blur the difference between “globally urgent” and “relevant to a small deployment segment.” Good teams will use the CVE record as a signal, not as a substitute for environment knowledge.
The Value of a Narrow Fix
One reason this CVE is notable is that the fix is elegant. Instead of trying to make every release and send path reason about all possible interleavings, the change moves allocation lifetime to a deeper destruction phase. That’s a pragmatic kernel fix: keep the buffer around until the socket object itself is dead, and let the destructor own the final free. Simplicity at teardown is often the best security outcome.Why this kind of fix ages well
A patch that reduces the number of places where memory can be freed is usually a good patch. It lowers the chance that a future refactor will free the object too early, and it makes the code easier to audit. This matters in long-lived protocol stacks because they tend to accumulate layers of compatibility, optional flags, and edg over time. Moving the free tosk_destruct creates a more obvious ownership boundary for future maintainers.This also reflects a broader truth about Linux security work in 2026: many of the best fixes are not glamorous. They are structural. They remove ambiguity, shrink race windows, and align cleanup with actual object lifetime. In a code base as large as the kernel, that kind of precision is often more valuable than a clever but brittle workaround.
- Fewer free sites mean fewer lifetime mistakes.
- Destructor-based cleanup is easier to audit.
- Longer-lived buffers reduce race exposure.
- Simpler ownership rules make backports safer.
- Maintenance teams benefit from clearer invariants.
- Future protocol changes are less likely to reopen the same flaw.
Risks and Concerns
The principal risk is that use-after-free bugs are inherently unpredictable. Even when the immediate impact appears limited to a crash or corrupted transmit path, memory safety flaws can sometimes have wider consequences depending on allocator behavior, kernel hardening, and surrounding code. The absence of a published CVSS score does not make the issue benign; it simply means formal scoring has not yet been completed.Where the danger is concentrated
The highest-risk scenarios are likely those where ISO-TP is actively used and where socket shutdown can race with ongoing transmission. Systems that process CAN traffic under load, or that frequently open and close transport sockets, are the most obvious candidatption detail is especially important because it points to a narrow but real timing-sensitive path rather than a passive background condition.Another concern is patch propagation. Kernel fixes often reach end users through vendor backports, and the version number alone may not show whether a given system is protected. That creates an audit problem for administrators who assume they can read a single release number and be done. In practice, security teams should verify the presence of the specific fix, not just the kernel family.
There is also a broader ecosystem risk: CAN stacks frequently exist in devices that are patched slowly, remotely, or not at all. If a vulnerability is published for such a subsystem, the threat window can remain open far longer than it would for consumer software. That makes responsible disclosure and rapid stable-tree backporting especially important in this part of the kernel.
- Timing-sensitive bugs are hard to reproduce and easy to underestimate.
- Embedded systems often patch more slowly than desktops.
- Vendor backports may obscure whether the fix is actually present.
- Signal interruption creates a realistic race window.
- Kernel memory bugs can sometimes escalate beyond a simple crash.
- Low apparent exposure can still matter in high-value embedded environments.
- The lack of a CVSS score should not be interpreted as low severity.
Looking Ahead
The next thing to watch is how quickly downstream vendors confirm backports. The kernel-side description is already specific enough to understand the bug and the shape of the fix, but many administrators will depend on distro and appliance maintainers to land the patch in a form they can deploy. That is especially true for long-term-support kernels, where vendors often carry security fixes without changing the headline version in obvious ways.What to watch next
- Vendor advisories confirming backports into enterprise kernel streams.
- Any further stable commits that touch ISO-TP transmit teardown.
- Whether the NVD record receives a finalized CVSS rating.
- Signs of regression testing around
sendmsgand socket close behavior. - Broader cleanup work in the CAN subsystem that tightens buffer ownership.
For administrators, the takeaway is not fear but discipline. If your systems use CAN ISO-TP, this is a real maintenance item. If they do not, it is still a useful reminder that kernel security is often decided by the smallest details: who owns a buffer, when a wait can be interrupted, and exactly which point in the object lifecycle is truly safe to free memory.
CVE-2026-31474 is not the kind of bug that dominates headlines, but it is exactly the kind of bug that teaches the kernel’s most enduring lesson: in low-level code, lifetime is security. The fix is appropriately restrained, the risk is concentrated but real, and the right response is to patch, verify, and keep an eye on the systems that actually exercise this transport path.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center