CVE-2026-31512 is a small-looking Linux kernel flaw with the kind of security significance that only packet-processing code can really deliver. The issue sits in the Bluetooth L2CAP path, where
The L2CAP layer is a core part of Bluetooth’s plumbing. It handles logical channels and segmentation/reassembly behavior, which means it often sits at the exact point where higher-level protocol assumptions meet raw packet data. That is also why these bugs tend to look deceptively small. A single unchecked length field can turn into an out-of-bounds read, a kernel warning, a crash, or a memory disclosure depending on the surrounding code and build configuration.
This particular CVE is notable because the fix is not a redesign. It is a validation adjustment: check the packet length before trying to interpret the SDU length field. That sounds ordinary, but ordinary is often what security hardening looks like in mature kernel code. The best fixes in this space usually do not invent new abstractions; they make sure the kernel only touches memory after the preconditions are satisfied. That is especially true in networking code, where performance pressure can sometimes tempt developers to assume the buffer is already in the expected shape.
The NVD record lists the issue as newly received from kernel.org and explicitly notes that NVD enrichment had not yet produced a CVSS score at the time of publication. That matters operationally because defenders cannot rely on a preassigned severity number to decide urgency. They have to make the call from the technical description itself, and from the broader context of how Bluetooth bugs tend to behave in real systems. The record also cites several stable commit references, which suggests the fix is already flowing through the normal Linux backport pipeline rather than waiting on a theoretical future patch.
The strongest histo the same subsystem is the ERTM reassembly path. There, the kernel already uses
The important part is not just the read itself, but the trustnel networking code often assumes a packet has already been shaped by prior layers, but that assumption only remains safe if every path enforces the same minimum-length discipline. When one path validates and another does not, you get inconsistent safety behavior that depends on which protocol mode was selected. That is how bugs survive code review: the code looks correct in one branch, and the analogous branch quietly misses the guard.
The broader lesson is that packet parsers should validate before they interpret. That is especially true for length-prefixed protocols, where the first field often determines how much additional state the kernel will trust next. The fix for CVE-2026-31512 follows that principle by forcing the data path to establish that the buffer contains the required SDU length field before dereferencing it.
This is why Linux maintainers so often prefer early rejection over late correction. Once the code has already dereferenced invalid data, the safe outcome has partly been lost. The bug might still only manifest as a warning on many builds, but the absence of a dramatic symptom should never be mistaken for the absence of impact. Quiet memory errors are often the ones that linger longest.
The Role of
The fix description makes one specific comparison that matters a reassembly path correctly calls
That is a familiar pattern in kernel security. A single subsystem often evolves multiple protocol variants over time, and thith nearly identical parsing logic. The danger appears when one branch gets hardened and the parallel branch does not. The result is not a wholly new design flaw but an implementation drift problem, where safety rules no longer line up across code paths that should have stayed in sync.
The CVE is also a reminder that secure coding in the kernel often means respecting existing patterns rather than inventing new ones. If one part of a subsystem already demands a buffer precondition, then related paths should not improvise a different rule without a very good reason. Here, there was no such reason visible in the public description, which makes the missing validation look exactly like the kind of omission that fuzzers and sanitizers are good at surfacing.
Because Bluetooth often feels like a consumer feature, organizations sometimes underestimate its presence in enterprise fleets. That is a mistake. Bluetooth radios shn clients, embedded endpoints, edge systems, and specialized equipment. Even when a device is not intended to be “managed by Bluetooth,” the stack may still be enabled for peripherals, provisioning, diagnostics, or local maintenance workflows. The attack surface is therefore broader than the average asset inventory suggests.
For enterprises, the concern is operational consistency. A kernel bug in Bluetooth can become a reliability issue on fleets where wireless peripherals are part of daily work, where mobile device provisioning relies on local connectivity, or where engineering and field-service teams use Bluetooth for diagnostics. Even a bug that only causes memory safety issues under narrow conditions can create a support burden if it lands on many endpoints at once. That is why “low probability” and “low priority” are not the same thing.
This also reflects a larger trend in kernel hardening. A lot of modern Linux security work is about making sure that code respects packet size, state lifecycle, and boundary conditions before it touches data.us than an exploit-chain patch, but it is often more important in practice because it removes the conditions that fuzzers, malformed peers, and edge-case hardware can exploit repeatedly.
It also helps that the validation logic is already established elsewhere in the subsystem. That gives maintainers a clear precedent and provides downstream vendors with a stronger basis for carrying the patch into their own kernels. When code already has a known-safe pattern, the right move is usually to apply that pattern consistently, not to invent a second version of safety. Uniformity is a security feature.
The second step is to understand where Bluetooth matters inside your organization. Some fleets use it constantly; others disable it entirely. But many organizations live in the middle: laptops with headsets, conference-room peripherals, mobile provis specialized devices that quietly depend on the stack. Those are the systems where a Bluetooth kernel flaw becomes operationally relevant. In mixed fleets, hidden exposure is common.
Consumers also tend to rely on vendors to silently absorb fixes. That means the absence of an obvious crash does not mean the system is unaffected. A corrected kernel can be sitting in a pending update while the user continues pairing headphones or keyboards without realizing the underlying one reason security communication from vendors matters so much in the consumer space: the user often cannot see the risk directly.
Another point that matters is the old security rule that “it’s just Bluetooth” is not a safe assumption. Short-range wireless can still be part of a meaningful attack chain, especially when the weak link is in kernel parsing rather than in a user-facing application. The absence of a flashy exploit writeup does not reduce the value of patching. It only means the bug is being reported at the layer where it actually lives.
A third concern is patch visibility. Because this is a kernel fix and because vendors often backport aggressively, the presence of a patched upstream commit does not guarantee that your deployed fleet has the fix. That gap is especially dangerous in enterprise environments where the operating-system version and the shipped kernel pae thing. The fourth concern is operational complacency: a vulnerability without a CVSS score can be treated as “unprioritized” when it should really be treated as “not yet numerically scored.”
The second thing to watch is whether maintainers use this as an opportunity to compare the ecred path against other Bluetooth receive functions. If one branch forgot the
The broader takeaway is that CVE-2026-31512 is the kind of Linux kernel issue that rarely makes a splash on its own but quietly reinforces an important rule: every packet parser must prove its preconditions before it trusts memory. In Bluetooth, where packets arrive from nearby devices and protocol behavior can be messy, that rule matters even more. If downstream vendors shd quickly, this CVE will likely fade into the long list of small but necessary kernel corrections. If they do not, it will become another reminder that tiny validation mistakes can carry outsize consequences once they sit inside the operating system’s networking core.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
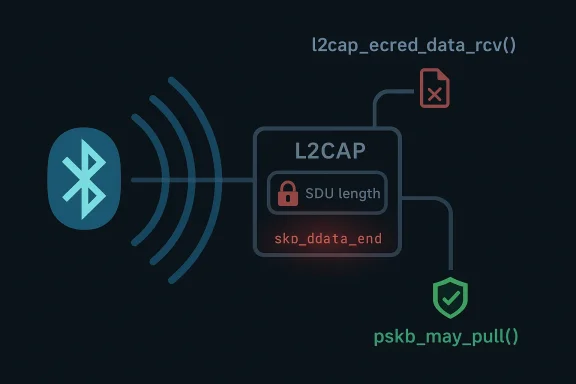
l2cap_ecred_data_rcv() can read the SDU length field before first confirming that the incoming skb actually contains the two bytes required for that read. In plain English, that means a malformed Bluetooth packet can push the kernel into reading past the valid data boundary, which is exactly the sort of bug that should make administrators pay attention even before a final severity score appears. The upstream fix mirrors a validation pattern already used in the ERTM reassembly path, which is a strong sign that the bug is less about exotic logic and more about a missing safety check in one of Bluetooth’s data paths. The CVE was published to the NVD on April 22, 2026, and the record points back to kernel.org as the originating source. tooth vulnerabilities in the Linux kernel have become a recurring theme over the last several years, and the reason is not hard to see. Bluetooth is simultaneously consumer-facing and deeply embedded, which means the same code can matter on a laptop, a phone-adjacent accessory host, an industrial gateway, or a server with a short-range radio attached. That creates a broad and uneven attack surface, with some systems exposed constantly and others only occasionally. When the bug lives inside kernel protocol parsing, the practical question is rarely whether the flaw is “real”; it is whether the affected path is reachable often enough to matter in your environment.The L2CAP layer is a core part of Bluetooth’s plumbing. It handles logical channels and segmentation/reassembly behavior, which means it often sits at the exact point where higher-level protocol assumptions meet raw packet data. That is also why these bugs tend to look deceptively small. A single unchecked length field can turn into an out-of-bounds read, a kernel warning, a crash, or a memory disclosure depending on the surrounding code and build configuration.
This particular CVE is notable because the fix is not a redesign. It is a validation adjustment: check the packet length before trying to interpret the SDU length field. That sounds ordinary, but ordinary is often what security hardening looks like in mature kernel code. The best fixes in this space usually do not invent new abstractions; they make sure the kernel only touches memory after the preconditions are satisfied. That is especially true in networking code, where performance pressure can sometimes tempt developers to assume the buffer is already in the expected shape.
The NVD record lists the issue as newly received from kernel.org and explicitly notes that NVD enrichment had not yet produced a CVSS score at the time of publication. That matters operationally because defenders cannot rely on a preassigned severity number to decide urgency. They have to make the call from the technical description itself, and from the broader context of how Bluetooth bugs tend to behave in real systems. The record also cites several stable commit references, which suggests the fix is already flowing through the normal Linux backport pipeline rather than waiting on a theoretical future patch.
The strongest histo the same subsystem is the ERTM reassembly path. There, the kernel already uses
pskb_may_pull() before reading the SDU length in the L2CAP_SAR_START case. The CVE description explicitly says the Enhanced Credit Based Flow Control path should apply the same validation. That is a useful clue: the bug is not a novel protocol flaw so much as an inconsistency between two similar data paths, one of which already had the guardrail and one of which did not.
 What the Vulnerability Actually level, the flaw is simple enough to summarize in one sentence:
What the Vulnerability Actually level, the flaw is simple enough to summarize in one sentence: l2cap_ecred_data_rcv() reads two bytes from skb->data using get_unaligned_le16() without first proving that those two bytes exist. If skb->len is less than 2, the read crosses beyond valid packet data and into memory the kernel should not be interpreting. That is a classic bounds-checking failure, and in kernel code, classic does not mean harmless.
The important part is not just the read itself, but the trustnel networking code often assumes a packet has already been shaped by prior layers, but that assumption only remains safe if every path enforces the same minimum-length discipline. When one path validates and another does not, you get inconsistent safety behavior that depends on which protocol mode was selected. That is how bugs survive code review: the code looks correct in one branch, and the analogous branch quietly misses the guard.Why the missing check matters
A 2-byte read does not sound dramatic, but in a kernel context the size of the access is less important than the fact that the access is unsanctioned. Out-of-bounds reads can crash under sanitizers, expose stale data, or trigger undefined behavior depending on the exact memory layout and compiler assumptions. Even when the immediate effect is “only” a read past the end of the skb, the underlying condition is still a memory-safety defect.The broader lesson is that packet parsers should validate before they interpret. That is especially true for length-prefixed protocols, where the first field often determines how much additional state the kernel will trust next. The fix for CVE-2026-31512 follows that principle by forcing the data path to establish that the buffer contains the required SDU length field before dereferencing it.
- The vulnerable code path reads from
skb->datatoo early. - The required bufferes, but the kernel never confirms those bytes are present first.
- The flaw is in the Enhanced Credit Based Flow Control path.
- The analogous ERTM path already performs the correct validation.
- The fix is to add the same pre-read safety check to this code path.
What makes this a kernel bug, not just a protocol quirk
In userspace, a malformed packet parser bug often leads to a clean exception or a contained process crash. In kernel space, the same mistake lives much closer to the operating system’s trust boundary. That is why even a narrow read-past-end condition can become a reliability problem, a disclosure primitive, or a stepping stone for follow-on exploitation if another weakness exists nearby. The kernel is not merely processing the packet; it is enforcing the machine’s memory rules while doing so.This is why Linux maintainers so often prefer early rejection over late correction. Once the code has already dereferenced invalid data, the safe outcome has partly been lost. The bug might still only manifest as a warning on many builds, but the absence of a dramatic symptom should never be mistaken for the absence of impact. Quiet memory errors are often the ones that linger longest.
The Role of pskb_may_pull()
The fix description makes one specific comparison that matters a reassembly path correctly calls pskb_may_pull() before reading the SDU length. That helper is the kernel’s way of ensuring the necessary data is actually linear and present in the skb before a read is attempted. In other words, the code already knew how to do this safely elsewhere; the vulnerability existed because the ecred path failed to borrow the same habit.That is a familiar pattern in kernel security. A single subsystem often evolves multiple protocol variants over time, and thith nearly identical parsing logic. The danger appears when one branch gets hardened and the parallel branch does not. The result is not a wholly new design flaw but an implementation drift problem, where safety rules no longer line up across code paths that should have stayed in sync.
Why helper reuse matters
Helpers likepskb_may_pull() are more than convenience wrappers. They encode collective hard-won knowledge about buffer handling, linearity, and packet access rules. Using them consistently reduces the odds that one parser path will subtly diverge from another under pressure from optimization or code churn. That consistency is a form of security control, even if the code itself does not look “security-oriented.”The CVE is also a reminder that secure coding in the kernel often means respecting existing patterns rather than inventing new ones. If one part of a subsystem already demands a buffer precondition, then related paths should not improvise a different rule without a very good reason. Here, there was no such reason visible in the public description, which makes the missing validation look exactly like the kind of omission that fuzzers and sanitizers are good at surfacing.
pskb_may_pull()validates that the skb has enough accessible data.- It prevents parsers from reading fields that may not be present yet.
- Tused this protection correctly.
- The ecred path should have matched that behavior from the start.
- Reusing trusted helpers reduces the odds of branch-specific regressions.
Why this matters for Bluetooth more broadly
Bluetooth code has to deal with small packets, fragmented state, and a wide range of device behaviors. Those are all conditions that can magnify the consequences of a missing bounds check. Unlike a simple file parser, Bluetooth paths are often exercised by transient radio events and imperfect peer behavior, which makes them harder to reason about by inspection alone. That is one reason Bluetooth remains a steady source of kernel fixes: the subsystem sits at the intersection of wireless unpredictability and low-level memory discipline. That combination is inherently fragile.Exposure and Attack Surface
The first question defenders ask is always the same: who can reach it? For CVE-2026-31512, the answer is any system that exposes the relevant Bluetooth L2CAP data path to malformed input. In practical terms, that means the exposed surface is tied to Bluetooth connectivity, Bluetooth-enabled Linux systems, and whatever kernels or distributions have this code path compiled in and reachable. The CVE text does not claim a final exploitability rating, but it does describe a real read past valid data, and that is enough to justify attention.Because Bluetooth often feels like a consumer feature, organizations sometimes underestimate its presence in enterprise fleets. That is a mistake. Bluetooth radios shn clients, embedded endpoints, edge systems, and specialized equipment. Even when a device is not intended to be “managed by Bluetooth,” the stack may still be enabled for peripherals, provisioning, diagnostics, or local maintenance workflows. The attack surface is therefore broader than the average asset inventory suggests.
Consumer vs enterprise impact
For consumers, the immediate risk is probably concentrated in the usual place: systems that keep Bluetooth enabled and routinely interact with nearby devices. That includes laptops in dense environments, workstations with headsets and keyboards, and systems that pair and unpair devices frequently. The plausible impact here is not necessarily dramatic remote takeover; it is more likely a crash, warning, or other abnormal behavior if the malformed path is reached.For enterprises, the concern is operational consistency. A kernel bug in Bluetooth can become a reliability issue on fleets where wireless peripherals are part of daily work, where mobile device provisioning relies on local connectivity, or where engineering and field-service teams use Bluetooth for diagnostics. Even a bug that only causes memory safety issues under narrow conditions can create a support burden if it lands on many endpoints at once. That is why “low probability” and “low priority” are not the same thing.
Why the publication timeline matters
The CVE record was published on April 22, 2026, and it arrived with NVD enrichment still incomplete. That timing suggests defenders should not wait for a polished severity label before checking their exposure. When a kernel issue is freshly published, especially one tied to stable commits, the practical response is to confirm whether your vendor kernels already carry the fix or whether they are still pending backport. Waiting for the score is often the slowest possible way to prioritize a kernel issue.- Bluetooth exposure is broader than many asset inventories assume.
- Consumer endpoints are more likely to see direct radio proximity exposure.
- Enterprise fleets care about availabilit much as exploitability.
- Fresh CVEs with incomplete enrichment still warrant immediate triage.
- Vendor backports matter more than headline kernel version numbers.
How the Fix Fits Linux Security Practice
The beauty of the fix is its restraint. The kernel does not need a sweeping refactor or a new packet abstraction to close the hole. It needs the same pre-read validation that already exists in a closely related path. That kind of patch is typical of Linux security maintenance at its best: narrow, understandable, and aimed at the exact point where trust should begin.This also reflects a larger trend in kernel hardening. A lot of modern Linux security work is about making sure that code respects packet size, state lifecycle, and boundary conditions before it touches data.us than an exploit-chain patch, but it is often more important in practice because it removes the conditions that fuzzers, malformed peers, and edge-case hardware can exploit repeatedly.
Why narrow fixes are usually the right ones
A narrow fix reduces regression risk. In networking code, broad changes can create as many problems as they solve because they perturb hot paths that are already performance-sensitive. By contrast, adding a missing length check before a read usually preserves the rest of the logic while closing the unsafe path. That makes the patch easier to backport and easier for downstream maintainers to trust.It also helps that the validation logic is already established elsewhere in the subsystem. That gives maintainers a clear precedent and provides downstream vendors with a stronger basis for carrying the patch into their own kernels. When code already has a known-safe pattern, the right move is usually to apply that pattern consistently, not to invent a second version of safety. Uniformity is a security feature.
- The fix is small enough to backport cleanly.
- It aligns the ecred path with the existing ERTM reassembly approach.
- It minimizes the chance of introducing a new regression.
- It improves maintainability by unifying validation behavior.
- It fits the kernel’s long-standing “validate before dereference” discipline.
What this says about fuzzing and sanitizers
This kind of bug is exactly what the Linux kernel’s testing ecosystem is built to find. Bounds checks, access order, and packet-length assumptions are all targets for fuzzing and runtime sanitizers. The fact that the public description calls out the specific missing validation suggests the issue was sufficiently concrete that it could be fixed directly, rather than requiring a broad redesign of the protocol stack. That is good news, because it usually means the remediation path is straightforward. It is also a reminder that better test coverage in one path can illuminate weaknesses in a sibling path that never got the same scrutiny.Enterprise Patch Prioritization
When a kernel CVE lands without a final NVD score, enterprise teams should resist the temptation to classify it as “wait and see.” The better approach is to ask three questions immediatelyd, is the affected kernel path present, and has the vendor already shipped the backport? That triage model is more valuable than a generic severity label because it maps directly to deployment reality.The second step is to understand where Bluetooth matters inside your organization. Some fleets use it constantly; others disable it entirely. But many organizations live in the middle: laptops with headsets, conference-room peripherals, mobile provis specialized devices that quietly depend on the stack. Those are the systems where a Bluetooth kernel flaw becomes operationally relevant. In mixed fleets, hidden exposure is common.
Practical prioritization steps
- Identify whether Bluetooth is enabled on production endpoints and managed devices.
- Check vendor advisories or package notes for the specific backported fix.
- Prioritize laptops, field devices, and radio-enabled embedded endpoints first.
- Validate whether local policy or hardware design makes Bluetooth externally reachable.
- Track the CVE as a kernel maintenance item even if the exploit path appears narrow.
Why version numbers can mislead
On Linux, the visible version string is only part of the story. Vendors frequently backport security fixes without bumping to the exact upstream version that first contained the patch. That means administrators need to verify package changelogs, vendor bulletins, or kernel build metadata rather than rely only onuname -r. This is especially important in enterprise Linux distributions and appliance-style deployments, where the fix may be present long before the underlying release train looks “new” to an outsider.- Check Bluetooth enablement, not just operating system type.
- Verify backports from the vendor side, not only upstream.
- Treat laptops and embedded radio-enabled systems as likely exposure points.
- Build the CVE into routine patch cycles for fleet governance.
- Assuman hide a fixed build.
Consumer Implications
For typical consumers, CVE-2026-31512 is probably less alarming than some of the more dramatic kernel bugs that circulate in the wild. Most users are not staging Bluetooth packets by hand, and most desktop interactions will never hit the malformed edge case. But that should not be mistaken for irrelevance. Kernel bugs in common connectivity stacks are worth patching precisely because users can do everything “normally” and still remain exposed to malformed nearby traffic.Consumers also tend to rely on vendors to silently absorb fixes. That means the absence of an obvious crash does not mean the system is unaffected. A corrected kernel can be sitting in a pending update while the user continues pairing headphones or keyboards without realizing the underlying one reason security communication from vendors matters so much in the consumer space: the user often cannot see the risk directly.
What consumer users should care about
The most important thing is to keep devices updated, especially laptops and systems that leave Bluetooth enabled at all times. If a vendor has published a kernel update that includes the fix, installing it is usually the right answer even if the device appears to work perfectly. The second point is to be aware of your threat environment. Dense public spaces, offices, and shared environments naturally create more opportunity for malformed wireless traffic to exist near your device.Another point that matters is the old security rule that “it’s just Bluetooth” is not a safe assumption. Short-range wireless can still be part of a meaningful attack chain, especially when the weak link is in kernel parsing rather than in a user-facing application. The absence of a flashy exploit writeup does not reduce the value of patching. It only means the bug is being reported at the layer where it actually lives.
- Keep Bluetooth-capable devices updated promptly.
- Do not assume “no obvious symptom” means “no exposure.”
- Pay extra attention to laptops used in public or shared spaces.
- Treat vendor-pushed kernel updates as security fixes, not optional polish.
- Remember that nearby wireless attack surface can still matter.
The likely user-visible symptom
The public description does not promise a dramatic exploit outcome. The more likely visible consequences are warning conditions, instability, or a crash if the malformed path is exercised under the right circumstances. That may sound modest, but in a desktop or mobile setting even intermittent instability can be serious if it affects peripherals, pairing workflows, or system reliability. In consumer support terms, small kernel bugs often look like “Bluetooth is flaky” long before anyone recognizes a CVE is behind them.Risks and Concerns
The most obvious concern is that out-of-bounds reads in kernel networking code are never just theoretical. Even if this flaw initially appears to be a narrow read-past-end condition, any kernel memory boundary issue deserves prompt attention because it may produce crashes, warnings, oosure. The second concern is exposure ambiguity: Bluetooth availability varies so widely across systems that many organizations may not realize how many endpoints can actually reach the vulnerable code.A third concern is patch visibility. Because this is a kernel fix and because vendors often backport aggressively, the presence of a patched upstream commit does not guarantee that your deployed fleet has the fix. That gap is especially dangerous in enterprise environments where the operating-system version and the shipped kernel pae thing. The fourth concern is operational complacency: a vulnerability without a CVSS score can be treated as “unprioritized” when it should really be treated as “not yet numerically scored.”
Risk factors to keep in view
- The bug is in kernel memory handling, not a benign user-space parser.
- Bluetooth exposure can be broader than administrators expect.
- Vendor backports may hide the real fix behind familiar version numbers.
- NVD scoring was not yet available at publication time.
- Quiet bugs can still be operationally disruptive if they affect fleets.
- Similar code paths in the subsystem may hide adjacent issues.
- Systems used in public or dense radio environments face more exposure.
What to Watch Next
The next major development will be how quickly downstream vendors absorb the fix into supported kernels. Because the CVE record already references stable commits, the code change is real and available, but enterprise value comes from seeing that change land in the exact builds people run. The gap between upstream and vendor-fixed can be short, but on mixed fleets it is still long enough to matter.The second thing to watch is whether maintainers use this as an opportunity to compare the ecred path against other Bluetooth receive functions. If one branch forgot the
pskb_may_pull()-style guard, there may be neighboring code that deserves a second look. That kind of follow-on review is often where the real long-term security gain happens.Whar kernel advisories and backport notes.
- Distribution package changelogs for Bluetooth/L2CAP fixes.
- Any follow-up patches in related L2CAP receive paths.
- Security tooling that maps the CVE to actual installed kernel builds.
- Bug-fix discussions that mention similar validation gaps.
The broader takeaway is that CVE-2026-31512 is the kind of Linux kernel issue that rarely makes a splash on its own but quietly reinforces an important rule: every packet parser must prove its preconditions before it trusts memory. In Bluetooth, where packets arrive from nearby devices and protocol behavior can be messy, that rule matters even more. If downstream vendors shd quickly, this CVE will likely fade into the long list of small but necessary kernel corrections. If they do not, it will become another reminder that tiny validation mistakes can carry outsize consequences once they sit inside the operating system’s networking core.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center