CVE-2026-31446 is the sort of Linux kernel bug that looks deceptively narrow until you follow the race all the way through the teardown path. The flaw sits in ext4’s
The vulnerability description says the problem emerged after commit
That pattern is familiar to anyone who follows kernel security. The first fix often reveals the next edge case, because these subsystems are not linear scripts but state machines with concurrent actors, delayed work, and teardown ordering that must remain valid under stress. The published CVE record shows that the final answer was not to back away from the earlier reordering, but to make the notification path refuse to touch sysfs once teardown has begun and to serialize the two critical operations so the state cannot flip between the check and tre is also a broader lesson here about modern kernel hardening. The Linux storage stack increasingly depends on asynchronous work, sysfs metadata, and reference-counted objects that can outlive or outdie their callers in subtle ways. That makes lifetime rules as important as correctness rules, and it means that a bug can be “just” a race while still earning a CVE because the race lands in memory-safety territory.
At the center of the issue is a delayed work item named
Thacause
Why the race is realract possibility. The teardown and delayed-work lifetimes overlap by design, and the vulnerability record shows the exact window in which the stale pointer becomes reachable. The critical detail is that
The dangerous part is that the kernel usually expects teardown to be idempotent and conservative, but sysfs notifications are not no-ops if the backing object is gone. They can walk through object state that has already been invalidated, which turns a harmless-looking “notify” call into a memory-lifetime hazard. In practice, that means the bug is hard to trigger casually, but very plausible during unmount stress, error handling, or workloads that cause ext4 to emit status updates late in teardown.
A few key facts make the issue especially sensitive:
That is why
Why
That is a much cleaner answer than tryld ordering everywhere. It recognizes that a notification after sysfs removal is not useful enough to justify touching freed memory. The behavior becomes fail-quietly rather than fail-dangerously, which is exactly what shutdown code should do.
The state bit alone is not enough, though. Without synchronization, a thread could observe
The upstream response is therefore more surgical. Instead of relying on a single ordering rule, the fix imposes a runtime check and a serialization lock so the two paths cannot diverge between decision and action. That is often the most robust answer in kernel code, because teardown paths tend to accumulate future callers, and a design that depends on one exact call order is usually brittle.
This is the kind of fix that makes a subsystem more predictable without turning it into a globally looes not freeze ext4 into a single-threaded teardown model; it just ensures the error-notify path and the sysfs teardown path share a coherent view of whether the object still exists. That restraint is important, because filesystem code cannot afford to grow new serialization points casually.
It also acknowledges a deeper truth about kernel races: ordering fixes alone are fragile if other code paths can still observe half-torn-down objects. The mutex gives the state check real meaning, which is why the CVE description calls it out as protection against TOCTOU behavior rather than a cosmetic change.
This CVE also underscores how modern ext4 issues often live in the borderlands between filesystems and kernel infrastructure. A bug in sysfs teardown is still an ext4 bug if ext4 owns the object lifetime and the workqueue that reaches it. In that sense, the vulnerability is less about a filesystem algorithm failing than about ext4’s control plane failing under concurrency.
That layered evolution is healthy, even if it means the bug history looks messy in the short term. Mature codebases do not avoid edge cases; they gradually fence them off. This CVE is a good example of that process in action.
The good news is that the trigger surface is narrow. The bad news is that enterprise environments are very good at turning narrow bugs into real outages, because orchestration, failover, and image management create lots of mount and unmount churn. If a system uses ext4 heavily and its kernel is vulnerable, the risk is concentrated in maintenance windows, recovery events, and other moments when reliability matters most.
The other enterprise problem is troubleshooting. A shutdown-time use-after-free may show up as a rare crash during unmount, a puzzling kernel warning, or a failure that only appears under stress testing. Those symptoms are notoriously hard to reproduce, and that raises the cost of incident response even when the bug itself is well understood.
Embedded and appliance-style Linux systems are more exposed because they frequently run constrained workloads with long uptimes and scripted recovery sequences. In that world, teardown bugs can manifest as failed boots, slow recovery, or odd behavior after a crash. Those are not glamorous attack scenarios, but they are exactly the sort of reliability failures that make vendors scramble for patch releases.
That means appliance vendors and embedded integrators should care about this CVE even if the exploitability looks limited. A filesystem teardown race can be enough to trigger reboot loops, corrupted shutdown states, or support escalations that are much more expensive than the patch itself.
The Linux storage stack is also getting more complex across the board. Modern filesystems and kernel subsystems increasingly rely on workqueues, sysfs integration, and layered teardown semantics. That means all major filesystems face similar classes of lifetime-management risk, even if the exact bug differs. The competitive story is less “ext4 is bad” and more “all advanced filesystems live close to the edge of concurrency correctness.”
At the same time, ext4’s deep deployment base remains a major advantage. The documentation’s emphasis on ext4’s mature feature set and sysfs visibility suggests a subsystem that is heavily used, widely reviewed, and continuously maintained. That combination generally leads to faster fixes and broader backporting, which can actually make ext4 safer over time than a less scrutinized alternative.
The important nuance is that the bug does not appear to be a classic attacker-controlled overflow. Instead, it is a state-lifetime bug triggered by shutdown timing. That makes it more likely to surface as a crash or corruption issue than as a direct privilege escalation, though kernel memory-safety bugs should always be treated cautiously because their final impact can depend on surrounding conditions.
That is why the kernel has so many lifetime rules, reference counts, and state bits. The problem is not that developers ignore them; it is that concurrent shutdown paths can invalidate assumptions faster than the code evolves. A bug like this is a reminder that memory safety in the kernel is often a sequencing problem disguised as a pointer bug.
The second question is whether this bug remains an isolated teardown race or turns out to be part of a wider audit of ext4’s sysfs and workqueue interactions. The history described in the vulnerability record suggests that shutdown ordering has already required one earlier correction, so additional hardening would not be surprising. That is not a sign of collapse; it is a sign of an active subsystem being tightened where concurrency matters mostnext
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
update_super_work logic, where a work item can still call into sysfs after unmount has already torn down the kobject backing /sys/fs/ext4, creating a classic use-after-free window. The upstream fix is not a sweeping redesign; it is a careful sequencing correction that teaches ext4_notify_error_sysfs to stop calling sysfs_notify once s_kobj.state_in_sysfs says the object has already left sysfs, while a dedicated mutex closes the time-of-check/time-of-use gap described in the CVE record and Microsoft’s advisory page is one of the Linux kernel’s most important filesystems, and that matters because even small correctness bugs can become operational incidents when they strike the wrong code path at the wrong time. The Linux kernel documentation describes ext4 as a mature filesystem with a long history of scalability and reliability work, and it also notes that each mounted filesystem exposes a directory in /sys/fs/ext4, which is directly relevant to this CVE’s teardown sequence. In other words, this is not a bug in an obscure corner of the stack; it is in the plumbing that administrators and tooling rely on to introspect mounted filesystems.The vulnerability description says the problem emerged after commit
b98535d09179, which moved ext4_unregister_sysfs earlier in the unmount path to prevent new error work from being queued during teardown. That change solved one race but exposed another: update_super_work could still invoke ext4_notify_error_sysfs, which ultimately reaches sysfs_notify after the kobject’s kernfs_node has already been freed by kobject_delve_dir path. The result is a stale pointer access in a shutdown sequence that should have been boring and deterministic.That pattern is familiar to anyone who follows kernel security. The first fix often reveals the next edge case, because these subsystems are not linear scripts but state machines with concurrent actors, delayed work, and teardown ordering that must remain valid under stress. The published CVE record shows that the final answer was not to back away from the earlier reordering, but to make the notification path refuse to touch sysfs once teardown has begun and to serialize the two critical operations so the state cannot flip between the check and tre is also a broader lesson here about modern kernel hardening. The Linux storage stack increasingly depends on asynchronous work, sysfs metadata, and reference-counted objects that can outlive or outdie their callers in subtle ways. That makes lifetime rules as important as correctness rules, and it means that a bug can be “just” a race while still earning a CVE because the race lands in memory-safety territory.
 What Happened in
What Happened in update_super_work
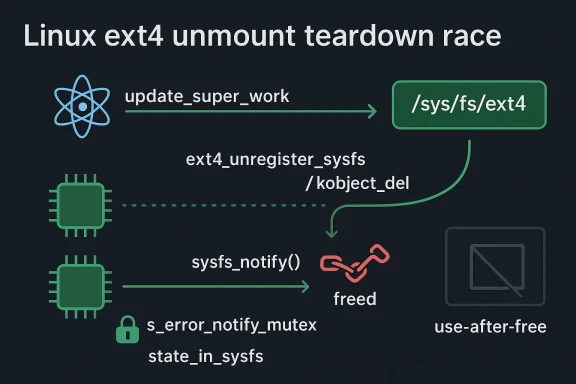
At the center of the issue is a delayed work item named update_super_work. That work item runs during ext4 shutdown and can still try to report an error through sysfs, even as the superblock is being dismantled. The vulnerability description lays out the sequence plainly: ext4_put_super calls ext4_unregister_sysfs, which invokes kobject_del(&sbi->s_kobj), removes the sysfs directory, nulls out kobj->sd, and eventually frees the kernfs_node; only later does the code reach ext4_journal_destroy and flush s_sb_upd_work.Thacause
sysfs_notify expects the kobject’s sysfs backing to still exist. When update_super_work runs late enough, it calls ext4_notify_error_sysfs(sbi), which in turn calls sysfs_notify(&sbi->s_kobj). By then, the kernel has already freed the associated kernfs_node, so the notification path dereferences a stale pointer and trips a use-after-free condition.Why the race is realract possibility. The teardown and delayed-work lifetimes overlap by design, and the vulnerability record shows the exact window in which the stale pointer becomes reachable. The critical detail is that ext4_unregister_sysfs now runs before flush_work(&sbi->s_sb_upd_work), so the work item may still fire after sysfs has been partially dismantled. That is a classic shutdown-time race: one thrent new work from being queued, while another is still allowed to execute already queued work.
The dangerous part is that the kernel usually expects teardown to be idempotent and conservative, but sysfs notifications are not no-ops if the backing object is gone. They can walk through object state that has already been invalidated, which turns a harmless-looking “notify” call into a memory-lifetime hazard. In practice, that means the bug is hard to trigger casually, but very plausible during unmount stress, error handling, or workloads that cause ext4 to emit status updates late in teardown.A few key facts make the issue especially sensitive:
update_super_workcan run after teardown has started.ext4_unregister_sysfsremoves the sysfs directory first.sysfs_notifystill assumes a livekernfs_node.- The bug is a use-after-free, not merely a lost notification.
- The race only shows up in a narrow teardown window, which is exactly why these bugs survive normal testing.
The Sysfs Lifetime Problem
The vulnerability is ultimatelme, not ext4 metadata logic. The Linux documentation makes clear that ext4 exposes per-filesystem state under/sys/fs/ext4, so the filesystem’s internal objects are tied to a sysfs representation that must be created, maintained, and destroyed in sync with mount state. If teardown gets ahead of notification, the filesystem can still believe it has a valid kobject while sysfs has already reclaimed the internal node backing it.That is why
kobject_del is such a sensitive point in the sequence. Once the object is removed from sysfs, the kernel may release the backing kernfs_node, and any later call that assumes the node remains present is on thin ice. In the CVE description, the stale pointer is specifically kobj->sd, which has been nulled and freed before sysfs_notify tries to acquire a reference again.Why state_infix hinges on a small but important state bit:s_kobj.state_in_sysfs. That flag tells the code whether the kobject is still registered in sysfs, and the patched logic uses it as a gate before attempting the notification. If sysfs teardown has already happened,ext4_notify_error_sysfssimply skipssysfs_notify` altogether.
That is a much cleaner answer than tryld ordering everywhere. It recognizes that a notification after sysfs removal is not useful enough to justify touching freed memory. The behavior becomes fail-quietly rather than fail-dangerously, which is exactly what shutdown code should do.The state bit alone is not enough, though. Without synchronization, a thread could observe
state_in_sysfs as true, then lose the race to kobject_del before the actual notify call executes. That is why the patch also introduces a dedicated mutex, s_error_notify_mutex, to serialize ext4_notify_error_sysfs against ext4_unregister_sysfs and prevent a TOCTOU race between the state check and the actual sysfs operation.Why the Fix Chose Synchronization Over Reordering
to a teardown bug is to move the cleanup later or earlier until the race disappears. That was already tried, at least partially, by commitb98535d09179, which moved sysfs teardown before flushing the workqueue to stop fresh work from being scheduled during unmount. But the CVE description makes clear that simply moving the order around is not enk item itself still retains a path back into sysfs.The upstream response is therefore more surgical. Instead of relying on a single ordering rule, the fix imposes a runtime check and a serialization lock so the two paths cannot diverge between decision and action. That is often the most robust answer in kernel code, because teardown paths tend to accumulate future callers, and a design that depends on one exact call order is usually brittle.
Why a mutex is the right tool here
The dedicateds_error_notify_mutex closes the race window that would otherwise remain even after checking state_in_sysfs. That matters because the object’s state can change between the check and the notify call if another CPU reaches the unregister path first. By serializing the notification path with kobject deletion, the kernel prevents the exact TOCTOU pattern that makes use-after-free bugs so hard to tame.This is the kind of fix that makes a subsystem more predictable without turning it into a globally looes not freeze ext4 into a single-threaded teardown model; it just ensures the error-notify path and the sysfs teardown path share a coherent view of whether the object still exists. That restraint is important, because filesystem code cannot afford to grow new serialization points casually.
What the patch avoids
The key advantage of this approach is that it avoids broad restructuring. The patch does not rewrite unmount sequencing, and it does not add new heavyweight global locks around ext4 teardown. Instead, it narrows the fix to the precise path that can still dereference sysfs state after shutdown has started. That kind of minimalism tends to backport well and reduces the risk of regressions.It also acknowledges a deeper truth about kernel races: ordering fixes alone are fragile if other code paths can still observe half-torn-down objects. The mutex gives the state check real meaning, which is why the CVE description calls it out as protection against TOCTOU behavior rather than a cosmetic change.
How This Fits the ext4 Maintenance Story
Ext4 has a long reputation for stability, but that reputation comes fromntenance rather than from being bug-free. The Linux kernel documentation emphasizes ext4’s scalability and reliability enhancements, and its general information page notes features such as journaling, mount options, and sysfs integration that all reflect the filesystem’s deep integration into the kernel’s object model. That integration is why shutdown bugs matter: the filesystem is not just writing blocks, it is managing state across multiple kernel subsystems.This CVE also underscores how modern ext4 issues often live in the borderlands between filesystems and kernel infrastructure. A bug in sysfs teardown is still an ext4 bug if ext4 owns the object lifetime and the workqueue that reaches it. In that sense, the vulnerability is less about a filesystem algorithm failing than about ext4’s control plane failing under concurrency.
Historical context
The vulnerability description explicitly points to a previous commit that attempted to fix a different unmount bug by changing the teardown order. That tells us the subsystem has been iterating on a tricky corner of its shutdown logic, which is a normal but important sign that the code path is both active and subtle. Kernel maintainers often learn these lessons in stages: first prevent queued work, then calling into dead infrastructure, then make the notification path aware that the infrastructure may already be gone.That layered evolution is healthy, even if it means the bug history looks messy in the short term. Mature codebases do not avoid edge cases; they gradually fence them off. This CVE is a good example of that process in action.
Enterprise Impact
For enterprise administrators, the main issue here is not dramatic exploitation but operational reliability. A use-after-free in a filesystem teardown path can lead to kernel crashes, hangs, or undefined behavior during unmount, especially if the affected kernel build is also exposed to heavy storage churn or automation that mounts and unmounts filesystems frequently. Those are exactly the conditions under which a rare race becomes a fleet problem rather than a lab curiosity.The good news is that the trigger surface is narrow. The bad news is that enterprise environments are very good at turning narrow bugs into real outages, because orchestration, failover, and image management create lots of mount and unmount churn. If a system uses ext4 heavily and its kernel is vulnerable, the risk is concentrated in maintenance windows, recovery events, and other moments when reliability matters most.
Why fleets feel this more than desktops
A single workstation may never hit the race. A fleet of servers, containers, or appliance nodes can hit it statistically because the shutdown path gets exercised thousands of times across the environment. That is especially true in systems that rely on frequent filesystem remounts, automated recovery, or ephemeral storage images.The other enterprise problem is troubleshooting. A shutdown-time use-after-free may show up as a rare crash during unmount, a puzzling kernel warning, or a failure that only appears under stress testing. Those symptoms are notoriously hard to reproduce, and that raises the cost of incident response even when the bug itself is well understood.
Operational takeaway
Administrators should treat this as a patch-priority reliability issue on affected kernels, especially where ext4 is used in production and unmount events are expected. It is not the kind of bug that usually screams in daily operations, but it is the kind that can surprise you during a planned reboot, failover, or cleanup task. In other words, it is a small bug with large operational consequences if left in place.Consumer and Embedded Systems
On consumer systems, the most likely symptom is a rare filesystem issue during shutdown or remount rather than a visible exploit chain. Most desktops will not constantly unmount and remount ext4 volumes in the way servers and appliances do, so the bug may never reveal itself outside of stress conditions. That said, consumers are not immune, especially on laptops and single-board systems that power off abruptly or remount external storage often.Embedded and appliance-style Linux systems are more exposed because they frequently run constrained workloads with long uptimes and scripted recovery sequences. In that world, teardown bugs can manifest as failed boots, slow recovery, or odd behavior after a crash. Those are not glamorous attack scenarios, but they are exactly the sort of reliability failures that make vendors scramble for patch releases.
Why embedded fleets should care
Embedded devices often lack the luxury of rich logging, interactive debugging, or easy patch cadence. If a filesystem bug only appears during unmount, the device may be in the field long before anyone sees the problem. When it does appear, the symptom can look like generic instability rather than a kernel defect, which makes root-cause analysis slow.That means appliance vendors and embedded integrators should care about this CVE even if the exploitability looks limited. A filesystem teardown race can be enough to trigger reboot loops, corrupted shutdown states, or support escalations that are much more expensive than the patch itself.
Consumer summary
- Most consumer systems are lower risk than fleets.
- Rare shutdown crashes are still possible on affected kernels.
- External-storage use and abrupt power loss raise the odds.
- Embedded and appliance systems deserve special attention.
- Recovery failures can look like generic instability, not a specific CVE.
Competitive and Ecosystem Implications
Ext4’s reputation is built on stability, so when a vulnerability like this appears, the impact is as much about trust as it is about code. Competing filesystems do not “win” outright because of a single ext4 bug, but every public race condition nudges procurement and operations teams to ask whether they want to stick with the default, switch to something else, or wait for the patch to land. That is a meaningful ecosystem effect, even if it does not change market share overnight.The Linux storage stack is also getting more complex across the board. Modern filesystems and kernel subsystems increasingly rely on workqueues, sysfs integration, and layered teardown semantics. That means all major filesystems face similar classes of lifetime-management risk, even if the exact bug differs. The competitive story is less “ext4 is bad” and more “all advanced filesystems live close to the edge of concurrency correctness.”
Why rivals benefit indirectly
Competing filesystems benefit because buyers often equate fewer public bug reports with lower risk. That perception is not always fair, but it is real. A serious ext4 CVE will remind conservative operators that even the most battle-tested code still needs scrutiny.At the same time, ext4’s deep deployment base remains a major advantage. The documentation’s emphasis on ext4’s mature feature set and sysfs visibility suggests a subsystem that is heavily used, widely reviewed, and continuously maintained. That combination generally leads to faster fixes and broader backporting, which can actually make ext4 safer over time than a less scrutinized alternative.
Ecosystem lessons
The broader lesson is that storage security is now as much about teardown correctness as it is about input validation. When filesystems interact with object lifetime, sysfs, delayed work, and crash recovery, the attack surface is often a race window rather than a parser bug. Those are harder to fuzz, harder to reason about, and more dependent on careful review.Technical Significance of the Use-After-Free
A use-after-free in kernel space is always serious because it means code can access memory after ownership has been revoked. In this case, the vulnerability record identifies the stale access as a freedkernfs_node reached through sysfs_notify after kobject_del has already torn down the sysfs directory. That is not just a logic error; it is a memory-saferivileged code.The important nuance is that the bug does not appear to be a classic attacker-controlled overflow. Instead, it is a state-lifetime bug triggered by shutdown timing. That makes it more likely to surface as a crash or corruption issue than as a direct privilege escalation, though kernel memory-safety bugs should always be treated cautiously because their final impact can depend on surrounding conditions.
Why these bugs are hard
The hardest part of this class of bug is that both halves of the sequence are individually reasonable.update_super_work wants to report an error. ext4_unregister_sysfs wants to tear down sysfs before new work gets queued. Each decision is defensible on its own, but together they create a tiny gap where the object is logically dead but still reachable from a delayed work item.That is why the kernel has so many lifetime rules, reference counts, and state bits. The problem is not that developers ignore them; it is that concurrent shutdown paths can invalidate assumptions faster than the code evolves. A bug like this is a reminder that memory safety in the kernel is often a sequencing problem disguised as a pointer bug.
How the fix reduces risk
The patch improves safety in two ways. First, it stops the code from notifying sysfs after teardown has already occurred by checkingstate_in_sysfs. Second, it prevents the state from flipping out from under the caller by holding s_error_notify_mutex across the decision and the action. That is a textbook example of turning a fragile lifetime assumption intoiant.Strengths and Opportunities
This fix is strong because it is narrowly targeted, easy to reason about, and aligned with the underlying lifetime rules rather than merely masking the symptom. It also gives downstream maintainers something practical to backport without rewriting the unmount sequence. In the larger picture, it shows that ext4 continues to receive the kind of careful concurrency hardening that mature kernel code needs.- The patch is surgical, not disruptive.
- It preserves existing ext4 teardown semantics where possible.
- It addresses the exact use-after-free window rather than a nearby symptom.
- It avoids a risky redesign of unmount ordering.
- The mutex makes the state check meaningful under concurrency.
- The fix should be relatively straightforward to backport.
- It demonstrates active maintenance of ext4’s sysfs integration.
Risks and Concerns
The main concern is that the bug lives in a path that may be rare in normal use but highly disruptive when triggered. Filesystem teardown failures are especially unpleasant because they often occur during shutdown, reboot, or recovery, when a system is already under pressure. If an organization relies on ext4 in automated environments, the race can become more visible than it first appears.- Affected kernels may still be exposed until vendors ship the fix.
- The bug is hard to reproduce in ordinary QA.
- Shutdown-time crashes can be mistaken for unrelated instability.
- Older stable branches may need careful backport validation.
- Systems with frequent mount/unmount cycles have more exposure.
- Recovery and support costs can be outsized compared with the code change.
- The same class of lifetime bug may exist in neighboring teardown paths.
Looking Ahead
The immediate question is how quickly the fix propagates into the kernel trees that matter most to enterprises and appliance vendors. The CVE record shows multiple stable references already attached to the issue, which is a good sign that the remediation is moving through the usual Linux distribution pipeline. For administrators, the practical task is to confirm whether the kernel they actually run incx, not merely whether a CVE exists.The second question is whether this bug remains an isolated teardown race or turns out to be part of a wider audit of ext4’s sysfs and workqueue interactions. The history described in the vulnerability record suggests that shutdown ordering has already required one earlier correction, so additional hardening would not be surprising. That is not a sign of collapse; it is a sign of an active subsystem being tightened where concurrency matters mostnext
- Stable backports landing in vendor kernels.
- Distribution advisories mapping the fix to packaged versions.
- Any follow-up ext4 patches involving sysfs teardown.
- Reports of shutdown-time crashes or mount anomalies on older kernels.
- Whether adjacent ext4 workqueue paths receive similar lifetime checks.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center