CVE-2026-43153 is a newly published Linux kernel vulnerability, disclosed on May 6, 2026, in the XFS filesystem code, where a confusing helper function called
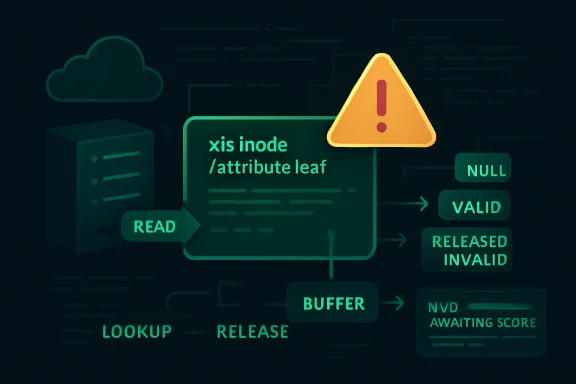
The vulnerability description for CVE-2026-43153 is unusually candid because it inherits the language of the upstream kernel fix. The problem sits in XFS extended-attribute handling, specifically around a helper whose calling convention had become too clever for its own good. Depending on which lower-level operation failed, the function could return no buffer, a valid buffer, or a non-NULL pointer to a buffer that had already been released.
That last case is the one that makes kernel developers wince. In C, an invalid pointer that still looks non-NULL is an invitation to misuse. It can turn a simple error path into a use-after-free-style hazard, a crash, or worse, depending on the surrounding call chain and whether an attacker can shape the inputs that reach it.
The upstream fix is not described as a grand redesign. It removes the helper and open-codes the relevant logic in the callers, so that each caller that reads an XFS attribute leaf is also responsible for releasing the buffer in a straightforward way. In other words, the patch is less about adding a new defense than deleting an abstraction that blurred ownership.
That is the first lesson in this CVE: a security bug does not always announce itself with a dramatic primitive. Sometimes the dangerous object is a convenience function whose return values encode too many states. If the cleanup path requires a mental truth table, the bug is already halfway written.
That matters because filesystem vulnerabilities have a strange blast radius. They are local in one sense: a bug in XFS is not automatically a remote network exploit. But they sit beneath almost everything else, and they often parse structures that can be influenced by users, containers, removable media, virtual disk images, backup restores, or corrupted storage.
Extended attributes add another layer of subtlety. They are not the file contents users think about; they are metadata attached to files and directories, used for security labels, capabilities, access-control systems, namespaces, and application-specific state. On modern Unix-like systems, extended attributes are part of the quiet machinery that lets policy travel with files.
That quietness is exactly why bugs here matter. A path that checks whether an attribute exists may seem far away from the high-drama world of exploit chains, but in kernel code the ordinary paths are the hot paths. They run with privilege, they manipulate shared state, and they are expected to get ownership and lifetime rules right every time.
When the leaf read failed, it returned a NULL buffer. When lookup reported ordinary states such as “attribute not found” or “attribute already exists,” it returned a valid buffer. When lookup failed with other errors, it could return a non-NULL pointer to a buffer that had already been released.
This is the kind of API contract that works until it doesn’t. It asks every caller to understand not just success and failure, but the provenance of failure. It is the kernel equivalent of a door that is sometimes locked, sometimes open, and sometimes missing while the handle remains in your hand.
The fix is therefore instructive. By removing the helper, the patch forces the code to keep read, lookup, and release logic in the same local scope. That sounds less elegant, but kernel filesystems are not graded on elegance; they are graded on not corrupting memory when a rare error path finally runs under pressure.
There is a broader software-engineering point here. Abstractions are supposed to hide complexity, not hide responsibility. When an abstraction makes resource ownership ambiguous, deleting it can be a security improvement.
A missing score is not a low score. It is an administrative state. NVD enrichment often lags the upstream disclosure, especially for Linux kernel CVEs where the initial record is generated from a kernel.org advisory stream and the operational impact still needs interpretation.
For defenders, the sequencing matters. The CVE was published with upstream references and a technical description before the neat vulnerability-management furniture arrived. That means patch teams have to reason from the code path, affected kernel streams, vendor backports, and local exposure rather than waiting for a single normalized severity value.
This is especially true for kernel issues because vendor kernels rarely map cleanly to upstream version numbers. A Red Hat, Ubuntu, Debian, SUSE, Amazon Linux, Oracle Linux, or Microsoft-maintained kernel may include backports without changing to the upstream version where a fix first appeared. The question is not merely “what kernel version am I running?” but “has my vendor carried this specific XFS fix into my kernel build?”
A Linux filesystem bug is therefore not outside the WindowsForum orbit. It is part of the same hybrid estate that Windows administrators now manage every day. The modern Microsoft admin is often also a Linux kernel consumer, whether through containers on Windows, Linux VMs in Azure, storage appliances, security tools, build agents, or developer environments.
This is one reason CVE-2026-43153 is worth attention even if your desktop fleet is Windows. The boundary between “Windows security” and “Linux security” has collapsed in enterprise operations. Identity, storage, CI/CD, virtualization, and cloud orchestration do not respect old platform silos.
Microsoft’s listing also reinforces a practical truth: vulnerability intelligence is now federated. A kernel.org record becomes an NVD placeholder, appears in vendor advisories, and then gets absorbed into enterprise dashboards that may not explain the underlying bug. The administrator sees a CVE; the meaningful work is figuring out whether it lands on any system that can actually exercise the vulnerable code.
This distinction matters because kernel CVEs are often flattened into the same alerting tone. A bug that can be triggered by an unprivileged local user on a default filesystem is very different from one that requires mounting a crafted disk image, having administrative privileges, or enabling a niche configuration. The description for CVE-2026-43153 does not yet provide that operational contour.
The risky cases to consider are predictable. Systems using XFS are the relevant population. Workloads that allow untrusted users to create, modify, or manipulate extended attributes deserve closer attention. Environments that process untrusted filesystem images, backup media, container layers, or tenant-controlled storage artifacts should be more cautious than single-user machines with tightly controlled local access.
But caution is not the same as panic. Until vendor advisories and kernel maintainers clarify affected versions and exploitability, this is best handled as a kernel storage-stack fix that should move through normal security update channels promptly, not as evidence of an Internet-wide emergency.
Administrators often want a single answer: fixed or not fixed. The Linux ecosystem tends to answer with a matrix. Mainline has one commit, stable branches have others, distribution kernels may have backports, and enterprise vendors may keep the same major kernel version while quietly applying thousands of fixes underneath.
That is why raw version comparison can mislead. A system running an older-looking enterprise kernel may be fixed because the vendor backported the patch. A system running a newer custom kernel may remain vulnerable because it missed the stable branch update. Security tooling that relies too heavily on upstream version strings can generate both false reassurance and false alarms.
The practical response is to trust vendor-specific package metadata over vanity version checks. On managed distributions, look for the vendor’s kernel advisory or changelog entry for CVE-2026-43153. On custom kernels, check whether the relevant XFS patch removing
Many organizations do not have that inventory at useful resolution. They know the operating system family and maybe the kernel package. They do not always know which hosts use XFS for root, which use it only for data volumes, which ingest disk images, and which expose local filesystem operations indirectly through applications.
This is where vulnerability management becomes systems administration again. A scanner can tell you that a CVE exists. It may not tell you that the affected code path is most relevant on your storage nodes, CI runners, container hosts, or backup restore servers. It certainly will not know which internal team treats extended attributes as part of an application workflow.
The organizations that handle this well will not be the ones with the loudest dashboards. They will be the ones that can answer boring questions quickly: where is XFS mounted, which kernels are vendor-supported, what update ring do those systems belong to, and what downtime window is needed if a reboot is required?
CVE-2026-43153 fits that pattern. It is technically specific, terse, and not yet enriched with the fields that enterprise tooling likes. It tells kernel developers exactly what went wrong, while leaving security teams to translate that into exposure, priority, and maintenance planning.
The upside is speed. The world learns about the fix early, and downstream vendors can map it into their kernels. The downside is interpretive burden. Every kernel bug with a CVE cannot be treated as a five-alarm incident, but every kernel memory-lifetime bug also deserves more respect than “NVD says N/A.”
This is the new middle ground: patch deliberately, investigate locally, and resist both extremes. The wrong response is to ignore it because there is no score. The other wrong response is to claim a catastrophic exploit chain that has not been demonstrated.
Developer laptops may use WSL for build tooling. Azure estates may run Linux VMs alongside Windows Server. Kubernetes clusters may host Windows and Linux nodes under the same operational umbrella. Security appliances, monitoring systems, backup platforms, and network services may all embed Linux kernels even when the business thinks of them as vendor products.
That mixed estate changes how a CVE like this should be read. It is not a patch-Tuesday-style Windows emergency. It is a test of whether your organization can follow a low-level Linux kernel issue across cloud, containers, appliances, and distribution-specific support channels.
There is also a cultural point. Windows administrators are used to centralized bulletins and comparatively coherent servicing models. Linux kernel maintenance is more distributed. If your operational model assumes every important vulnerability arrives in one familiar console with a severity score and a reboot flag, Linux will continue to surprise you.
Start with scope. Identify systems using XFS, especially servers and appliances where untrusted users or workloads can influence file metadata. Then map those systems to vendor kernel packages and update streams. If you run distribution kernels, wait for and apply the vendor’s kernel security update rather than trying to cherry-pick upstream commits into production.
Custom kernel users have more work. They need to confirm that the fix removing
Finally, plan for reboots. Kernel fixes do not become operationally real until the fixed kernel is running. Live patching may help in some environments, but filesystem code and distribution support policies vary. A patched package sitting on disk under a still-running vulnerable kernel is a compliance artifact, not a fix.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
xfs_attr_leaf_hasname() could hand callers an invalid buffer pointer after certain extended-attribute lookup failures. That is the dry version, and it sounds like the sort of kernel plumbing only filesystem maintainers should care about. The more useful reading is that yet another CVE has been assigned to a correctness fix deep in Linux’s storage stack, before NVD has scored it, before vendors have fully explained exposure, and before administrators have a neat severity badge to sort by. This is where modern vulnerability management now lives: in the uncomfortable gap between a real kernel bug and the operational story that tells you whether it matters.
 The Bug Is Small, but the Pattern Is Not
The Bug Is Small, but the Pattern Is Not
The vulnerability description for CVE-2026-43153 is unusually candid because it inherits the language of the upstream kernel fix. The problem sits in XFS extended-attribute handling, specifically around a helper whose calling convention had become too clever for its own good. Depending on which lower-level operation failed, the function could return no buffer, a valid buffer, or a non-NULL pointer to a buffer that had already been released.That last case is the one that makes kernel developers wince. In C, an invalid pointer that still looks non-NULL is an invitation to misuse. It can turn a simple error path into a use-after-free-style hazard, a crash, or worse, depending on the surrounding call chain and whether an attacker can shape the inputs that reach it.
The upstream fix is not described as a grand redesign. It removes the helper and open-codes the relevant logic in the callers, so that each caller that reads an XFS attribute leaf is also responsible for releasing the buffer in a straightforward way. In other words, the patch is less about adding a new defense than deleting an abstraction that blurred ownership.
That is the first lesson in this CVE: a security bug does not always announce itself with a dramatic primitive. Sometimes the dangerous object is a convenience function whose return values encode too many states. If the cleanup path requires a mental truth table, the bug is already halfway written.
XFS Is Where Boring Infrastructure Becomes Security-Relevant
XFS is not exotic. It is a mature, high-performance filesystem used in serious Linux deployments, especially where large files, parallel I/O, and long-lived storage matter. Enterprise Linux administrators know it less as a novelty than as part of the landscape: the thing under databases, object stores, backup targets, hypervisor hosts, and occasionally developer workstations that have outgrown default assumptions.That matters because filesystem vulnerabilities have a strange blast radius. They are local in one sense: a bug in XFS is not automatically a remote network exploit. But they sit beneath almost everything else, and they often parse structures that can be influenced by users, containers, removable media, virtual disk images, backup restores, or corrupted storage.
Extended attributes add another layer of subtlety. They are not the file contents users think about; they are metadata attached to files and directories, used for security labels, capabilities, access-control systems, namespaces, and application-specific state. On modern Unix-like systems, extended attributes are part of the quiet machinery that lets policy travel with files.
That quietness is exactly why bugs here matter. A path that checks whether an attribute exists may seem far away from the high-drama world of exploit chains, but in kernel code the ordinary paths are the hot paths. They run with privilege, they manipulate shared state, and they are expected to get ownership and lifetime rules right every time.
The Real Smell Is a Return Value That Means Three Things
The CVE description gives us enough to reconstruct the core engineering failure.xfs_attr_leaf_hasname() was meant to answer a simple question: does this XFS attribute leaf contain the requested name? But its behavior depended on two different underlying operations, xfs_attr3_leaf_read() and xfs_attr3_leaf_lookup_int(), and the helper mixed lookup results with buffer lifetime management.When the leaf read failed, it returned a NULL buffer. When lookup reported ordinary states such as “attribute not found” or “attribute already exists,” it returned a valid buffer. When lookup failed with other errors, it could return a non-NULL pointer to a buffer that had already been released.
This is the kind of API contract that works until it doesn’t. It asks every caller to understand not just success and failure, but the provenance of failure. It is the kernel equivalent of a door that is sometimes locked, sometimes open, and sometimes missing while the handle remains in your hand.
The fix is therefore instructive. By removing the helper, the patch forces the code to keep read, lookup, and release logic in the same local scope. That sounds less elegant, but kernel filesystems are not graded on elegance; they are graded on not corrupting memory when a rare error path finally runs under pressure.
There is a broader software-engineering point here. Abstractions are supposed to hide complexity, not hide responsibility. When an abstraction makes resource ownership ambiguous, deleting it can be a security improvement.
NVD’s Empty Scorecard Is Not a Risk Assessment
As of publication, the NVD entry is marked as awaiting enrichment and does not provide CVSS 4.0, CVSS 3.x, or CVSS 2.0 scoring. That absence will tempt some organizations to treat the issue as informational until a number appears. It should not.A missing score is not a low score. It is an administrative state. NVD enrichment often lags the upstream disclosure, especially for Linux kernel CVEs where the initial record is generated from a kernel.org advisory stream and the operational impact still needs interpretation.
For defenders, the sequencing matters. The CVE was published with upstream references and a technical description before the neat vulnerability-management furniture arrived. That means patch teams have to reason from the code path, affected kernel streams, vendor backports, and local exposure rather than waiting for a single normalized severity value.
This is especially true for kernel issues because vendor kernels rarely map cleanly to upstream version numbers. A Red Hat, Ubuntu, Debian, SUSE, Amazon Linux, Oracle Linux, or Microsoft-maintained kernel may include backports without changing to the upstream version where a fix first appeared. The question is not merely “what kernel version am I running?” but “has my vendor carried this specific XFS fix into my kernel build?”
Microsoft’s Presence Is the Cloud Story Hiding in Plain Sight
The source surfaced through Microsoft’s Security Update Guide, which may surprise readers who still think of Linux kernel CVEs as someone else’s problem in Redmond. That view is obsolete. Microsoft ships, hosts, maintains, and secures Linux across Azure, WSL, Azure Kubernetes Service, Azure Linux, appliance-like services, and countless customer workloads running on Microsoft infrastructure.A Linux filesystem bug is therefore not outside the WindowsForum orbit. It is part of the same hybrid estate that Windows administrators now manage every day. The modern Microsoft admin is often also a Linux kernel consumer, whether through containers on Windows, Linux VMs in Azure, storage appliances, security tools, build agents, or developer environments.
This is one reason CVE-2026-43153 is worth attention even if your desktop fleet is Windows. The boundary between “Windows security” and “Linux security” has collapsed in enterprise operations. Identity, storage, CI/CD, virtualization, and cloud orchestration do not respect old platform silos.
Microsoft’s listing also reinforces a practical truth: vulnerability intelligence is now federated. A kernel.org record becomes an NVD placeholder, appears in vendor advisories, and then gets absorbed into enterprise dashboards that may not explain the underlying bug. The administrator sees a CVE; the meaningful work is figuring out whether it lands on any system that can actually exercise the vulnerable code.
The Exploitability Story Is Still Unwritten
The CVE language does not, by itself, prove remote code execution, privilege escalation, data theft, or reliable exploitation. It identifies a resolved kernel bug involving an invalid buffer pointer in XFS attribute handling. That is serious enough to patch, but not enough to responsibly claim a specific attack outcome without more analysis.This distinction matters because kernel CVEs are often flattened into the same alerting tone. A bug that can be triggered by an unprivileged local user on a default filesystem is very different from one that requires mounting a crafted disk image, having administrative privileges, or enabling a niche configuration. The description for CVE-2026-43153 does not yet provide that operational contour.
The risky cases to consider are predictable. Systems using XFS are the relevant population. Workloads that allow untrusted users to create, modify, or manipulate extended attributes deserve closer attention. Environments that process untrusted filesystem images, backup media, container layers, or tenant-controlled storage artifacts should be more cautious than single-user machines with tightly controlled local access.
But caution is not the same as panic. Until vendor advisories and kernel maintainers clarify affected versions and exploitability, this is best handled as a kernel storage-stack fix that should move through normal security update channels promptly, not as evidence of an Internet-wide emergency.
Stable Trees Turn One Patch Into Many Decisions
The references attached to the CVE point to multiple stable kernel commits, which is typical for Linux kernel fixes. A change lands upstream and then has to be carried into stable and long-term-support trees that differ enough to need separate commits. That multiplicity is healthy, but it complicates tracking.Administrators often want a single answer: fixed or not fixed. The Linux ecosystem tends to answer with a matrix. Mainline has one commit, stable branches have others, distribution kernels may have backports, and enterprise vendors may keep the same major kernel version while quietly applying thousands of fixes underneath.
That is why raw version comparison can mislead. A system running an older-looking enterprise kernel may be fixed because the vendor backported the patch. A system running a newer custom kernel may remain vulnerable because it missed the stable branch update. Security tooling that relies too heavily on upstream version strings can generate both false reassurance and false alarms.
The practical response is to trust vendor-specific package metadata over vanity version checks. On managed distributions, look for the vendor’s kernel advisory or changelog entry for CVE-2026-43153. On custom kernels, check whether the relevant XFS patch removing
xfs_attr_leaf_hasname() has been applied to the exact source tree you build from.Filesystem Bugs Punish Sloppy Asset Inventories
CVE-2026-43153 is also a reminder that “Linux server” is too vague an asset category. The important question is whether a machine uses XFS in a way that can reach the vulnerable code. That requires knowing filesystem types, mount points, workload roles, and who or what can write metadata.Many organizations do not have that inventory at useful resolution. They know the operating system family and maybe the kernel package. They do not always know which hosts use XFS for root, which use it only for data volumes, which ingest disk images, and which expose local filesystem operations indirectly through applications.
This is where vulnerability management becomes systems administration again. A scanner can tell you that a CVE exists. It may not tell you that the affected code path is most relevant on your storage nodes, CI runners, container hosts, or backup restore servers. It certainly will not know which internal team treats extended attributes as part of an application workflow.
The organizations that handle this well will not be the ones with the loudest dashboards. They will be the ones that can answer boring questions quickly: where is XFS mounted, which kernels are vendor-supported, what update ring do those systems belong to, and what downtime window is needed if a reboot is required?
The Kernel CVE Firehose Has Changed the Administrator’s Job
Linux kernel CVEs have become more formalized and more numerous, in part because the kernel project has moved toward assigning CVEs to many bug fixes that have plausible security impact. That makes sense from a transparency perspective. It also means defenders are increasingly handed records whose first public form looks like a commit message, not a polished advisory.CVE-2026-43153 fits that pattern. It is technically specific, terse, and not yet enriched with the fields that enterprise tooling likes. It tells kernel developers exactly what went wrong, while leaving security teams to translate that into exposure, priority, and maintenance planning.
The upside is speed. The world learns about the fix early, and downstream vendors can map it into their kernels. The downside is interpretive burden. Every kernel bug with a CVE cannot be treated as a five-alarm incident, but every kernel memory-lifetime bug also deserves more respect than “NVD says N/A.”
This is the new middle ground: patch deliberately, investigate locally, and resist both extremes. The wrong response is to ignore it because there is no score. The other wrong response is to claim a catastrophic exploit chain that has not been demonstrated.
Windows Administrators Should Care Because Their Linux Footprint Is Real
For WindowsForum readers, the obvious objection is that XFS is not NTFS and this is not a Windows kernel bug. True, but increasingly incomplete. Windows shops now run Linux in places that matter, often without thinking of those machines as part of the same endpoint story.Developer laptops may use WSL for build tooling. Azure estates may run Linux VMs alongside Windows Server. Kubernetes clusters may host Windows and Linux nodes under the same operational umbrella. Security appliances, monitoring systems, backup platforms, and network services may all embed Linux kernels even when the business thinks of them as vendor products.
That mixed estate changes how a CVE like this should be read. It is not a patch-Tuesday-style Windows emergency. It is a test of whether your organization can follow a low-level Linux kernel issue across cloud, containers, appliances, and distribution-specific support channels.
There is also a cultural point. Windows administrators are used to centralized bulletins and comparatively coherent servicing models. Linux kernel maintenance is more distributed. If your operational model assumes every important vulnerability arrives in one familiar console with a severity score and a reboot flag, Linux will continue to surprise you.
The Sensible Response Is Boring, Which Is Usually Correct
There is no evidence in the supplied record that CVE-2026-43153 is being exploited in the wild. There is no NVD severity yet. There is no public claim in the record of remote exploitation. The correct response is therefore not theatrical; it is methodical.Start with scope. Identify systems using XFS, especially servers and appliances where untrusted users or workloads can influence file metadata. Then map those systems to vendor kernel packages and update streams. If you run distribution kernels, wait for and apply the vendor’s kernel security update rather than trying to cherry-pick upstream commits into production.
Custom kernel users have more work. They need to confirm that the fix removing
xfs_attr_leaf_hasname() is present in their tree or that their branch is not affected. They also need to think about how quickly they can test and deploy a kernel update, because storage-stack changes deserve real validation before being rolled across production fleets.Finally, plan for reboots. Kernel fixes do not become operationally real until the fixed kernel is running. Live patching may help in some environments, but filesystem code and distribution support policies vary. A patched package sitting on disk under a still-running vulnerable kernel is a compliance artifact, not a fix.
The Five Checks That Separate Action From Alarm
CVE-2026-43153 is not a headline-grabbing named vulnerability, at least not yet, and that is precisely why it is useful as a discipline test. The teams that handle it well will turn a sparse upstream record into a small number of concrete operational checks.- Confirm which Linux systems in your estate use XFS, including data volumes, cloud images, backup targets, and container hosts.
- Check your distribution or vendor kernel advisories for CVE-2026-43153 rather than relying only on upstream version numbers.
- Treat the lack of an NVD CVSS score as an absence of enrichment, not as evidence that the vulnerability is harmless.
- Prioritize systems where untrusted users, tenants, jobs, or imported filesystem images can influence extended attributes or XFS metadata.
- Make sure the fixed kernel is actually booted after patching, because installing a kernel update without restarting leaves the old code in memory.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center