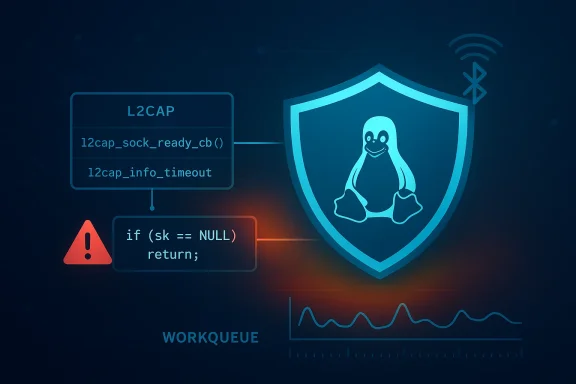
Linux has published another Bluetooth kernel fix that looks small on the surface but matters for anyone tracking availability and stability risks in the network stack. CVE-2026-31510 covers a null-pointer dereference in l2cap_sock_ready_cb, where the kernel now checks whether the sk pointer is null before using it. The crash report associated with the issue shows a KASAN-detected fault in the Bluetooth L2CAP path, and the call trace ties it directly to
The NVD record shows the issue was published on April 22, 2026, and the description explicitly links it to a Linux kernel resolution in Bluetooth L2CAP. The same record also includes several stable-branch references, which is usually a strong signal that maintainers have already carried the patch into supported release lines rather than leaving it as a purely upstream change. Microsoft’s Security Update Guide also picked up the CVE entry, which matters because many enterprises use Microsoft’s vulnerability tracking as a cross-platform intake source even when the affected software is Linux-based.
The crash details embedded in the record are equally important. The trace shows a KASAN null-ptr-deref, a workqueue path, and a call stack that reaches
The real story here is not that Linux Bluetooth has a single bad pointer check. It is that the kernel still has a large surface where state transitions, timing, and object lifetime interact in ways that are difficult to reason about perfectly. That is why these fixes keep appearing, and why the stable kernel process remains so important. Small changes can have outsized value when they protect hot paths in widely deployed subsystems.
The public description is concise: before using the sk pointer, the code should check whether it is null. In practical terms, that means
That is the essence of a kernel null-pointer dereference: the code expects a live object, but the object has already disappeared or was never properly established in the first place. In user space, that usually means a process crash. In kernel space, it can mean a full system panic, watchdog reset, or service outage depending on configuration and crash policy.
A narrow fix is also a clue about severity. If a bug can be stopped with a guard clause and does not require a broader redesign, it often indicates the dangerous behavior is localized. That does not make the flaw harmless, but it does suggest the patch should be easier for downstream vendors to backport cleanly.
That distinction is important. Timeouts and workqueues are often harder to test than direct function calls, and they can create the kind of race-adjacent behavior that sanitizers like KASAN are particularly good at exposing. In other words, the bug is less about a single bad line and more about the reliability of asynchronous Bluetooth state management.
That is because L2CAP is not an optional addon. It is part of the plumbing that almost every meaningful Bluetooth interaction depends on, whether that is a headset, a keyboard, a wearable, or a gateway device. If the kernel’s L2CAP state machine stumbles, the user experience often looks like “Bluetooth stopped working,” even when the root cause is a very specific callback failure.
That is why kernel developers keep adding more defensive checks around callback entry points. The code may have been logically correct when written, but logical correctness and lifecycle safety are not always the same thing in concurrent systems.
For enterprises, the question is broader. Fleet laptops, point-of-sale systems, industrial tablets, and managed endpoints often rely on Bluetooth more heavily than people realize. In those environments, a bug in connection readiness can become a support burden long before anyone labels it a security issue.
At the same time, the record itself says NVD has not yet assigned a CVSS score. That is not unusual for newly published kernel CVEs. It usually means the public record exists before NVD enrichment has fully caught up, not that the issue is somehow unimportant. The lack of a score should be read as “assessment sent”.
This matters operationally because downstream vendors often backport the exact logic change rather than bumping the whole kernel version. So version numbers alone are rarely enough. What administrators actually need to know is whether their vendor kernel includes the specific backported fix.
That is a useful reminder that many kernel CVEs are found not through live exploitation but through instrumentation, testing, and sanitizers. In the Bluetooth stack, where asynchronous events and multiple layers of state are normal, those tools are especially valuable.
That trend is not accidental. The kernel is too large and too performance-sensitive for broad defensive overhauls everywhere. Instead, maintainers keep adding explicit checks at the boundary where bad state first becomes visible. The result is a steady stream of small but important corrections.
The operational value comes from the combination of factors: privileged execution, asynchronous callbacks, and a subsystem people expect to “just work.” Bluetooth is not treated like a critical server path until it fails. Then it becomes critical very quickly.
This is also why CVEs in networking and wireless stacks often deserve more attention than their short descriptions suggest. A defect can be narrow and still be high impact if it sits in a common path with broad deployment.
That principle shows up all over modern kernel hardening. It is not glamorous, but it is effective.
Enterprise exposure is more complicated and more important. In managed fleets, failures that appear “rare” on a single device can become very expensive when multiplied across hundreds or thousands of endpoints. A Bluetooth crash on a business laptop may be a help-desk ticket. The same issue on a field device, kiosk, or shared workstation can become a workflow interruption.
The issue also matters more where kernel crashes are operationally expensive. If a device needs manual recovery, loses unsaved work, or interrupts active connections, then a “mere null deref” stops being a theoretical bug and becomes a business problem.
That is why the practical response should focus on what the bug can do to uptime, not just on whether it can be weaponized.
The second thing to watch is whether any related Bluetooth callback paths get additional scrutiny. A null check fix in one readiness callback often leads reviewers to ask whether similar assumptions exist elsewhere in the subsystem. That kind of follow-up audit is one of the healthiest outcomes a CVE can produce.
The practical checklist from here is straightforward:
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
l2cap_info_timeout and l2cap_conn_start, which makes this more than a theoretical cleanup item oth vulnerabilities in Linux have a familiar shape by now: a relatively small logic mistake in a deeply shared subsystem, followed by a crash that only needs the wrong timing or state transition to become visible. The L2CAP layer sits right in the middle of Bluetooth’s connection-management machinery, so bugs there tend to be disruptive even when they do not clearly lead to code execution. In this case, the public description says the fix is simply to avoid dereferencing a null socket pointer, but kernel history suggests that “simply” is doing a lot of work.The NVD record shows the issue was published on April 22, 2026, and the description explicitly links it to a Linux kernel resolution in Bluetooth L2CAP. The same record also includes several stable-branch references, which is usually a strong signal that maintainers have already carried the patch into supported release lines rather than leaving it as a purely upstream change. Microsoft’s Security Update Guide also picked up the CVE entry, which matters because many enterprises use Microsoft’s vulnerability tracking as a cross-platform intake source even when the affected software is Linux-based.
The crash details embedded in the record are equally important. The trace shows a KASAN null-ptr-deref, a workqueue path, and a call stack that reaches
l2cap_sock_ready_cb during l2cap_info_timeout. That kind of evidence is useful because it confirms this is not just a naming exercise or a speculative issue; it is a reproduced failure mode in a retooth bugs also occupy a strange place in modern risk ranking. On consumer laptops they can feel minor because the affected code may sit idle much of the time, but on devices that depend on Bluetooth peripherals, embedded connectivity, or managed fleet endpoints, a kernel crash can quickly become operationally visible. A bug that lives in connection setup or socket readiness code is especially annoying because it may strike during pairing, reconnect, or timeout handling — exactly the moments when administrators expect the stack to be least fragile.The real story here is not that Linux Bluetooth has a single bad pointer check. It is that the kernel still has a large surface where state transitions, timing, and object lifetime interact in ways that are difficult to reason about perfectly. That is why these fixes keep appearing, and why the stable kernel process remains so important. Small changes can have outsized value when they protect hot paths in widely deployed subsystems.
 What the CVE Actually Says
What the CVE Actually Says
The public description is concise: before using the sk pointer, the code should check whether it is null. In practical terms, that means l2cap_sock_ready_cb was assuming a socket object existed in a code path where that assumption could fail. Once the pointer is null, even a seemingly harmless access can send the kernel into a fault path.That is the essence of a kernel null-pointer dereference: the code expects a live object, but the object has already disappeared or was never properly established in the first place. In user space, that usually means a process crash. In kernel space, it can mean a full system panic, watchdog reset, or service outage depending on configuration and crash policy.
Why a null check is enough here
The fix described for CVE-2026-31510 appears narrowly scoped. Rather than reworking Bluetooth connection management, the patch simply makes the callback defensive about the socket pointer. That is usually the right move when the bug is caused by a missing assumption rather than a larger architectural error.A narrow fix is also a clue about severity. If a bug can be stopped with a guard clause and does not require a broader redesign, it often indicates the dangerous behavior is localized. That does not make the flaw harmless, but it does suggest the patch should be easier for downstream vendors to backport cleanly.
- The bug is in Bluetooth L2CAP, not a separate driver stack.
- The failure is a null-ptr-deref, not an obvious memory corruption primitive.
- The crash happens in a workqueue-driven path.
- The fix is a pre-use null check.
- The stable kernel references imply backports are already underway.
What the trace tells us
The embedded crash text matters because it gives the vulnerability a concrete execution path. The trace showsl2cap_info_timeout leading into l2cap_conn_start, which then reaches l2cap_sock_ready_cb. That suggests the bug can surface during timed connection handling, not just during explicit.That distinction is important. Timeouts and workqueues are often harder to test than direct function calls, and they can create the kind of race-adjacent behavior that sanitizers like KASAN are particularly good at exposing. In other words, the bug is less about a single bad line and more about the reliability of asynchronous Bluetooth state management.
Why Bluetooth L2CAP Matters
L2CAP, the Logical Link Control and Adaptation Protocol, is one of the foundational layers of Bluetooth. It handles multiplexing and segmentation, and it helps translate between higher-level Bluetooth logic and lower-level transport realities. When something goes wrong there, the impact is usually broader than the code diff suggests.That is because L2CAP is not an optional addon. It is part of the plumbing that almost every meaningful Bluetooth interaction depends on, whether that is a headset, a keyboard, a wearable, or a gateway device. If the kernel’s L2CAP state machine stumbles, the user experience often looks like “Bluetooth stopped working,” even when the root cause is a very specific callback failure.
Timing bugs in protocol code
A lot of networking and wireless bugs in the kernel are not dramatic exploitation stories. They are timing bugs, lifecycle bugs, or assumption bugs. That is true here as well. A callback that expects a live socket can be invoked at a moment when the socket has already been torn down, detached, or invalidated by a prior state transition.That is why kernel developers keep adding more defensive checks around callback entry points. The code may have been logically correct when written, but logical correctness and lifecycle safety are not always the same thing in concurrent systems.
- Callback paths are especially sensitive to object lifetime.
- Timeout-driven work often exposes stale assumptions.
- Bluetooth state machines are highly asynchronous.
- KASAN is valuable because it surfaces these failures early.
- A null guard prevents a crash, even if it does not explain the root cause by itself.
Consumer and enterprise exposure
For consumers, the risk usually depends on how central Bluetooth is to the workflow. If a laptop depends on Bluetooth for input devices or audio, an intermittent kernel panic is not a minor annoyance. It can mean data loss, forced reboots, or a device that becomes unreliable enough to mistrust.For enterprises, the question is broader. Fleet laptops, point-of-sale systems, industrial tablets, and managed endpoints often rely on Bluetooth more heavily than people realize. In those environments, a bug in connection readiness can become a support burden long before anyone labels it a security issue.
The Evidence Behind the Fix
The NVD record links CVE-2026-31510 to multiple stable-branch kernel references, and that is often the best early indicator that the Linux community considered the patch worth shipping beyond mainline. Kernel fixes that are both small and clearly bounded are the easiest to backport, which increases the chance that distributions will absorb them quickly.At the same time, the record itself says NVD has not yet assigned a CVSS score. That is not unusual for newly published kernel CVEs. It usually means the public record exists before NVD enrichment has fully caught up, not that the issue is somehow unimportant. The lack of a score should be read as “assessment sent”.
The stable-kernel signal
Stable references are useful for a second reason: they imply maintainers already believe the patch is low risk. Linux stable backports generally favor targeted, comprehensible changes that preserve existing behavior while removing the fault. That is exactly what a null-check fix tends to look like.This matters operationally because downstream vendors often backport the exact logic change rather than bumping the whole kernel version. So version numbers alone are rarely enough. What administrators actually need to know is whether their vendor kernel includes the specific backported fix.
Why KASAN is relevant
The crash report in the CVE text comes from KASAN, Linux’s memory error detection tooling. KASAN does not create the bug; it reveals it. In practice, that means the issue may have been sitting quietly in an edge path until a test or fuzzing setup hit the bad state.That is a useful reminder that many kernel CVEs are found not through live exploitation but through instrumentation, testing, and sanitizers. In the Bluetooth stack, where asynchronous events and multiple layers of state are normal, those tools are especially valuable.
- KASAN identifies access to invalid memory ranges.
- Workqueue traces often point to asynchronous timing issues.
- Stable patches usually indicate a fix is mature enough for backporting.
- New CVEs can appear before CVSS scoring is finalized.
- Vendor kernels may already contain the fix even if the mainline version number has not changed.
How This Fits the 2026 Linux Kernel Security Pattern
CVE-2026-31510 fits a broader pattern we have seen repeatedly in Linux kernel security work: many modern fixes are about tightening assumptions, not rewriting huge subsystems. Kernel developers are increasingly focused on preventing the code from reaching dangerous states in the first place, especially in concurrent or callback-driven paths.That trend is not accidental. The kernel is too large and too performance-sensitive for broad defensive overhauls everywhere. Instead, maintainers keep adding explicit checks at the boundary where bad state first becomes visible. The result is a steady stream of small but important corrections.
Small fixes, large operational value
A patch like this can look trivial to outsiders. After all, “check whether the pointer is null” is a classic defensive programming move. But in kernel space, that classic move often blocks a real crash that would otherwise disrupt a machine that is already under load.The operational value comes from the combination of factors: privileged execution, asynchronous callbacks, and a subsystem people expect to “just work.” Bluetooth is not treated like a critical server path until it fails. Then it becomes critical very quickly.
This is also why CVEs in networking and wireless stacks often deserve more attention than their short descriptions suggest. A defect can be narrow and still be high impact if it sits in a common path with broad deployment.
Kernel hardening as lifecycle management
One of the more interesting aspects of this CVE is that it reinforces the idea that security is often just disciplined lifecycle management. If a callback can be invoked after the object it wants is gone, then the right answer is to refuse to proceed, not to hope the pointer is valid.That principle shows up all over modern kernel hardening. It is not glamorous, but it is effective.
- Check object validity before dereferencing shared state.
- Treat asynchronous callbacks as potentially stale.
- Prefer explicit failure over speculative recovery.
- Backport surgical fixes quickly.
- Use sanitizers to catch lifetime bugs before production users do.
Enterprise Versus Consumer Impact
Consumer impact will likely be uneven. Many desktop users rarely hit the exact Bluetooth state transition that triggers the crash. But for those who rely on Bluetooth keyboards, mice, audio devices, or wearables, a kernel panic is still a serious quality-of-life issue. The fact that the flaw shows up in a timeout path also means it may feel random, which is often worse from a usability standpoint.Enterprise exposure is more complicated and more important. In managed fleets, failures that appear “rare” on a single device can become very expensive when multiplied across hundreds or thousands of endpoints. A Bluetooth crash on a business laptop may be a help-desk ticket. The same issue on a field device, kiosk, or shared workstation can become a workflow interruption.
Where the risk concentrates
The systems most likely to care about this fix are the ones where Bluetooth is not just a convenience layer. That includes portable corporate endpoints, specialized retail hardware, ruggedized field devices, and embedded products that expose wireless peripherals or accessories. In those environments, reliability is the security story.The issue also matters more where kernel crashes are operationally expensive. If a device needs manual recovery, loses unsaved work, or interrupts active connections, then a “mere null deref” stops being a theoretical bug and becomes a business problem.
- Bluetooth-dependent peripherals increase user-visible impact.
- Managed fleets multiply the maintenance burden.
- Embedded and kiosk systems may have weak recovery options.
- Workqueue-triggered failures can appear intermittent.
- Crash-only bugs still create availability risk.
A note on perception
One reason these issues get under-prioritized is that Bluetooth is often thought of as peripheral, literally and figuratively. That perception is outdated. On modern systems, Bluetooth is part of the baseline user experience. If the stack becomes unstable, users notice immediately, even if the actual vulnerability sits deep in the kernel.That is why the practical response should focus on what the bug can do to uptime, not just on whether it can be weaponized.
Strengths and Opportunities
The good news is that this CVE looks like a classic narrow fix with a clean remediation path. That is exactly the sort of vulnerability downstream vendors can absorb quickly, and it gives administrators a concrete item to verify in their patch inventories.- The patch is small and surgical.
- The bug is easy to explain to non-specialists.
- Stable-branch references suggest broad backporting.
- The crash is concrete and reproducible.
- The fix likely carries low regression risk.
- Enterprises can validate vendor backports without waiting for a full major release.
- The issue reinforces better lifecycle checks in callback-heavy code.
Risks and Concerns
The main risk is underestimation. A null-pointer dereference sounds mundane compared with code execution or data theft, but in a kernel it can still crash a machine, interrupt services, and force recovery work. For laptops and endpoint-heavy environments, that is enough to justify prompt patching.- The bug may be dismissed as “just a crash.”
- Timeout-driven failures can be hard to reproduce.
- Some vendor kernels may lag the upstream fix.
- Consumers may not notice until Bluetooth peripherals fail.
- Enterprises may miss exposure if they only track mainline versions.
- Workarounds are unlikely to be satisfying because the issue is in the kernel path.
- The absence of a CVSS score should not be mistaken for low priority.
Looking Ahead
The immediate question is not whether the bug was fixed upstream — it was — but how quickly the fix reaches the kernels people actually deploy. That is the recurring pattern with Linux security work in 2026: upstream publication is only the first mile. Vendor packaging, distribution backports, and fleet rollout are where the real exposure window lives.The second thing to watch is whether any related Bluetooth callback paths get additional scrutiny. A null check fix in one readiness callback often leads reviewers to ask whether similar assumptions exist elsewhere in the subsystem. That kind of follow-up audit is one of the healthiest outcomes a CVE can produce.
The practical checklist from here is straightforward:
- Confirm whether your kernel branch includes the CVE-2026-31510 fix.
- Verify vendor advisories rather than relying on version numbers alone.
- Test Bluetooth-dependent devices after patching.
- Watch for instability in reconnect, timeout, or pairing paths.
- Prioritize fleets where Bluetooth is operationally essential.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center