 XFS use-after-free CVE-2026-31454 exposes a familiar kernel trap in a very specific corner of Linux metadata management
XFS use-after-free CVE-2026-31454 exposes a familiar kernel trap in a very specific corner of Linux metadata management
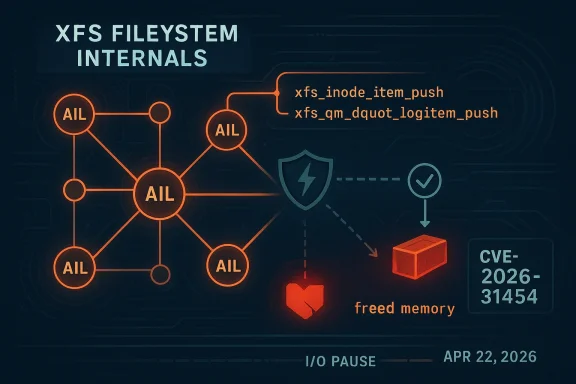
A newly published Linux kernel vulnerability, tracked as CVE-2026-31454, affects XFS and stems from a classic concurrency mistake: a pointer is dereferenced after the code has dropped the lock that made it safe. In practical terms, the bug sits in the path used by XFS push callbacks when the filesystem is trying to flush metadata out of the Active Item List (AIL), and the problem is dangerous because the item can disappear while the callback is doing I/O. The fix is straightforward in concept but important in consequence: save the AIL pointer before dropping the lock, so the callback does not later reach back through a freed log item. Microsoft has already surfaced the issue in its Security Update Guide, and the CVE record was published on April 22, 2026.Background
XFS has always been a filesystem built around speed, scale, and careful write ordering. Its logging model is designed to preserve metadata integrity under heavy concurrency, which means there are multiple layers of state tracking between an inode or dquot being modified and that change finally making it to disk. The AIL is one of those layers, and it exists to manage log items that have been committed but still need to be written back. That makes the AIL powerful, but it also makes it a place where locking discipline matters a great deal.The vulnerability description points directly at two functions: xfs_inode_item_push and xfs_qm_dquot_logitem_push. In those callbacks, the AIL lock is dropped while buffer I/O is performed. That is a normal-looking optimization in kernel code, because you do not want to hold a global lock while waiting on disk. But once that lock is gone, background reclaim or the dquot shrinker can free the log item, and the callback’s later dereference of lip->li_ailp becomes a use-after-free. In kernel terms, that is the kind of bug that can turn ordinary cleanup work into memory corruption.
The upstream XFS design documents explain why this area is so subtle. XFS permits items to be relogged, moved, and completed across several phases, and the log code explicitly warns that object lifetime and list membership are not the same thing. In other words, the filesystem already assumes that state can change rapidly, so any callback that reaches back into the log item after temporarily giving up protection is skating on thin ice. The documented design also emphasizes that AIL tracking and item tracking must remain separate, precisely because the same object can be in motion while the log machinery is still processing it.
The new CVE is not an abstract theoretical race. The broader Linux ecosystem has seen repeated XFS memory-safety issues over the years, and syzkaller has historically been good at shaking them loose. That matters because filesystem bugs often require precise timing, but once a race is identified, the kernel community usually moves quickly to harden the affected paths. Here, the bug is especially noteworthy because the fix does not require redesigning the logging architecture; it just requires preserving the right pointer at the right moment.
What Actually Went Wrong
At the heart of CVE-2026-31454 is a timing window. The callback enters with the AIL lock held, which means the log item is currently safe to use. Then the code drops the lock to perform I/O, because holding a spinlock across a potentially slow operation would be a mistake. After the I/O completes, the callback tries to reacquire state by dereferencing lip->li_ailp, but the log item may already have been reclaimed.That pattern is easy to explain and hard to get right in practice. The bug is not in the decision to release the lock; it is in assuming that the object remains alive just because the code is about to continue working on it. In kernel memory management, that assumption is often false unless the code has arranged for an independent lifetime guarantee. Here, there is no such guarantee once the callback steps outside the protection of the AIL lock.
Why the dereference is dangerous
The dangerous line is not merely a stale read. Once a freed object has been recycled, the memory may contain unrelated kernel data, which means the callback could follow a corrupted pointer, spin on invalid state, or trigger a crash. In the best case, the system oopses and the damage is contained. In the worst case, a use-after-free can become a primitive for privilege escalation if an attacker can influence allocation patterns.The kernel’s own documentation repeatedly stresses the importance of holding the correct references and respecting the intended lock ordering. That is especially true in XFS, where objects can be in the AIL, in the CIL, or in transition between the two. The line between “still valid” and “already gone” is thin enough that code must preserve the relevant state before leaving the protected region.
Key consequences of the bug include:
- Potential use-after-free in a metadata callback.
- Crash risk under reclaim pressure or quota activity.
- Memory corruption exposure if freed memory is reused.
- Hard-to-reproduce timing dependence, which complicates testing.
- Broad impact on XFS metadata reliability, even if exploitation is not trivial.
The Fix Is Small, but the Lesson Is Big
The remedy described in the CVE record is elegantly minimal: save the ailp pointer into a local variable while the AIL lock is still held, and only then drop the lock for I/O. That means the callback keeps a stable reference to the AIL structure it needs, instead of reaching back through a possibly dead log item afterward. This kind of change is often the best kind of kernel fix, because it narrows the race without introducing new behavior.What makes this a good fix is that it aligns with the principle the kernel community repeats constantly: capture the state you need while you still own the protection for it. The bug did not require a redesign of XFS logging or a new lifecycle model. It required a defensive snapshot of the pointer that the callback will need later, before the lock protecting the object goes away.
Why this pattern is common in kernel code
Kernel developers often face a tradeoff between concurrency and safety. If you hold a lock too long, you hurt throughput and risk deadlocks. If you release it too early, you risk races and lifetime bugs. The right answer is usually to copy out the minimum required state, drop the lock, and continue with the copied state rather than the mutable original.That is exactly what is happening here. The bug illustrates a broader rule: if a callback needs information after a lock is dropped, that information should usually be preserved in a local variable or a separately pinned structure. The details vary by subsystem, but the pattern is universal. Do not trust the original object to still exist once you have voluntarily let go of the protection that kept it alive.
The CVE record references a series of stable kernel commits, indicating the fix has been propagated across supported trees. That is the right operational response for a filesystem bug, because the affected code can live in long-term support branches for years. Once a race is identified, the patch needs to move quickly to the places where real systems are actually running.
Why XFS Was a Plausible Candidate
XFS has a long history of sophisticated metadata handling, and that sophistication comes with complexity. The filesystem’s delayed logging design separates transaction commit, checkpointing, AIL insertion, and final cleanup into multiple phases. That architecture is excellent for performance, but it also means a single object can pass through several different lifetimes before finally becoming quiescent.The design documentation makes clear that log items are not static records. They can be pinned, unpinned, relogged, and removed from the AIL at different times, often under different locks. That flexibility is one of XFS’s strengths, but it also means callback authors need to be hyper-aware of what is still guaranteed to exist after a lock is released. The vulnerability shows what happens when that discipline slips for just one pointer.
AIL, CIL, and object lifetime
The Committed Item List (CIL) and the AIL serve different purposes, and that distinction matters here. The CIL holds committed items awaiting log writeout, while the AIL tracks items that have been committed and still need writeback to disk. If a callback assumes an item will remain valid just because it was recently active, it may be confusing these phases.That confusion is exactly the sort of thing that causes subtle kernel bugs. The design docs explicitly note that the log item can be relogged while it is in the AIL, which means object state is inherently dynamic. As a result, the code must be careful not to lean on fields that only remain safe under the lock that just got dropped.
Important design realities include:
- XFS log items can move through multiple states.
- The AIL is not a lifetime guarantee by itself.
- Callbacks often need to drop locks for I/O.
- Relogging can happen while items are still active.
- Pointer safety must be preserved independently of I/O latency.
Enterprise and Consumer Impact
For enterprise operators, this is the more serious kind of filesystem CVE: not noisy, but foundational. XFS is heavily used in servers, storage appliances, virtualization hosts, and other Linux systems where metadata consistency is not optional. A use-after-free in log handling can mean anything from sporadic crashes under quota pressure to a broader reliability incident on busy multi-tenant systems.For consumer Linux users, the impact is usually narrower but still real. Desktop and workstation systems that use XFS are less likely to hit heavy reclaim or dquot activity, but they are not immune. The practical risk is that a bug in a low-level filesystem path can manifest as an intermittent crash, a locked-up workload, or a corrupted metadata state that is painful to diagnose after the fact.
Why this matters beyond the affected systems
Filesystem vulnerabilities are rarely isolated to one product story. They affect backup systems, hypervisors, container hosts, and fleet management tools that assume the filesystem layer is dependable. When a metadata path goes wrong, the problem can spread upward into application outages, even if the original bug is “just” in a kernel callback.That is why the publication of a CVE matters even when the score has not yet been assigned. Administrators need the signal early, because a seemingly small race in a filesystem can become a support-ticket avalanche if it appears in the wrong storage tier. In infrastructure, reliability is a security feature.
A sensible response strategy is:
- Identify kernels and distributions that carry the affected XFS code.
- Check whether the fix has been backported to the supported branch.
- Prioritize hosts using XFS with quota activity or heavy reclaim pressure.
- Schedule updates in maintenance windows where possible.
- Monitor for panics, warnings, or unexpected filesystem stalls after patching.
The Kernel Community’s Defensive Pattern
This CVE also highlights the kernel community’s preferred style of remediation. Instead of building a heavy abstraction layer around every callback, developers typically fix the exact race and keep the path fast. That is especially important in XFS, where performance-sensitive metadata I/O cannot afford unnecessary serialization.The fact that the fix appears to be limited to capturing ailp locally suggests that maintainers judged the lifetime guarantee to be the real problem, not the overall design of AIL push callbacks. That is reassuring because it means the issue is likely a narrow correctness bug, not evidence that the XFS logging model is fundamentally broken. Still, narrow bugs can have wide consequences when they sit in code that runs in the background for the lifetime of the filesystem.
How this compares to other kernel fixes
This resembles other recent Linux kernel memory-safety repairs in one important respect: the code already had the right high-level idea, but it failed to preserve the necessary state across an unlock boundary. That pattern shows up across subsystems, from network drivers to filesystems, because once you start juggling locks, callbacks, and asynchronous work, lifetime bugs are everywhere.The distinction between “protected state” and “remembered state” is central. Protected state is only safe while the relevant lock or reference is held. Remembered state must be copied, pinned, or refcounted in a way that survives the unlock. CVE-2026-31454 is a textbook case of what happens when a callback forgets which category its data belongs to.
Notable kernel-hardening themes here are:
- Snapshot critical pointers before unlocking.
- Avoid dereferencing mutable log-item fields after I/O.
- Keep I/O latency away from lock-holding paths.
- Prefer minimal, local fixes over invasive redesigns.
- Treat background reclaim as an active adversary to object lifetime.
Microsoft’s Security Guide Signal Matters
Microsoft’s inclusion of the CVE in its Security Update Guide is an important signal for Windows-adjacent audiences, even though the vulnerability itself is in Linux kernel code. Microsoft’s security ecosystem increasingly tracks open-source components that may appear in enterprise environments, support tooling, or partner distributions. For large organizations, that means a Linux kernel CVE does not live in a separate universe; it belongs in the same risk-triage flow as other infrastructure issues.The NVD entry currently shows no CVSS score at the time of publication, which is not unusual for a freshly listed issue. Early disclosure often arrives before formal scoring has been completed. That leaves defenders in a familiar situation: they must evaluate operational exposure based on the bug’s behavior rather than waiting for the final severity number to tell the whole story.
What the absence of a score really means
An unscored CVE is not a harmless CVE. It usually means the process of enrichment is still underway, not that the issue lacks impact. In this case, the description itself is enough to establish that the bug involves a use-after-free in core filesystem code, which is already a strong reason to pay attention.The absence of a score also creates a subtle communications problem. Some teams wait for a number before scheduling remediation, but that can be a mistake when the weakness is obvious from the code path and from the attack surface. The technical description often matters more than the numeric label.
Operational takeaways:
- Do not wait for CVSS before assessing exposure.
- Treat filesystem UAFs as high-priority hygiene issues.
- Verify backport status in your distribution stream.
- Use the vendor advisory as a trigger for internal review.
- Track kernel patch levels separately from application patch levels.
Strengths and Opportunities
The good news is that this vulnerability appears to have a contained, comprehensible fix. XFS maintainers can preserve the needed pointer locally, keep the lock drop for I/O, and avoid the dangerous post-unlock dereference without rewriting the subsystem. That is the kind of patch profile operators like to see because it usually means limited regression risk and a clear backport path.The broader opportunity is to use this event as a reminder that concurrency bugs are often more about lifecycle discipline than about exotic exploitation. Better review habits, targeted testing, and more aggressive race-focused fuzzing can catch similar issues earlier.
- Minimal fix surface reduces the chance of collateral regressions.
- Clear root cause makes code review and verification easier.
- Stable-tree backports are likely to be straightforward.
- Filesystem maintainers can reuse the lesson across similar callbacks.
- Fuzzing and KASAN-style testing remain highly valuable.
- Enterprise administrators get a concrete patch target rather than a vague warning.
- The issue may help harden other reclaim-sensitive XFS paths.
Risks and Concerns
The main concern is that use-after-free bugs in kernel filesystem code can be difficult to reproduce until they suddenly are not. A race that only triggers under pressure can remain invisible in testing but show up in production under load, which is exactly where it is most disruptive. That makes rapid patching important even when exploitability is not yet fully characterized.Another worry is that similar patterns may exist elsewhere in the XFS codebase or in other filesystem callbacks. Once a project finds one object-lifetime bug in a family of functions, reviewers usually go back and inspect adjacent paths for the same mistake. That is healthy, but it also means the published CVE may be only the first visible symptom of a larger audit effort.
- Timing-dependent crashes may evade casual validation.
- Backport mistakes can introduce new regressions if rushed.
- Adjacent callback paths may share the same design hazard.
- Quota-heavy or reclaim-heavy systems may be more exposed.
- Systems with long-lived XFS mounts may carry the risk longer.
- Operational teams may underestimate a “small” UAF in core storage code.
- Patched and unpatched kernels may behave differently under edge conditions, complicating support.
Looking Ahead
The next thing to watch is how quickly the fix propagates through major Linux distributions and enterprise kernel branches. Because the issue was recently published and the NVD scoring is still pending, many administrators will be in the window where the advisory exists but the downstream package update has not yet landed. That is often when temporary risk acceptance turns into a real outage if teams wait too long.It will also be worth watching whether kernel maintainers identify related patterns in other XFS push or reclaim paths. The current bug is specific, but the underlying lesson is broad: once the code drops a lock to perform asynchronous work, anything reachable only through the freed object’s fields becomes suspect. In a codebase as concurrent as XFS, that kind of review often pays dividends well beyond one CVE.
Items to monitor
- Distribution backports for supported Linux kernels.
- Any follow-on XFS patches that harden related callbacks.
- Future NVD enrichment for CVSS scoring and CWE assignment.
- Reports of crashes or KASAN findings in patched versus unpatched builds.
- Whether storage vendors issue their own advisories for appliance kernels.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center