Linux administrators received a fresh reminder this week that ext4’s maturity does not make it immune to memory-safety bugs. CVE-2026-31449 is a slab-out-of-bounds read in the Linux kernel’s ext4 extent-tree logic, and it appears in a code path that corrects index entries after leaf extents are modified. The flaw is narrow in scope, but the fix matters because it closes a gap where a corrupted or crafted on-disk extent header could push an index pointer beyond the valid range and let the kernel read past the end of an allocated buffer.
What makes this bug notable is not only the technical detail, but the pattern it reinforces: filesystem code tends to be robust on healthy media and far less forgiving when metadata is hostile. The published description says the upstream remedy is to validate the index pointer against
ext4 remains one of the most widely deployed Linux filesystems, especially in general-purpose servers, virtual machines, removable media, and consumer Linux distributions. Its longevity comes from a combination of stability, performance, and compatibility, but those same strengths create a large attack surface. Any parser that interprets on-disk metadata has to assume that the metadata may be incomplete, corrupted, or deliberately malicious, and that assumption becomes critical whenever the kernel walks trees or follows pointers derived from disk content.
The new CVE fits into a long line of ext4 hardening work. The filesystem’s extent tree code is designed to keep logical file ranges mapped efficiently to physical blocks, but the logic also has to recover and “correct” metadata when a leaf changes. That recovery path is exactly where this issue lives. A pointer named
That kind of bug is dangerous even when it is only a read. A slab-out-of-bounds read does not immediately imply code execution, but in kernel space it can leak adjacent memory, trigger crashes, or destabilize the filesystem in ways that are hard to reproduce. In practice, even a “mere” read can become a stepping stone for more serious exploitation if it helps an attacker learn kernel layout or corrupt internal state through follow-on effects.
The kernel community has increasingly treated this class of issue as corruption handling rather than normal error recovery. That distinction matters. If the extent tree is compromised enough that a pointer has wandered outside the valid range, the safe response is to stop, report corruption, and avoid making the situation worse. In that sense,
The kernel description says the fix validates
This is why ext4 hardening keeps returning to the same theme: validate first, then trust. The published fix reflects that philosophy by making the boundary check explicit and by harmonizing the failure mode with the rest of the extent-tree code. That consistency matters because inconsistent error handling is often where later bugs hide.
The new CVE suggests that the code assumed
That approach is conservative, and in kernel code conservative is good. It avoids depending on the optimism of earlier code paths and lowers the chance that a later refactor turns one checked access back into an unchecked one. It also gives maintainers a clearer template for future extent-tree work.
The likely practical impact here depends on the exact deployment. On a workstation with a local user mounting a known-good filesystem, the risk may be lower than in a server that mounts untrusted images or ingests uploaded disk artifacts. On appliances and recovery tools, the threat rises again because those systems are often expected to open foreign media.
Why
The value of this response is partly psychological and partly technical. It nudges upper layers toward conservative handling and avoids masking the root cause. It also helps maintain a consistent corruption model across ext4, which makes later debugging and auditing easier.
That is especially true for enterprise Linux vendors and cloud images, where the kernel is both a security boundary and a support boundary. A filesystem CVE can force a reboot, a maintenance window, or a live-patching decision even when there is no public exploitation. Those operational costs are part of the real-world impact.
The pattern also shows why filesystem maintainers favor explicit checks over “reasonable assumptions.” Disk data can be damaged by power loss, buggy firmware, bad sectors, or deliberate fuzzing. A filesystem that survives in that environment must be relentlessly defensive, even if the performance cost is a few extra comparisons.
The operational issue is not just exploitation. A malformed volume that triggers repeated kernel errors can interrupt jobs, complicate incident response, and degrade confidence in the storage stack. That can force administrators to isolate systems or suspend workflows while patches roll out.
This is one reason Microsoft’s own Linux-facing documentation keeps reiterating CVE scanning and patch workflows in Azure Linux and SQL Server on Linux contexts. Microsoft notes that Azure Linux scans for vulnerabilities twice a day and treats high and critical CVEs with special urgency, while SQL Server on Linux guidance continues to list ext4 and XFS as supported filesystems on current Linux platforms. That broader ecosystem context shows how quickly a kernel filesystem issue can surface in enterprise support planning.
The real risk is not the default desktop mount path alone, but the growing number of places where ext4 data is ingested from outside the device. That includes backups, sync tools, and vendor update workflows. Every extra mount point is another possible path into the kernel parser.
It also reinforces the kernel’s preference for making corruption obvious. A filesystem that keeps marching after invalid metadata is often the one that later suffers deeper data loss. Stopping early is usually the safer choice, even if it inconveniences the mount or the caller.
For security operations teams, that creates a familiar but unavoidable burden. Kernel CVEs are not purely theoretical, because they almost always map to actual release engineering work. The older the fleet, the more likely it is that some systems need manual validation or a reboot schedule.
The second question is whether this CVE prompts more scrutiny of other extent-tree paths. That would be healthy. Bugs like this tend to cluster around the same design pressure points: metadata trust, pointer range checks, and recovery code that assumes too much about the shape of corrupted trees. The lesson for maintainers is not to panic, but to keep hardening the parser with the same discipline that fixed this issue.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
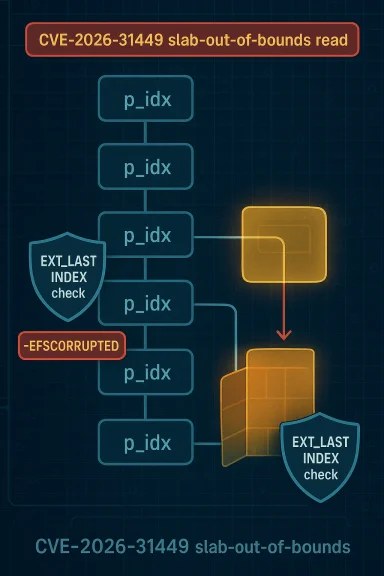
What makes this bug notable is not only the technical detail, but the pattern it reinforces: filesystem code tends to be robust on healthy media and far less forgiving when metadata is hostile. The published description says the upstream remedy is to validate the index pointer against
EXT_LAST_INDEX at two access points and return -EFSCORRUPTED when the pointer is out of bounds, aligning the behavior with other ext4 bounds checks. That is the kind of fix that looks small in a diff but is large in consequence, because it changes a dangerous undefined read into an explicit corruption error.
 Overview
Overview
ext4 remains one of the most widely deployed Linux filesystems, especially in general-purpose servers, virtual machines, removable media, and consumer Linux distributions. Its longevity comes from a combination of stability, performance, and compatibility, but those same strengths create a large attack surface. Any parser that interprets on-disk metadata has to assume that the metadata may be incomplete, corrupted, or deliberately malicious, and that assumption becomes critical whenever the kernel walks trees or follows pointers derived from disk content.The new CVE fits into a long line of ext4 hardening work. The filesystem’s extent tree code is designed to keep logical file ranges mapped efficiently to physical blocks, but the logic also has to recover and “correct” metadata when a leaf changes. That recovery path is exactly where this issue lives. A pointer named
p_idx is used while walking upward through the extent tree, and the description indicates there was no validation that it remained within the valid index range before dereferencing path[k].p_idx->ei_block.That kind of bug is dangerous even when it is only a read. A slab-out-of-bounds read does not immediately imply code execution, but in kernel space it can leak adjacent memory, trigger crashes, or destabilize the filesystem in ways that are hard to reproduce. In practice, even a “mere” read can become a stepping stone for more serious exploitation if it helps an attacker learn kernel layout or corrupt internal state through follow-on effects.
The kernel community has increasingly treated this class of issue as corruption handling rather than normal error recovery. That distinction matters. If the extent tree is compromised enough that a pointer has wandered outside the valid range, the safe response is to stop, report corruption, and avoid making the situation worse. In that sense,
-EFSCORRUPTED is not just an error code; it is a policy decision about preserving the integrity of the rest of the filesystem.What CVE-2026-31449 Actually Affects
At a technical level, CVE-2026-31449 affectsext4_ext_correct_indexes, a helper that walks up the extent tree after the first extent in a leaf is modified. The vulnerable behavior appears when the code accesses path[k].p_idx->ei_block without first proving that p_idx still points to a legitimate index entry for that tree level. If the header’s eh_entries value is corrupted or crafted, the pointer can step beyond the allocated buffer.Why the pointer matters
Extent trees are not ordinary arrays in the developer’s mental model, but they behave like one when the kernel iterates through index entries. A single off-by-range mistake in such code can push the kernel beyond the object boundary and into adjacent slab memory. That is especially concerning in filesystem paths, where the input is not an API call alone but a combination of syscalls, block contents, mount state, and delayed metadata updates.The kernel description says the fix validates
path[k].p_idx against EXT_LAST_INDEX at both access sites: before the loop and inside it. That means the defensive check is placed where the code can actually use it, rather than relying on earlier assumptions that might no longer hold by the time the loop iterates again. It is a small change in structure, but a meaningful change in trust boundaries.- The vulnerable site is in the extent index correction path.
- The out-of-bounds condition depends on corrupted or crafted extent metadata.
- The observed failure mode is a slab-out-of-bounds read.
- The fix is to perform range validation before each dereference.
- The error returned is
-EFSCORRUPTED, not silent recovery.
The role of crafted ext4 images
Filesystem bugs often become security bugs because the kernel must parse untrusted data at privilege level. A crafted ext4 image can present the kernel with extent headers that appear structurally plausible while hiding invalid values in specific fields. If validation is incomplete, the kernel may follow a pointer that should have been rejected long before dereference.This is why ext4 hardening keeps returning to the same theme: validate first, then trust. The published fix reflects that philosophy by making the boundary check explicit and by harmonizing the failure mode with the rest of the extent-tree code. That consistency matters because inconsistent error handling is often where later bugs hide.
How the Extent Tree Logic Breaks Down
The ext4 extent tree is built for scale. It allows a file to map large contiguous ranges of blocks efficiently, which is far better than a fragmented indirect-block scheme for modern storage workloads. But the same tree structure that improves performance also creates multiple levels of parent/child relationships, and every level introduces another place where pointer arithmetic can go wrong.Walking upward after a leaf change
ext4_ext_correct_indexes runs when the first extent in a leaf changes and the tree above it may need to be updated. In other words, the function is part of the logic that keeps parent index blocks in sync with leaf contents. That sounds mundane, but metadata synchronization is one of the kernel’s most sensitive jobs because the code is simultaneously preserving consistency and interpreting disk-backed state.The new CVE suggests that the code assumed
p_idx was valid simply because the surrounding extent structures looked valid. That assumption is fragile. If eh_entries is corrupted, the iteration count can be wrong even if the structure’s outer shell still looks reasonable. A stale or bad index pointer then becomes a memory boundary issue instead of a normal metadata mismatch.Why boundary checks need to be repeated
A common mistake in low-level code is to validate a pointer once and then assume it stays valid throughout the loop. That assumption is often wrong when the loop condition itself depends on mutable metadata or when nested structure state can be re-evaluated. Here, the fix reportedly adds validation both before the while loop and inside it, which signals that the author recognized the need to defend every dereference.That approach is conservative, and in kernel code conservative is good. It avoids depending on the optimism of earlier code paths and lowers the chance that a later refactor turns one checked access back into an unchecked one. It also gives maintainers a clearer template for future extent-tree work.
- Repeated checks reduce reliance on stale assumptions.
- Corrupted metadata can affect both loop bounds and pointer range.
- Defensive validation is especially important in tree-walking code.
- The fix aligns with ext4’s broader corruption-first behavior.
- Multiple checks help future-proof the code against refactoring mistakes.
Why a Read Bug Still Matters
Security reporting sometimes makes readers overfocus on write primitives because writes are easier to associate with direct corruption or code execution. But read bugs in the kernel are still serious. They can disclose memory, alter control flow indirectly, or destabilize core subsystems through unexpected data dependencies. In filesystem code, an out-of-bounds read can also expose adjacent slab contents that belong to unrelated kernel objects.Information exposure and kernel layout
A slab-out-of-bounds read can reveal bytes that were never meant to leave kernel memory. On modern systems that may include object fields, allocator metadata, or remnants of previous work. Even when the leak is small, it can undermine defenses that depend on memory secrecy. That is why “read only” should not be mistaken for “low risk.”The likely practical impact here depends on the exact deployment. On a workstation with a local user mounting a known-good filesystem, the risk may be lower than in a server that mounts untrusted images or ingests uploaded disk artifacts. On appliances and recovery tools, the threat rises again because those systems are often expected to open foreign media.
Crash risk and operational disruption
Even if an attacker cannot turn the bug into a dependable leak, the read can still provoke a kernel fault or corrupt follow-up logic. Filesystem code is especially sensitive to such failures because a single bad mount can affect boot, data availability, or backup operations. In enterprise environments, that can quickly become a service-impacting event rather than a narrow security incident.- Kernel reads are not harmless just because they do not overwrite memory.
- The bug could support information disclosure.
- The bug could also contribute to denial of service.
- Mounting untrusted ext4 images increases exposure.
- Recovery and forensics workflows are often the most exposed use cases.
The Fix and Its Design Choices
The published description says the solution is to checkp_idx against EXT_LAST_INDEX at both access sites and return -EFSCORRUPTED if the pointer is out of range. That is a classic kernel-hardening move: make invalid state explicit, fail closed, and avoid letting the code continue in a partially trusted condition.Why -EFSCORRUPTED is the right response
-EFSCORRUPTED tells callers that the underlying filesystem metadata is not trustworthy. That matters because many kernel filesystem helpers distinguish between ordinary I/O failures and semantic corruption. If a block cannot be read because of a transient storage issue, recovery may still be possible. If the extent tree itself is malformed, continuing is often the wrong decision.The value of this response is partly psychological and partly technical. It nudges upper layers toward conservative handling and avoids masking the root cause. It also helps maintain a consistent corruption model across ext4, which makes later debugging and auditing easier.
Why this is more than a local patch
A fix like this tends to ripple outward. Distribution kernels may backport it to supported stable lines, security scanners may start matching it to advisories, and support teams may update their guidance for systems that mount untrusted media. The exact blast radius depends on kernel version and vendor packaging, but the pattern is familiar: a one-function fix in upstream Linux becomes a fleet-wide maintenance issue downstream.That is especially true for enterprise Linux vendors and cloud images, where the kernel is both a security boundary and a support boundary. A filesystem CVE can force a reboot, a maintenance window, or a live-patching decision even when there is no public exploitation. Those operational costs are part of the real-world impact.
- The fix changes unsafe reads into explicit corruption errors.
- It supports defense in depth by refusing to trust invalid metadata.
- It is likely to be backported into stable kernels.
- It may affect live patching and reboot scheduling.
- It simplifies incident triage for support teams.
How this compares with prior ext4 hardening
ext4 has seen numerous correctness and security fixes over the years, many of them focused on boundary validation and metadata consistency. That is not evidence of a broken filesystem; it is evidence of a heavily used one. Whenever a subsystem is trusted to parse disk state at scale, the security bar rises with deployment volume.The pattern also shows why filesystem maintainers favor explicit checks over “reasonable assumptions.” Disk data can be damaged by power loss, buggy firmware, bad sectors, or deliberate fuzzing. A filesystem that survives in that environment must be relentlessly defensive, even if the performance cost is a few extra comparisons.
Enterprise, Cloud, and Consumer Impact
The practical impact of CVE-2026-31449 differs by environment. A consumer laptop may encounter ext4 only on its root partition and a handful of removable devices, while an enterprise server may mount dozens of volumes, snapshots, images, and containers. Cloud and virtualization layers complicate this further because an image can be untrusted even if the host OS itself is well managed.Enterprise servers
Enterprise environments are often the most sensitive to filesystem bugs because they store important state and frequently automate mounting behavior. Backup servers, forensic workstations, CI systems, and virtualization hosts all routinely process disk images that originate outside the local trust boundary. In those contexts, even a read bug can become a security and reliability problem.The operational issue is not just exploitation. A malformed volume that triggers repeated kernel errors can interrupt jobs, complicate incident response, and degrade confidence in the storage stack. That can force administrators to isolate systems or suspend workflows while patches roll out.
Cloud and container platforms
Cloud platforms may be affected even when the end user never mounts a filesystem directly. Images, block volumes, snapshots, and ephemeral root disks all depend on kernel filesystem code. If a provider uses ext4 in image pipelines or guest workloads, then the fix becomes part of the patch cadence for both hosts and guests.This is one reason Microsoft’s own Linux-facing documentation keeps reiterating CVE scanning and patch workflows in Azure Linux and SQL Server on Linux contexts. Microsoft notes that Azure Linux scans for vulnerabilities twice a day and treats high and critical CVEs with special urgency, while SQL Server on Linux guidance continues to list ext4 and XFS as supported filesystems on current Linux platforms. That broader ecosystem context shows how quickly a kernel filesystem issue can surface in enterprise support planning.
Consumer desktops and embedded devices
On consumer Linux systems, exposure is usually lower, but not negligible. External drives, SD cards, rescue media, and shared filesystems all create opportunities to mount untrusted ext4 metadata. Embedded devices may be even more constrained because they often run older kernels for long periods and cannot patch as quickly as desktop distributions.The real risk is not the default desktop mount path alone, but the growing number of places where ext4 data is ingested from outside the device. That includes backups, sync tools, and vendor update workflows. Every extra mount point is another possible path into the kernel parser.
- Enterprises face higher exposure from untrusted images and automation.
- Cloud operators care because images and volumes cross trust boundaries.
- Consumer systems remain exposed through removable media.
- Embedded devices may be at risk due to slow patch cadence.
- Support teams need to treat filesystem CVEs as availability issues, not just security notices.
How This Fits the Linux Kernel Security Model
Linux kernel security is often described through broad categories like privilege escalation, arbitrary write, or information disclosure, but filesystem bugs sit at the intersection of all three. They operate in privileged code, consume attacker-influenced input, and can affect both confidentiality and availability. That is why the kernel community leans hard on validation, bounds checks, and corruption-aware failure paths.Security through fail-closed behavior
The extent-tree fix is a textbook example of fail-closed design. Rather than guessing whether a pointer is close enough to valid, the code now requires it to be demonstrably in range. That discipline is especially important in a kernel that must handle many filesystems, storage stacks, and hardware combinations.It also reinforces the kernel’s preference for making corruption obvious. A filesystem that keeps marching after invalid metadata is often the one that later suffers deeper data loss. Stopping early is usually the safer choice, even if it inconveniences the mount or the caller.
The importance of stable backports
Because the Linux kernel supports multiple stable branches, a fix like this can take on a second life as a backported patch. That means security teams should not only ask “is my distro vulnerable?” but also “has my vendor merged the stable fix?” The answer may differ between mainline, long-term support, and vendor kernels.For security operations teams, that creates a familiar but unavoidable burden. Kernel CVEs are not purely theoretical, because they almost always map to actual release engineering work. The older the fleet, the more likely it is that some systems need manual validation or a reboot schedule.
A reminder about filesystem trust
The CVE also underlines a broader lesson: filesystems are parsers. People often talk about parsers in the context of browsers, document readers, or multimedia codecs, but a filesystem parser is just as exposed. It interprets attacker-controlled structure, follows offsets, and makes privileged memory decisions based on what it reads.- Filesystems are kernel parsers.
- Boundary validation is a security control, not just a correctness check.
- Stable backports are crucial for real-world mitigation.
- Corruption handling should favor containment over optimism.
- Kernel bugs often affect confidentiality, integrity, and availability at once.
What Administrators Should Do Now
For most organizations, the first step is straightforward: identify which kernels include the upstream or vendor-fixed ext4 code and patch accordingly. The second step is more nuanced: review where your systems mount ext4 volumes from untrusted or semi-trusted sources, and treat those workflows as higher-risk paths. If you run support-sensitive workloads, you may also need to coordinate reboots or live patch windows rather than relying on ordinary maintenance cycles.Practical response steps
- Inventory systems that use ext4 in production, recovery, virtualization, or container workflows.
- Check vendor advisories and kernel changelogs for the
ext4_ext_correct_indexesfix. - Prioritize hosts that mount untrusted images, removable media, or customer-supplied volumes.
- Validate whether your environment uses live patching or requires a reboot for kernel updates.
- Reassess monitoring for filesystem corruption and mount errors so you can spot abnormal behavior quickly.
Where patch urgency is highest
- Systems that mount third-party disk images
- Forensic and recovery workstations
- Hypervisors and cloud hosts with guest image intake
- Backup appliances and media gateways
- Older LTS kernels that may need vendor backports
Strengths and Opportunities
This fix is small, targeted, and aligned with the kernel’s broader safety philosophy. It also demonstrates how Linux maintainers continue to refine mature code paths without changing the external behavior of healthy filesystems. That is a strength, but it is also an opportunity to improve operational discipline around storage security.- The patch is surgical, limiting regression risk.
- It improves defensive validation in a high-value kernel path.
- It fits cleanly with ext4’s existing corruption handling model.
- It should be straightforward to backport across stable branches.
- It gives vendors a clear basis for security advisories and patch notes.
- It reinforces a valuable engineering norm: never trust disk metadata by default.
- It may motivate better fuzzing and image validation in downstream pipelines.
Risks and Concerns
The biggest concern is that filesystem bugs are often underestimated because they look like ordinary robustness issues. In reality, they live at a privileged boundary where a malformed on-disk structure can influence kernel execution paths. That makes the risk broader than a simple crash report suggests.- A slab-out-of-bounds read can expose kernel memory.
- Crafted ext4 images may trigger the issue through mount-time or repair-time flows.
- Systems that process untrusted media are disproportionately exposed.
- Older kernels may remain vulnerable if vendors delay backports.
- Operators may overlook the issue because NVD scoring was not yet assigned at publication time.
- Incomplete fleet inventories can leave some machines unpatched longer than expected.
- Filesystem corruption can cascade into availability problems even without exploitation.
Looking Ahead
The most important question now is not whether ext4 is safe in general, but how quickly the fixed code reaches production kernels across the ecosystem. Mainline resolution is only the first step. The real security outcome depends on stable backports, distribution packaging, and how promptly administrators apply them.The second question is whether this CVE prompts more scrutiny of other extent-tree paths. That would be healthy. Bugs like this tend to cluster around the same design pressure points: metadata trust, pointer range checks, and recovery code that assumes too much about the shape of corrupted trees. The lesson for maintainers is not to panic, but to keep hardening the parser with the same discipline that fixed this issue.
Signals to watch
- Stable kernel backports and vendor advisories for ext4.
- Distribution security updates that explicitly mention CVE-2026-31449.
- Whether monitoring teams update alerts for filesystem corruption events.
- Any follow-on hardening in related extent-tree helpers.
- Downstream guidance for cloud images, appliances, and recovery environments.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center