A recently assigned CVE, CVE-2025-38198, identifies a memory-safety bug in the Linux kernel's framebuffer console subsystem (fbcon) that can trigger an array-index-out-of-bounds error when the system processes writes to the fbcon store_modes sysfs node. The flaw is rooted in insufficient validation of the console-to-framebuffer mapping — specifically, the code can index the global fbcon array with a sentinel value (-1) when a console is unregistered, leading to undefined behavior detected by UBSAN and corrected upstream. This article explains what the bug is, how it arises, who is affected, how vendors have mitigated it, what administrators should do now, and the practical risk profile for production systems.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
What is fbcon and why it matters
The fbcon (framebuffer console) subsystem provides kernel-level support for simple text and graphics consoles driving framebuffer devices (fbdev). Historically important on embedded devices, kiosks, rescue systems, and older Linux desktops, fbcon exposes control points via sysfs and other kernel interfaces that let privileged actors query and configure display modes, console mappings, and per-console mode lists. Because it runs in kernel space, bugs in fbcon can have outsized consequences for stability and security compared with userspace utilities.How consoles and framebuffers are mapped
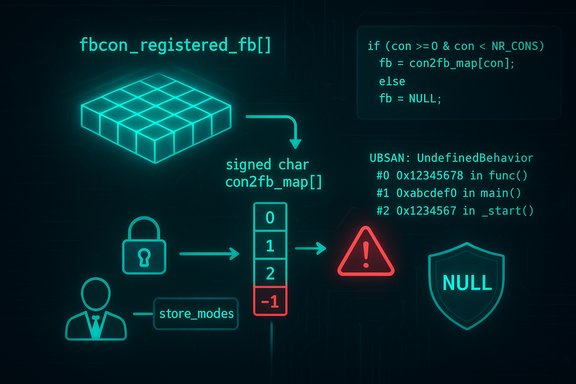
Internally, fbcon maintains arrays that map virtual consoles (e.g., tty1, tty2) to framebuffer devices. Two key pieces are:- fbcon_registered_fb[]: an array of pointers to framebuffer information structures.
- con2fb_map[]: a signed-char mapping indexed by console number that points into fbcon_registered_fb[]. A value of -1 in con2fb_map indicates that a console has no registered framebuffer.
If code dereferences fbcon_registered_fb[con2fb_map[console] without validating the con2fb_map entry, an index of -1 becomes an array lookup with an out-of-range index — the exact fault reported by UBSAN in this case.
The technical bug (what went wrong)
The crash trace and root cause
The vulnerability was brought to light by an Undefined Behavior Sanitizer (UBSAN) report that shows an array-index-out-of-bounds originating from drivers/video/fbdev/core/fbcon.c. The execution path as reported is:- fbcon_info_from_console reads con2fb_map[console] and returns fbcon_registered_fb[con2fb_map[console] without validating that con2fb_map[console] is non-negative.
- fbcon_new_modelist and fb_new_modelist call into code that ends up invoking store_modes via the sysfs attribute for modes.
- Writing to the fbdev store_modes sysfs node in certain states can cause con2fb_map entries to be -1, which in turn yields an index of -1 into fbcon_registered_fb[], triggering UBSAN's bounds check.
Why a sentinel value caused harm
Using a sentinel like -1 in a signed char mapping is common to indicate “no mapping,” but C array indexing with a negative value is undefined behavior. The codebase relied on callers avoiding dereference when the returned pointer was invalid — but that defensive assumption broke down because the negative index was applied before any pointer-level check existed. UBSAN exposed the mistake; the correct fix is explicit validation at the mapping-to-pointer stage, not optimistic indexing.Affected code paths and attack surface
Where the vulnerability is reachable
- The direct trigger reported is a write to the store_modes sysfs node exposed by the fbdev subsystem. That sysfs attribute is typically writable only by root, so the immediate attack surface is local privileged users or processes that can gain file-write access to sysfs attributes.
- The bug is not a remotely reachable network service flaw. Exploitation requires local privileged access (or a way to escalate to such access) to write to the relevant sysfs interface.
Potential outcomes of hitting the bug
- On systems compiled with UBSAN or with strict debugging options, an out-of-bounds access can trigger kernel diagnostics and possibly an oops/panic. In other configurations, it can cause memory corruption that leads to instability or escalate into more serious integrity issues.
- Public advisories and trackers rate the issue as a local-only vulnerability with integrity and availability impact potential, rather than a confidentiality compromise. Vendor advisories vary slightly in prioritization, but none report direct, widespread remote exploitation.
Vendor responses and fixed versions
Upstream kernel fix
The kernel maintainer branch contains a small, targeted change to ensure that fbcon_info_from_console returns NULL when con2fb_map has the sentinel indicating "no framebuffer" for that console. This change avoids the negative index lookup and lets callers handle a NULL safely. Multiple stable kernel trees received backports or fixes across versions after publication. Several distribution security trackers reference kernel commit IDs and explicitly list patched kernel versions.Distribution security status (representative samples)
- Debian: Lists affected packages and notes fixes in several release streams, with bookworm and various unstable and stable trees updated to incorporate kernel versions with the patch. Debian’s tracker shows patched package versions such as 6.1.147-1 and later for specific releases.
- Ubuntu: Publishes an advisory describing the issue and categorizes the priority as Medium. The Ubuntu advisory text mirrors the technical description and recommends applying kernel updates when available.
- Red Hat / RHEL: Security trackers acknowledge the issue and list it as kernel-related; vendor package-level fixes depend on the RHEL kernel packaging lifecycle, and at times vendors report "no fix" for some backport streams until a scheduled kernel update arrives. Administrators on enterprise distributions should consult vendor-specific errata.
- Other ecosystems (Amazon Linux, Snyk advisories, and third-party trackers) also document the vulnerability and link to kernel commits; many have issued or scheduled kernel updates in affected kernel branches.
Note on kernel variants and embedded devices
Because fbdev/fbcon remains present in many kernel builds for embedded and specialized devices, the vulnerability can appear in kernels for devices that do not track mainline kernel updates frequently. Vendors of embedded appliances, SoC-based devices, and some thin-client firmware may require firmware/kernel updates from the device OEM rather than a simple package upgrade. This increases mitigation lag for such deployments.Risk assessment and exploitability
Attack complexity and privileges
- The vulnerability's attack vector is local. The attacker needs the ability to write to the store_modes sysfs node — typically a privileged operation restricted to root or processes with appropriate capabilities.
- Because exploitation requires local privileged access, the immediate attack value of this bug for remote attackers is limited. However, if a separate privilege-escalation path exists on a system, chaining could be possible. Advisories list the CVSS vector elements as having local vector and requiring privileges, consistent with the code path.
Public exploit availability
- No credible public proof-of-concept (PoC) exploit for CVE-2025-38198 was found in common exploit repositories or vendor advisories at the time of this analysis. Security trackers and distribution advisories do not report active exploitation in the wild. That said, absence of a public PoC does not prove the vulnerability is harmless — local, privilege-required kernel flaws are often weaponized privately or in targeted campaigns. Administrators should treat the flaw seriously and prioritize patching.
Practical impact summary
- Likely impact: Denial of service (kernel crash / oops) or integrity issues from memory corruption, depending on kernel build and runtime state.
- Remote exploitation: No — requires local write-access to sysfs (root or equivalent).
- Urgency for servers: Moderate — apply kernel updates per distribution advisories, especially for multi-tenant or shared-hosting environments where local actors may have access.
Mitigation and remediation guidance
Recommended immediate actions (priority order)
- Patch the kernel: Apply vendor-supplied kernel updates where available. Distribution advisories list fixed kernel package versions; upgrading to the patched kernel is the definitive fix. For Debian users, refer to the fixed package versions noted in the Debian security tracker.
- Restrict access to sysfs: Ensure that only the root user and trusted administrative processes have write access to fbdev sysfs nodes such as store_modes. Use mount options, SELinux/AppArmor policies, or stricter file-system ACLs where possible to reduce the set of processes that can write to sysfs.
- Audit local users and privilege escalation vectors: Since exploitation requires local privilege, remove or harden any local privilege escalation paths (SUID binaries, weak sudo rules, exposed root shells) that could allow untrusted users to reach root-level capabilities.
- Vendor firmware updates for appliances: For embedded or appliance-type devices (kiosks, SoC boards, some thin clients), consult the OEM for firmware/kernel images with the patch applied — the device vendor’s upgrade process may be required.
Workarounds when immediate kernel upgrades are impractical
- Disable fbcon/fbdev: On systems that do not require framebuffer console functionality, rebuild or reconfigure kernels to omit fbcon/fbdev support. This is a heavy-handed option and often impractical for commodity distributions, but viable in controlled embedded builds.
- Temporarily limit sysfs writes: Use infrastructure tooling to monitor and block unauthorized writes to /sys/class/graphics/ attributes, or use mandatory access-control policy enforcement to deny writes to store_modes*. This does not fix the kernel but reduces exposure surface.
Why the fix is simple — but important
The upstream fix is small and principled: validate the mapping before indexing. In practice, many memory-safety bugs that produce UBsan reports are due to minor defensive lapses rather than systemic design failures. That said, small fixes in kernel space are important because they close off potential escalation paths and improve overall robustness. The story here is a classic example of a sentinel value (-1) used without converting to a safe pointer check; returning NULL and letting callers check the pointer is the correct kernel-practice pattern.Operational checklist for admins (exact steps)
- Inventory: Identify systems that run kernels with fbdev/fbcon enabled. Check kernel config (CONFIG_FB, CONFIG_FB_CONSOLE) and presence of /sys/class/graphics/*.
- Vendor advisories: Check distribution security trackers or vendor errata for fixed kernel package versions. Schedule updates accordingly. Debian and Ubuntu advisories list fixed versions for relevant releases.
- Patch: Apply kernel packages or vendor-provided kernel images. Reboot as required to load the updated kernel.
- Harden: Implement SELinux/AppArmor profiles to deny untrusted processes from writing to sysfs display attributes and review sudoers and SUID binaries to reduce local-privilege risk.
- Monitor: Add detection for unusual writes to fbdev sysfs nodes and kernel oops messages referencing fbcon or array-index errors. Maintain an incident response plan for any signs of memory-corruption or crashes following the fix rollout.
- Track embedded devices: Contact OEMs for appliances and IoT devices and schedule firmware/kernel updates where the device vendor is responsible for shipping patched kernels.
Transparency: What we confirmed and what remains uncertain
- Confirmed:
- The bug is an array-index-out-of-bounds in fbcon triggered by con2fb_map entries containing -1. This is documented by multiple vendor advisories and vulnerability trackers.
- The immediate trigger reported is writes to the store_modes sysfs node; the code-path and UBSAN trace support that claim.
- Upstream kernel fixes and distribution patches exist; Debian and other trackers list fixed kernel package versions for multiple branches.
- Unverified / cautionary:
- No public PoC or evidence of in-the-wild exploitation was found in public advisories and trackers consulted. This is current as of the advisories checked, but absence in public sources does not preclude private or targeted exploitation. Treat the “no PoC” status as provisional and continue to monitor vendor advisories and public exploit repositories.
- The exact impact on any given production workload depends on kernel configuration, distribution backports, and whether fbcon is enabled on that system — testing in a representative non-production environment is advised before mass deployments.
Conclusion
CVE-2025-38198 is a localized kernel memory-safety issue in the framebuffer console code that manifests when an unregistered console mapping is used as an array index. The fix is straightforward and has been released upstream and backported to multiple distribution kernels. Because the flaw requires local privileged write access to sysfs, its immediate danger to remote-facing systems is limited — however, the memory-corruption potential and the prevalence of fbdev in embedded and appliance kernels makes timely patching and vendor coordination essential. Administrators should prioritize kernel updates where possible, lock down sysfs write access where patching is delayed, and monitor affected systems for related kernel oops or instability indicators.Source: MSRC Security Update Guide - Microsoft Security Response Center