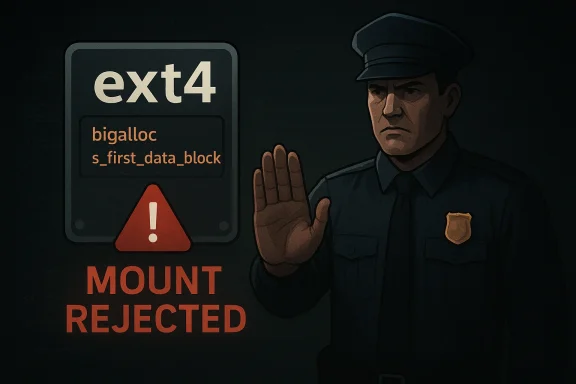
The Linux kernel has published CVE-2026-31447 for an ext4 mount-time validation flaw, and the fix is narrow but important: reject filesystems that combine bigalloc with a nonzero s_first_data_block. In plain terms, ext4 already does not support that geometry, so the kernel now refuses to mount it rather than risk undefined behavior. The upstream record ties the issue directly to the ext4 code path and notes that the affected combination should simply be blocked at mount time, which is exactly the kind of defensive hardening administrators want in a filesystem parser .
What makes this CVE noteworthy is not that it introduces a flashy exploit narrative, but that it formalizes a long-standing invariant. Filesystem code often has to distinguish between “technically parsed” and “actually supported,” and this patch moves ext4 firmly into the second camp. That matters because mount code is one of the kernel’s highest-trust inputs: if the filesystem metadata says one thing while the implementation assumes another, the result can range from denial of service to silent corruption. Here, the kernel authors chose the safest possible route—reject the mount early, before any further assumptions can be made .
ext4 remains one of the most widely deployed Linux filesystems because it is predictable, well understood, and conservative by design. It is not the most experimental option in the Linux storage stack, but that is precisely why its validation rules matter so much. Operators tend to trust ext4 precisely because it has a reputation for boring reliability, and any edge-case mount inconsistency undermines that trust in a way that is disproportionate to the size of the code change.
The specific issue behind CVE-2026-31447 concerns bigalloc, ext4’s cluster-based allocation mode, and the s_first_data_block field, which identifies the first data block on the filesystem. The vulnerability record says that the combination of bigalloc and a nonzero first data block is not supported, and the remedy is to reject mounting such a filesystem altogether . That tells us this is a format-validation defect, not a deep data-path algorithmic bug.
This sort of bug occupies an uncomfortable middle ground in kernel security. It may not look like the classic remote code execution issue that dominates headlines, but it still matters operationally because filesystems are a trust boundary. Once the kernel begins interpreting on-disk metadata, every unsupported edge case becomes a possible route to denial of service, misread structures, or recovery failure. In other words, a mount-time validation flaw can become a platform reliability problem very quickly.
The disclosure timing also matters. The CVE record was published on April 22, 2026, and the upstream reference was already attached to the record at that point. That suggests the fix had moved through the normal Linux development pipeline before the advisory appeared in the public vulnerability feed, which is the ideal sequence for a low-drama kernel hardening change. It is a reminder that many “security issues” in Linux are really consistency corrections that become security-relevant because they protect the system from invalid assumptions.
At a higher level, ext4 continues to illustrate a core truth about mature storage code: the safer the subsystem appears, the more important its invariants become. A tiny mismatch in what the filesystem claims to support can have cascading effects when operators automate image creation, provisioning, recovery, or cloning. For that reason, even a one-line mount refusal can be a meaningful security event.
This is a good example of fail closed design. Filesystem mount code has to assume that on-disk input may be malformed, inconsistent, or generated by an older tool with different assumptions. By refusing this unsupported geometry, ext4 avoids entering a state where later code paths might behave unpredictably. The fix is small, but its value is in preventing an entire class of downstream ambiguity.
From an engineering standpoint, that is preferable to trying to recover gracefully from an impossible layout. Graceful recovery is useful only when the layout is actually a tolerated variant. Here, the better choice is to abort early and surface the error to the administrator or installer.
It also improves observability. Administrators are far better served by a deterministic mount failure than by a system that appears healthy until it starts returning inconsistent I/O behavior. In practice, a clean refusal is easier to diagnose and much safer to automate around.
The key point is that cluster-based allocation introduces another layer of alignment logic. If the starting layout does not match those expectations, even a filesystem that appears readable may no longer conform to the implementation’s internal model. That is why fields like s_first_data_block are so sensitive: they define the baseline from which all later block calculations are derived.
In this case, ext4 is refusing a combination it cannot support rather than trying to treat it as a borderline case. That makes the code more predictable for both kernel developers and storage administrators. It also keeps the filesystem’s semantics honest, which is invaluable in enterprise environments that depend on reproducible behavior.
That is why Linux filesystem bugs are frequently assigned CVEs even when they do not map neatly to exploit chains. The real question is whether the defect crosses a trust boundary and can cause meaningful harm in production. Here, the answer is yes: the kernel’s mount logic is part of the trust boundary, and an unsupported ext4 geometry should never be admitted past it.
That is why the CVE label matters even for what looks like a simple validation fix. It gives operators a common tracking point and signals that the upstream project considers the issue worth structured remediation. The availability of a CVE also helps downstream vendors map the fix into their own advisory and patching systems.
Historically, filesystem bugs often came from ambiguous feature combinations rather than obvious parsing errors. The more feature flags and optional modes a filesystem accumulates, the easier it becomes for unsupported combinations to slip through. That is especially true when a format remains backward compatible across many kernel generations and toolchain versions.
This CVE is a textbook example of why mount code deserves as much scrutiny as the I/O hot path. The mount path may not process user data at line rate, but it establishes the rules everything else depends on. If those rules are wrong, the whole filesystem can be operating under a broken contract.
The effect will likely be most visible in Linux servers, storage appliances, and specialized embedded systems that rely on ext4 images created by automated pipelines. If those pipelines emit a geometry combination that ext4 now rejects, the new behavior will surface as a hard failure rather than a silent acceptance. That is a good outcome from a safety perspective, but it can still break workflows that assumed the older behavior.
In enterprise environments, the strongest response is inventory discipline. Administrators should know which systems use ext4 with bigalloc, which provisioning tools create those filesystems, and whether any older images or templates remain in circulation. That is especially important in fleets where Linux storage layouts are standardized by automation rather than hand-built.
For home users, the most likely symptom would be a mount failure after a disk image migration, firmware update, or recovery attempt. That failure might be mistaken for a corrupt filesystem or failing storage medium, when in fact the root cause is an unsupported layout combination. The fix is not to “retry harder,” but to ensure the image is generated with supported parameters.
This is where strong validation pays off. A filesystem that refuses an unsupported mount is better than one that appears to work until a later crash or reboot. On constrained devices, boot reliability is often more important than maximizing feature density, so the stricter behavior is especially appropriate.
That makes this case more akin to a policy enforcement fix than a classic vulnerability chain. The kernel is not stopping an attacker from exploiting a buffer overflow; it is preventing itself from accepting an unsupported state. That distinction is important, but it should not lead anyone to dismiss the fix as minor.
This matters because kernel changes that touch mount behavior can be risky if they are broad or speculative. A narrow rejection condition is far easier to reason about than a wide-reaching rework of the filesystem’s allocation logic. It also makes downstream QA more manageable.
That kind of discipline pays off in both security and operations. It reduces ambiguity, improves error handling, and gives downstream maintainers a clear rule to backport. It also reinforces the idea that kernel hardening is often about saying “no” earlier and more cleanly.
There is also a documentation risk. If operators are not aware that bigalloc and nonzero s_first_data_block are incompatible, they may misdiagnose the failure as media corruption or a kernel regression. That is why clear vendor advisories and good release notes matter. In filesystem work, the line between “security fix” and “support boundary correction” is often very thin.
It will also be worth watching whether the ext4 maintainers use this case to tighten any adjacent mount-time checks. Small validation fixes often lead to a broader audit of neighboring invariants, especially in mature filesystems where many assumptions were historically encoded in tooling rather than in kernel-side guards. That kind of follow-on hardening is usually a good sign.
CVE-2026-31447 is a small patch with a large lesson: the safest filesystem is the one that refuses to pretend an unsupported state is acceptable. That principle is unglamorous, but in kernel work it is often the difference between a clean failure and a long, expensive recovery problem.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
What makes this CVE noteworthy is not that it introduces a flashy exploit narrative, but that it formalizes a long-standing invariant. Filesystem code often has to distinguish between “technically parsed” and “actually supported,” and this patch moves ext4 firmly into the second camp. That matters because mount code is one of the kernel’s highest-trust inputs: if the filesystem metadata says one thing while the implementation assumes another, the result can range from denial of service to silent corruption. Here, the kernel authors chose the safest possible route—reject the mount early, before any further assumptions can be made .
 Background
Background
ext4 remains one of the most widely deployed Linux filesystems because it is predictable, well understood, and conservative by design. It is not the most experimental option in the Linux storage stack, but that is precisely why its validation rules matter so much. Operators tend to trust ext4 precisely because it has a reputation for boring reliability, and any edge-case mount inconsistency undermines that trust in a way that is disproportionate to the size of the code change.The specific issue behind CVE-2026-31447 concerns bigalloc, ext4’s cluster-based allocation mode, and the s_first_data_block field, which identifies the first data block on the filesystem. The vulnerability record says that the combination of bigalloc and a nonzero first data block is not supported, and the remedy is to reject mounting such a filesystem altogether . That tells us this is a format-validation defect, not a deep data-path algorithmic bug.
This sort of bug occupies an uncomfortable middle ground in kernel security. It may not look like the classic remote code execution issue that dominates headlines, but it still matters operationally because filesystems are a trust boundary. Once the kernel begins interpreting on-disk metadata, every unsupported edge case becomes a possible route to denial of service, misread structures, or recovery failure. In other words, a mount-time validation flaw can become a platform reliability problem very quickly.
The disclosure timing also matters. The CVE record was published on April 22, 2026, and the upstream reference was already attached to the record at that point. That suggests the fix had moved through the normal Linux development pipeline before the advisory appeared in the public vulnerability feed, which is the ideal sequence for a low-drama kernel hardening change. It is a reminder that many “security issues” in Linux are really consistency corrections that become security-relevant because they protect the system from invalid assumptions.
At a higher level, ext4 continues to illustrate a core truth about mature storage code: the safer the subsystem appears, the more important its invariants become. A tiny mismatch in what the filesystem claims to support can have cascading effects when operators automate image creation, provisioning, recovery, or cloning. For that reason, even a one-line mount refusal can be a meaningful security event.
What CVE-2026-31447 Changes
The direct behavioral change is simple: if ext4 sees bigalloc together with s_first_data_block != 0, it now rejects the mount instead of proceeding. That is a classic kernel hardening pattern. Rather than trying to reinterpret the metadata or guess the administrator’s intent, the code draws a clean boundary around unsupported state and refuses to continue.This is a good example of fail closed design. Filesystem mount code has to assume that on-disk input may be malformed, inconsistent, or generated by an older tool with different assumptions. By refusing this unsupported geometry, ext4 avoids entering a state where later code paths might behave unpredictably. The fix is small, but its value is in preventing an entire class of downstream ambiguity.
Why the combination is invalid
The record is explicit that bigalloc with s_first_data_block != 0 is not supported . That means the vulnerability is not about a rare arithmetic bug in one helper function. It is about a filesystem configuration that should never have been treated as valid in the first place. The kernel’s new behavior aligns the implementation with the real support matrix.From an engineering standpoint, that is preferable to trying to recover gracefully from an impossible layout. Graceful recovery is useful only when the layout is actually a tolerated variant. Here, the better choice is to abort early and surface the error to the administrator or installer.
Why mount-time rejection is the right fix
Mount-time rejection is effective because it prevents invalid metadata from propagating deeper into the filesystem stack. Once the kernel mounts a filesystem, it may cache assumptions about allocation, block mapping, and feature compatibility. If those assumptions are wrong, the bug can show up much later in a harder-to-debug form. Early rejection reduces that blast radius.It also improves observability. Administrators are far better served by a deterministic mount failure than by a system that appears healthy until it starts returning inconsistent I/O behavior. In practice, a clean refusal is easier to diagnose and much safer to automate around.
- It preserves the filesystem’s documented support boundaries.
- It prevents invalid combinations from reaching later code paths.
- It reduces the risk of subtle corruption or recovery problems.
- It makes provisioning failures obvious instead of latent.
- It supports safer backporting because the change is narrow and local.
Understanding ext4 bigalloc
Bigalloc is ext4’s cluster-based allocation mode, designed to reduce metadata overhead on some storage workloads by allocating in larger chunks than traditional block-by-block ext4 behavior. That can be useful on flash-heavy or large-volume systems where allocation efficiency matters more than fine-grained packing. But it also means the filesystem has stricter geometry assumptions.The key point is that cluster-based allocation introduces another layer of alignment logic. If the starting layout does not match those expectations, even a filesystem that appears readable may no longer conform to the implementation’s internal model. That is why fields like s_first_data_block are so sensitive: they define the baseline from which all later block calculations are derived.
Why geometry matters so much
Filesystem geometry is not cosmetic. It determines how the kernel interprets every metadata pointer, every inode location, and every allocation decision. When a geometry field is off, the problem can remain hidden until the system needs to allocate, recover, or replay metadata under pressure. That is one reason mount-time validation is critical.In this case, ext4 is refusing a combination it cannot support rather than trying to treat it as a borderline case. That makes the code more predictable for both kernel developers and storage administrators. It also keeps the filesystem’s semantics honest, which is invaluable in enterprise environments that depend on reproducible behavior.
Bigalloc in practice
Bigalloc is often chosen for specialized deployments rather than general-purpose desktop systems. That means the affected population is likely narrower than for a ubiquitous parser bug, but the operational stakes can still be high. Specialized storage layouts are exactly where unsupported combinations sneak in through imaging tools, automation scripts, or vendor customization.- Clustered allocation can improve metadata efficiency.
- It can also increase the consequences of geometry mismatches.
- Hidden layout assumptions are especially dangerous in automated provisioning.
- Recovery paths are usually less forgiving than normal mounting.
- Unsupported modes are best rejected before they are trusted.
Why This Became a CVE
At first glance, this looks like a correctness patch rather than a security issue. But that distinction is often misleading in kernel space. If invalid filesystem metadata can cause the kernel to mount an unsupported configuration, the result can become a denial-of-service condition, a recovery failure, or a corruption path that affects the trustworthiness of the entire volume.That is why Linux filesystem bugs are frequently assigned CVEs even when they do not map neatly to exploit chains. The real question is whether the defect crosses a trust boundary and can cause meaningful harm in production. Here, the answer is yes: the kernel’s mount logic is part of the trust boundary, and an unsupported ext4 geometry should never be admitted past it.
Security versus stability
A lot of administrators instinctively separate “security bugs” from “stability bugs,” but kernel maintainers increasingly treat those categories as overlapping. If a mount can be coerced into an unsupported state, then the consequences are not limited to a crash log. The filesystem can poison recovery behavior, confuse automation, or create inconsistent I/O assumptions that linger long after the original mount.That is why the CVE label matters even for what looks like a simple validation fix. It gives operators a common tracking point and signals that the upstream project considers the issue worth structured remediation. The availability of a CVE also helps downstream vendors map the fix into their own advisory and patching systems.
The operational risk profile
The practical risk here is likely concentrated in systems that use custom ext4 provisioning, older tooling, or image pipelines that may have produced unsupported layouts without triggering obvious errors. Most users will never encounter this state manually, but the dangerous cases are often the ones introduced indirectly. Automation is excellent at reproducing mistakes at scale.- Image builders may propagate bad geometry silently.
- Older installers may not validate the combination consistently.
- Recovery workflows may encounter the issue only after a failure.
- Mixed fleets can hide the problem until a rare mount event.
- Appliance-style Linux systems may expose the issue more often than general-purpose desktops.
Historical Context Around ext4 Validation
ext4’s design philosophy has always leaned toward robust, conservative validation. That history matters because it means changes like this are not random course corrections; they are part of the filesystem’s long-running effort to keep unsupported states out of the kernel’s active data structures. As ext4 gained features over time, the validation logic had to become more explicit, not less.Historically, filesystem bugs often came from ambiguous feature combinations rather than obvious parsing errors. The more feature flags and optional modes a filesystem accumulates, the easier it becomes for unsupported combinations to slip through. That is especially true when a format remains backward compatible across many kernel generations and toolchain versions.
The role of mount-time checks
Mount-time checks are ext4’s first line of defense against impossible layouts. They matter because many later invariants assume the mount has already filtered out incompatible states. If the initial gate is too permissive, all subsequent code starts from a false premise. That is how small validation errors become deeper operational problems.This CVE is a textbook example of why mount code deserves as much scrutiny as the I/O hot path. The mount path may not process user data at line rate, but it establishes the rules everything else depends on. If those rules are wrong, the whole filesystem can be operating under a broken contract.
Why this kind of bug slips through
Format-validation bugs often survive testing because they require a very specific on-disk combination to trigger. In a lab, that combination may not appear unless someone intentionally constructs it. In the field, it may be introduced by migration tooling, vendor images, or recovery from older environments. That makes reproduction and detection harder than for ordinary runtime failures.- Invalid combinations are often rare and environment-specific.
- Automated tests may cover common layouts but miss edge cases.
- Tooling can create unsupported states without obvious symptoms.
- The mount code may not exercise the bad path until deployment.
- Administrators may misattribute the failure to hardware or media damage.
Enterprise Impact
For enterprise administrators, the biggest takeaway is that CVE-2026-31447 is a reliability and supportability issue first, and a security issue second. That does not make it less important. In real-world production environments, a mount refusal on critical storage can be just as disruptive as a more dramatic exploit, especially when it blocks boot, recovery, or storage provisioning.The effect will likely be most visible in Linux servers, storage appliances, and specialized embedded systems that rely on ext4 images created by automated pipelines. If those pipelines emit a geometry combination that ext4 now rejects, the new behavior will surface as a hard failure rather than a silent acceptance. That is a good outcome from a safety perspective, but it can still break workflows that assumed the older behavior.
What administrators should care about
The practical concern is not just whether a kernel is “vulnerable” in the abstract. It is whether the organization has any image, volume, or recovery process that could produce the unsupported combination. If so, the new rejection behavior is both a safeguard and a signal that some provisioning assumptions need to be revisited.In enterprise environments, the strongest response is inventory discipline. Administrators should know which systems use ext4 with bigalloc, which provisioning tools create those filesystems, and whether any older images or templates remain in circulation. That is especially important in fleets where Linux storage layouts are standardized by automation rather than hand-built.
Why mixed fleets complicate response
Mixed environments complicate even simple kernel fixes because different vendors and distributions backport patches on different schedules. The ext4 code itself may be straightforward, but the operational question is whether the build running on a given server includes the new rejection logic. Assuming that a CVE has been fixed everywhere just because it appears in an advisory is a common mistake.- Verify the actual kernel build, not just the distribution version.
- Check whether custom images use ext4 bigalloc at all.
- Review installation and recovery pipelines for unsupported layouts.
- Coordinate patch timing across vendors and branches.
- Treat mount refusals as configuration signals, not random failures.
Consumer and Edge Device Impact
Consumer desktops are less likely to be affected than enterprise storage systems, mainly because most users never intentionally enable ext4 bigalloc. Still, consumer and edge devices are not immune. Many embedded Linux products use tailored filesystem images and custom provisioning logic that can drift from upstream assumptions over time. That is where a mount validation issue can become a field problem.For home users, the most likely symptom would be a mount failure after a disk image migration, firmware update, or recovery attempt. That failure might be mistaken for a corrupt filesystem or failing storage medium, when in fact the root cause is an unsupported layout combination. The fix is not to “retry harder,” but to ensure the image is generated with supported parameters.
Why edge devices deserve attention
Edge and appliance deployments often have the worst of both worlds: they are built from Linux components, but they are maintained with the care of embedded products rather than general-purpose servers. That means filesystem choices are frequently locked in early, and update cycles are slower. In those settings, a mount rejection can become a support ticket that is difficult to diagnose remotely.This is where strong validation pays off. A filesystem that refuses an unsupported mount is better than one that appears to work until a later crash or reboot. On constrained devices, boot reliability is often more important than maximizing feature density, so the stricter behavior is especially appropriate.
What the user experience looks like
Most consumers will never notice this CVE directly, but the few who do may see confusing symptoms. A device may boot until a filesystem check or remount occurs, then refuse to continue. Alternatively, a migration tool may complete successfully only for the next boot to fail during storage initialization. Those are frustrating failure modes, but they are far easier to fix when the kernel surfaces them early.- The issue is likely invisible to most standard desktop users.
- Custom images and appliance systems are the more realistic exposure.
- The failure mode is a clear mount rejection, not silent corruption.
- Diagnostic logs should help distinguish invalid layout from media failure.
- Recovery tools should be checked for compatibility with the new rule.
How This Differs From Other Linux Kernel CVEs
Not every kernel CVE is about memory safety, privilege escalation, or network attack surface. CVE-2026-31447 is a good reminder that filesystem validation bugs are often about correctness first and security second. Yet they still matter because the kernel is responsible for deciding whether on-disk data can be trusted.That makes this case more akin to a policy enforcement fix than a classic vulnerability chain. The kernel is not stopping an attacker from exploiting a buffer overflow; it is preventing itself from accepting an unsupported state. That distinction is important, but it should not lead anyone to dismiss the fix as minor.
The value of narrow fixes
The best kernel security fixes are often the most boring ones. They refuse bad input, tighten assumptions, and leave the happy path alone. That is exactly what ext4 is doing here. The more surgical the fix, the lower the regression risk and the easier it is to backport across supported branches.This matters because kernel changes that touch mount behavior can be risky if they are broad or speculative. A narrow rejection condition is far easier to reason about than a wide-reaching rework of the filesystem’s allocation logic. It also makes downstream QA more manageable.
Why the CVE label still matters
A CVE gives the issue a stable identifier across vendors, distributions, and tracking systems. That is especially useful for enterprise environments where Linux security changes are often monitored alongside Windows and cloud infrastructure advisories. The CVE number becomes a practical coordination tool, not just a record entry.- It standardizes issue tracking across fleets.
- It helps vendors map fixes into support channels.
- It lets administrators search advisories quickly.
- It improves audit and compliance reporting.
- It reduces ambiguity when multiple kernel branches are involved.
Strengths and Opportunities
The strongest aspect of this fix is its restraint. It does not try to reinterpret an unsupported filesystem layout, and it does not create new complexity in the mount path. Instead, it codifies an existing support boundary and makes ext4’s behavior more predictable for everyone who depends on it.That kind of discipline pays off in both security and operations. It reduces ambiguity, improves error handling, and gives downstream maintainers a clear rule to backport. It also reinforces the idea that kernel hardening is often about saying “no” earlier and more cleanly.
- Clear and narrow remediation.
- Low conceptual risk compared with a broader redesign.
- Strong alignment with ext4’s documented support model.
- Easier to backport than a structural storage change.
- Better diagnostics for administrators and tooling.
- Reduced chance of latent recovery issues.
- Reinforces trust in ext4 mount behavior.
Risks and Concerns
The main concern is that unsupported filesystem layouts can be introduced indirectly, especially by automation or older provisioning pipelines. If a system has been quietly relying on an invalid ext4 geometry, the new mount rejection may look like a regression even though it is really exposing a preexisting mismatch. That can create confusion during updates or recovery events.There is also a documentation risk. If operators are not aware that bigalloc and nonzero s_first_data_block are incompatible, they may misdiagnose the failure as media corruption or a kernel regression. That is why clear vendor advisories and good release notes matter. In filesystem work, the line between “security fix” and “support boundary correction” is often very thin.
- Legacy images may contain unsupported layouts.
- Automated provisioning may propagate the bad combination.
- Mount failures can be misread as disk damage.
- Mixed fleets may update at different times.
- Recovery workflows may need to be revalidated.
- Vendor backports may differ slightly across branches.
- Poor documentation can turn a clean fix into an operational headache.
Looking Ahead
The immediate thing to watch is downstream uptake. Since the upstream fix is already recorded alongside the CVE, the next question is how quickly distribution kernels and vendor-supported branches carry the rejection logic into production. For most users, that will matter more than the publication date of the CVE itself.It will also be worth watching whether the ext4 maintainers use this case to tighten any adjacent mount-time checks. Small validation fixes often lead to a broader audit of neighboring invariants, especially in mature filesystems where many assumptions were historically encoded in tooling rather than in kernel-side guards. That kind of follow-on hardening is usually a good sign.
What administrators should monitor
- Kernel releases that backport the ext4 rejection check.
- Vendor advisories describing affected image or mount workflows.
- Internal provisioning templates that use ext4 bigalloc.
- Recovery tooling that may encounter the unsupported geometry.
- Fleet logs for repeated mount refusals on the same volumes.
CVE-2026-31447 is a small patch with a large lesson: the safest filesystem is the one that refuses to pretend an unsupported state is acceptable. That principle is unglamorous, but in kernel work it is often the difference between a clean failure and a long, expensive recovery problem.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center