A newly published Linux kernel CVE is drawing attention for a deceptively small reason: the X.25 networking stack could let one internal packet counter grow past its safe bounds, and the fix now requires both an overflow check and a reset during queue cleanup. Microsoft’s Security Update Guide has already surfaced the issue as CVE-2026-31417, while the Linux stable tree points to the upstream fix that closes the hole before it can snowball into corrupted bookkeeping or unstable packet handling. The record is still awaiting NVD enrichment, so there is no final CVSS score yet, but the code change itself tells the story clearly enough: this is a classic kernel-hardening bug in a legacy protocol path, not a flashy exploit chain. Linux kernel’s networking stack is a study in layered history. Newer protocols and fast-path drivers often get the spotlight, but older subsystems like X.25 continue to live on because the kernel is expected to support long-tail industrial, telecom, and embedded environments. That is part of why bugs in these paths matter: they are easy to ignore until a deployment depends on them, and then they become operationally expensive very quickly. The fix for CVE-2026-31417 is a good example of this kind of maintenance work because it addresses accounting logic rather than packet parsing, crypto, or a modern transport feature.
The vulnerability dly direct. It says the kernel now adds a check to ensure that
That pattern matters because kernel netwils in a vacuum. A stale length field can distort later decisions about how much data has been queued, whether a fragment set is complete, and whether the socket should keep accepting more payload. Even when the immediate symptom is only a wraparound or a miscount, the broader effect can be packet loss, abnormal state transitions, or a crash if downstream code assumes the accounting is trustworthy. In the kernel, trustworthy bookkeeping is security-relevant bookkeeping.
Microsoft’s appearance in the disclosure path is also notableity Update Guide increasingly serves as a central intake point for Linux CVEs that matter to enterprise administrators, especially in mixed-platform environments. That does not mean Windows is affected here; it means the vulnerability is being tracked where many IT teams already look for actionable remediation data. Microsoft’s own Linux documentation for Azure Linux notes that CVEs are monitored and that security updates are published through its update mechanisms, reinforcing the idea that Linux defects now live in a broader enterprise disclosure ecosystem rather than a single distro mailing list.
Legacy does not mean irrelevant. In fact, older protocol support is often where the most subtle defects remain because the code paths are exercised less frequently and tested less aggressively. X.25 is not a headline feature on a modern desktop, but kernel support for older networks, industrial gateways, and specialized appliances means the code remains part of the threat surface. A bug in such a subsystem can sit dormant for years and still matter the moment a site deploys it in a real operational environment.
The important point is that “rarely used” is not the same thing as “safe to ignore.” A protocol path that only runs in niche deployments is still worth fixing because those deployments are often the ones with the least flexibility, the longest maintenance windows, and the most painful downtime. That is exactly the kind of environment where a quiet kernel CVE can become a serious support event.
That is the kind of bug that often looks boring in isolation but becomes much more serious when it sits in the middle of packet assembly. If a length accumulator is allowed to rnel can lose track of how much data is actually buffered. Once that happens, follow-on logic may make the wrong decision about queue completion, fragmentation status, or buffer limits. The danger is not just the wrap itself; it is the false confidence created after the wrap.
The role of
That distinction is why the fix has two parts. A pure overflow check would stop the counter from rolling over, but it would not address the case where a queue purge leaves the old length behind. Resetting the field during
That is why cleanup logic is often as important as the accumulation logic itself. In kernel code, a bug in teardown can be just as dangerous as a bug in allocation, because teardown defines the boundary between one packet state and the next. When that boundary is unclear, the kernel can inherit stale assumptions across sessions.
The NVD record still says the case is awaiting enrichment, which means the current public data does not yet include a final severity score. That should not be mistaken for uncertainty about the bug itself. It simply me is still being completed, and triage teams should rely on the kernel fix description, the stable references, and local exposure analysis rather than waiting for a perfect score to appear.
In practice, this kind of flaw often ends up in the “availability risk” bucket. That still matters a great deal. A packet-processing bug that can trigger crashes or inconsistent handling in a host or appliance can have the same operational consequences as a louder exploit if it takes down services that sit in the data path.
The practical lesson is simple: if your environment does not knowingly use X.25, the risk is probably low. If it does, or if you run a specialized appliance that embeds kernel networking features you do not fully control, then this becomes a real patch item rather than an abstract advisory.
That said, small fixes often reveal larger lessons. The fact that the field needs resetting in
That is why robust kernel fixes often combine three ideas: validate inputs, constrain accumulation, and sanitize teardown. Remove any one of those and you may still have a hole. CVE-2026-31417 appears to address all three through a narrowly targeted change.
That makes this CVE a reminder that teardown is a security boundary. When the kernel clears queues, the associated counters should return to a clean state. If they do not, the code is carrying hidden memory of the prior session into the next one.
The Microsoft Security Update Guide angle matters here because many enterprises already aggregate vulnerability data through Microsoft tooling. That makes a Linux kernel CVE visible in the same dashboards as Windows and Azure-related issues, which is useful for prioritization. It ce that a niche Linux bug slips through because the operations team is watching a mixed estate from one place. Microsoft’s Azure Linux documentation explicitly describes CVE monitoring and patch publication as part of its security model, which shows how mainstream this cross-platform visibility has become.
A second exposure point is vendor backport lag. The upstream fix may be straightforward, but enterprises rarely run raw upstream trees. They run distro kernels, appliance firmware, or cloud images, and each of those can ship on a different schedule.
The safest approach is to treat this as a normal kernel maintenance item, not a one-off headline. If X.25 is not in your environment, the remediation burden is low. If it is, version checking and backport validation should happen quickly.
Still, consumers should not assume “niche protocol” means “irrelevant.” Plenty of consumer-adjacent hardware runs Linux under the hood, including routers, home gateways, and lab equipment. If a vendor has embedded older kernel networking code and has not backported the fix, the issue could show up in ways that are hard to diagnose. Small kernel bugs often surface first as weird instability, n.
That is why firmware updates should not be skipped just because the issue sounds technical or niche. Vendors often bundle these fixes into routine maintenance releases, and users rarely know which kernel subsystems are active behind the scenes.
A consumer does not need to become an X.25 expert. They do need to keep routers, gateways, and embedded Linux devices updated. That is where a bug like this is most likely to matter outside the data center.
That is significant because it changes how defenders consume information. Instead of waiting for a distro mailing list or a single upstream advisory, teams can encounter the same issue in a Microsoft-visible portal that already feeds compliance and asset-management workflows. For a practical IT operation, that is less about politics and more about reducing blind spots.
The flip side is that teams must still verify applicability locally. A Linux CVE in a Microsoft portal does not automatically mean your Windows estate is exposed. It means the advisory is relevant to your inventory workflow, not necessarily to every endpoint you manage.
That is especially important for bugs like this one, where the likely impact depends heavily on whether X.25 is enabled, how the subsystem is used, and whether the affected kernel branch has already received the backport.
The broader opportunity is operational discipline. Teams can use this CVE as a reminder to inventory rare protocol paths, validate kernel backports, and improve their handling of “niche” advisories that still affect critical infrastructure.
There is also a long-tail risk that vendor backports will not land uniformly. In the Linux ecosystem, the public fix and the shipped fix are often separated by packaging, maintenance windows, and appliance release schedules. That means exposure can persist long after the upstream correction is public.
It will also be worth watching whether this fix triggers a broader audit of old packet-accumulation code in adjacent networking paths. Kernel bugs often travel in families: once one state-lifecycle mistake is found, reviewers may discover that neighboring subsystems share the same weak pattern. That is where one small CVE can become a useful signal for a larger hardening effort.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
The vulnerability dly direct. It says the kernel now adds a check to ensure that
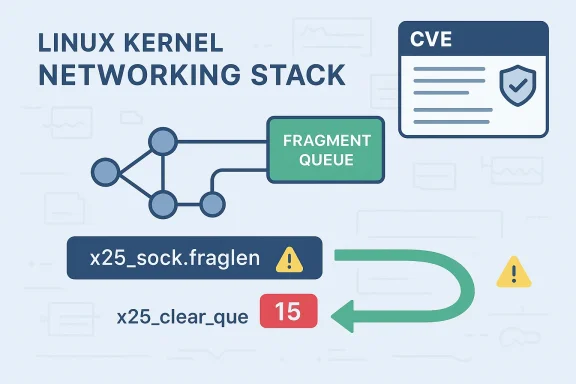
x25_sock.fraglen cannot overflow, and that fraglen also has to be reset when fragment_queue is purged in x25_clear_queues(). That combination tells you the bug is not just a single arithmetic oversight. It is also a state-lifecycle problem, which is often how these issues survive code review: the number stays “valid” for a while, then a cleanup path fails to zero it out, and the next accumulation starts from a stale value.That pattern matters because kernel netwils in a vacuum. A stale length field can distort later decisions about how much data has been queued, whether a fragment set is complete, and whether the socket should keep accepting more payload. Even when the immediate symptom is only a wraparound or a miscount, the broader effect can be packet loss, abnormal state transitions, or a crash if downstream code assumes the accounting is trustworthy. In the kernel, trustworthy bookkeeping is security-relevant bookkeeping.
Microsoft’s appearance in the disclosure path is also notableity Update Guide increasingly serves as a central intake point for Linux CVEs that matter to enterprise administrators, especially in mixed-platform environments. That does not mean Windows is affected here; it means the vulnerability is being tracked where many IT teams already look for actionable remediation data. Microsoft’s own Linux documentation for Azure Linux notes that CVEs are monitored and that security updates are published through its update mechanisms, reinforcing the idea that Linux defects now live in a broader enterprise disclosure ecosystem rather than a single distro mailing list.
 Why legacy protocol bugs still get CVEs
Why legacy protocol bugs still get CVEs
Legacy does not mean irrelevant. In fact, older protocol support is often where the most subtle defects remain because the code paths are exercised less frequently and tested less aggressively. X.25 is not a headline feature on a modern desktop, but kernel support for older networks, industrial gateways, and specialized appliances means the code remains part of the threat surface. A bug in such a subsystem can sit dormant for years and still matter the moment a site deploys it in a real operational environment.The important point is that “rarely used” is not the same thing as “safe to ignore.” A protocol path that only runs in niche deployments is still worth fixing because those deployments are often the ones with the least flexibility, the longest maintenance windows, and the most painful downtime. That is exactly the kind of environment where a quiet kernel CVE can become a serious support event.
What the Bug Actually Is
At a technical level, CVE-2026-31417 appears to be an integer and state-management bug in the X.25 fragment-accumulation path. The kernel tracks fragment length inx25_sock.fraglen, and the new fix adds a guard so that the field cannot wrap when packets are accumulated. The stable reference also says the field must be reset when fragment_queue is cleared, which implies the old logic could preserve a stale running total and let later packets inherit a misleading baseline.That is the kind of bug that often looks boring in isolation but becomes much more serious when it sits in the middle of packet assembly. If a length accumulator is allowed to rnel can lose track of how much data is actually buffered. Once that happens, follow-on logic may make the wrong decision about queue completion, fragmentation status, or buffer limits. The danger is not just the wrap itself; it is the false confidence created after the wrap.
The role of fraglen
fraglen is doing more than counting bytes. It is effectively a piece of protocol state that tells the kernel how much fragmented data has been collected for the current the value is accurate, later code can reason safely about fragment progression. When it is stale or overflowed, the rest of the subsystem is working with a fiction.That distinction is why the fix has two parts. A pure overflow check would stop the counter from rolling over, but it would not address the case where a queue purge leaves the old length behind. Resetting the field during
x25_clear_queues() closes that second door and makes the lifecycle behavior consistent.Why the queue purge matters
Purge paths are where latent bugs tend to hide. Normal traffic exercises the “happy path,” but error recovery, teardown, and reset operations are often less frequently tested. If a fragment queue is dropped without resetting the associated length field, the next fragment sequence can begin with a corrupted count and behave unpredictably.That is why cleanup logic is often as important as the accumulation logic itself. In kernel code, a bug in teardown can be just as dangerous as a bug in allocation, because teardown defines the boundary between one packet state and the next. When that boundary is unclear, the kernel can inherit stale assumptions across sessions.
- The issue is in fragment length accounting.
- The fix adds a bounds check on accumulation.
- The fix also resets
fraglenduring queue purge. - The vulnerability lives in a legacy X.25 path.
- The impact is likely tied to incorrect state handling and potential instability.
Why This Became a Security Issue
Not every kernel bug is immediately a security bug, but CVE-2026-31417 sits in a category that defenders have learned to take seriously. Any flaw that lets internal counts wrap or stale state persist can create denial-of-service conditions, crash conditions, or logic corruption. In kernel networking, reliability and security overlap heavily, because the same bad state that drops packets can also destabilize the whole subsystem.The NVD record still says the case is awaiting enrichment, which means the current public data does not yet include a final severity score. That should not be mistaken for uncertainty about the bug itself. It simply me is still being completed, and triage teams should rely on the kernel fix description, the stable references, and local exposure analysis rather than waiting for a perfect score to appear.
Security relevance without drama
There is a tendency to equate “security vulnerability” with memory corruption, code execution, or credential theft. But the kernel community has increasingly treated correctness bugs as security-relevaabilize shared infrastructure or create state confusion. That is especially true in networking paths, where malformed or adversarial traffic can repeatedly exercise the weak point.In practice, this kind of flaw often ends up in the “availability risk” bucket. That still matters a great deal. A packet-processing bug that can trigger crashes or inconsistent handling in a host or appliance can have the same operational consequences as a louder exploit if it takes down services that sit in the data path.
The legacy protocol factor
The fact that X.25 is older infrastructure cuts both ways. On one hand, the attack surface is smaller because fewer systems use it. On the other hand, older subsystems can be harder to audit and easier to overlook during routine patching. That makes vendor backports and distribution advisories especially important.The practical lesson is simple: if your environment does not knowingly use X.25, the risk is probably low. If it does, or if you run a specialized appliance that embeds kernel networking features you do not fully control, then this becomes a real patch item rather than an abstract advisory.
Patch Mechanics and Code-Path Hygiene
The beauty of this fix is that it is small but conceptually complete. It does not try to redesign X.25, and it does not introduce a complicated workaround. Instead, it tightens the arithmetic boundary and makes cleanup deterministic. In kernel engineering, that is often the best possible shape of a patch because it corrects the root cause without spreading new complexity through the rest of the stack.That said, small fixes often reveal larger lessons. The fact that the field needs resetting in
x25_clear_queues() shows that the original implementation likely relied on an implied lifecycle guarantee that was not actually enforced. The new fix makes that guother words, the patch is not only about overflow prevention; it is about making object lifetime and queue state line up properly.Why arithmetic checks are not enough
A counter overflow is the obvious bug, but counters in kernel code are almost never isolated. They are part of a bigger state machine. If a field is checked at one point but not reset later, then the system can still start from a broken baseline, and the bug reappears in a different form.That is why robust kernel fixes often combine three ideas: validate inputs, constrain accumulation, and sanitize teardown. Remove any one of those and you may still have a hole. CVE-2026-31417 appears to address all three through a narrowly targeted change.
The cleanup-path lesson
Cleanup-path bugs are easy to miss because they often do not show up in short-lived testing. A socket that is opened, used once, and closed may never reveal the stale-state problem. But long-lived systems, repeated queue flushes, and recovery scenarios are where the bug starts to matter.That makes this CVE a reminder that teardown is a security boundary. When the kernel clears queues, the associated counters should return to a clean state. If they do not, the code is carrying hidden memory of the prior session into the next one.
- Arithmetic checks catch wraparound.
- State resets prevent stale reuse.
- Queue purge logic must clear associated counters.
- Legacy subsystems need the same rigor as newer ones.
- Cleanup correctness is part of security correctness.
Enterprise Impact
For enterprises, the question is not whether X.25 is fashionable. It is whether any production system depends on it, directly or through a vendor appliance. If the answer is yes, then the patch deserves the same attention as any other kernel fix, especially if the system plays a networking or gateway role. A small accounting flaw can become a broad outage if the affected host is in the packet path for multiple services.The Microsoft Security Update Guide angle matters here because many enterprises already aggregate vulnerability data through Microsoft tooling. That makes a Linux kernel CVE visible in the same dashboards as Windows and Azure-related issues, which is useful for prioritization. It ce that a niche Linux bug slips through because the operations team is watching a mixed estate from one place. Microsoft’s Azure Linux documentation explicitly describes CVE monitoring and patch publication as part of its security model, which shows how mainstream this cross-platform visibility has become.
Where exposure is likely to be highest
The highest-risk environments are probably not consumer desktops. They are more likely to be gateways, industrial systems, telecom appliances, and specialized Linux deployments that still retain protocol support for older infrastructure. Those environments often value long uptime, which paradoxically increases the odds of carrying older kernel code long enough for a bug like this to matter.A second exposure point is vendor backport lag. The upstream fix may be straightforward, but enterprises rarely run raw upstream trees. They run distro kernels, appliance firmware, or cloud images, and each of those can ship on a different schedule.
Why patch verification matters
Because the public record is still being enriched, defenders should verify more than just “a fix exists.” They should verify that the specific package or kernel build they run contains the backported change. That is especially important for long-term-support distributions where the code may be patched without the version number changing in a way that is immediately obvious.The safest approach is to treat this as a normal kernel maintenance item, not a one-off headline. If X.25 is not in your environment, the remediation burden is low. If it is, version checking and backport validation should happen quickly.
Consumer Impact
For typical consumer Windows and Linux users, the direct risk from CVE-2026-31417 is probably limited. Most desktops and laptops do not use X.25, and many users will never encounter the affected code path in ordinary life. That is a good reason not to overstate the urgency for home systems that never touch specialized networking gear.Still, consumers should not assume “niche protocol” means “irrelevant.” Plenty of consumer-adjacent hardware runs Linux under the hood, including routers, home gateways, and lab equipment. If a vendor has embedded older kernel networking code and has not backported the fix, the issue could show up in ways that are hard to diagnose. Small kernel bugs often surface first as weird instability, n.
The embedded-device angle
This is where the consumer story starts to resemble the enterprise story. Home networking equipment, small-office appliances, and hobbyist systems may all rely on vendor-maintained Linux builds that lag upstream. A bug in packet accumulation logic may not be obvious unless a user notices unexplained instability, dropped traffic, or odd restart behavior.That is why firmware updates should not be skipped just because the issue sounds technical or niche. Vendors often bundle these fixes into routine maintenance releases, and users rarely know which kernel subsystems are active behind the scenes.
Why the average user should still care
The average user may not need to manually chase this CVE, but it is a reminder that the kernel is a shared foundation beneath an enormous number of devices. Even niche bugs deserve attention because they can land in products far outside the obvious desktop space.A consumer does not need to become an X.25 expert. They do need to keep routers, gateways, and embedded Linux devices updated. That is where a bug like this is most likely to matter outside the data center.
Microsoft’s Role in Tracking Linux CVEs
Microsoft’s inclusion of this Linux CVE is part of a larger trend: the boundary between “Microsoft security data” and “Linux security data” is getting thinner for enterprise administrators. The company’s security ecosystem increasingly acts as a consolidation layer for vulnerability intelligence, especially in mixed environments where a single team has to watch Windows, Azure, and Linux infrastructure together.That is significant because it changes how defenders consume information. Instead of waiting for a distro mailing list or a single upstream advisory, teams can encounter the same issue in a Microsoft-visible portal that already feeds compliance and asset-management workflows. For a practical IT operation, that is less about politics and more about reducing blind spots.
Why this matters for patch teams
Patch teams benefit when the same vulnerability identifier appears in multiple channels. It improves matching, reduces confusion, and makes it easier to map a CVE to a fleet-wide remediation process. For Linux vulnerabilities that affect enterprise appliances or Azure-adjacent images, that visibility can be the difference between a timely patch and a missed maintenance cycle.The flip side is that teams must still verify applicability locally. A Linux CVE in a Microsoft portal does not automatically mean your Windows estate is exposed. It means the advisory is relevant to your inventory workflow, not necessarily to every endpoint you manage.
What the enrichment status implies
The “awaiting analysis” status in the NVD record is also a reminder that disclosure is staged. Kernel developers may have a clear fix, but NVD enrichment, scoring, and downstream interpretation can take longer. During that gap, operators should look at the actual kernel change, not just the absence of a final severity number.That is especially important for bugs like this one, where the likely impact depends heavily on whether X.25 is enabled, how the subsystem is used, and whether the affected kernel branch has already received the backport.
Strengths and Opportunities
The good news is that this looks like a surgical fix to a clearly bounded bug rather than a sprawling redesign. That makes it easier for maintainers to backport and for vendors to verify. It also shows that the Linux kernel’s stable process is still catching and correcting quiet but important flaws in older networking code.The broader opportunity is operational discipline. Teams can use this CVE as a reminder to inventory rare protocol paths, validate kernel backports, and improve their handling of “niche” advisories that still affect critical infrastructure.
- Narrow patch scope should make backporting easier.
- Two-part fix improves correctness and lifecycle hygiene.
- Legacy protocol hardening reduces long-tail risk.
- Enterprise visibility improves through Microsoft’s guide.
- Stable-tree propagationdors move faster.
- Inventory review can uncover other forgotten protocol paths.
- Patch workflows get better when niche CVEs are tracked centrally.
Risks and Concerns
The main concern is underestimation. Because the bug is in a legacy protocol path and the public record still lacks a completed CVSS assessment, some teams may dismiss it as low priority. That would be a mistake if they actually rely on X.25 or run hardware that embeds the affected code path.There is also a long-tail risk that vendor backports will not land uniformly. In the Linux ecosystem, the public fix and the shipped fix are often separated by packaging, maintenance windows, and appliance release schedules. That means exposure can persist long after the upstream correction is public.
- Low visibility can lead to delayed patching.
- Legacy deployments may remain exposed for years.
- Backport differences can make verification tricky.
- Cleanup-path bugs are easy to miss in testing.
- **Vendor fal operational risk.
- Missing CVSS data should not be treated as “no issue.”
- Specialized appliances are often the hardest to update.
Looking Ahead
The next thing to watch is downstream confirmation. Once distro maintainers and appliance vendors publish their own advisories or package updates, the real-world exposure window will become clearer. Until then, the safest assumption is that any system using X.25 support should be reviewed promptly rather than waiting for a more polished NVD score.It will also be worth watching whether this fix triggers a broader audit of old packet-accumulation code in adjacent networking paths. Kernel bugs often travel in families: once one state-lifecycle mistake is found, reviewers may discover that neighboring subsystems share the same weak pattern. That is where one small CVE can become a useful signal for a larger hardening effort.
- Confirm whether your kernel build includes the stable fix.
- Check whether any production or embedded system uses X.25.
- Verify vendor backports rather than assuming uch for related cleanup bugs in other legacy packet paths.
- Prioritize gateways, appliances, and long-lived Linux deployments.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center