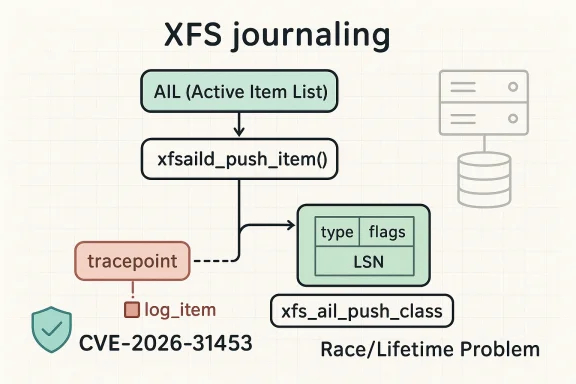
Linux administrators are waking up to a new XFS kernel flaw that looks deceptively small in code but serious in consequence. CVE-2026-31453 affects the Linux kernel’s XFS journaling path, where tracepoint code can dereference a log item after a push callback has already made it eligible for freeing. The fix is elegant but telling: capture the object’s type, flags, and LSN before the callback, then feed those stable values into a new trace event class instead of touching the potentially freed log item afterward. Microsoft has already surfaced the issue in its update guidance, while the kernel community has published the upstream fix and linked it to stable backports.
XFS is one of the Linux kernel’s most mature and performance-oriented filesystems, and its logging subsystem is built around carefully ordered metadata transitions. The filesystem uses the Active Item List (AIL) to track committed metadata that still needs to be pushed to disk, and that mechanism depends on locks, callbacks, and lifecycle rules that are easy to get wrong if code assumes an object remains valid across every phase. The kernel documentation for XFS logging emphasizes that items move through distinct states and that delayed logging and checkpointing intentionally separate commit-time work from later completion work.
That separation is exactly why this flaw matters. When
The upstream fix addresses the problem by changing what the tracepoint consumes. Instead of reading fields from the live log item after the callback, the patch captures the item type, flags, and LSN beforehand and passes those pre-recorded values along with the AIL pointer into a new trace class. That is an important design clue: the bug is not in the push operation itself, but in the assumption that debug and tracing logic can safely inspect an object after the object’s lifetime has become conditional.
For enterprise operators, the practical consequence is less dramatic than a remote code execution bulletin and more serious than a harmless log message bug. XFS is widely deployed in Linux servers, storage appliances, virtualization hosts, and enterprise distributions; a use-after-free in kernel space can mean crashes, data-path instability, or in some circumstances a path toward privilege escalation depending on how the bug is reached and what memory reuse looks like. The public record available so far does not include a NVD vector string, so impact should be treated conservatively until downstream vendors publish their own assessments.
What makes this bug especially subtle is that the trace path is happening after the callback returns, not inside an obvious free routine. That means the bug can remain invisible in normal operation and show up only under churn, reclaim pressure, or highly concurrent metadata workloads. In a filesystem like XFS, which is engineered for scale and concurrency, that sort of bug can sit undetected for a long time before a busy production workload trips it.
This is a good example of instrumentation-aware hardening. Kernel tracing is invaluable for debugging storage problems, but instrumentation itself must never become a source of instability. By redefining the trace interface instead of trying to “carefully” read the old pointer later, the patch removes the entire class of timing assumptions that created the issue.
The fact that this issue arose in the trace path is also instructive. Debug code is often written under the assumption that it is “only observing,” but observing still has to respect ownership and locking. In a filesystem that uses delayed logging and multiple reclaim mechanisms, observation after unlock is sometimes just as risky as mutation after unlock.
The public CVE text does not yet provide a scored severity rating, so downstream risk decisions should be based on exposure and operational criticality rather than on a number from NVD. That may feel unsatisfying, but it is normal in the early days of a newly published kernel CVE. In practice, administrators should assume the issue deserves prompt patching wherever XFS is in production.
Consumer Linux distributions may also backport the fix into maintenance kernels before users ever see the original upstream CVE writeup. That makes the practical question less about who reads the CVE and more about who receives the corrected kernel build. As with many Linux security issues, the distribution’s packaging cadence matters as much as the upstream commit history.
That is reassuring here because the fix is not a behavioral change to XFS write ordering or recovery semantics. It only changes where the trace information comes from. In other words, it is the kind of patch that is more likely to be accepted quickly by maintainers and less likely to introduce regressions, which is exactly what you want from a security update in a mature filesystem stack.
Here, the kernel community appears to have fixed the issue in the safest possible way: eliminate the post-callback dependency altogether. That is usually more durable than trying to add extra checks after the fact, because checks do not help if the memory has already been reclaimed and repurposed. Prevention is cleaner than verification when the object lifetime itself is the problem.
For environments with heavy XFS use, it is also worth correlating crash logs, watchdog resets, and unexpected kernel faults with filesystem activity. Tracepoint-heavy instrumentation or debugging can make race conditions more visible, but it can also increase noise; the useful signal is whether failures cluster around reclaim pressure or metadata churn. Do not wait for a reproducible exploit if the fix is already available.
The longer-term lesson for the kernel community is familiar but important: lifecycle assumptions need to be explicit, especially around callbacks that can drop locks and allow reclamation. In a filesystem like XFS, where performance depends on aggressive concurrency, the safest code is the code that never asks a freed object for one more piece of information. That is why this patch matters beyond the immediate CVE record.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Overview
Overview
XFS is one of the Linux kernel’s most mature and performance-oriented filesystems, and its logging subsystem is built around carefully ordered metadata transitions. The filesystem uses the Active Item List (AIL) to track committed metadata that still needs to be pushed to disk, and that mechanism depends on locks, callbacks, and lifecycle rules that are easy to get wrong if code assumes an object remains valid across every phase. The kernel documentation for XFS logging emphasizes that items move through distinct states and that delayed logging and checkpointing intentionally separate commit-time work from later completion work.That separation is exactly why this flaw matters. When
xfsaild_push_item invokes the item’s iop_push callback, the AIL lock may be dropped, and once that happens the log item can be freed by concurrent inode reclaim or the dquot shrinker. If the code then returns to a tracepoint path and dereferences the original log item pointer, the kernel is using memory that may no longer belong to it. In kernel terms, that is a classic lifetime bug with a narrow race window but broad diagnostic and stability implications.The upstream fix addresses the problem by changing what the tracepoint consumes. Instead of reading fields from the live log item after the callback, the patch captures the item type, flags, and LSN beforehand and passes those pre-recorded values along with the AIL pointer into a new trace class. That is an important design clue: the bug is not in the push operation itself, but in the assumption that debug and tracing logic can safely inspect an object after the object’s lifetime has become conditional.
For enterprise operators, the practical consequence is less dramatic than a remote code execution bulletin and more serious than a harmless log message bug. XFS is widely deployed in Linux servers, storage appliances, virtualization hosts, and enterprise distributions; a use-after-free in kernel space can mean crashes, data-path instability, or in some circumstances a path toward privilege escalation depending on how the bug is reached and what memory reuse looks like. The public record available so far does not include a NVD vector string, so impact should be treated conservatively until downstream vendors publish their own assessments.
How the Bug Emerged
The failure mode is a race between metadata lifecycle management and diagnostic instrumentation. XFS usesiop_push to advance log items through AIL processing, but the callback can temporarily release the AIL lock. During that unlocked interval, other kernel code paths such as inode reclaim or the dquot shrinker can free the item. When control returns, the code’s tracepoint switch statement still expects to inspect the log item pointer, even though that pointer may already be invalid.Why tracepoints matter here
Tracepoints are usually designed to be low-friction instrumentation, not a source of new risk. But in a kernel filesystem, even diagnostic paths must obey the same lifetime rules as production code, because they often run in the same critical sections and under the same concurrency pressure. The kernel’s tracing documentation makes clear that tracepoints are intended to capture system behavior precisely; they are not supposed to become a hidden dependency on unstable memory.What makes this bug especially subtle is that the trace path is happening after the callback returns, not inside an obvious free routine. That means the bug can remain invisible in normal operation and show up only under churn, reclaim pressure, or highly concurrent metadata workloads. In a filesystem like XFS, which is engineered for scale and concurrency, that sort of bug can sit undetected for a long time before a busy production workload trips it.
- The dangerous window opens when the AIL lock is dropped.
- The item can be freed by reclaim or shrinker activity.
- The tracepoint still dereferences the original pointer.
- The result is a possible use-after-free in kernel space.
What Changed in the Fix
The upstream fix does three things at once. First, it records the log item’s type, flags, and LSN before invokingxfsaild_push_item. Second, it introduces a dedicated xfs_ail_push_class trace event class. Third, it switches the trace call site from passing a live log item pointer to passing the AIL pointer plus the captured metadata values. The kernel’s public references show the fix was backported into stable branches, which is usually a strong signal that maintainers viewed the bug as worth correcting across supported trees.Why the new trace class is important
A new trace event class is not just refactoring. It is a way to preserve diagnostic fidelity while severing the dependency on a potentially freed object. The trace still tells developers what happened, but it does so using data copied at a safe point in time. That gives maintainers the visibility they need without violating memory ownership rules.This is a good example of instrumentation-aware hardening. Kernel tracing is invaluable for debugging storage problems, but instrumentation itself must never become a source of instability. By redefining the trace interface instead of trying to “carefully” read the old pointer later, the patch removes the entire class of timing assumptions that created the issue.
- Capture values before the callback.
- Avoid post-callback dereferencing.
- Keep traceability intact.
- Preserve the AIL pointer for context.
- Remove lifetime coupling from debugging code.
Why XFS Is Exposed to These Kinds of Races
XFS is a high-throughput filesystem built around concurrency, delayed logging, and asynchronous completion. Its design intentionally decouples metadata changes from disk writeout, which is great for performance but also means there are many more state transitions in flight at once. The XFS design documentation explains that log items move through commit, checkpoint, and AIL traversal phases, and that items can be independently reclaimed or cleaned as those phases progress.The role of reclaim and shrinkers
Inode reclaim and dquot shrinking are both memory-management paths that can reclaim filesystem metadata structures when conditions allow. That is perfectly normal behavior, but it becomes hazardous when unrelated code assumes a metadata object will remain intact just because a tracing path still wants to read it. The vulnerability shows how kernel subsystems that are individually correct can still interact in unsafe ways when lifetime assumptions are too optimistic.The fact that this issue arose in the trace path is also instructive. Debug code is often written under the assumption that it is “only observing,” but observing still has to respect ownership and locking. In a filesystem that uses delayed logging and multiple reclaim mechanisms, observation after unlock is sometimes just as risky as mutation after unlock.
- XFS uses asynchronous logging for performance.
- AIL traversal is concurrent with other kernel work.
- Reclaim paths can free metadata objects independently.
- Tracepoints must not outlive the objects they inspect.
- Small race windows can still produce kernel crashes.
Enterprise Impact
For enterprises, the immediate concern is not just whether an attacker can weaponize the bug, but whether the bug can destabilize busy servers under load. Filesystem crashes or kernel faults on storage-heavy hosts can interrupt databases, virtual machines, backup jobs, and container platforms even if no adversary is present. That makes this the kind of flaw that security teams and platform teams both need to track.Workload sensitivity
The most relevant environments are the ones that keep XFS under constant metadata churn. Those include virtualization clusters, file servers, large build farms, and database deployments that rely on XFS for journaling behavior and predictable write ordering. Microsoft’s own SQL Server on Linux guidance continues to list XFS as a supported and recommended filesystem in several Linux deployment scenarios, which underscores how widely XFS persists in enterprise environments.The public CVE text does not yet provide a scored severity rating, so downstream risk decisions should be based on exposure and operational criticality rather than on a number from NVD. That may feel unsatisfying, but it is normal in the early days of a newly published kernel CVE. In practice, administrators should assume the issue deserves prompt patching wherever XFS is in production.
- Production Linux servers may experience instability.
- Busy metadata workloads increase the likelihood of triggering the race.
- Hosted infrastructure can multiply the impact of a single crash.
- Backup and storage appliances may be affected indirectly.
- Patch urgency should follow workload criticality.
Consumer and Desktop Impact
Home users are less likely than enterprise operators to notice the bug, but they are not fully insulated from it. Any Linux system using XFS can encounter the affected code paths, especially if the machine runs heavier local workloads, development tools, virtual machines, or storage-intensive sync jobs. The difference is that consumer systems usually have less continuous metadata pressure, so the race may be harder to trigger in day-to-day use.What “low visibility” does not mean
It is tempting to assume that a bug hidden inside tracepoints is harmless for ordinary users. That would be a mistake. Kernel bugs often stay dormant until the right combination of reclaim, logging, and scheduling occurs, and when they do surface, the symptom is often a sudden crash or lockup rather than a graceful error message. Low visibility is not the same thing as low risk.Consumer Linux distributions may also backport the fix into maintenance kernels before users ever see the original upstream CVE writeup. That makes the practical question less about who reads the CVE and more about who receives the corrected kernel build. As with many Linux security issues, the distribution’s packaging cadence matters as much as the upstream commit history.
- Desktops can still be affected if they use XFS.
- Local crashes are more likely than remote exploitation.
- Heavy compile, VM, or backup activity raises exposure.
- Kernel updates matter even for “non-server” Linux installs.
- Distribution backports may arrive before formal scoring does.
The Role of Upstream and Stable Backports
Kernel security work rarely ends with a single commit. The Linux kernel’s CVE process encourages fixes to be tracked by the original commit IDs and then carried into stable trees, which is why the public references associated with this CVE matter as much as the description itself. The stable links attached to the record indicate that maintainers considered the issue suitable for backporting across supported branches.Why stable backports matter
Backports are where security work becomes operational reality. Most users never build mainline kernels from scratch, so the relevant question is whether their distro kernel picks up the fix quickly and cleanly. A stable backport also signals that the patch was judged small and self-contained enough to be safe for older maintained code.That is reassuring here because the fix is not a behavioral change to XFS write ordering or recovery semantics. It only changes where the trace information comes from. In other words, it is the kind of patch that is more likely to be accepted quickly by maintainers and less likely to introduce regressions, which is exactly what you want from a security update in a mature filesystem stack.
- Stable backports reduce exposure window.
- Small patches are usually safer to ship quickly.
- Trace-only changes lower regression risk.
- Kernel vendors can integrate them with less churn.
- Users benefit when the fix lands before exploitation discussions do.
Security Significance
This CVE is a reminder that not all kernel vulnerabilities are dramatic in appearance. Some are the product of a single unsafe dereference in code that exists mainly to help developers observe the system, yet those bugs still sit inside the trusted kernel boundary. In a filesystem path, that means they can affect both reliability and security posture in production.Use-after-free remains a major class of kernel bug
Use-after-free issues keep appearing in kernel CVE streams because they emerge whenever object lifetimes become difficult to reason about across callbacks, locks, and asynchronous work. Once freed memory can be reused, the consequences range from null-pointer-style crashes to more dangerous memory corruption, depending on what lands in the freed slot. The exact outcome is often workload-dependent, which is why early descriptions frequently avoid firm exploitability claims.Here, the kernel community appears to have fixed the issue in the safest possible way: eliminate the post-callback dependency altogether. That is usually more durable than trying to add extra checks after the fact, because checks do not help if the memory has already been reclaimed and repurposed. Prevention is cleaner than verification when the object lifetime itself is the problem.
- The bug class is memory safety, not a policy misconfiguration.
- Trace code can be just as dangerous as fast-path code.
- Race conditions are often hard to reproduce but easy to abuse once understood.
- The safest fix is to stop touching the object after the unsafe point.
- Kernel boundary bugs deserve prompt remediation.
Operational Guidance
Administrators should treat the fix as a normal kernel maintenance priority rather than a niche filesystem optimization. The exact package path will depend on the distribution, but the important operational question is whether the installed kernel includes the upstream stable patch or a vendor backport of the same change. If you run mixed fleets, that distinction matters more than the CVE label alone.Practical response steps
A good response plan is straightforward and should be familiar to any Linux operations team. First, identify systems using XFS for important workloads. Second, check the vendor’s kernel advisory stream or package changelog for the backported fix. Third, schedule reboots or rolling maintenance according to the organization’s tolerance for interruption.For environments with heavy XFS use, it is also worth correlating crash logs, watchdog resets, and unexpected kernel faults with filesystem activity. Tracepoint-heavy instrumentation or debugging can make race conditions more visible, but it can also increase noise; the useful signal is whether failures cluster around reclaim pressure or metadata churn. Do not wait for a reproducible exploit if the fix is already available.
- Inventory hosts that use XFS.
- Check the vendor kernel build for the stable backport.
- Prioritize production servers and shared infrastructure.
- Test the update in a controlled maintenance window.
- Roll out the patched kernel broadly once validated.
- Verify whether your distro has already backported the fix.
- Watch for crash signatures tied to filesystem activity.
- Keep logs from affected systems before rebooting.
- Include storage and virtualization teams in the rollout.
- Treat kernel updates as part of normal risk management.
Strengths and Opportunities
This incident also shows some of the strengths of the Linux kernel ecosystem. The upstream fix is small, targeted, and easy to reason about, and the stable-tree machinery makes it possible to distribute the correction quickly once maintainers agree on the patch. Just as importantly, the XFS documentation and trace infrastructure make it possible to understand why the fix was needed, not just that it exists.- Small, surgical fix reduces regression risk.
- Stable backporting speeds real-world protection.
- Trace abstraction preserves debugging value.
- Clear lifetime model improves maintainability.
- Enterprise awareness is already high because XFS is common in servers.
- Patch reviewability is strong thanks to narrow scope.
- Diagnostic quality improves when tracepoints avoid unsafe dereferences.
Risks and Concerns
The main risk is that a bug that looks like “just a tracepoint problem” can still destabilize a whole system if it is reached inside the kernel. Another concern is that visibility into the exact severity remains limited while NVD enrichment and vendor scoring catch up. That means organizations have to make decisions in the gray area, which is never ideal when a core filesystem is involved.- Race conditions are notoriously hard to reproduce in the lab.
- Kernel crashes can take down unrelated services.
- Incomplete scoring can delay prioritization.
- Mixed fleet packaging makes patch tracking harder.
- Backport divergence can create false confidence.
- Operational overload may cause admins to postpone reboots.
- Hidden exposure exists where XFS is deployed but not prominently tracked.
Looking Ahead
The next milestones will likely be distribution advisories, backport confirmations, and any eventual NVD scoring that clarifies severity for downstream consumers. For admins, the key question is not whether the bug is “interesting” but whether the running kernel has already incorporated the fix. In most environments, that answer should be checked at the package level, not inferred from version strings alone.The longer-term lesson for the kernel community is familiar but important: lifecycle assumptions need to be explicit, especially around callbacks that can drop locks and allow reclamation. In a filesystem like XFS, where performance depends on aggressive concurrency, the safest code is the code that never asks a freed object for one more piece of information. That is why this patch matters beyond the immediate CVE record.
- Track vendor kernel advisories for the stable backport.
- Confirm whether XFS hosts rebooted into patched kernels.
- Watch for any follow-up fixes in XFS tracing code.
- Review monitoring around reclaim-heavy workloads.
- Treat future tracepoint changes with the same lifetime scrutiny.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center