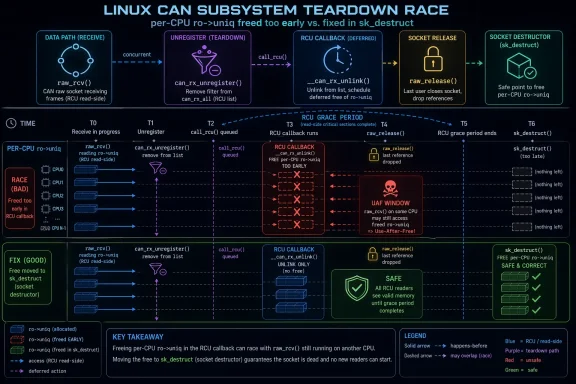
In the Linux kernel’s CAN subsystem, CVE-2026-31532 closes a use-after-free bug in the raw socket receive path, specifically in
This is a classic Linux kernel lifetime bug: one side of the code thinks teardown is complete, while another side still has a legitimate path to the object. In this case, the object is not a simple heap buffer but percpu uniq storage, which makes the bug especially relevant to low-level networking correctness. The important detail is that the vulnerability does not hinge on malformed input in the usual user-space sense; it arises from the interaction between asynchronous cleanup and RCU-protected receive processing.
The kernel description makes the sequence clear.
NVD has not yet assigned a CVSS score, so defenders should not read the absence of a published severity as reassurance. Awaiting enrichment simply means the record has been ingested before full scoring and triage metadata are complete. In practice, kernel bugs like this are often treated as production-significant because they touch memory safety and concurrency at the same time.
The broader pattern is familiar to anyone who tracks Linux kernel security: the fix is small, but the lesson is large. Kernel maintainers often solve these issues by moving cleanup to a point in the lifecycle where object ownership is unambiguous. Here, that means tying the
The CAN raw path is not the sort of code path most end users think about daily, but kernel bugs are rarely limited by user awareness. A vulnerability in teardown logic can be exercised by automated services, network daemons, containerized workloads, or embedded software that creates and destroys sockets repeatedly. That means the operational blast radius can exceed the apparent scope of the subsystem.
The fix is reassuring because it is conceptually simple: delay the free until the destructor runs. That kind of patch usually indicates maintainers have identified the exact ownership boundary and can enforce it with minimal collateral damage. Minimal change is often the best sign in a kernel security fix, because it lowers the odds of introducing a second bug while eliminating the first.
Key points:
This is a good example of fixing the ownership model rather than just patching one symptom. A weaker response would be to add an ad hoc delay or an extra check in
That distinction matters for long-term maintainability. Kernel networking code evolves constantly, and fixes that preserve the original object model are usually safer than workarounds layered on top of it. A clean teardown contract also makes it easier for stable maintainers to backport the patch across supported trees without altering unrelated behavior.
In practical terms, RCU guarantees the reader side will run within a grace-period framework, but the free still has to occur at the right point in the object’s lifecycle. If the destructor is the point where all relevant references are finally gone, then that is where the memory must be released. The fix follows that rule exactly.
The real risk profile depends less on the word “CAN” and more on whether a given deployment uses the raw socket path at all. In a fleet where CAN is core to telemetry or device control, the bug becomes a practical stability and security concern. In a desktop-only fleet, exposure may be lower, but it is not automatically zero if the affected module is present and used by software.
This also illustrates why enterprise vulnerability management has to look beyond headline CVSS scores. A kernel memory-safety issue can be operationally serious even when it does not come with a neat exploit narrative. If a bug can crash a critical service or destabilize a host, it deserves patch attention regardless of subsystem size.
A few practical distinctions matter:
For administrators, that cross-vendor visibility is useful. It means a Linux kernel issue can surface in a Microsoft-centered vulnerability workflow, which is increasingly relevant in mixed estates where Linux runs underneath Windows-heavy management practices. This is not a Linux-only problem anymore; it is a fleet-management problem.
The upside is better coordination. The downside is that different sources may present the same issue with different timing, metadata completeness, or remediation notes. NVD’s “Awaiting Enrichment” status is a reminder that defenders should not wait for a perfectly polished entry before acting on upstream kernel fixes.
That is especially true for kernel flaws, where impact often depends on deployment context. A narrow subsystem with broad operational importance can be more disruptive than a higher-scored issue that affects little real-world infrastructure. Context beats abstraction when the bug lives in the kernel.
The networking stack is especially exposed because it mixes hot paths, RCU, percpu storage, and deferred work. Those design choices are deliberate and necessary for performance, but they make lifetime bugs harder to spot. The bug in
That is why kernel maintainers tend to prefer lifecycle-correct fixes over surface-level guards. If the cleanup point is wrong, no amount of extra checking inside the fast path fully solves the problem. Moving the free to the destructor ensures the storage remains valid for the entire period in which it can still be reached.
The lesson for maintainers is straightforward but unforgiving: do not free supporting state until every callback and reader that can still observe it has drained. The lesson for operators is equally direct: kernel bugs in cleanup paths deserve the same attention as flashy remote-exploit advisories.
Next, inventory where CAN raw support is actually used. Many teams know they have Linux, but not which hosts use specialized socket families or peripheral-facing interfaces. That is especially important in embedded estates, where CAN may be a core dependency rather than an edge case.
Finally, treat this as both a security and stability fix. A use-after-free in the networking stack can manifest as crashes, data corruption, or nondeterministic failures, even if no one has produced a public exploit. Stability bugs in the kernel are security bugs in disguise when they sit on infrastructure-critical code paths.
It is also worth watching whether adjacent CAN paths receive similar lifetime hardening. Kernel fixes often expose nearby assumptions that were safe only by accident. If one receive-path teardown bug existed, maintainers may revisit related cleanup code to ensure other pointers are released at the correct lifecycle stage.
What operators should track next:
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
raw_rcv(). The flaw is subtle but important: raw_release() unregisters CAN receive filters while receiver deletion is deferred via call_rcu(), creating a window where raw_rcv() can still run after ro->uniq has been freed. The fix moves free_percpu(ro->uniq) out of raw_release() and into a raw-specific socket destructor so the per-CPU storage is not released until the relevant RCU callbacks have drained. NVD lists the record as Awaiting Enrichment, with the CVE published on April 23, 2026, and references to upstream kernel commits already attached.
 Overview
Overview
This is a classic Linux kernel lifetime bug: one side of the code thinks teardown is complete, while another side still has a legitimate path to the object. In this case, the object is not a simple heap buffer but percpu uniq storage, which makes the bug especially relevant to low-level networking correctness. The important detail is that the vulnerability does not hinge on malformed input in the usual user-space sense; it arises from the interaction between asynchronous cleanup and RCU-protected receive processing.The kernel description makes the sequence clear.
can_rx_unregister() removes receive filters, but the actual receiver deletion is deferred, and that delay is long enough for raw_rcv() to overlap with socket teardown. Once ro->uniq is freed too early, any later access in the receive path becomes a use-after-free. That is the kind of bug that can stay invisible in normal testing and then surface under teardown churn, high traffic, or unlucky timing.NVD has not yet assigned a CVSS score, so defenders should not read the absence of a published severity as reassurance. Awaiting enrichment simply means the record has been ingested before full scoring and triage metadata are complete. In practice, kernel bugs like this are often treated as production-significant because they touch memory safety and concurrency at the same time.
The broader pattern is familiar to anyone who tracks Linux kernel security: the fix is small, but the lesson is large. Kernel maintainers often solve these issues by moving cleanup to a point in the lifecycle where object ownership is unambiguous. Here, that means tying the
uniq release to the socket destructor rather than the earlier release path. That preserves the concurrency guarantees already implied by can_rx_unregister() and RCU.Why This Bug Matters
At first glance, this looks like a narrow bug in a niche networking subsystem. In reality, it is exactly the kind of flaw that kernel teams worry about because it involves object lifetime, deferred deletion, and read-side concurrency all at once. The failure mode is not theoretical: once memory is released while code still assumes it exists, the kernel can read stale or repurposed data, crash, or corrupt state in hard-to-predict ways.The CAN raw path is not the sort of code path most end users think about daily, but kernel bugs are rarely limited by user awareness. A vulnerability in teardown logic can be exercised by automated services, network daemons, containerized workloads, or embedded software that creates and destroys sockets repeatedly. That means the operational blast radius can exceed the apparent scope of the subsystem.
The fix is reassuring because it is conceptually simple: delay the free until the destructor runs. That kind of patch usually indicates maintainers have identified the exact ownership boundary and can enforce it with minimal collateral damage. Minimal change is often the best sign in a kernel security fix, because it lowers the odds of introducing a second bug while eliminating the first.
The teardown race in plain language
The race is easy to describe even if the implementation is intricate. One path is trying to unregister and free a socket’s receive state, while another path may still be traversing the receive logic under RCU protection. If the release path gets ahead of the callback drain, the receive side can dereference data that no longer belongs to it. That is the textbook shape of a use-after-free.Key points:
- The bug is caused by teardown timing, not by a parser mistake.
- The vulnerable object is percpu uniq storage.
- The risky window exists because deletion is deferred with call_rcu().
- The correct fix is to release memory in sk_destruct, not in
raw_release().
How the Linux Kernel Fix Works
The kernel note is unusually direct about the remediation.free_percpu(ro->uniq) is moved out of raw_release() and into a raw-specific socket destructor, ensuring the memory survives until the socket’s final teardown point. That matters because can_rx_unregister() itself holds an extra socket reference and only drops it from the RCU callback, so freeing the storage at destructor time aligns the free with the reference lifecycle.This is a good example of fixing the ownership model rather than just patching one symptom. A weaker response would be to add an ad hoc delay or an extra check in
raw_rcv(), but that would leave the core lifetime mismatch intact. By relocating the free, the kernel makes the lifetime contract explicit and easier to reason about.That distinction matters for long-term maintainability. Kernel networking code evolves constantly, and fixes that preserve the original object model are usually safer than workarounds layered on top of it. A clean teardown contract also makes it easier for stable maintainers to backport the patch across supported trees without altering unrelated behavior.
Why RCU is not a complete shield
RCU protects readers from some forms of concurrent deletion, but it does not automatically make every dereference safe if the code releases supporting storage too early. The key misconception is that “RCU-managed” means “safe to free whenever the unregister call returns.” That is not how reference lifetimes work in a kernel that mixes deferred callbacks with direct teardown.In practical terms, RCU guarantees the reader side will run within a grace-period framework, but the free still has to occur at the right point in the object’s lifecycle. If the destructor is the point where all relevant references are finally gone, then that is where the memory must be released. The fix follows that rule exactly.
What the Vulnerability Could Affect
The most immediate impact is on systems that actively use Linux CAN raw sockets, especially where sockets are created and torn down frequently. That may sound specialized, but kernel CVEs rarely remain confined to the idealized subsystem in which they were born. Containers, test harnesses, industrial control software, and embedded networking applications can all create the right timing conditions.The real risk profile depends less on the word “CAN” and more on whether a given deployment uses the raw socket path at all. In a fleet where CAN is core to telemetry or device control, the bug becomes a practical stability and security concern. In a desktop-only fleet, exposure may be lower, but it is not automatically zero if the affected module is present and used by software.
This also illustrates why enterprise vulnerability management has to look beyond headline CVSS scores. A kernel memory-safety issue can be operationally serious even when it does not come with a neat exploit narrative. If a bug can crash a critical service or destabilize a host, it deserves patch attention regardless of subsystem size.
Consumer, enterprise, and embedded angles
For consumers, the likely exposure is limited unless specialized hardware or software uses CAN raw sockets. For enterprise and embedded operators, the calculus changes quickly because CAN is common in industrial, automotive, lab, and appliance environments. The same bug that looks obscure on paper may be business-critical in a control system.A few practical distinctions matter:
- Consumer PCs are less likely to hit the path.
- Enterprise Linux servers may encounter it through tooling, virtualization, or fleet automation.
- Embedded and industrial systems may use CAN routinely and therefore face higher exposure.
- Test and CI environments can trigger teardown races more readily than production workloads.
Why This Arrives Through NVD and Microsoft’s Advisory Flow
One detail that stands out in the record is the publication path. NVD lists the source as kernel.org, while Microsoft’s Security Update Guide also hosts a CVE entry for the issue. That may look surprising at first, but it reflects a broader reality: Linux kernel vulnerabilities are now tracked across multiple security ecosystems, not just by Linux distributions themselves.For administrators, that cross-vendor visibility is useful. It means a Linux kernel issue can surface in a Microsoft-centered vulnerability workflow, which is increasingly relevant in mixed estates where Linux runs underneath Windows-heavy management practices. This is not a Linux-only problem anymore; it is a fleet-management problem.
The upside is better coordination. The downside is that different sources may present the same issue with different timing, metadata completeness, or remediation notes. NVD’s “Awaiting Enrichment” status is a reminder that defenders should not wait for a perfectly polished entry before acting on upstream kernel fixes.
What the missing CVSS does and does not mean
A missing score is not a statement that the bug is harmless. It only means the database entry has not been fully enriched yet. Security teams should treat the description, the patch location, and the involved lifetime semantics as the primary indicators of risk until scoring arrives.That is especially true for kernel flaws, where impact often depends on deployment context. A narrow subsystem with broad operational importance can be more disruptive than a higher-scored issue that affects little real-world infrastructure. Context beats abstraction when the bug lives in the kernel.
Why Kernel Teardown Bugs Keep Happening
This CVE fits a recurring pattern in kernel engineering: asynchronous cleanup is hard. Objects are torn down one way, callbacks run another way, and reference counts can survive longer than the code that allocated the storage expects. When those paths are not aligned perfectly, use-after-free bugs appear.The networking stack is especially exposed because it mixes hot paths, RCU, percpu storage, and deferred work. Those design choices are deliberate and necessary for performance, but they make lifetime bugs harder to spot. The bug in
raw_rcv() is less about CAN specifically and more about the challenge of designing safe teardown in a concurrent kernel.That is why kernel maintainers tend to prefer lifecycle-correct fixes over surface-level guards. If the cleanup point is wrong, no amount of extra checking inside the fast path fully solves the problem. Moving the free to the destructor ensures the storage remains valid for the entire period in which it can still be reached.
The hidden danger of “almost finished” teardown
A teardown sequence can look complete from one code path’s perspective while still being active elsewhere. That mismatch is the essence of many kernel memory bugs. In this case,raw_release() thinks it has done enough, but RCU still allows the receive side to run briefly.The lesson for maintainers is straightforward but unforgiving: do not free supporting state until every callback and reader that can still observe it has drained. The lesson for operators is equally direct: kernel bugs in cleanup paths deserve the same attention as flashy remote-exploit advisories.
Operational Response for Administrators
If you maintain Linux systems that use CAN raw sockets, the first step is to verify whether your vendor kernel includes the fix. NVD already points to upstream stable references, which means the patch is moving through the normal kernel backport pipeline, but that does not guarantee every distro build has it yet. Vendor backport status is what matters in production.Next, inventory where CAN raw support is actually used. Many teams know they have Linux, but not which hosts use specialized socket families or peripheral-facing interfaces. That is especially important in embedded estates, where CAN may be a core dependency rather than an edge case.
Finally, treat this as both a security and stability fix. A use-after-free in the networking stack can manifest as crashes, data corruption, or nondeterministic failures, even if no one has produced a public exploit. Stability bugs in the kernel are security bugs in disguise when they sit on infrastructure-critical code paths.
Practical checklist
- Confirm whether your running kernel includes the backported fix.
- Review whether CAN raw sockets are enabled or used in production.
- Check embedded, industrial, and test systems separately from general-purpose servers.
- Align patch timing with your vendor’s kernel cadence, not just upstream status.
- Watch for unexplained crashes or teardown-related anomalies in systems using CAN.
Strengths and Opportunities
The strongest aspect of this case is that the fix appears tightly scoped and conceptually clean. It does not rewrite the subsystem; it corrects the lifetime boundary. That makes the patch easier to review, backport, and validate in downstream kernels. The incident also reinforces why RCU-aware teardown design matters so much in modern Linux.- The bug has a clear root cause.
- The remediation is small and targeted.
- The patch aligns with existing kernel ownership rules.
- The issue is already visible in mainstream vulnerability tracking.
- The fix should be relatively backport-friendly for vendors.
- The CVE improves operational tracking for mixed Linux estates.
- Administrators get a concrete reason to audit CAN usage in their fleets.
Risks and Concerns
The main concern is that this kind of bug can be easy to underestimate because it lives in a specialized subsystem. That is a mistake. Narrow exposure does not mean low impact when the vulnerability can destabilize a kernel or corrupt memory in a critical path. The other concern is patch lag: upstream fixes often arrive before vendor kernels do.- Exposure may be hidden inside embedded or industrial systems.
- The bug may be hard to reproduce in normal testing.
- Some operators may not realize they use CAN raw sockets at all.
- Vendor backports may land on different schedules.
- The absence of a CVSS score may cause false reassurance.
- Teardown races can produce intermittent symptoms that look unrelated.
- A UAF in kernel networking can have broader side effects than the first report suggests.
Looking Ahead
The next thing to watch is downstream packaging. Once the fix appears in vendor kernels, administrators will need to verify not just that a patch exists in source control, but that it has been integrated into the exact build they deploy. That distinction is especially important in long-term-support and appliance environments, where kernel versions move more slowly.It is also worth watching whether adjacent CAN paths receive similar lifetime hardening. Kernel fixes often expose nearby assumptions that were safe only by accident. If one receive-path teardown bug existed, maintainers may revisit related cleanup code to ensure other pointers are released at the correct lifecycle stage.
What operators should track next:
- Vendor advisories that mention the CAN raw socket fix.
- Backport confirmation in long-term kernel branches.
- Any follow-up changes to
can_rx_unregister()or raw socket destructors. - Regressions or crash reports in CAN-heavy embedded fleets.
- Whether distros label the issue as a security update or a stability update.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center