CVE-2026-31498 is a reminder that some of the most consequential kernel bugs are not dramatic buffer overflows or headline-grabbing remote exploits, but state-machine failures and validation gaps buried in long-lived protocol code. In this case, the Linux kernel’s Bluetooth L2CAP layer can be driven into an ERTM reinitialization leak and, separately, an infinite loop when a zero-length
The specific issue behind CVE-2026-31498 lives in the Bluetooth: L2CAP path for ERTM, the Enhanced Retransmission Mode. The CVE description says
The second half of mportant, and arguably more alarming from an availability perspective. The CVE record says
That combination matters because it blends of bug into one vulnerability record. One is a resource leak caused by double initialization. The other is an infinite loop / resource exhaustion condition caused by a missing lower-bound check. Either issue is bad on its own; together they paint a picture of a subsystem that was trusting state a little too much and validating it a little too late.
The upstream fix is conceptually simple, which is often a clue that the bug was hiding in a subtle branch condition rather than in a sprawling algorithm. The patch avoids the double initialization by skipping
That sort of fix is typically the right shape for kernel maintet preserves valid behavior, and it changes the contract only where the bug exists. In other words, the patch does not redesign Bluetooth; it teaches the existing code to stop trusting an impossible state.
At a high level, CVE-2026-31498 is a textbook example of why reconfiguration paths deserve as much scrutiny as first-time initialization paths. Developers usually think more carefully about the code that brings a channel up for the first time, because that is where object allocation and state setup are most obvious. But once a subsystem permits repeated configuration changes on an already connected channel, the state machine becomes more complicated, and the risk of reinitializing something that was meant to persist rises sharply.
The kernel description makes this plain.
This is why kernel networking bugs often survive review. The code can look reasonable when read linearly, because each step is individually legal. The problem appears only when the same path is entered a second time and an assumption that was true during first initialization becomes false during reconfiguration. That is also why the fix is so focused on skipping the reinitialization call rather than trying to patch up the leak after the fact.
That matters because kernel loops are not like ordinary application loops. A tight, unbounded loop in a protocol path can saturate CPU, keep allocating structures, and drive memory consumption upward until the system becomes unstable. In the worst case, the kernel can enter a denial-of-service spiral where the fix is not just “close a socket” but “reboot the machine.”
That is why these disclosures need careful reading. A “no CVSS yet” field does not mean “no urgency.” It often means only that the record is new enough that the scoring process has not settled. In practice, the kernel description and the fix tell us more than a placeholder severity rating would.
In the reinit case, the problem is that the channel is already in the connected state, yet the configuration code still wanders into the same setup routine used for initial bring-up. That routine re-creates
That is the kind of bug operators often underestimate because leaks feel less dramatic than corruptions. But in a long-running system, a leak is a slow-motion outage. If the Bluetooth stack is reconfigured repeatedly, the memory loss compounds. The symptoms may show up as degraded performance, allocation failures elsewhere in the kernel, or in extreme cases a machine that appears healthy until it suddenly is not.
The zero
The second defect is more obviously dangerous in terms of immediate availability. If
This is exactly why boundary checks matter in protocol code. Zero is not always an error in userland APIs, but in packet segmentation it often is. A function that slices data into chunks must have a nonzero chunk size or it cannot make progress. The bug is not subtle once described, but it is the sort of detail that can be missed if the code assumes upstream parsing already guaranteed a valid minimum.
The significance here is that the affected objects are not decorative.
This is one of the hardest parts of kernel hardening. The code is usually written to be fast and compact, and therefore it tends to compress a lot of logic into a small number of branches. That is efficient, but it also means a branch can become overloaded with meaning. When that happens, the chance of an unintended fall-through rises.
It also complicates diagnostics. A memory leak in protocol state often shows up far away from the source. By the time the system starts failing allocations, the original triggering activity may have ended, leaving only symptoms and no obvious culprit. That is why patches like this matter even when the issue does not read as dramatic as a code execution flaw.
It is also the sort of change that can backport well. Narrow fixes with clear behavioral intent are more likely to make it into stable kernels quickly, which is especially important for Bluetooth bugs that may affect a wide range of hardware shipped with vendor kernels. When a patch is small and obvious, maintainers can carry it with less risk.
Why the Zero
The infinite-loop half of this CVE is the more straightforward availability problem. Once
This kind of bug is especially dangerous because it is self-amplifying. The loop does not merely stall; it keeps executing until memory is exhausted. That makes it more than a simple bug. It becomes a resource sink that can degrade the host as it tries to recover or continue processing work. The CVE description explicitly says the condition can exhaust all available memory, which is the sort of symptom that turns a logic error into a system outage .
This is why proper validation usually belongs at the parser layer, not at the last possible moment. The kernel should reject impossible values as soon as it knows they are impossible. Doing so avoids spreading the bad state into helper routines that were never meant to defend against it.
In operational terms, this is the kind of bug that is easy to underestimate if you only look for immediate crashes. Systems can look “fine” while the loop is quietly building pressure. By the time administrators notice, the failure can already be systemic.
Why the safeguard in
Even if earlier validation is supposed to catch the bad value, the extra
That kind of redundancy is not overkill; it is realism. Kernel subsystems evolve, and assumptions made in one part of the stack can be broken by future changes in another. A local guard is often the cheapest insurance policy a maintainer can add.
For vendors and downstream distributions, the practical challenge is backporting. A bug like this needs to be fixed in the stable lines that ship to users, not just in the lhe kernel.org references in the record indicate multiple stable commit links were attached, which suggests maintainers have already prepared the usual backport pipeline . That is good news, because most production systems will consume the fix through vendor packages rather than by compiling mainline themselves.
It also reinforces an uncomfortable truth: the more integrated the device, the more likely a subtle kernel fault becomes a fleet issue. A bug that seems local in the source tree can become widespread simply because the subsystem is shipped everywhere. That is why defenders need to patch based on risk class, not only on whether they personally use Bluetooth every day.
The more relevant distinction is not consumer versus enterprise in the abstract, but active use versus passive presence. If the Bluetooth stack is frequently engaged, the bug matters more. If it is disabled or unused, the practical risk falls. But in a world where wireless peripherals, headsets, and nearby device interactions are ubiquitous, that is not a comforting escape hatch.
In that sense, the CVE is not just a security story. It is also a test of ecosystem hygiene. The faster the fix reaches stable trees and downstream packages, the less likely operators are to keep running a version with a hidden memory leak and a zero-length loop hazard.
The other positive is that the issue is relatively easy to reason about once described. The reinit problem and the zero-length segmentation problem are distinct, understandable, and each can be validated in code review or regression testing. That gives maintainers and distributors a real chance to land the patch quickly and confidently.
There is also the issue of underreaction. Because the CVE record did not yet have a final NVD score at publication time, some teams may assume they can wait for a more polished advisory before acting. That would be a mistake. The technical description already identifies a memory leak and a potential infinite loop, both of which are operationally meaningful regardless of the pending score .
The other item to watch is whether additional Bluetooth or ce around the same reconfiguration flow. Security work in the kernel often exposes neighboring assumptions, and once one path is tightened, adjacent paths are worth review. If a zero-length condition made it through in one spot, maintainers will likely want to confirm that similar minimum-value assumptions hold elsewhere too.
CVE-2026-31498 may not be the loudest kernel bug of the year, but it is exactly the kind of vulnerability that separates stable infrastructure from brittle infrastructure. The patch is small, the logic is clear, and the operational lesson is durable: never let reconfiguration masquerade as initialization, and never let a zero-length packet path decide it can keep going forever.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
pdu_len slips through segmentation logic. The result is a vulnerability that can quietly exhaust memory, destabilize a system, and leave administrators with a problem that looks routine on paper but ugly in production. Microsoft’s Security Update Guide has already picked up the CVE record, and the underlying fix was published by kernel.org with multiple stable references, which tells us this is not speculative theory but a concrete remediation path tooth stack bugs have a long history of showing how much complexity hides beneath ordinary consumer features. L2CAP, the Logical Link Control and Adaptation Protocol, sits at a foundational layer and is responsible for multiplexing and segmentation duties that most users never think about, precisely because the stack is expected to handle them invisibly. That invisibility is what makes these bugs so interesting from a security standpoint: when the code works, it is boring; when the code fails, it can fail in ways that are hard to diagnose and even harder to contain.The specific issue behind CVE-2026-31498 lives in the Bluetooth: L2CAP path for ERTM, the Enhanced Retransmission Mode. The CVE description says
l2cap_config_req() processes CONFIG_REQ requests for channels already in BT_CONNECTED, allowing reconfiguration such as MTU changes. But because both CONF_INPUT_DONE and CONF_OUTPUT_DONE may already be set from the original setup, the code can fall through into l2cap_ertm_init() again. That reinitializes several queues and lists without freeing the prior allocations, and it can also null out chan->sdu without releasing the existing skb, producing a leak of all previously allocated ERTM resources .The second half of mportant, and arguably more alarming from an availability perspective. The CVE record says
l2cap_parse_conf_req() does not validate the minimum value of remote_mps derived from the RFC max_pdu_size option. If that value becomes zero, it propagates to l2cap_segment_sdu(), where pdu_len also becomes zero. Once that happens, the while loop never makes progress because len is never decremented, so the kernel can spin forever and consume all available memory .That combination matters because it blends of bug into one vulnerability record. One is a resource leak caused by double initialization. The other is an infinite loop / resource exhaustion condition caused by a missing lower-bound check. Either issue is bad on its own; together they paint a picture of a subsystem that was trusting state a little too much and validating it a little too late.
The upstream fix is conceptually simple, which is often a clue that the bug was hiding in a subtle branch condition rather than in a sprawling algorithm. The patch avoids the double initialization by skipping
l2cap_ertm_init() and l2cap_chan_ready() when the channel is already in BT_CONNECTED, while still allowing l2cap_parse_conf_req() to update the reconfiguration parameters. It also adds a pdu_len == 0 safeguard in l2cap_segment_sdu() so the loop cannot run without progress .That sort of fix is typically the right shape for kernel maintet preserves valid behavior, and it changes the contract only where the bug exists. In other words, the patch does not redesign Bluetooth; it teaches the existing code to stop trusting an impossible state.
 Overview
Overview
At a high level, CVE-2026-31498 is a textbook example of why reconfiguration paths deserve as much scrutiny as first-time initialization paths. Developers usually think more carefully about the code that brings a channel up for the first time, because that is where object allocation and state setup are most obvious. But once a subsystem permits repeated configuration changes on an already connected channel, the state machine becomes more complicated, and the risk of reinitializing something that was meant to persist rises sharply.The kernel description makes this plain.
l2cap_config_req() is designed to support reconfiguration while the channel is in BT_CONNECTED, which means the function is not merely handling a one-shot handshake. It is part of the ongoing lifecycle of the channel. If the code assumes the same “done” flags always imply a fresh setup path, it can accidentally reenter initialization logic at exactly the wrong time. That is where the leak comes from: queues and lists are recreated without first releasing or resetting the prior allocations in a balanced way .Why this is a lifecycle bug, not just a coding typo
The important pattern here iunction names but the lifecycle mismatch. The channel is already live, but the code appears to treat the reconfiguration path like a cold-start path. That is a classic kernel mistake because object state is often encoded in flags, and flags can be easy to interpret too literally. If a flag means “configuration completed once,” it does not automatically mean “configuration should be repeated from scratch.”This is why kernel networking bugs often survive review. The code can look reasonable when read linearly, because each step is individually legal. The problem appears only when the same path is entered a second time and an assumption that was true during first initialization becomes false during reconfiguration. That is also why the fix is so focused on skipping the reinitialization call rather than trying to patch up the leak after the fact.
Why the zero-length case is especially dangerous
Thepdu_len == 0 issue is a different kind of logic failure, but it follows the same theme: a boundary value was not rejected early enough. In packet-splitting code, zero is not merely a small size; it is often a forbidden state because it destroys progress guarantees. If a loop depends on subtracting pdu_len from the remaining length, and pdu_len is zero, the loop’s termination condition is no longer meaningful.That matters because kernel loops are not like ordinary application loops. A tight, unbounded loop in a protocol path can saturate CPU, keep allocating structures, and drive memory consumption upward until the system becomes unstable. In the worst case, the kernel can enter a denial-of-service spiral where the fix is not just “close a socket” but “reboot the machine.”
What the CVE record tells us
The publication metadata is also useful context. The record says the CVE was newly received from kernel.org on April 22, 2026, and that NVD enrichment had not yet produced a final assessment at the time of publication . That is a familiar pattern for freshly published Linux kernel vulnerabilities. The technical description lanam scoring catches up later, and administrators are left to judge urgency from the nature of the bug rather than from a neat numerical label.That is why these disclosures need careful reading. A “no CVSS yet” field does not mean “no urgency.” It often means only that the record is new enough that the scoring process has not settled. In practice, the kernel description and the fix tell us more than a placeholder severity rating would.
How the Bug Manifests
The easiest way to understand CVE-2026-31498 is to follow the two failure chains separately and then see how they map to real-world symptoms. One chain produces leaked ERTM resources because the channel is reinitialized without freeing the prior objects. The other produces an endless segmentation loop because the packet size calculation can collapse to zero. Both can be triggered through ordinary configuration logic rather than through some exotic payload.In the reinit case, the problem is that the channel is already in the connected state, yet the configuration code still wanders into the same setup routine used for initial bring-up. That routine re-creates
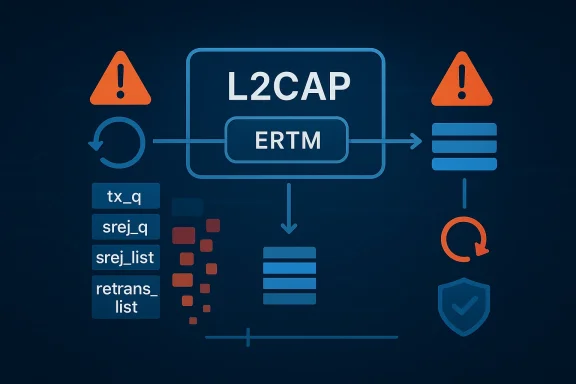
tx_q, srej_q, srej_list, and retrans_list, and it also sets chan->sdu to NULL while leaving the old skb behind. The result is a leak of all previously allocated ERTM resources, which means repeated reconfiguration can steadily chew through memory even if nothing “crashes” immediately .The ERTM reinitialization problem
ERTM is meant to improve reliability by giving the protocol retransmission and selective rose capabilities depend on internal queues and lists that track packet lifecycle. Reinitializing those structures without first freeing or otherwise retiring the old ones is a bookkeeping failure, not a protocol feature. It creates the illusion of a fresh state while the old allocations remain stranded.That is the kind of bug operators often underestimate because leaks feel less dramatic than corruptions. But in a long-running system, a leak is a slow-motion outage. If the Bluetooth stack is reconfigured repeatedly, the memory loss compounds. The symptoms may show up as degraded performance, allocation failures elsewhere in the kernel, or in extreme cases a machine that appears healthy until it suddenly is not.
The zero pdu_len path
The second defect is more obviously dangerous in terms of immediate availability. If remote_mps is allowed to become zero from the max_pdu_size option, l2cap_segment_sdu() may compute a zero pdu_len. Once the loop enters a state where it cannot subtract anything from the remaining length, it is no longer a loop in the useful sense; it is a machine designed to run until resources are exhausted.This is exactly why boundary checks matter in protocol code. Zero is not always an error in userland APIs, but in packet segmentation it often is. A function that slices data into chunks must have a nonzero chunk size or it cannot make progress. The bug is not subtle once described, but it is the sort of detail that can be missed if the code assumes upstream parsing already guaranteed a valid minimum.
Practical symptoms administrators might see
The likely user-visible effects are not always neat kernel panics. Some systems may simply become sluggish or start leaking memory in ways that are hard to correlate with Bluetooth activity. Others may show abrupt instability after repeated pairing, reconnection, or configuration changes.- Progressive memory growth after repeated L2CAP reconfiguration.
- Bluetooth subsystem instability under repeated connected-state config requests.
- Soft lockups or hangs if the zero
pdu_lenpath is hit. - Out-of-memory pressure in workloads that keep the Bluetooth stack active.
- Difficult-to-trace resource retention because the leak is in protocol bookkeeping rather than obvious user memory.
Why ERTM Re-init Is a Big Deal
A lot of kernel bugs become severe not because a single call is wrong, but because the code repeats an assumption that was only safe during first initialization. That appears to be the core of the ERTM half of this CVE. The channel state machine already knows it is connected, but the logic seems to re-enter a setup flow that was never meant to be run twice without cleanup.The significance here is that the affected objects are not decorative.
tx_q, srej_q, srej_list, and retrans_list are part of ERTM’s internal machinery, so leaking or duplicating them does more than waste memory. It erodes the correctness of the retransmission path itself. The protocol may continue operating, but with behind-the-scenes allocations piling up in a way that the normal lifecycle never expected.The state-machine lesson
The most valuable lesson is that “already connected” does not mean “safe to reinitialize.” In kernel code, flags often get used as shorthand for a bundle of invariants, but those invariants must be read carefully. If a path was designed for a one-time setup sequence, reusing it during an in-band reconfiguration can have side effects that are invisible until they accumulate.This is one of the hardest parts of kernel hardening. The code is usually written to be fast and compact, and therefore it tends to compress a lot of logic into a small number of branches. That is efficient, but it also means a branch can become overloaded with meaning. When that happens, the chance of an unintended fall-through rises.
Why the leak matters even if the machine doesn’t crash
Leaking kernel resources is not a “minor” defect. In practical terms, it means the system becomes less predictable over time. On a laptop, a Bluetooth leak might be irritating. On embedded hardware or an always-on system, it can be serious. If the machine is expected to manage repeated device interactions, every lost allocation is a little less headroom for the next one.It also complicates diagnostics. A memory leak in protocol state often shows up far away from the source. By the time the system starts failing allocations, the original triggering activity may have ended, leaving only symptoms and no obvious culprit. That is why patches like this matter even when the issue does not read as dramatic as a code execution flaw.
Why the fix is a good one
The upstream response is elegant because it preserves the legitimate reconfiguration path while refusing to double-initialize the already connected channel. In other words, the fix separates parameter update from object re-creation. That is exactly the distinction the code needed.It is also the sort of change that can backport well. Narrow fixes with clear behavioral intent are more likely to make it into stable kernels quickly, which is especially important for Bluetooth bugs that may affect a wide range of hardware shipped with vendor kernels. When a patch is small and obvious, maintainers can carry it with less risk.
- Reconfiguration is still allowed.
- The channel is no longer forced through a duplicate init path.
- Existing ERTM allocations are not silently discarded or leaked.
- The patch minimizes collateral behavior changes.
- Stable backports should be relatively straightforward.
Why the Zero pdu_len Loop Matters
The infinite-loop half of this CVE is the more straightforward availability problem. Once l2cap_segment_sdu() reaches a state where pdu_len is zero, the loop that depends on reducing len stops having a terminating condition. That is a classic kernel anti-pattern: a loop that assumes progress, but does not verify it.This kind of bug is especially dangerous because it is self-amplifying. The loop does not merely stall; it keeps executing until memory is exhausted. That makes it more than a simple bug. It becomes a resource sink that can degrade the host as it tries to recover or continue processing work. The CVE description explicitly says the condition can exhaust all available memory, which is the sort of symptom that turns a logic error into a system outage .
Why zero is not a harmless edge case
Developers sometimes think zero deserves special treatment because it is a “valid integer” even if it is an iue. In segmentation code, though, zero is often a red flag. A packetizer must be able to consume the source data in chunks. If the chunk size is zero, then no consumption occurs, and any loop built around consumption becomes stuck.This is why proper validation usually belongs at the parser layer, not at the last possible moment. The kernel should reject impossible values as soon as it knows they are impossible. Doing so avoids spreading the bad state into helper routines that were never meant to defend against it.
The memory-exhaustion angle
The real hazard here is not only CPU burn. The description says the loop can keep allocating until all memory is exhausted. That means this is not just a hang; it is a path to broad system degradation. Once memory pressure rises, unrelated subsystems begin failing too. Logging may falter, background workers may stall, and the OOM killer may become part of the drama.In operational terms, this is the kind of bug that is easy to underestimate if you only look for immediate crashes. Systems can look “fine” while the loop is quietly building pressure. By the time administrators notice, the failure can already be systemic.
Why the safeguard in l2cap_segment_sdu() matters
Even if earlier validation is supposed to catch the bad value, the extra pdu_len == 0 check is sensible defense in depth. Kernel code benefits from a belt and suspenders approach where an obviously invalid state is blocked twice, especially when one of the blocks sits inside a complex protocol path. The safeguard ensures that even if parsing logic regresses later, the segmentation loop still cannot become self-sustaining.That kind of redundancy is not overkill; it is realism. Kernel subsystems evolve, and assumptions made in one part of the stack can be broken by future changes in another. A local guard is often the cheapest insurance policy a maintainer can add.
- Zero-length packet units are not merely inefficient; they are unsafe in loop-based segmentation.
- Progress guarantees should be explicit, not inferred.
- Parser validation and runtime safeguards solve different parts of the problem.
- Memory exhaustion is a realistic outcome, not a hypothetical one.
- The patch hardens both input handling and execution safety.
Competitive and Ecosystem Implications
While this is a Linux kernel vulnerability, its impact is not confined to Linux enthusiasts or Bluetooth hobbyists. The presence of the CVE in Microsoft’s Security Update Guide underscores how Linux kernel issues now live inside a broader enterprise coordination ecosystem. That matters because modern organizations increasingly track Linux remediation alongside Windows, cloud, and endpoint updates in the same governance workflow .For vendors and downstream distributions, the practical challenge is backporting. A bug like this needs to be fixed in the stable lines that ship to users, not just in the lhe kernel.org references in the record indicate multiple stable commit links were attached, which suggests maintainers have already prepared the usual backport pipeline . That is good news, because most production systems will consume the fix through vendor packages rather than by compiling mainline themselves.
Why enterprise buyers should care
Enterprise cusux kernel Bluetooth” as a standalone feature, but they absolutely buy devices and systems that embed it. That includes laptops, industrial gateways, field systems, and specialized appliances. If one of those devices relies on Bluetooth for provisioning, telemetry, or maintenance, then a protocol-leak plus infinite-loop bug is not a niche curiosity. It is a support problem.It also reinforces an uncomfortable truth: the more integrated the device, the more likely a subtle kernel fault becomes a fleet issue. A bug that seems local in the source tree can become widespread simply because the subsystem is shipped everywhere. That is why defenders need to patch based on risk class, not only on whether they personally use Bluetooth every day.
Why consumer impact is different
Consumer desktops may feel less exposed because many users do not repeatedly reconfigure Bluetooth channels in the way embedded or enterprise systems do. But “less exposed” is not the same as “safe.” Bluetooth is one of the few kernel subsystems that sits close to ordinary user behavior while still operating at kernel privilege. That makes it a persistent attack surface and a recurring stability concern.The more relevant distinction is not consumer versus enterprise in the abstract, but active use versus passive presence. If the Bluetooth stack is frequently engaged, the bug matters more. If it is disabled or unused, the practical risk falls. But in a world where wireless peripherals, headsets, and nearby device interactions are ubiquitous, that is not a comforting escape hatch.
The broader competitive picture
From a platform perspective, every kernel hardening event like this strengthens the case for rigorous upstream tracking and rapid vendor synchronization. Linux distributions compete partly on how quickly they ingest and backport fixes without breaking user space. Bugs like CVE-2026-31498 reward that discipline. They also punish vendors that lag on stable patch integration, because the remediation is straightforward enough to be expected.In that sense, the CVE is not just a security story. It is also a test of ecosystem hygiene. The faster the fix reaches stable trees and downstream packages, the less likely operators are to keep running a version with a hidden memory leak and a zero-length loop hazard.
Strengths and Opportunities
The good news is that this vulnerability has a clean, targeted fix. It does not require a redesign of Bluetooth, and it does not demand a risky semantic change to the L2CAP stack. That is important because the best security patches are often the ones that solve the problem at the exact boundary where it occurs.The other positive is that the issue is relatively easy to reason about once described. The reinit problem and the zero-length segmentation problem are distinct, understandable, and each can be validated in code review or regression testing. That gives maintainers and distributors a real chance to land the patch quickly and confidently.
- Narrow patch scope reduces the chance of collateral regressions.
- Early input validation improves the API contract for future callers.
- Defense in depth with the
pdu_lensafeguard lowers recurrence risk. - Stable backport suitability should help downstream adoption.
- Clear failure mode makes test coverage easier to design.
- Protocol state cleanup improves long-term maintainability.
- Reconfiguration support remains intact, which is the right balance for existing users.
Risks and Concerns
The biggest concern is that the bug can look like a routine Bluetooth glitch until it has already done damage. A leak in the ERTM lifecycle may not explode immediately, and a zero-length segmentation loop may manifest only under unusual configuration conditions. That means the bug can hide in plain sight for longer than administrators would like.There is also the issue of underreaction. Because the CVE record did not yet have a final NVD score at publication time, some teams may assume they can wait for a more polished advisory before acting. That would be a mistake. The technical description already identifies a memory leak and a potential infinite loop, both of which are operationally meaningful regardless of the pending score .
- Silent memory leaks can accumulate before anyone notices.
- Zero-length segmentation can lead to a runaway loop.
- Reconfiguration-only triggers may evade routine testing.
- **Build and distro differenceinconsistent.
- Downstream patch lag could leave fleets exposed longer than expected.
- Lack of a final score yet may mislead teams into delaying remediation.
- Bluetooth’s ordinary appearance may cause teams to underestimate the subsystem.
Looking Ahead
The next thing to watch is how quickly the fix makes its way into vendor kernels and long-term support branches. The presence of stable commit references in the CVE record is encouraging, because it suggests the remediation has already entered the upstream maintenance pipeline . For most users, that means the practical question will be whether their distribution has backported the relevant change rather than whether they need to chase mainline themselves.The other item to watch is whether additional Bluetooth or ce around the same reconfiguration flow. Security work in the kernel often exposes neighboring assumptions, and once one path is tightened, adjacent paths are worth review. If a zero-length condition made it through in one spot, maintainers will likely want to confirm that similar minimum-value assumptions hold elsewhere too.
Items to monitor
- Vendor advisories announcing backported fixes.
- Stable kernel release notes referencing the L2CAP patch.
- Distribution errata that map the CVE to package versions.
- Any follow-on Bluetooth fixes that touch reconfiguration or segmentation.
- Reports of memory leaks or hangs in Bluetooth-heavy deployments.
CVE-2026-31498 may not be the loudest kernel bug of the year, but it is exactly the kind of vulnerability that separates stable infrastructure from brittle infrastructure. The patch is small, the logic is clear, and the operational lesson is durable: never let reconfiguration masquerade as initialization, and never let a zero-length packet path decide it can keep going forever.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center