CVE-2026-31446 is a reminder that some of the most dangerous Linux kernel flaws are not dramatic crashes or headline-grabbing remote exploits, but small timing mistakes in teardown code that only appear under real operational pressure. In this case, the ext4 filesystem can hit a use-after-free while
The vulnerability sits in one of Linux’s most battle-tested filesystems, which is precisely why it deserves attention. Ext4 is widely used because it is familiar, conservative, and generally robust, but its maturity also means that many of its most subtle bugs are lifecycle bugs rather than simple parsing mistakes. This CVE is rooted in the way ext4 tears down per-filesystem sysfs state during unmount while background work can still attempt to report errors through that same interface.
The specific problem arose after an earlier fix, commit
That means the bug is not “ext4 forgot to clean up.” It is more specific than that. The teardown order made sense for one race, but it exposed another, and the new failure mode is a classic use-after-free on the kernel object graph. In kernel terms, that is exactly the sort of bug that can remain invisible under normal testing but become dangerous under heavy unmount, recovery, or error-reporting activity.
The upstream description makes the sequence easy to visualize.
This is the sort of bug that matters beyond a single filesystem call path because it touches the contract between kernel subsystems. Ext4 owns the lifetime of its kobject, sysfs assumes that object is still valid when a notification is issued, and workqueue timing can invalidate both assumptions at once. When that happens, the problem stops being a filesystem quirk and becomes a broader lesson about object lifetime discipline in concurrent kernel code.
That distinction matters because kernel workqueues are designed to decouple producers and consumers in time. Once a work item has been queued, it may run while unmount is already freeing the structures it expects to use. The ext4 bug is a textbook example of why “flush later” and “delete now” can be an unsafe combination when object ownership is shared across code paths.
The locking is also important because it acknowledges a real concurrency hazard rather than pretending the sysfs state flag alone is enough. Kernel developers often have to combine a validity check with serialization to make the check meaningful. Without the mutex, the
That makes the vulnerability more serious than a simple cleanup bug, even if the public description does not assign a CVSS score yet. Memory safety violations in kernel teardown paths are dangerous because they can lead to crashes, data corruption, or in some cases a more exploitable primitive depending on surrounding conditions. The safest assumption is that such bugs deserve timely patching even when their exact exploitability is still under analysis.
The most immediate consequences are operational, not theatrical. You can get unexpected kernel warnings, unmount instability, or failure modes that complicate incident response. If the bug intersects with error reporting or filesystems being torn down after a fault, it can also make the postmortem harder because the very path meant to report a problem becomes part of the problem.
Consumer impact is usually a lower-probability stability issue, while enterprise impact is a higher-probability operational issue. That distinction matters for patch priority. A home user may wait for the next routine update cycle, but an infrastructure team should treat a filesystem teardown UAF as something to verify promptly across supported kernels.
That pattern appears across the kernel: a flag alone is not enough when multiple threads can mutate the underlying object. This is why so many memory-safety fixes end up involving some mixture of refcounting, serialization, and state validation. The architecture of the fix often tells you as much as the bug itself.
The new patch is better because it accepts that background work may still exist and makes the notification path robust even after teardown. That is a more maintainable way to deal with concurrent unmounts, because it protects the path that is hardest to reason about: the one that can run late.
That same pattern is why kernel maintainers are generally willing to accept extra synchronization in teardown paths if it avoids a lifetime hazard. The cost is usually a small amount of complexity or overhead; the benefit is avoiding a bug that can ruin an entire mount or reboot sequence. In storage code, correctness always outranks elegance.
This is also a reminder that sysfs is not just cosmetic. It is part of the kernel’s live object model, and tearing it down incorrectly can have real memory-safety consequences. A filesystem with sysfs hooks must treat those hooks as first-class objects with lifetimes that deserve the same discipline as the data structures that back actual I/O.
A fourth benefit is that the fix preserves existing behavior for the normal case. If sysfs is still present, notification still happens. If it has already been torn down, the notification is safely skipped. That makes the patch less invasive than alternative approaches that would reshuffle the entire unmount sequence.
Still, operators should not assume all ext4 kernels are immediately protected just because the CVE is public. In practice, exposure depends on whether the running kernel has the fix or a proper backport. Version verification matters more than advisory headlines.
The ecosystem takeaway is more subtle: the Linux kernel continues to evolve through countless small correctness fixes rather than giant rewrites. That is how mature software gets safer. Each fix hardens a specific invariant, and each invariant strengthens the reliability story that administrators depend on.
The competitive advantage belongs to vendors and distributions that can ingest such fixes quickly and prove they did so accurately. In mixed fleets, patch velocity is part of reliability, and reliability is part of security. That is as true for a filesystem lifetime bug as it is for a flashy remote exploit.
A third concern is underestimation. Because this CVE is not a glamorous exploit chain, it would be easy to relegate it below louder issues. That would be a mistake. Reliability problems in kernel teardown can become outages, and outages are security problems when they affect availability, recovery, or the integrity of the storage stack. The absence of spectacle does not mean the absence of risk.
CVE-2026-31446 will not dominate headlines, but it will matter to the people who keep Linux systems healthy under load. The patch is good engineering because it respects the kernel’s concurrency model, restores the safety of sysfs notification during teardown, and avoids the temptation to solve a race with a blunt reorder that might simply move the bug elsewhere. In practical terms, that is the right outcome: a quiet fix to a quiet bug, delivered before the race becomes someone’s production incident.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
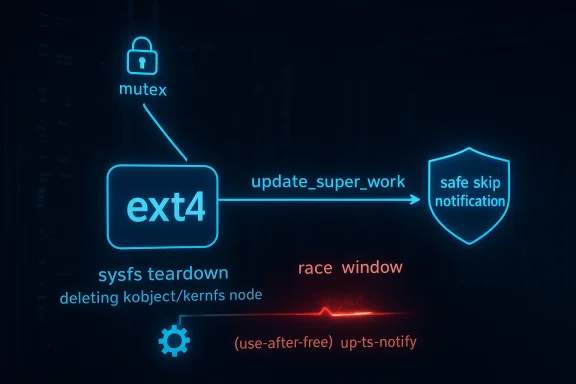
update_super_work races with umount, creating a window where sysfs teardown and delayed error notification step on each other. The fix is notable not because it rewrites ext4, but because it tightens the object-lifetime rules around sysfs notification and prevents a stale kernfs_node from being touched after deletion. That makes the issue especially relevant to administrators who rely on ext4 at scale, where rare races become inevitable over time.
 Background
Background
The vulnerability sits in one of Linux’s most battle-tested filesystems, which is precisely why it deserves attention. Ext4 is widely used because it is familiar, conservative, and generally robust, but its maturity also means that many of its most subtle bugs are lifecycle bugs rather than simple parsing mistakes. This CVE is rooted in the way ext4 tears down per-filesystem sysfs state during unmount while background work can still attempt to report errors through that same interface.The specific problem arose after an earlier fix, commit
b98535d09179, moved ext4_unregister_sysfs() before flushing s_sb_upd_work. That change was meant to stop new error work from being queued via /proc/fs/ext4/xx/mb_groups reads during unmount. The trade-off was subtle: by tearing down sysfs earlier, ext4 created a new race where update_super_work() could still call ext4_notify_error_sysfs() after the kobject backing the sysfs directory had already been deleted.That means the bug is not “ext4 forgot to clean up.” It is more specific than that. The teardown order made sense for one race, but it exposed another, and the new failure mode is a classic use-after-free on the kernel object graph. In kernel terms, that is exactly the sort of bug that can remain invisible under normal testing but become dangerous under heavy unmount, recovery, or error-reporting activity.
The upstream description makes the sequence easy to visualize.
ext4_put_super() calls ext4_unregister_sysfs(sb), which invokes kobject_del(&sbi->s_kobj). That eventually clears kobj->sd, drops the sysfs directory reference, and frees the underlying kernfs_node. Meanwhile, update_super_work can still reach ext4_notify_error_sysfs(sbi), which calls sysfs_notify(&sbi->s_kobj) and dereferences the stale kobj->sd pointer. The result is a race between teardown and notification, with the loser being memory safety.This is the sort of bug that matters beyond a single filesystem call path because it touches the contract between kernel subsystems. Ext4 owns the lifetime of its kobject, sysfs assumes that object is still valid when a notification is issued, and workqueue timing can invalidate both assumptions at once. When that happens, the problem stops being a filesystem quirk and becomes a broader lesson about object lifetime discipline in concurrent kernel code.
What Changed in Ext4
The fix does not attempt to reorder the whole unmount path again. Instead, it adds a guard soext4_notify_error_sysfs() can detect that sysfs has already been torn down and simply skip sysfs_notify() in that case. The test uses s_kobj.state_in_sysfs, which is the correct signal that the sysfs object is no longer live. That is a small change in code, but a large change in safety.Why the earlier reordering was not enough
The previous fix was trying to solve a legitimate problem: avoid queueing new delayed work while unmount is already in progress. But teardown order alone could not safely coordinate all concurrent readers and workers, because a work item already in flight can outlive the sysfs object it wants to notify. In other words, stop new work is not the same thing as make existing work harmless.That distinction matters because kernel workqueues are designed to decouple producers and consumers in time. Once a work item has been queued, it may run while unmount is already freeing the structures it expects to use. The ext4 bug is a textbook example of why “flush later” and “delete now” can be an unsafe combination when object ownership is shared across code paths.
The new locking model
To close the remaining window, ext4 introduces a dedicated mutex,s_error_notify_mutex, to serialize ext4_notify_error_sysfs() against kobject_del() in ext4_unregister_sysfs(). That prevents a time-of-check/time-of-use gap where sysfs could be present during the state check but gone by the time sysfs_notify() runs. This is the right kind of fix: narrow, explicit, and aligned with the race being patched.The locking is also important because it acknowledges a real concurrency hazard rather than pretending the sysfs state flag alone is enough. Kernel developers often have to combine a validity check with serialization to make the check meaningful. Without the mutex, the
state_in_sysfs test could still become stale before notification. That is the essence of the race.- The bug was introduced by a previous teardown reordering.
- The vulnerable path involves delayed work and sysfs notification.
- The fix skips notification after sysfs teardown.
- A dedicated mutex blocks the TOCTOU race.
- The patch is surgical rather than architectural.
The Race Condition in Plain English
At a high level, ext4 is trying to tell sysfs about an error state while the filesystem is being dismantled. If the unmount path tears down the sysfs object first, and the worker thread arrives a little later, the worker may still think it has a valid object to notify. That is how a stale pointer becomes a live kernel memory access.A simplified timeline
ext4_put_super()starts unmount.ext4_unregister_sysfs()deletes the kobject.sysfs_remove_dir()clears the sysfs link and releases the node.- The
update_super_workitem finally runs. ext4_notify_error_sysfs()callssysfs_notify()on an object that no longer has a validkernfs_node.
Why this is a use-after-free
The key detail is thatsysfs_notify() reaches through kobj->sd to obtain the kernfs node. Once kobject_del() and sysfs_remove_dir() have run, that pointer can be stale, and the underlying kernfs_node may already have been freed via RCU. The bug is therefore not a benign null dereference; it is a genuine UAF on freed kernel memory.That makes the vulnerability more serious than a simple cleanup bug, even if the public description does not assign a CVSS score yet. Memory safety violations in kernel teardown paths are dangerous because they can lead to crashes, data corruption, or in some cases a more exploitable primitive depending on surrounding conditions. The safest assumption is that such bugs deserve timely patching even when their exact exploitability is still under analysis.
sysfs_notify()assumes a live kobject.kobject_del()invalidates the backing sysfs state.- The worker can run after unmount has started.
- A stale
kernfs_nodecreates memory safety risk. - The race is timing-dependent, not input-dependent.
Why This Bug Matters to Administrators
For most users, ext4 is “just the filesystem,” which can make this CVE feel abstract. But filesystem bugs land squarely in the operational layer: they affect mounts, unmounts, recovery behavior, and the reliability of storage-backed services. If a production kernel can race itself into a use-after-free during teardown, the practical concern is stability first and exploitability second.Enterprise impact
In enterprise environments, this kind of bug is amplified by scale. A single unmount race might never be noticed on a test VM, but thousands of systems performing routine maintenance, crash recovery, or container churn will eventually exercise it. That is the cruel math of concurrency: the rarer the condition, the more likely fleet scale will find it.The most immediate consequences are operational, not theatrical. You can get unexpected kernel warnings, unmount instability, or failure modes that complicate incident response. If the bug intersects with error reporting or filesystems being torn down after a fault, it can also make the postmortem harder because the very path meant to report a problem becomes part of the problem.
Consumer and edge-device impact
Consumer desktops are less likely to trigger this path often, but that does not make them immune. The risk rises on devices that mount and unmount frequently, on embedded Linux systems with storage churn, or on appliances that use ext4 in automation-heavy workflows. Rare does not mean irrelevant when the bug lives in a kernel core path.Consumer impact is usually a lower-probability stability issue, while enterprise impact is a higher-probability operational issue. That distinction matters for patch priority. A home user may wait for the next routine update cycle, but an infrastructure team should treat a filesystem teardown UAF as something to verify promptly across supported kernels.
- Fleet scale turns rare races into real exposure.
- Recovery and unmount workflows are the main trigger surface.
- The bug can complicate diagnostics during an already-bad event.
- Embedded and appliance systems may be disproportionately exposed.
- Enterprise teams should verify backports, not assume them.
The Kernel Engineering Lesson
This CVE is a good example of why kernel fixes are often about preserving invariants, not just plugging holes. The earlier ext4 change solved one ordering problem by moving sysfs teardown earlier, but that altered the lifetime assumptions of another code path. In kernel work, that kind of fix can be correct and still incomplete.Lifetime checks are not optional
The fix’s use ofstate_in_sysfs is a reminder that checking object state is useful only if it is synchronized correctly. Otherwise, the code risks a TOCTOU bug where the object appears valid during the check and invalid by the time it is used. The mutex matters because it turns a best-effort check into an enforceable contract.That pattern appears across the kernel: a flag alone is not enough when multiple threads can mutate the underlying object. This is why so many memory-safety fixes end up involving some mixture of refcounting, serialization, and state validation. The architecture of the fix often tells you as much as the bug itself.
Why “just reorder it” is risky
The tempting answer to these problems is to move one cleanup call before another and hope the race disappears. But teardown code is rarely linear in practice. If any worker, notifier, or callback can still reference the object, then reordering can eliminate one race while exposing another. That is what happened here.The new patch is better because it accepts that background work may still exist and makes the notification path robust even after teardown. That is a more maintainable way to deal with concurrent unmounts, because it protects the path that is hardest to reason about: the one that can run late.
- Flags need serialization to be meaningful.
- Reordering teardown can shift, not solve, the race.
- Late-running work is the hardest path to secure.
- Small lifetime fixes often prevent large classes of bugs.
- Concurrency correctness is a security feature.
Historical Context Around Ext4 Teardown Bugs
Ext4 has a long history of careful hardening because it sits at the heart of Linux storage reliability. The existence of a CVE like this should not be read as a sign that ext4 is fragile; rather, it shows that mature code still encounters edge cases when teardown, sysfs, and workqueues interact. The more features a filesystem accumulates over time, the more these timing edges matter.Why filesystem bugs are subtle
Filesystem code is state-machine code. It tracks objects that live across I/O, metadata, error handling, crash recovery, and teardown. A bug may only surface when two correct paths run in the wrong order, which is exactly why filesystem vulnerabilities often look boring in isolation but serious in aggregate.That same pattern is why kernel maintainers are generally willing to accept extra synchronization in teardown paths if it avoids a lifetime hazard. The cost is usually a small amount of complexity or overhead; the benefit is avoiding a bug that can ruin an entire mount or reboot sequence. In storage code, correctness always outranks elegance.
What this says about ext4 maintenance
The upstream fix shows ext4 maintainers are still actively refining not only performance and correctness, but also error-reporting behavior. That matters because error-reporting paths are easy to overlook during development. They are not part of the “happy path,” yet they often run exactly when the system is least healthy and least tolerant of mistakes.This is also a reminder that sysfs is not just cosmetic. It is part of the kernel’s live object model, and tearing it down incorrectly can have real memory-safety consequences. A filesystem with sysfs hooks must treat those hooks as first-class objects with lifetimes that deserve the same discipline as the data structures that back actual I/O.
- Error-reporting paths are security-relevant.
- Filesystem teardown is a high-risk lifecycle moment.
- Sysfs objects need explicit lifetime protection.
- Mature code still needs concurrency hardening.
- Reliability fixes can be as important as feature work.
How the Fix Changes Risk
The good news is that the patch is narrow and practical. It does not redesign ext4, alter on-disk formats, or introduce broad serialization across the filesystem. Instead, it prevents a specific late notification from happening after sysfs is gone, and it synchronizes the relevant code paths so that the decision is stable. That is exactly what a good kernel security fix should do.Positive implications
The first positive is reduced crash risk during unmount and teardown stress. The second is a cleaner lifecycle boundary between ext4’s delayed work and its sysfs representation. The third is that the patch should be easy for downstream maintainers to understand and backport, because the reasoning is localized and explicit.A fourth benefit is that the fix preserves existing behavior for the normal case. If sysfs is still present, notification still happens. If it has already been torn down, the notification is safely skipped. That makes the patch less invasive than alternative approaches that would reshuffle the entire unmount sequence.
Compatibility and backporting
Because the patch is surgical, it is the kind of change vendors can usually backport without major drama. That matters in the real world, where enterprise kernels are often a mix of upstream stable branches, vendor integrations, and long-term support builds. The simpler the fix, the easier it is to verify that a distribution’s backport actually matches the upstream intent.Still, operators should not assume all ext4 kernels are immediately protected just because the CVE is public. In practice, exposure depends on whether the running kernel has the fix or a proper backport. Version verification matters more than advisory headlines.
- The patch reduces teardown-time memory safety risk.
- The normal notification path is preserved.
- The fix should backport cleanly in principle.
- Verification of vendor kernels still matters.
- Localized fixes are easier to audit than redesigns.
Competitive and Ecosystem Implications
Filesystem CVEs rarely create winners and losers in the direct sense, but they do shape trust. Ext4’s reputation is built on stability, broad deployment, and conservative engineering, so a lifecycle bug like this is mostly a reminder that even the most familiar Linux storage stack can be vulnerable in edge conditions. In the marketplace of operational confidence, trust is cumulative and fragile.Ext4 versus the rest of the stack
Operators compare ext4 not just to competitors like XFS or Btrfs, but to the broader question of how much risk they are willing to accept in the storage layer. A bug like CVE-2026-31446 does not automatically push users away from ext4, but it does reinforce the value of prompt patching and disciplined kernel maintenance. That is especially true for environments where ext4 is chosen precisely because it is expected to be boring.The ecosystem takeaway is more subtle: the Linux kernel continues to evolve through countless small correctness fixes rather than giant rewrites. That is how mature software gets safer. Each fix hardens a specific invariant, and each invariant strengthens the reliability story that administrators depend on.
Enterprise confidence and patch velocity
For enterprise buyers, the bigger signal is not that ext4 had a bug; it is that the bug is now public, understood, and fixable. That is the upside of the current disclosure model. Once a vulnerability is documented clearly, downstream vendors can align backports, and operations teams can map the fix to their own patch windows.The competitive advantage belongs to vendors and distributions that can ingest such fixes quickly and prove they did so accurately. In mixed fleets, patch velocity is part of reliability, and reliability is part of security. That is as true for a filesystem lifetime bug as it is for a flashy remote exploit.
- Operational trust matters as much as raw functionality.
- Conservative filesystems are judged on longevity and predictability.
- Public fixes help downstream vendors move faster.
- Patch velocity is a differentiator in enterprise environments.
- Small bugs can influence broader platform perception.
Strengths and Opportunities
The best thing about this fix is that it is precise. It addresses a single race window, keeps the normal path intact, and uses the right kernel primitives to serialize teardown against notification. That means administrators get a meaningful safety improvement without paying the cost of a broad architecture change.- Narrow, well-scoped remediation.
- Minimal disruption to normal ext4 behavior.
- Clear lifetime boundary for sysfs notification.
- Straightforward downstream backport potential.
- Better crash-time and unmount-time robustness.
- Strong example of disciplined kernel concurrency handling.
- Improves confidence in ext4 teardown paths.
Risks and Concerns
The main concern is that this is a memory safety bug in kernel teardown code, which is always worth treating seriously. Even if the immediate symptom is “only” a crash or instability, use-after-free bugs live in a class of issues that can be hard to reason about and harder to fully dismiss without patching.- Kernel UAFs can produce crashes or worse.
- The race is timing-based and hard to reproduce.
- Older vendor kernels may lag on backports.
- Filesystem teardown is already an error-prone path.
- The fix must be correctly backported to be effective.
- Mixed fleets can hide exposure if version tracking is weak.
- Operational incidents may be mistaken for unrelated storage flakiness.
A third concern is underestimation. Because this CVE is not a glamorous exploit chain, it would be easy to relegate it below louder issues. That would be a mistake. Reliability problems in kernel teardown can become outages, and outages are security problems when they affect availability, recovery, or the integrity of the storage stack. The absence of spectacle does not mean the absence of risk.
Looking Ahead
The next thing to watch is how quickly downstream kernels pick up the fix. For most organizations, the practical question is not the CVE record itself, but whether the exact kernel build in production contains the corrected ext4 teardown logic. That makes vendor advisories, stable backports, and distro-specific changelogs more important than the initial publication date.What administrators should verify
- Whether the running kernel includes the ext4 sysfs teardown fix.
- Whether vendor backports match the upstream intent.
- Whether container hosts, storage nodes, and appliances are covered.
- Whether regression testing includes unmount and recovery workflows.
- Whether monitoring can distinguish filesystem teardown failures from unrelated instability.
CVE-2026-31446 will not dominate headlines, but it will matter to the people who keep Linux systems healthy under load. The patch is good engineering because it respects the kernel’s concurrency model, restores the safety of sysfs notification during teardown, and avoids the temptation to solve a race with a blunt reorder that might simply move the bug elsewhere. In practical terms, that is the right outcome: a quiet fix to a quiet bug, delivered before the race becomes someone’s production incident.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center