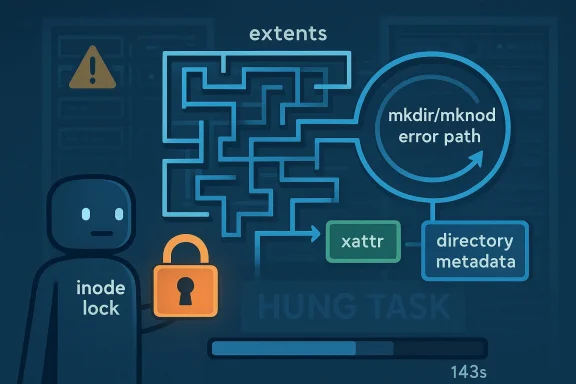
In the Linux kernel’s ext4 filesystem, a newly published vulnerability, CVE-2026-31448, exposes a failure path that can leave the filesystem spinning in an infinite loop while holding critical locks. The issue is tied to how ext4 handles extent-tree insertion failures during
What makes this bug especially notable is that it is not a simple crash or a straightforward memory corruption issue. Instead, it sits in the intersection of metadata consistency, block allocation, and xattr handling, where a single error-handling decision can ripple into lock contention and repeated retries. That makes it relevant not just to kernel developers, but to anyone running Linux servers, appliances, or virtualized workloads that depend on ext4 for their root or data volumes.
Ext4 remains one of the most widely deployed Linux filesystems because it strikes a practical balance between maturity, performance, and administrative simplicity. It is not the newest filesystem in the Linux ecosystem, but it is still the default choice in many distributions and heavily used in servers, embedded systems, and cloud images. That broad footprint is exactly why even a narrowly scoped ext4 bug deserves attention: a bug in the kernel’s filesystem core can become a fleet-wide reliability issue very quickly.
The core of this vulnerability lies in ext4’s extent tree machinery. Extents are ext4’s way of mapping logical file blocks to physical disk blocks efficiently, and that mapping logic must stay synchronized with allocation, journaling, and quota accounting. When the filesystem is creating directories or special files, the kernel has to allocate metadata blocks, update on-disk structures, and manage error paths carefully if something goes wrong.
The new CVE shows what happens when those layers lose track of one another. According to NVD’s description, if inserting a new extent fails after a physical block has already been reserved,
That stale reference creates a particularly awkward failure mode because ext4 then sees the same buffer head in two different roles at once. One side believes it is operating on directory data, while the other believes it is dealing with extended attributes. The result can be a persistent retry loop inside
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
mkdir and mknod, and it can snowball into a long-running blocked task that looks a lot like a deadlock from the outside. NVD says the flaw was published on April 22, 2026, and it traces back to kernel.org’s fix for “avoid infinite loops caused by residual data.”What makes this bug especially notable is that it is not a simple crash or a straightforward memory corruption issue. Instead, it sits in the intersection of metadata consistency, block allocation, and xattr handling, where a single error-handling decision can ripple into lock contention and repeated retries. That makes it relevant not just to kernel developers, but to anyone running Linux servers, appliances, or virtualized workloads that depend on ext4 for their root or data volumes.
 Background
Background
Ext4 remains one of the most widely deployed Linux filesystems because it strikes a practical balance between maturity, performance, and administrative simplicity. It is not the newest filesystem in the Linux ecosystem, but it is still the default choice in many distributions and heavily used in servers, embedded systems, and cloud images. That broad footprint is exactly why even a narrowly scoped ext4 bug deserves attention: a bug in the kernel’s filesystem core can become a fleet-wide reliability issue very quickly.The core of this vulnerability lies in ext4’s extent tree machinery. Extents are ext4’s way of mapping logical file blocks to physical disk blocks efficiently, and that mapping logic must stay synchronized with allocation, journaling, and quota accounting. When the filesystem is creating directories or special files, the kernel has to allocate metadata blocks, update on-disk structures, and manage error paths carefully if something goes wrong.
The new CVE shows what happens when those layers lose track of one another. According to NVD’s description, if inserting a new extent fails after a physical block has already been reserved,
ext4_ext_map_blocks may free the block but fail to delete the corresponding tree data. That leaves stale state behind, so a later mkdir can reuse a physical block number that has already been reassigned elsewhere, specifically to an xattr block.That stale reference creates a particularly awkward failure mode because ext4 then sees the same buffer head in two different roles at once. One side believes it is operating on directory data, while the other believes it is dealing with extended attributes. The result can be a persistent retry loop inside
ext4_xattr_block_set, which in turn keeps the inode lock held and blocks progress for a prolonged period. NVD’s reference to a 143-second blocked task under syzbot is a reminder that “hung task” symptoms can emerge from logic bugs just as easily as from classic deadlocks.Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center