A small but important Linux kernel hardening landed this month: the framebuffer console (fbcon) subsystem was patched to clear stale pointers by setting fb_display*->mode to NULL when a framebuffer mode is released, closing a use‑after‑free discovered by syzkaller that could otherwise allow a local actor to crash or corrupt kernel memory.
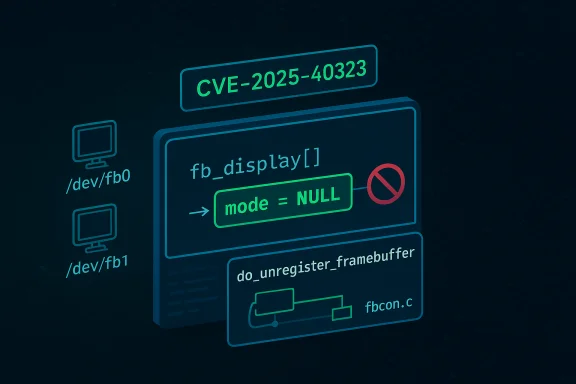
The Linux framebuffer console (fbcon) provides a simple kernel-side text console on framebuffer devices and is widely used in embedded systems, appliance kernels, and some distributions' fallback console implementations. A recently assigned CVE — CVE‑2025‑40323 — tracks a robustness defect in fbcon where a released videomode could leave a dangling pointer in the global fb_display[] array. The issue was surfaced by syzkaller (a kernel fuzzing tool), which produced a KASAN-detectable slab use‑after‑free in fb_mode_is_equal that led to a kernel read of freed memory. The kernel community accepted a surgical patch that clears fb_display->mode during framebuffer unregistration, preventing later accesses from following a freed pointer. This is a defensive, correctness fix: the underlying cause is lifecycle/cleanup asymmetry in the framebuffer code paths (mode lists being freed without nulling out pointers stored in fb_display[]). The practical risk is primarily availability (kernel oops/panic) and stability, although any kernel memory corruption has a theoretical potential to contribute to a more serious exploit chain under additional, unrelated primitives. Multiple vulnerability databases have recorded the CVE and the upstream/stable patches have been merged.
Administrators should treat this as a routine kernel hardening: verify whether fbcon/fbdev is present and in use in their infrastructure, prioritize the vendor kernel updates that include the stable backport, and apply the patches in the next maintenance window. Systems that do not need framebuffer support are good candidates for further hardening by disabling the subsystem entirely. The community discussion, upstream commits, and stable patching activity provide sufficient evidence that the issue has been analyzed and resolved; however, operators must still perform host‑level inventory and confirm the applied kernel commits when validating remediation.
Source: MSRC Security Update Guide - Microsoft Security Response Center**
 Background / Overview
Background / Overview
The Linux framebuffer console (fbcon) provides a simple kernel-side text console on framebuffer devices and is widely used in embedded systems, appliance kernels, and some distributions' fallback console implementations. A recently assigned CVE — CVE‑2025‑40323 — tracks a robustness defect in fbcon where a released videomode could leave a dangling pointer in the global fb_display[] array. The issue was surfaced by syzkaller (a kernel fuzzing tool), which produced a KASAN-detectable slab use‑after‑free in fb_mode_is_equal that led to a kernel read of freed memory. The kernel community accepted a surgical patch that clears fb_display->mode during framebuffer unregistration, preventing later accesses from following a freed pointer. This is a defensive, correctness fix: the underlying cause is lifecycle/cleanup asymmetry in the framebuffer code paths (mode lists being freed without nulling out pointers stored in fb_display[]). The practical risk is primarily availability (kernel oops/panic) and stability, although any kernel memory corruption has a theoretical potential to contribute to a more serious exploit chain under additional, unrelated primitives. Multiple vulnerability databases have recorded the CVE and the upstream/stable patches have been merged. What went wrong — technical anatomy
The failing lifetime model
At a high level, the kernel framebuffer code manages per‑device mode lists (fb_info->modelist) and a global array of console display descriptors (fb_display[]). Some userspace/driver operations can cause a given fb_info's mode structures to be freed (for example when a framebuffer device module is removed), yet those same mode pointers may have previously been referenced from fb_display[]. The bug occurs when the code frees modelist memory but does not sweep fb_display[] to remove references to now‑freed mode objects. Subsequent code paths that reference fb_display*->mode can therefore touch freed memory and trigger a use‑after‑free. This exact sequence was reproduced in a multi‑step syzkaller test case posted by the reporter.Example reproduction (simplified)
- Have /dev/fb0 registered and in use.
- Insert a kernel module that registers /dev/fb1.
- Map fb1’s mode into the global fb_display[] (via FBIOPUT_CON2FBMAP).
- Switch the visible console away from fb (for example to VGA) so fb1 can be rmmodded cleanly.
- rmmod the kernel module that provided fb1, which frees fb1->modelist but does not clear fb_display[].
- Trigger an operation that tries to delete or compare a mode on fb0; fbcon code dereferences fb_display->mode and hits freed memory, producing a KASAN slab‑use‑after‑free and a kernel OOPS. **
This sequence maps directly to the syzkaller output included in the public advisories and to the patch discussion. The root cause is a mismatch between the code paths that free modelist memory and the code paths that maintain the global display pointers. The pragmatic fix is to make the unregistration path defensive: when a mode is being unregistered, ensure no fb_display[] entries still point to it.
The upstream fix: small, surgical, and targeted
The accepted upstream patch (small modifications in drivers/video/fbdev/core/fbcon.c and a couple of related spots) adds logic to the framebuffer unregistration path so that when a mode is freed the code walks the fb_display[] array and clears any entries that pointed to the freed mode. The patch set is intentionally tiny — roughly 20 lines of insertion — and focuses on explicit pointer hygiene rather than refactoring bigger subsystems. The change was applied to the upstream kernel and cherry‑picked into the stable trees; stable maintainers have included the fix in the 6.17 stable update series. Why is this approach appropriate?- It addresses the concrete, fuzz-reported lifecycle bug without touching unrelated fbcon semantics.
- It is backwards-compatible and low risk to backport to distribution kernels and vendor trees.
- It resolves the KASAN‑detected UAF by ensuring that freed mode pointers cannot be observed again through fb_display[].
Severity, exploitability, and practical risk
Attack surface and vector
- Vector: Local. An attacker or malfunctioning local process must be able to exercise ioctl operations (fb ioctls) and to load/unload framebuffer modules or otherwise cause a mode to be freed while a stale pointer remains. On many systems the framebuffer device nodes are not world‑writable, so the practical attack surface is constrained to local accounts with device access or privileged users.
- Privileges: Low-to-medium depending on system configuration. On embedded or single‑user systems where framebuffer devices are accessible to unprivileged processes the risk increases; on hardened multi‑user servers the practical exploitability is likely low.
- Impact: Availability (kernel OOPS / panic) and potential memory corruption. The immediate observed symptom in syzkaller runs was a slab use‑after‑free detected by KASAN; that manifests as a crash or kernel trace. While kernel memory corruption sometimes forms part of privilege escalation chains, there is no authoritative, public report of a remote or local privilege escalation achieved solely via this bug. Treat more serious exploitation as theoretical* rather than observed at the time of disclosure.
CVSS and scoring
At the time of publication the NVD record is present but marked "Awaiting Analysis" for NVD’s numeric CVSS scoring; public trackers have recorded the technical details but distribution vendors are treating this as a robustness/DoS fix rather than an immediate RCE/ESC vector. Operators should assume the fix is prioritized for availability/stability reasons and follow normal patching practice for kernel updates.Who is affected
- Systems that include fbcon/fbdev support in their kernels and expose framebuffer devices (for example embedded Linux devices, appliances, some desktop kernels that keep fbcon for backward compatibility).
- Distributions and vendors who ship kernels with framebuffer console enabled in configuration or with vendor drivers that register framebuffer devices.
- Virtualized or cloud hosts where guests or host agents can access framebuffer devices — although modern cloud VM images often use kernel modesetting (KMS) and DRM rather than the legacy fbdev/fbcon path, vendor‑specific kernels and appliance images can still contain the vulnerable code path until patched.
Patching and mitigation guidance
Apply the upstream and vendor patches promptly in the following order of preference:- Install vendor-supplied kernel updates that include the stable backport. Major distributions and the stable tree maintainers have integrated the patch into the stable kernel updates; check your distribution security tracker for package updates that map to the upstream commit.
- If you maintain your own kernels or build custom images, merge the upstream commit (the patch applied to drivers/video/fbdev/core/fbcon.c, commit referenced in the stable tree) and rebuild your kernel. The change is deliberately small and easy to backport.
- Where immediate patching is not possible, reduce exposure by removing or restricting access to framebuffer device nodes:
- Remove device nodes for unused framebuffer devices (for example, /dev/fb1) or set restrictive permissions.
- Ensure only trusted users/groups can access /dev/fb* (e.g., root or a limited video group).
- If possible, disable fbcon/fbdev in kernel builds (unselect CONFIG_FB_CONSOLE and related options) for systems that do not use the framebuffer console.
Quick triage checklist
- Check for /dev/fb* on hosts:
- If none exist, likelihood of exposure is low.
- If present, determine which processes/groups have access to them.
- Inspect kernel config:
- If CONFIG_FB and CONFIG_FB_CONSOLE are enabled, the code paths are present.
- Review vendor changelogs and security advisories for kernel updates that reference fbcon fixes or include the commit IDs listed in upstream stable merges.
- Plan rolling reboots on hosts as required to deploy patched kernels safely.
Operational considerations for cloud and enterprise environments
Enterprises should remember that containers inherit the host kernel. A patched container image does not mitigate an unpatched host kernel. In shared or multi‑tenant environments, a local kernel crash on a host affects all tenants; therefore patching host kernels that include the vulnerable code should be prioritized according to your risk model. For Azure and other cloud customers, vendor attestations and product‑scope mappings can help prioritize remediation, but they are inventory statements — they do not guarantee the absence of the vulnerable code in other vendor artifacts. Microsoft and other vendors have adopted machine‑readable VEX/CSAF attestations to help automate triage; use those attestations in conjunction with host‑level inventory to make patching decisions.Why this class of bug matters beyond immediate crashes
Even though the patch and the vulnerability look modest — a missing NULL assignment for a pointer swept into a global array — these are the exact kinds of lifetime bugs that produce flakey crashes and hard-to‑diagnose behavior in production systems. A few operational implications:- For debugging and forensics: UAF bugs often leave inconsistent crash traces. Kernel oops logs and vmcores captured during crashes are invaluable when validating that the stable patch eliminates the path to freed memory.
- For maintenance windows: Even small patches require kernel upgrades and reboots; plan for the reboot downtime in production environments.
- For security posture: Small memory-corruption bugs can be combined with other primitives (e.g., user‑controlled pointers, driver-specific acceleration code) in complex exploit chains. While no public exploit demonstrates escalation here, defenders prefer to remove such primitives where possible.
Patch anatomy — what changed in the code
The upstream commits add logic to the framebuffer unregistration routine (do_unregister_framebuffer/ fbcon_mode_deleted paths) to walk fb_display[] and set any fb_display*->mode pointers equal to the mode being freed to NULL. The change is minimal:- Added a short loop that iterates over the fb_display[] entries and clears matching mode pointers.
- Touched only the specific files involved in mode management: drivers/video/fbdev/core/fbcon.c (primary), with minor include or helper adjustments in fbmem.c and fbcon.h as appropriate.
- The patch was reviewed and accepted by stable maintainers, then cherry‑picked into the stable update series to ease downstream rollouts.
What to tell operations and managers
- This CVE is a correctness/hardening fix that prevents kernel use‑after‑free in framebuffer console code.
- The immediate risk is local crash / DoS; exploit escalation to root from this single primitive has not been publicly demonstrated.
- Prioritize applying vendor/supplier kernel updates that include the patched stable commits. If you run custom kernels, backport the upstream commit and rebuild.
- For systems that do not use framebuffer devices, validate and disable framebuffer support in kernel configs where operationally feasible.
- For multi‑tenant hosts and appliances, include this patch in the next maintenance window and collect crash logs that can be correlated to the syzkaller KASAN traces if you saw prior OOPSes.
Strengths and potential risks of the upstream response
Notable strengths
- The fix is small, focused, and easy to review; it addresses the precise lifetime bug raised by syzkaller.
- Upstream maintainers prioritized merging to stable branches and included stable maintainers in the review loop, which speeds downstream distribution backports.
- Multiple independent vulnerability feeds and distribution trackers have ingested the CVE entry, which simplifies triage and automated inventory tools.
Potential risks and caveats
- The remediation requires kernel updates and reboots. Environments that delay kernel patches (embedded devices, appliances, vendor‑locked systems) may remain exposed for extended periods.
- Some downstream kernels or vendor kernels may have differing fbdev configurations; simply matching a kernel version number is not sufficient to guarantee the patch is present — operators must verify the presence of the upstream commit or the vendor changelog for confirmation.
- The presence of framebuffer devices in an environment is often a policy decision (for example, enabled for debugging or installed by OEMs); lack of visibility into custom images or marketplace artifacts can leave blind spots. Use kernel config inventories and image SBOMs where available.
Recommended next steps (concise)
- Inventory hosts for framebuffer devices (/dev/fb*).
- Check vendor security advisories and apply kernel updates that reference fbcon fixes or stable commit IDs.
- If immediate patching is not possible, restrict access to framebuffer device nodes and disable fbcon where feasible.
- Capture and preserve any kernel oops traces or vmcores from hosts that have experienced fbcon-related crashes for post‑patch validation.
- For custom kernels, merge the upstream commit and rebuild; for vendor kernels request a backport or validated update.
Closing analysis
CVE‑2025‑40323 is a reminder that small lifecycle mistakes in kernel drivers produce stability and availability issues that matter in the real world. The Linux kernel community’s response — a minimal, carefully reviewed patch and stable backports — is the right practical approach for a bug that is primarily a local, availability‑oriented robustness defect. The technical fix (nulling stale pointers during unregister) eliminates the observed KASAN-detected use‑after‑free and is low‑risk to deploy.Administrators should treat this as a routine kernel hardening: verify whether fbcon/fbdev is present and in use in their infrastructure, prioritize the vendor kernel updates that include the stable backport, and apply the patches in the next maintenance window. Systems that do not need framebuffer support are good candidates for further hardening by disabling the subsystem entirely. The community discussion, upstream commits, and stable patching activity provide sufficient evidence that the issue has been analyzed and resolved; however, operators must still perform host‑level inventory and confirm the applied kernel commits when validating remediation.
Source: MSRC Security Update Guide - Microsoft Security Response Center**