CVE-2026-31497 is another reminder that the most interesting Linux kernel bugs are often the quiet ones. In this case, the flaw sits in the Bluetooth USB driver’s handling of SCO alternate settings, where a small lookup table was being indexed with an unbounded value derived from the number of active SCO links. The fix is narrow—clamp the index before using it—but the lesson is broader: even mature kernel paths can carry out-of-bounds risks when state is translated from one subsystem into another without a final sanity check. Microsoft’s advisory mirrors the kernel.org description, and the upstream stable patch shows the bug has already been treated as serious enough for backporting across multiple supported branches
Bluetooth bugs tend to be deceptive because they often look like quality-of-life issues before they reveal their security value. A failed headset handshake, a flaky audio route, or a weird disconnect can easily be dismissed as user error, yet the kernel code underneath is still making decisions about memory, device state, and protocol behavior. CVE-2026-31497 belongs to that family of defects: the visible path is Bluetooth audio over USB, but the underlying mistake is a classic array-bounds problem in privileged code.
The affected function,
What makes the fix elegant is that it does not try to redesign the feature. It simply constrains the index to the last valid entry using
The patch also has a clear provenance trail. The upstream fix is attributed to Pengpeng Hou and marked with the stable-kernel “Fixes” chain back to
The specific path here sits in
The important detail is that the driver had a small, fixed table of valid alternate settings for a very specific voice mode. A three-element table implies a three-step model: up to three active SCO links, up to three corresponding selections, and no more. But
This is why the stable patch matters as much as the CVE record. The upstream fix was already rolling into stable branches, including 5.15, 6.12, 6.18, and 6.19 review series as seen in the Linux stable mailing lists. That indicates the issue is not just theoretical or developer-facing; it is the kind of defect that maintainers expect downstream vendors to absorb quickly
The broader Bluetooth context also matters. In the last few kernel cycles, Bluetooth-related regressions have repeatedly shown how small transport-layer assumptions can have outsized effects on end users. Sometimes the outcome is a crash, sometimes it is a pairing failure, and sometimes it is simply a mismatch between expected and actual device behavior. CVE-2026-31497 sits in the subtle but real category: the bug is narrow, but the code path is privileged and user-facing, which is enough to make it worth attention.
What the patch changes is therefore straightforward and correct: it creates
The best way to think about this bug is that it is not an exotic exploit primitive. It is a bounds mistake with security implications. In the kernel, that distinction matters less than the fact that a memory read can escape its intended container. Even when the immediate symptom is benign, out-of-bounds reads can destabilize logic, leak data, or create an opening for follow-on faults.
The CVE description explicitly notes that the table only defines alternate settings for up to three SCO links, while
The
The stable review process itself is also a signal. The same patch appears in multiple stable mailing-list threads, which means maintainers were preparing it for several supported kernel lines. That is an operational clue for administrators: if your fleet runs long-term support kernels, this is the kind of change that should arrive through vendor backports, not just mainline tracking.
That simplicity is a strength. Kernel security teams love fixes that can be summarized in one sentence and verified with one small diff. It is also why this CVE is likely to show up in distro advisories with minimal drama once vendors finish folding in the stable commits.
The third risk is misdiagnosis. Users are likely to experience the issue as a Bluetooth glitch, not as a security problem. That can slow remediation because administrators tend to prioritize visible outages over correctness bugs that do not immediately stop the machine. In practice, subtle bugs often linger longer than dramatic ones.
There is also the larger problem of patch lag. Even though the upstream fix is public, many systems run vendor kernels, appliance images, or long-term support branches. Those systems may not pick up the exact repair until downstream maintainers merge it. That means exposure can persist well after the issue is widely known.
A disciplined way to read this CVE is to see it as part of a larger hardening pattern. The kernel community continues to replace implicit assumptions with explicit bounds checks, and every one of those changes narrows the space in which strange device states can cause trouble. That is not glamorous, but it is how mature platform security improves.
That distinction matters. Enterprises often think in terms of server vs. desktop, but the modern workplace is full of Bluetooth-dependent endpoints. In those environments, a kernel bug can become a support issue even if it is not a classic security incident. The cost is then measured in service tickets, user disruption, and time spent proving that the fault is kernel-side rather than in the headset or application layer.
That is where security triage gets messy. It is easy to patch a package by version number; it is harder to decide whether a feature path is reachable in the first place. Because the bug is in a USB transport driver, the affected exposure depends on hardware, driver loading, and the active profile. You do not just need the kernel version; you need the workload context too.
This is also a good example of why kernel fixes can feel boring while still being important. A table clamp does not sound like an urgent security update, but it can be the difference between predictable behavior and a driver that steps beyond its bounds. Consumer systems are full of small assumptions like this, and kernels have a long memory for the mistakes they inherit.
Another practical point is that Bluetooth defects tend to be distributed unevenly. A bug may affect only certain adapters, only certain kernel branches, or only specific audio modes. That means some users will never notice it, while others will experience repeated problems and wonder why the fix seems to apply to everyone else first.
This pattern shows up constantly in driver code. A developer knows the current device family supports a small number of states, writes a compact table, and trusts the higher-level logic to stay in range. Months or years later, another feature extends the state machine, and the old assumption becomes the bug. That is why code review in the kernel is as much about historical context as it is about line-by-line correctness.
The fix for CVE-2026-31497 uses exactly that philosophy. Instead of letting the active SCO count dictate array access, it forces the count to fit the known table. That means even if higher layers produce a larger number, the driver remains within safe bounds. That is the kernel equivalent of putting a guardrail on a narrow bridge.
There is also a wider hardening lesson to watch for. Whenever a driver translates one subsystem’s count into another subsystem’s selection logic, there is an opportunity for similar clamping mistakes. Kernel maintainers will likely continue auditing Bluetooth paths, especially around audio and USB transport, because those are precisely the areas where compact tables and device-specific assumptions tend to accumulate.
One final thing to watch is reporting quality. Early CVE records often start with a precise technical description and little else, then gain richer scoring and remediation detail as NVD enrichment and vendor advisories catch up. For organizations running mixed Linux fleets, the practical answer is simple: verify your build, confirm the backport, and do not wait for a larger symptom before acting.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Overview
Overview
Bluetooth bugs tend to be deceptive because they often look like quality-of-life issues before they reveal their security value. A failed headset handshake, a flaky audio route, or a weird disconnect can easily be dismissed as user error, yet the kernel code underneath is still making decisions about memory, device state, and protocol behavior. CVE-2026-31497 belongs to that family of defects: the visible path is Bluetooth audio over USB, but the underlying mistake is a classic array-bounds problem in privileged code.The affected function,
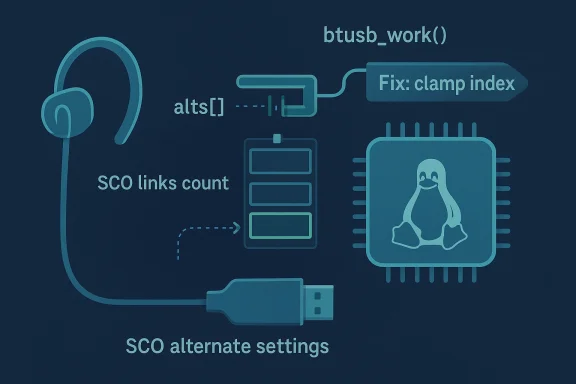
btusb_work, maps the number of active SCO links to USB alternate settings. When the device is using CVSD traffic with transparent voice settings, the code consults a three-entry table named alts and previously used data->sco_num - 1 directly as the index. The issue is that data->sco_num comes from hci_conn_num, which can exceed the table’s capacity, so the code could read past the end of alts if more links were present than the table anticipated.What makes the fix elegant is that it does not try to redesign the feature. It simply constrains the index to the last valid entry using
min_t(unsigned int, data->sco_num - 1, ARRAY_SIZE(alts) - 1) and then proceeds exactly as before. That preserves behavior for supported configurations while closing the memory-safety gap. In kernel maintenance terms, this is the ideal shape of a repair: preserve intent, remove ambiguity, and keep the patch easy to backportThe patch also has a clear provenance trail. The upstream fix is attributed to Pengpeng Hou and marked with the stable-kernel “Fixes” chain back to
baac6276c0a9, the commit that introduced mSBC audio handling over USB endpoints. That matters because the CVE is not being treated as a random cleanup; it is being explicitly tied to the original feature work that created the assumption in the first place.Background
Bluetooth audio in Linux is a layered system, and that layering is exactly why small mistakes can become harder to spot. The stack has to coordinate controller state, voice settings, USB endpoint selection, and the timing of active SCO links. Every layer adds legitimate complexity, but each layer also increases the chance that a value produced in one place will be used too literally in another.The specific path here sits in
btusb, the USB transport driver for Bluetooth devices. Inside that driver, btusb_work is responsible for adjusting alternate settings when SCO traffic is active. Alternate settings are not cosmetic; they determine how the USB interface behaves for a particular mode of operation. If the driver selects the wrong setting, performance may degrade, audio may break, or the code may wander into invalid state.The important detail is that the driver had a small, fixed table of valid alternate settings for a very specific voice mode. A three-element table implies a three-step model: up to three active SCO links, up to three corresponding selections, and no more. But
data->sco_num is not inherently bounded by that table. It reflects active connection count, not “table-safe” count. That mismatch is a typical kernel bug pattern: one subsystem assumes a conceptual limit, another subsystem provides a raw operational count.This is why the stable patch matters as much as the CVE record. The upstream fix was already rolling into stable branches, including 5.15, 6.12, 6.18, and 6.19 review series as seen in the Linux stable mailing lists. That indicates the issue is not just theoretical or developer-facing; it is the kind of defect that maintainers expect downstream vendors to absorb quickly
The broader Bluetooth context also matters. In the last few kernel cycles, Bluetooth-related regressions have repeatedly shown how small transport-layer assumptions can have outsized effects on end users. Sometimes the outcome is a crash, sometimes it is a pairing failure, and sometimes it is simply a mismatch between expected and actual device behavior. CVE-2026-31497 sits in the subtle but real category: the bug is narrow, but the code path is privileged and user-facing, which is enough to make it worth attention.
How the Bug Works
The vulnerability lives in a single decision point: selectingnew_alts from a fixed lookup table. When hdev->voice_setting & 0x0020 is set and the air mode is CVSD, the code uses alts = { 2, 4, 5 } to determine the USB alternate setting. The old logic assumed data->sco_num - 1 would always land within the array bounds, but that assumption breaks if the active SCO count exceeds three.The key mismatch
The problem is not that the table is too small by accident. It is that the code never re-validated the derived index against the size of the table. In a kernel driver, that is a dangerous omission because derived values often travel through several layers before they are consumed. By the time the lookup happens, the driver is already operating with elevated privilege and direct hardware access.What the patch changes is therefore straightforward and correct: it creates
sco_idx, clamps it to ARRAY_SIZE(alts) - 1, and uses the clamped index. That means any count beyond the supported range now resolves to the last valid alternate setting rather than wandering into adjacent memory. It also means the driver continues to choose the highest supported option when the link count is high, which is a sensible fallback behavior.The best way to think about this bug is that it is not an exotic exploit primitive. It is a bounds mistake with security implications. In the kernel, that distinction matters less than the fact that a memory read can escape its intended container. Even when the immediate symptom is benign, out-of-bounds reads can destabilize logic, leak data, or create an opening for follow-on faults.
Why a three-entry table is still risky
A fixed-size table feels safe because it is small and visible. But small tables are often more dangerous in kernel code, not less, because developers may treat them as self-evidently safe and skip the check that would otherwise have been obvious. This is especially true in code that converts protocol state into device settings. The mapping looks simple until the underlying state grows beyond the assumptions baked into the table.The CVE description explicitly notes that the table only defines alternate settings for up to three SCO links, while
data->sco_num comes from hci_conn_num and is used directly. That is the bug in one sentence: a raw count became an array index without a defensive boundary check. The patch restores the missing guardrail and leaves the rest of the logic intact.The Upstream Fix
The upstream fix is a textbook example of surgical kernel remediation. It changes just a few lines indrivers/bluetooth/btusb.c, but those lines are doing important work. Rather than trusting the count, the new code clamps the derived index to the final valid slot in the alternate-setting table. That prevents reading past alts while preserving the intended behavior for legitimate values.Why the patch shape matters
This kind of fix is valuable because it is obviously correct to reviewers. It does not introduce new data structures, it does not alter control flow dramatically, and it does not require new locking. In the Linux kernel, that matters a great deal because every extra moving part increases the risk of regressions in adjacent code paths.The
Fixes: tag also gives the repair an important historical anchor. By pointing back to the mSBC-over-USB-endpoints commit, maintainers are acknowledging that the vulnerability stems from a specific feature assumption rather than a generic Bluetooth failure. That makes the bug easier to audit and easier to reason about across stable branches.The stable review process itself is also a signal. The same patch appears in multiple stable mailing-list threads, which means maintainers were preparing it for several supported kernel lines. That is an operational clue for administrators: if your fleet runs long-term support kernels, this is the kind of change that should arrive through vendor backports, not just mainline tracking.
Why backports are usually straightforward here
Because the fix is so compact, downstream integration should be low friction in most cases. That does not mean every vendor kernel will absorb it immediately, but it does mean the risk of semantic drift is small. The patch only changes how an index is computed; it does not alter the surrounding Bluetooth state machine.That simplicity is a strength. Kernel security teams love fixes that can be summarized in one sentence and verified with one small diff. It is also why this CVE is likely to show up in distro advisories with minimal drama once vendors finish folding in the stable commits.
Security Impact
From a pure severity standpoint, this is not the kind of bug that would make headlines outside the Linux world. It is not a remote code execution chain, and the published advisory does not attach a finalized NVD score yet. But that should not be mistaken for triviality. In kernel security, out-of-bounds reads in privileged paths still matter, especially when they sit in code that configures device behavior.Possible real-world consequences
The first and most obvious risk is instability in Bluetooth audio handling. If the wrong alternate setting is selected or an out-of-bounds value perturbs the flow, the result could be anything from misbehavior to a crash, depending on how the surrounding code responds. The second risk is data integrity inside the kernel itself: even a read past the table can be a foothold for unpredictable behavior.The third risk is misdiagnosis. Users are likely to experience the issue as a Bluetooth glitch, not as a security problem. That can slow remediation because administrators tend to prioritize visible outages over correctness bugs that do not immediately stop the machine. In practice, subtle bugs often linger longer than dramatic ones.
There is also the larger problem of patch lag. Even though the upstream fix is public, many systems run vendor kernels, appliance images, or long-term support branches. Those systems may not pick up the exact repair until downstream maintainers merge it. That means exposure can persist well after the issue is widely known.
Why Bluetooth deserves more respect than it gets
Bluetooth code is often treated as peripheral, but that is a mistake. It is in constant use on laptops, desktops, conferencing setups, headsets, docking stations, and embedded devices. A bug in the Bluetooth stack may not be “critical infrastructure” in the traditional sense, but it still affects a real attack and reliability surface across the modern endpoint estate.A disciplined way to read this CVE is to see it as part of a larger hardening pattern. The kernel community continues to replace implicit assumptions with explicit bounds checks, and every one of those changes narrows the space in which strange device states can cause trouble. That is not glamorous, but it is how mature platform security improves.
Enterprise Implications
Enterprises should treat CVE-2026-31497 as a low-lift but meaningful maintenance item. The patch is small, the affected path is specific, and the code change is easy to verify. That combination makes it a good candidate for normal patch-cycle handling rather than emergency response, provided your environments do not rely heavily on Bluetooth voice handling in production.Where the practical exposure is highest
The most likely affected systems are laptops, docking stations, conference-room endpoints, developer workstations, and specialized Linux devices that use Bluetooth audio heavily. Most servers will never touch the path, but organizations with mobile fleets or workstation-heavy environments may see the bug more often simply because they use the Bluetooth stack more aggressively.That distinction matters. Enterprises often think in terms of server vs. desktop, but the modern workplace is full of Bluetooth-dependent endpoints. In those environments, a kernel bug can become a support issue even if it is not a classic security incident. The cost is then measured in service tickets, user disruption, and time spent proving that the fault is kernel-side rather than in the headset or application layer.
Why inventory matters
A patch is only useful if administrators know where to deploy it. If you run Linux workstations, thin clients, or kiosk-style systems with Bluetooth audio use, this CVE deserves attention. If your fleet is almost entirely headless servers, the operational priority is lower. The challenge is that many organizations do not inventory Bluetooth usage with enough granularity to know the difference.That is where security triage gets messy. It is easy to patch a package by version number; it is harder to decide whether a feature path is reachable in the first place. Because the bug is in a USB transport driver, the affected exposure depends on hardware, driver loading, and the active profile. You do not just need the kernel version; you need the workload context too.
- Review endpoints that rely on Bluetooth audio.
- Check whether vendor kernels already carry the backport.
- Verify that long-term support builds include the clamp fix.
- Prioritize systems with frequent SCO usage.
- Do not assume “desktop-only” means “low priority.”
- Include Bluetooth-heavy workstations in patch validation.
- Treat any kernel memory-safety bug as worth checking, even if the first symptom is just a device glitch.
Consumer Implications
For most consumers, CVE-2026-31497 is likely to be more of a reliability issue than an obvious security crisis. Ordinary users may never encounter the vulnerable path, and many will only notice Bluetooth behavior if they are using headsets, calls, or voice-driven workflows on Linux laptops. Still, consumer relevance should not be dismissed, because this is exactly the kind of bug that tends to surface in everyday peripherals.Why the average user should care
Bluetooth is one of those technologies that feels invisible until it fails. When it fails at the kernel layer, users typically see strange symptoms: audio cutouts, unstable device switching, or hardware that behaves differently after a system update. That makes it hard to distinguish from a normal compatibility problem, which is why public advisories like this matter.This is also a good example of why kernel fixes can feel boring while still being important. A table clamp does not sound like an urgent security update, but it can be the difference between predictable behavior and a driver that steps beyond its bounds. Consumer systems are full of small assumptions like this, and kernels have a long memory for the mistakes they inherit.
Another practical point is that Bluetooth defects tend to be distributed unevenly. A bug may affect only certain adapters, only certain kernel branches, or only specific audio modes. That means some users will never notice it, while others will experience repeated problems and wonder why the fix seems to apply to everyone else first.
What users should watch for
Users running Linux desktops or laptops should pay attention to kernel updates from their distribution, especially if they use Bluetooth audio frequently. If a vendor ships a backported kernel fix, the version number may not clearly reveal it, so the release notes matter more than the raw package string. That is a common trap with backported security fixes.- Bluetooth audio behaving strangely after a kernel update.
- Headsets or microphones that fail in voice-call scenarios.
- Vendor kernel releases that mention btusb or SCO handling.
- Distro updates that do not obviously change the mainline version.
- Systems where multiple Bluetooth devices are active at once.
- An apparent “compatibility” bug that keeps returning after reboot.
- Userspace tools showing no obvious clue that the fault is in the driver.
Why This Kind of Bug Keeps Happening
Kernel code is full of translated state: a count becomes an index, a protocol flag becomes a USB mode, a device condition becomes a workqueue action. Every translation is a place where assumptions can drift away from reality. CVE-2026-31497 is a reminder that the kernel is not just executing logic; it is continuously converting one form of truth into another.The risk of “small tables”
Small tables are seductive because they feel bounded and safe. But they often represent a policy decision, not a mathematical law. If the policy changes—or if the code feeding the table does not share the same limit—the table becomes a trap. That is exactly what happened here: the alternate-setting table had a real ceiling, but the input count did not inherit that ceiling automatically.This pattern shows up constantly in driver code. A developer knows the current device family supports a small number of states, writes a compact table, and trusts the higher-level logic to stay in range. Months or years later, another feature extends the state machine, and the old assumption becomes the bug. That is why code review in the kernel is as much about historical context as it is about line-by-line correctness.
The importance of clamping
Clamping is one of those humble techniques that solves a lot of real problems. It does not prevent all logic errors, but it prevents a class of them from becoming memory-safety issues. In a system as complex as Linux, that is not a small win. It is a hardening principle that should be everywhere, especially where hardware-facing drivers consume counts, sizes, and indexes from multiple subsystems.The fix for CVE-2026-31497 uses exactly that philosophy. Instead of letting the active SCO count dictate array access, it forces the count to fit the known table. That means even if higher layers produce a larger number, the driver remains within safe bounds. That is the kernel equivalent of putting a guardrail on a narrow bridge.
- Raw counts should rarely become raw indexes.
- Tables define policy, not certainty.
- Defensive clamping is cheap compared with debugging memory faults.
- Driver code should assume upstream state can be broader than expected.
- Backward-compatible fixes are usually the best fixes.
- Tiny bugs in device mode selection can still be security-relevant.
- Historical feature commits often explain the present-day vulnerability.
Strengths and Opportunities
The good news is that this is the kind of bug the Linux ecosystem is well suited to fix. The repair is simple, the affected path is narrow, and the stable-maintainer pipeline is already engaged. That gives vendors a clean path to backport the change and gives administrators a straightforward way to verify whether their kernels are protected- The fix is surgical and low-risk to backport.
- The affected code path is easy to identify in audits.
- The bug has a clear root cause and a clear remediation.
- The patch preserves intended behavior for valid inputs.
- Stable branches are already carrying the change.
- It reinforces the value of clamping derived indices.
- It gives distro maintainers a straightforward security story.
- It can be used to review nearby Bluetooth driver assumptions.
- It encourages better input-to-index hygiene across drivers.
- It is a good example of why narrow fixes often age well.
Risks and Concerns
The biggest concern is underestimation. Because the bug looks like a small bounds issue rather than a dramatic exploit, organizations may rank it too low and leave it unpatched longer than they should. That would be a mistake, because kernel out-of-bounds reads in device-facing paths are exactly the kind of “small” defects that can produce unpredictable behavior later- Administrators may dismiss it as a low-severity Bluetooth annoyance.
- Vendor backports may lag behind the public stable patch.
- Some users may never know whether their build includes the fix.
- Bluetooth-heavy endpoint fleets can hide more exposure than server inventories suggest.
- The bug could be misdiagnosed as a peripheral compatibility problem.
- Multiple supported kernel branches increase patch-tracking complexity.
- A small memory-safety issue can still destabilize a privileged driver.
- Version strings alone may not reveal whether the clamp is present.
- End users may assume symptoms are hardware-related and delay updates.
- The risk window can remain open quietly in long-term support builds.
Looking Ahead
The immediate question is not whether the upstream kernel is fixed—it is—but how quickly the patch lands in the kernel builds people actually run. That is always the real issue with Linux CVEs. Production exposure is determined less by the mainline commit and more by the vendor backport, the distro update cadence, and the hardware mix inside each environment.There is also a wider hardening lesson to watch for. Whenever a driver translates one subsystem’s count into another subsystem’s selection logic, there is an opportunity for similar clamping mistakes. Kernel maintainers will likely continue auditing Bluetooth paths, especially around audio and USB transport, because those are precisely the areas where compact tables and device-specific assumptions tend to accumulate.
One final thing to watch is reporting quality. Early CVE records often start with a precise technical description and little else, then gain richer scoring and remediation detail as NVD enrichment and vendor advisories catch up. For organizations running mixed Linux fleets, the practical answer is simple: verify your build, confirm the backport, and do not wait for a larger symptom before acting.
- Watch for distro advisories referencing the btusb clamp fix.
- Confirm whether your long-term support kernel contains the patch.
- Validate Bluetooth-heavy workstation fleets first.
- Look for adjacent driver code that maps counts to tables.
- Recheck any vendor kernel whose versioning hides backports.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center