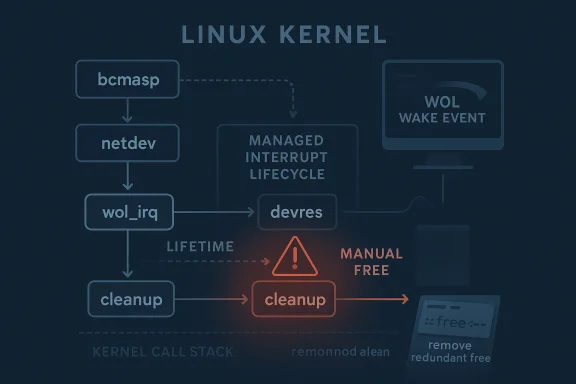
The Linux kernel has disclosed CVE-2026-31506, a bug in the bcmasp network driver that can trigger a double free of the Wake-on-LAN IRQ if the cleanup path frees an interrupt that was already managed by
The central detail in the advisory is the use of
That makes the issuing from an engineering perspective. The code probably worked most of the time, which is how ownership bugs persist in mature kernels. They often show up only when teardown happens in the right order, on the right hardware, or under the right error path. Those are the moments when a resource is released twice, a reference count goes negative, or a cleanup hook assumes it is the only one standing.
The CVE record is also a reminder that not every security-relevant Linux issue is a glamorous remote-code-execution candidate. Some are quieter, lower-level, and more about kernel integrity than direct compromise. Yet even a “mere” double free in kernel space is a serious event because memory and resource management bugs can ripple outward into crashes, corruption, or future exploitability if the surrounding conditions align.
At its simplest, the issue is a mismatch between who allocates and who frees. The
The fix is therefore not to add more cleanup, but to subtract it. That may sound backwards to non-kernel developers, yet it is one of the most common patterns in Linux maintenance: if you chose a managed API, you must let the framework own the teardown path. Mixing manual and managed cleanup is how double frees happen.
In practical terms, the issue is likely to affect error handling and device removal more than normal packet flow. That matters because the most dangerous bugs are often hidden in shutdown paths, suspend/resume transitions, and probe failures where reviewers are naturally less focused than they are on the hot path.
The bcmasp driver name tells us this is a Broadcom-related network path, which means the code likely sits in an area where low-level hardware integration matters more than abstract protocol logic. Network drivers are particularly prone to lifecycle mismatches because they often need to register interrupts, map device memory, and hold on to hardware state while the kernel also expects clean resource ownership boundaries.
Managed device APIs such as
This is why the advisory’s wording matters so much. The fix is not a redesign. It is a correction of the contract between the driver and the kernel’s managed-resource layer. That kind of fix is often very backportable because it changes behavior only where the bug exists, without restructuring the subsystem.
It is tempting to assume that a modern kernel’s safety layers will catch everything. They won’t. The kernel is still full of subsystems that depend on precise lifetimes, and managed APIs only work when the surrounding code honors them. If the driver already handed cleanup over to the device framework, a second manual free is not harmless redundancy; it is an invalid operation.
The reason this often survives into production is simple: cleanup code is hard to test exhaustively. Most test suites exercise success paths, while resource ownership problems often emerge during rare error transitions or teardown sequences. That is one reason Linux maintainers continue to assign CVEs to bugs that are “just” correctness issues on paper but operationally important in the field.
But managed APIs are not magic. They are contracts. If a driver registers an IRQ through a managed helper and later frees the same IRQ manually, it is effectively bypassing the ownership model the kernel established. That breaks the abstraction and introduces a bug where the framework and the driver both believe they are responsible for the same resource.
The fix in this case follows the cleanest possible rule: remove the manual free and trust the framework. That is not just stylistically correct; it is semantically correct. The device core can only protect you if you let it own the release path.
A few practical implications follow from that design:
That is the kind of bug that slips through when code evolves in stages. A driver may begin with manual cleanup, then later be converted to use a managed helper, and the old free call remains behind as dead weight. The result is a subtle duplication of responsibility that is easy to miss unless the reviewer is specifically checking lifecycle ownership.
Kernel developers are especially sensitive to this because allocator state is shared infrastructure. A double free can corrupt the very bookkeeping the kernel uses to determine what is still live. Even if the immediate symptoms are only a warning or a panic, the underlying corruption can have wider consequences if the bug is ever chained with other defects.
The useful lesson is not merely “double frees are bad.” It is that lifetime semantics are security-relevant. A driver does not have to read from user input to create a security problem; it only has to violate the kernel’s resource model in a way that destabilizes privileged code.
This is why kernel maintainers treat double frees as more than correctness nits. They are signs that state transitions are not fully understood or not fully respected. The issue may be narrow, but the principle is broad: if a subsystem cannot reliably say whether a resource is still owned, it can eventually do the wrong thing with that resource.
That is why WoL bugs often show up in suspend/resume, shutdown, and error-recovery flows. Those paths are inherently more complex than ordinary packet handling because they cross subsystem boundaries. A driver that works perfectly during normal operation can still fail in these corner cases.
The fact that the vulnerable object is an IRQ makes the issue more delicate. Interrupts are core kernel primitives, and handling them incorrectly can have consequences far beyond the driver itself. A bad release path may not just affect WoL; it can affect the driver’s entire relationship with the device lifecycle.
In that sense, the bug is about more than a wake feature. It is about how the driver and the kernel coordinate hardware state transitions. That is a subtle but important distinction for administrators who may think WoL is a niche feature when in reality it touches low-level resource management.
In other words, this is a reliability issue with security implications, not a headline-grabbing exploit primitive. That does not make it unimportant. It makes it the kind of bug that slips through in deployed fleets because the trigger conditions are specialized and the visible symptom may be intermittent.
This is also the kind of fix that tends to age well. If future developers revisit the code, they see one clear rule: the IRQ is managed by the device core. There is no ambiguity about whether cleanup belongs in one function, two functions, or a fallback path. Clarity is a real security control in kernel code.
The larger lesson is that less code can be safer when it removes ownership ambiguity. That is especially true in driver teardown logic, where the same object may be touched by multiple subsystems at once.
A concise way to understand the patch is:
It also means downstream vendors are likely to fold the fix into their own kernel streams relatively quickly, especially if the driver is used on shipping hardware. The lack of a completed NVD severity assessment at publication time does not change the technical urgency of the underlying correction, even if it delays centralized scoring
That said, consumer visibility is not the same as consumer irrelevance. If a kernel bug is present in widely distributed builds, it can still matter for future hardening and for preventing rare but disruptive failures. Kernel quality work often protects users who never know the bug was there.
The impact is especially relevant for systems where WoL is part of operational policy. Data center nodes, office endpoints managed for remote wake, and appliances that need reliable power-state transitions all have a stake in this kind of fix. Even if the exploitability is not obvious, the operational correctness is.
The broader enterprise takeaway is that low-level driver bugs can be patch-priority items when they affect infrastructure reliability. That is true even when the CVE is not associated with a dramatic attack story. In production, stability is security.
It will also be worth watching whether any related cleanup bugs surface in adjacent network-driver code. Once a managed-resource mismatch appears in one driver, reviewers often become more attentive to similar patterns elsewhere. That is one of the quieter benefits of CVE handling: it sharpens scrutiny across the subsystem.
In the end, CVE-2026-31506 is a reminder that kernel hardening often advances one carefully corrected ownership bug at a time. The code change is modest, but the principle behind it is foundational: when the device core owns cleanup, the driver must not try to own it too. That rule keeps the kernel honest, and in low-level systems work, honesty about ownership is what keeps the machine standing.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
devm_request_irq(). Because the device-managed IRQ framework automatically releases resources, the bug is fundamentally one of ownership confusion rather than exotic exploitation, but kernel ownership bugs are still the kind that can destabilize systems in ways administrators do not appreciate until they see a crash or a hard-to-reproduce fault. The published description and reference history make clear that the upstream fix is a small but important correction: stop freeing wol_irq manually and let devres do the job it was designed to do VE sits squarely in the class of Linux kernel defects that are easy to dismiss at first glance and hard to ignore once you understand the failure mode. The code path is narrow, the wording is terse, and the patch is conceptually simple. But that simplicity is exactly why this sort of bug matters: the kernel is a system of tightly coupled lifetimes, and if one subsystem assumes it owns a resource that another subsystem already manages, the result can be a release bug with unpredictable consequences.The central detail in the advisory is the use of
devm_request_irq(). That API does not just register an interrupt line; it also binds the IRQ lifecycle to the device lifecycle so that the kernel’s managed-resource framework can clean it up automatically. In other words, the driver should not act as though it is separately responsible for freeing the IRQ. The fix acknowledges that contract and removes the redundant manual free pathThat makes the issuing from an engineering perspective. The code probably worked most of the time, which is how ownership bugs persist in mature kernels. They often show up only when teardown happens in the right order, on the right hardware, or under the right error path. Those are the moments when a resource is released twice, a reference count goes negative, or a cleanup hook assumes it is the only one standing.
The CVE record is also a reminder that not every security-relevant Linux issue is a glamorous remote-code-execution candidate. Some are quieter, lower-level, and more about kernel integrity than direct compromise. Yet even a “mere” double free in kernel space is a serious event because memory and resource management bugs can ripple outward into crashes, corruption, or future exploitability if the surrounding conditions align.
 What the Bug Is Actually Doing
What the Bug Is Actually Doing
At its simplest, the issue is a mismatch between who allocates and who frees. The wol_irq interrupt appears to have been instantiated with a managed helper, but code elsewhere still tried to free it explicitly. That creates a second release of the same resource, which is precisely the kind of lifecycle violation kernel developers work hard to avoid.The fix is therefore not to add more cleanup, but to subtract it. That may sound backwards to non-kernel developers, yet it is one of the most common patterns in Linux maintenance: if you chose a managed API, you must let the framework own the teardown path. Mixing manual and managed cleanup is how double frees happen.
In practical terms, the issue is likely to affect error handling and device removal more than normal packet flow. That matters because the most dangerous bugs are often hidden in shutdown paths, suspend/resume transitions, and probe failures where reviewers are naturally less focused than they are on the hot path.
- Managed resources exist specifically to reduce cleanup mistakes.
- Manual release of a managed IRQ can create a double free.
- The bug is tied to teardown semantics, not everyday traffic.
- The fix is conceptually small but structurally important.
Background
Wake-on-LAN support is one of those features that seems mundane until someone needs to power up a machine remotely and it fails at the worst possible time. In Ethernet drivers, WoL typically means keeping a minimal amount of logic alive so that a sleeping system can respond to a special packet and wake itself up. That requires a delicate balance between power management, interrupt handling, and device state tracking.The bcmasp driver name tells us this is a Broadcom-related network path, which means the code likely sits in an area where low-level hardware integration matters more than abstract protocol logic. Network drivers are particularly prone to lifecycle mismatches because they often need to register interrupts, map device memory, and hold on to hardware state while the kernel also expects clean resource ownership boundaries.
Managed device APIs such as
devm_request_irq() were created to reduce the class of bugs where a driver author forgets a cleanup path or frees a resource twice. They shift responsibility to the device core, which automatically unwinds allocations when the device goes away. That is a reliability win, but only if the driver code respects the abstraction and does not second-guess it later.This is why the advisory’s wording matters so much. The fix is not a redesign. It is a correction of the contract between the driver and the kernel’s managed-resource layer. That kind of fix is often very backportable because it changes behavior only where the bug exists, without restructuring the subsystem.
Why Double Free Bugs Still Matter
A double free is not just a theoretical memory-management mistake. In kernel space, it can corrupt allocator state, trigger crashes, or produce undefined behavior that only manifests under certain timing conditions. Even when the immediate impact appears limited, these bugs are treated seriously because they erode the assumptions that keep the kernel stable.It is tempting to assume that a modern kernel’s safety layers will catch everything. They won’t. The kernel is still full of subsystems that depend on precise lifetimes, and managed APIs only work when the surrounding code honors them. If the driver already handed cleanup over to the device framework, a second manual free is not harmless redundancy; it is an invalid operation.
The reason this often survives into production is simple: cleanup code is hard to test exhaustively. Most test suites exercise success paths, while resource ownership problems often emerge during rare error transitions or teardown sequences. That is one reason Linux maintainers continue to assign CVEs to bugs that are “just” correctness issues on paper but operationally important in the field.
- WoL is a low-power feature with nontrivial driver complexity.
- bcmasp sits in a hardware-facing part of the networking stack.
- Managed cleanup APIs are only safe when used consistently.
- Double free defects are especially dangerous in kernel allocators.
- Rare teardown paths are a common source of these bugs.
The Role of devm_request_irq()
The managed IRQ API is the heart of this CVE.devm_request_irq() does more than register an interrupt handler; it ties the lifetime of that IRQ to the device object so the kernel can free it automatically when the device is released. That saves drivers from writing bespoke cleanup code and reduces the chance of leaks or mismatched teardown.Why Managed Cleanup Exists
The Linux kernel has long moved toward managed helpers because they lower the burden on driver authors and make error paths more reliable. Instead of requiring every exit branch to remember every allocation, the device core unwinds resources in a predictable order. That is exactly the kind of structural support that prevents cleanup bugs in complex drivers.But managed APIs are not magic. They are contracts. If a driver registers an IRQ through a managed helper and later frees the same IRQ manually, it is effectively bypassing the ownership model the kernel established. That breaks the abstraction and introduces a bug where the framework and the driver both believe they are responsible for the same resource.
The fix in this case follows the cleanest possible rule: remove the manual free and trust the framework. That is not just stylistically correct; it is semantically correct. The device core can only protect you if you let it own the release path.
A few practical implications follow from that design:
- Managed APIs reduce boilerplate, but they also reduce wiggle room.
- Manual cleanup must not duplicate managed cleanup.
- Ownership should be obvious from the call site.
- If a resource is managed, teardown should be centralized.
Kernel Memory Safety and Ownership
Memory safety bugs in the kernel are not all shaped alike. Some are use-after-free defects, some are overflows, and some are double frees. What makes this CVE notable is that the bug does not depend on a large attack surface or an external parser. It is a pure ownership mistake inside a driver cleanup flow.Why Ownership Bugs Are So Persistent
Ownership bugs often survive code review because each individual line looks reasonable in isolation. The driver requests an IRQ, later it cleans up the IRQ, and at a glance the logic appears symmetrical. The catch is that symmetry is only valid if the acquisition path and release path are both manual. Once a managed helper enters the picture, the symmetry is broken by design.That is the kind of bug that slips through when code evolves in stages. A driver may begin with manual cleanup, then later be converted to use a managed helper, and the old free call remains behind as dead weight. The result is a subtle duplication of responsibility that is easy to miss unless the reviewer is specifically checking lifecycle ownership.
Kernel developers are especially sensitive to this because allocator state is shared infrastructure. A double free can corrupt the very bookkeeping the kernel uses to determine what is still live. Even if the immediate symptoms are only a warning or a panic, the underlying corruption can have wider consequences if the bug is ever chained with other defects.
The useful lesson is not merely “double frees are bad.” It is that lifetime semantics are security-relevant. A driver does not have to read from user input to create a security problem; it only has to violate the kernel’s resource model in a way that destabilizes privileged code.
What Makes This Different from a Simple Leak
A memory leak is usually a resource exhaustion issue. A double free is more dangerous because it can actively confuse the allocator about the state of memory or resources that have already been returned. That means the kernel may be operating on assumptions that are no longer true, and those assumptions are what keep complex subsystems coherent.This is why kernel maintainers treat double frees as more than correctness nits. They are signs that state transitions are not fully understood or not fully respected. The issue may be narrow, but the principle is broad: if a subsystem cannot reliably say whether a resource is still owned, it can eventually do the wrong thing with that resource.
- Double frees can corrupt allocator metadata.
- They often arise from mixed ownership models.
- Managed APIs reduce risk only when used consistently.
- Cleanup paths deserve the same scrutiny as hot paths.
- Kernel state transitions must be unambiguous.
Why WoL Paths Are Sensitive
Wake-on-LAN support often lives in the boundary zone between power management and networking, which makes it unusually sensitive to teardown mistakes. The driver has to keep just enough state alive for wake events while also participating in normal device lifecycle changes. That creates more opportunities for mistakes than a feature that stays fully on or fully off.Power-State Transitions Increase Complexity
When a machine enters sleep or transitions into a low-power state, the kernel and driver must agree on what remains active. Interrupts may be armed, device context may be preserved, and wake capability may be held in a special mode. Any mismatch in that sequence can leave the driver trying to free something the device core is already planning to release.That is why WoL bugs often show up in suspend/resume, shutdown, and error-recovery flows. Those paths are inherently more complex than ordinary packet handling because they cross subsystem boundaries. A driver that works perfectly during normal operation can still fail in these corner cases.
The fact that the vulnerable object is an IRQ makes the issue more delicate. Interrupts are core kernel primitives, and handling them incorrectly can have consequences far beyond the driver itself. A bad release path may not just affect WoL; it can affect the driver’s entire relationship with the device lifecycle.
In that sense, the bug is about more than a wake feature. It is about how the driver and the kernel coordinate hardware state transitions. That is a subtle but important distinction for administrators who may think WoL is a niche feature when in reality it touches low-level resource management.
Operational Impact
For consumers, the likely impact is limited unless the affected hardware and driver combination is actually in use. For enterprises, especially those deploying Broadcom-based systems or relying on WoL for remote power control, the risk is more meaningful. A failure in cleanup or suspend logic may not be visible until the moment the machine is expected to wake cleanly or shut down safely.In other words, this is a reliability issue with security implications, not a headline-grabbing exploit primitive. That does not make it unimportant. It makes it the kind of bug that slips through in deployed fleets because the trigger conditions are specialized and the visible symptom may be intermittent.
- WoL interacts with power management and interrupts.
- Suspend/resume flows are harder to test than normal traffic.
- Hardware-specific paths often hide lifecycle bugs.
- Enterprise systems are more likely to notice operational fallout.
- The issue is likely niche, but not negligible.
How the Fix Works
The appeal of this patch is its restraint. The upstream change does not try to outsmart the framework or add more conditionals. It simply recognizes thatwol_irq came from a managed request and therefore should not be freed manually. That is the right shape of fix for a resource-ownership error.A Cleaner Ownership Model
The most robust fix for a double free is usually to remove the second free. Anything more elaborate risks preserving the original confusion under a different form. By allowing devres to handle the teardown, the code becomes easier to reason about and less likely to break again in future refactors.This is also the kind of fix that tends to age well. If future developers revisit the code, they see one clear rule: the IRQ is managed by the device core. There is no ambiguity about whether cleanup belongs in one function, two functions, or a fallback path. Clarity is a real security control in kernel code.
The larger lesson is that less code can be safer when it removes ownership ambiguity. That is especially true in driver teardown logic, where the same object may be touched by multiple subsystems at once.
A concise way to understand the patch is:
devm_request_irq()acquires the IRQ as a managed resource.- The device core registers ownership for later automatic cleanup.
- The driver’s explicit free duplicates that responsibility.
- The fix removes the duplicate free and trusts devres.
Why This Is Backport-Friendly
Patches like this are attractive to stable maintainers because they are narrow, low-risk, and easy to reason about. They do not change feature behavior, only ownership semantics. That reduces the chance of introducing unrelated regressions while still eliminating the bug.It also means downstream vendors are likely to fold the fix into their own kernel streams relatively quickly, especially if the driver is used on shipping hardware. The lack of a completed NVD severity assessment at publication time does not change the technical urgency of the underlying correction, even if it delays centralized scoring
- The fix removes a *duplicate releaseanaged cleanup now owns the IRQ lifecycle end to end.
- The patch is small enough for stable backports.
- Simpler ownership rules reduce future maintenance risk.
- Clarity in teardown code improves long-term reliability.
Enterprise and Consumer Impact
For most home users, the practical exposure is probably low unless they are using hardware and kernel builds that actually exercise the bcmasp driver’s WoL path. The average desktop or laptop is unlikely to be a frequent victim of a double free that only appears during device teardown. In that sense, this is not the sort of issue that will dominate consumer security headlines.Consumer Perspective
Consumers should still care in principle because kernel bugs are kernel bugs. But the real-world likelihood of noticing symptoms is often tied to specific hardware support and lifecycle events. If WoL is not used, or if the system does not rely on the affected driver, the issue may never surface.That said, consumer visibility is not the same as consumer irrelevance. If a kernel bug is present in widely distributed builds, it can still matter for future hardening and for preventing rare but disruptive failures. Kernel quality work often protects users who never know the bug was there.
Enterprise Perspective
Enterprises have a different calculus. They care about remote management, fleet uptime, and predictable shutdown behavior. If a managed IRQ is double-freed in a device path, that can turn into a crash or a hard-to-debug failure on hardware that is otherwise considered stable.The impact is especially relevant for systems where WoL is part of operational policy. Data center nodes, office endpoints managed for remote wake, and appliances that need reliable power-state transitions all have a stake in this kind of fix. Even if the exploitability is not obvious, the operational correctness is.
The broader enterprise takeaway is that low-level driver bugs can be patch-priority items when they affect infrastructure reliability. That is true even when the CVE is not associated with a dramatic attack story. In production, stability is security.
- Consumer risk is likely lower unless the hardware path is in use.
- Enterprise risk rises when WoL is part of fleet management.
- Driver teardown bugs are especially relevant for managed systems.
- Reliability failures can be expensive even without exploitation.
- Patch priority should follow operational dependence.
Strengths and Opportunities
This CVE also highlights several positive aspects of the Linux maintenance process. The fix is narrow, the ownership error is easy to understand once exposed, and the kernel’s managed-resource model gives maintainers a straightforward way to prevent the bug from recurring. That combination is exactly what you want in a backportable driver security fix.- Clear root cause: the bug is an ownership mismatch, not a mysterious crash.
- Small patch surface: the fix removes a redundant free, limiting side effects.
- Good framework fit: devres is designed to prevent this kind of error.
- Low regression risk: behavior changes only where the bug existed.
- Backport potential: stable kernels can absorb the fix cleanly.
- Better maintainability: future readers will see one source of cleanup truth.
- Stronger lifecycle discipline: managed APIs reinforce safer driver patterns.
Risks and Concerns
Even though the patch is small, the underlying lesson is serious. Kernel cleanup mistakes can remain dormant for a long time, surface only under rare conditions, and still create high-impact failures when they do appear. That makes them particularly troublesome in infrastructure settings where debugging time is expensive.- Double-free risk can lead to allocator corruption or a crash.
- Rare trigger paths make the bug hard to catch in routine testing.
- Mixed ownership models invite future regressions if code is refactored again.
- Hardware specificity may delay detection in diverse fleets.
- Teardown bugs can affect suspend, shutdown, and error recovery.
- Operational disruption may be the first visible symptom.
- False confidence is a danger when the fix looks “too simple.”
Looking Ahead
The next thing to watch is how quickly downstream kernel vendors fold this fix into their supported streams, especially on platforms where bcmasp-based hardware is deployed. Because the patch is narrowly scoped and clearly tied to a managed-resource misuse, it is the kind of change that maintainers can adopt with relatively low risk. That should speed its way through stable trees and vendor kernels.It will also be worth watching whether any related cleanup bugs surface in adjacent network-driver code. Once a managed-resource mismatch appears in one driver, reviewers often become more attentive to similar patterns elsewhere. That is one of the quieter benefits of CVE handling: it sharpens scrutiny across the subsystem.
Key things to watch
- Stable kernel backports for supported Linux branches.
- Vendor advisories that identify affected hardware and package versions.
- Any follow-up cleanup fixes in adjacent driver lifecycle code.
- Reports of shutdown, suspend, or WoL-related regressions in field deployments.
- Whether additional IRQ ownership mismatches are found in other Broadcom-related paths.
In the end, CVE-2026-31506 is a reminder that kernel hardening often advances one carefully corrected ownership bug at a time. The code change is modest, but the principle behind it is foundational: when the device core owns cleanup, the driver must not try to own it too. That rule keeps the kernel honest, and in low-level systems work, honesty about ownership is what keeps the machine standing.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center